Today it's exactly five years ago since I first published The Elements of Digital Ethics. I've received so much positive feedback on that chart. People from around the world, tutors and practitioners alike, have shared with me how they make use of the tool in their work and teaching.
So, on this 5-year anniversary, I decided to make it even easier for anyone to start using the elements in everyday work. I've made them into interactive playing cards on a website – and it's free to use for all.
You can visit cards.axbom.com and you'll find two sets of cards already there, The Elements of Digital Ethics and 13 Principles for Good Technology. Jump on over there if you want, but I do recommend first watching my quick video introducing the features of the website.
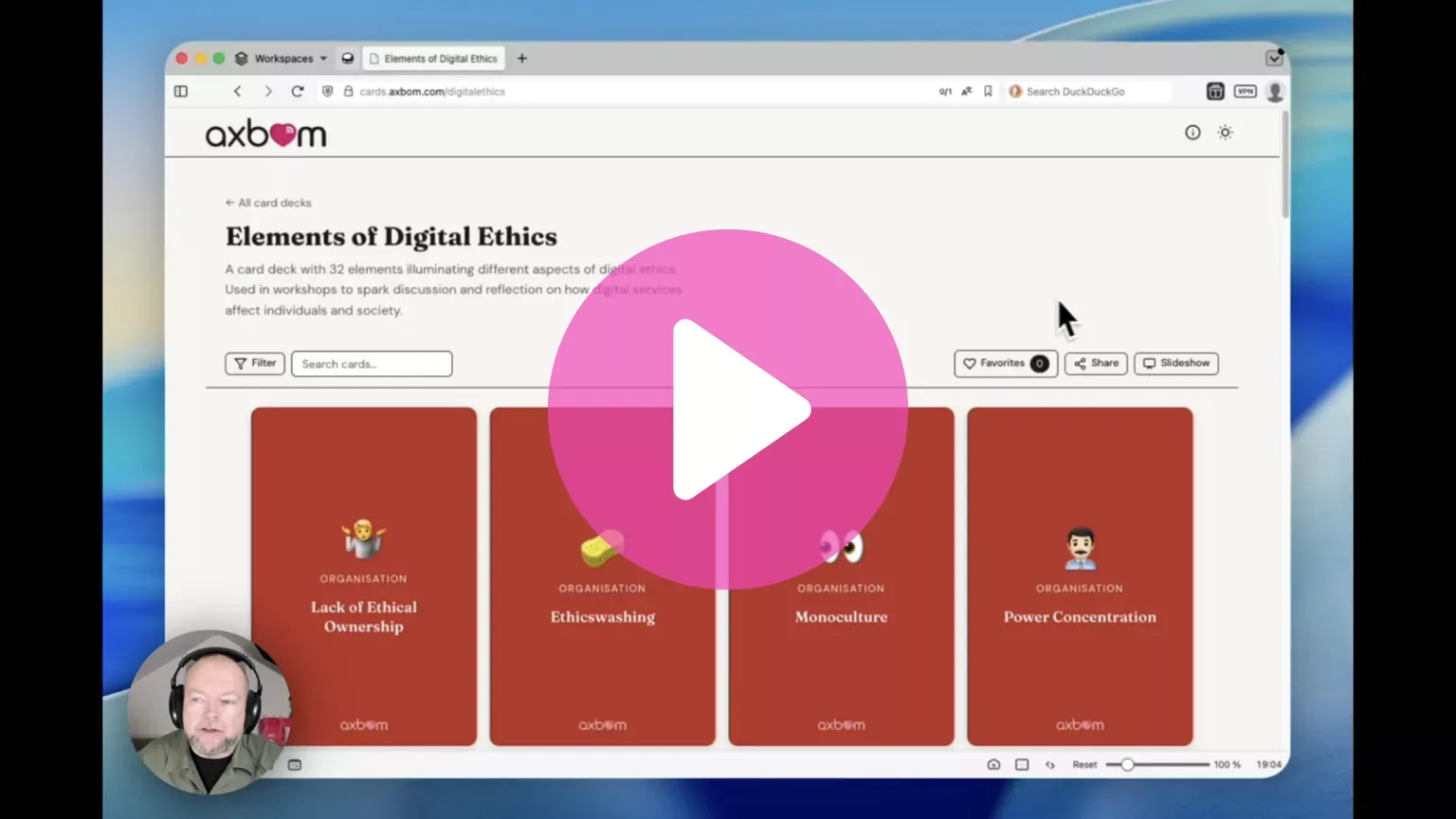
Have a play around with the cards and let me know what you think. And later on, let me know how you get on with using them in a professional setting. ❤️
I'll be adding more card decks with time, and my friends in Sweden will be happy to know the same card decks are available in Swedish on kort.axbom.se.
]]>
This means that we have to seriously start talking about the thought experiment Schrödinger's chat. We
]]>The people behind Chat Control claim that they are not breaking end-to-end encryption. At the same time, private messages on services with end-to-end encryption will be intercepted to uncover crimes.
This means that we have to seriously start talking about the thought experiment Schrödinger's chat. We can safely continue to use chat services that offer secure communication as long as we buy into the premise that the end-to-end encryption is not broken even when each message is available to a third-party service managed by the state. Yep, the secret communication from sender to recipient is both encrypted and unencrypted at the same time.
Or we ask politicians to get their act together and really understand and be honest about the mass surveillance they intend to introduce.
Image description: Schrödinger's chat: A communication that is both encrypted and unencrypted at the same time. Example: Chat Control monitors to expose crimes, but “does not break end-to-end encryption”. The illustration shows two people sending messages to each other. At the top of the image, a person is wearing headphones attached to a listening device that has cords looping behind the back of each person chatting and attaches to their phones.
]]>I get that voice cloning is a wonderful technology for people who have lost their voice and want to use their own voice for expressing their own words. That is giving someone control over self-expression, and self-respect. But when voice cloning is used to copy someone else’s voice for expressing things they never said, that is about removing control and dignity and moving their power across to another actor.
When people use language models to express themselves they are not engaging in self-expression. They are using the copied voices of thousands of other human beings (living and dead) for generating thoughts those people never said, mimicking and averaging the individual quirks and wordplay of texts written in the very real joy, agony and consumed minds of those humans.
It’s Frankenstein expression.
LinkedIn, the Microsoft platform for professional networking, updated its policy regarding hateful and offensive content a few days ago. Specifically, they have removed wording that constituted a clear stance against harassment directed at trans people.
The change was discovered by Open Terms Archive, an organization and service that monitors changes in terms of service and policy texts since early 2023.
The changes follow a clear pattern where a number of large American companies and authorities have downplayed – or completely deleted – content that expresses support for diversity, equity and inclusion. This follows the American president's demands for exactly this, and all major tech platforms in the USA have chosen to scale down, or remove, stated protections against hate speech. Particularly when it concerns trans people.
In LinkedIn's case, they have now removed the clarification that deadnaming and misgendering are prohibited.
- Deadnaming refers to when a trans or non-binary person is addressed or referred to by their previous name after choosing a new name, with a wish for their birth name to be kept private.
- Misgendering happens when someone keeps referring to a trans person using pronouns that don't match their gender identity.
Note that deadnaming can contribute to immediate danger, given there are many prejudiced and violent people. Trans people are threatened, murdered and harassed all over the world. Deliberately using the wrong name also communicates how one chooses to see another human being and wishes for them to be treated. It's happened that malicious individuals systematically search long hours for names that their targets no longer want to be associated with.
Hold Platforms Accountable
When Meta made changes in January and removed several stances against hateful content – including those concerning gender identity – Mark Zuckerberg described it as "restoring free speech." The tech emperors enjoy not having to take responsibility. And having the power to give voice to their own prejudices.
Free speech is of course really about platforms being able to choose which values they want to live by. But then we as users should also demand transparency on exactly this. And we need to decide how our own actions constitute silent consent for things that can be directly harmful to others, or communicate a held position.
The date given for when LinkedIn's policy was last changed has been updated, but the reason for the changes has otherwise not been communicated in their Trust & Safety blog, which is usually standard practice.
In light of this it's important to react to LinkedIn's actions and talk about it. Anything but silence. When far-right propaganda is allowed to spread, this type of event is just the beginning. It's a way to gauge whether there is any real resistance or if most people just give in. Silence signifies consent to let them move forward in the same spirit with the next constructed social group on the list.
I am confident that letters of protest will appear. Sign them. It may not feel like it helps, but it's far better than silence. And those who feel the hardest hits need more support, more people to react.
It took years of struggle to get these wordings into the policy documents. It took seconds to delete them.
I now have to pause and consider how I will manage my own presence on LinkedIn going forward.
Note: The changes have occurred in the English-language text. When Open Terms Archive made checks, it seems that other language versions have not been updated since their monitoring started. That is somewhat odd in itself.
References







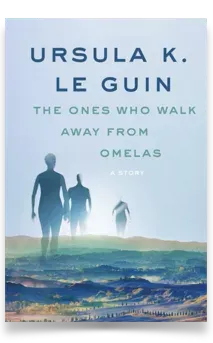
In 1973, Ursula K. Le Guin wrote her award-winning story The Ones Who Walk Away From Omelas. This short science fiction story describes an idyllic city, Omelas, where everyone is happy and healthy. The city celebrates its summer festival with flowers, delicious food, flute playing, and children racing on horseback. The bliss and pleasure embodied by the city feels too good to be true.
And it is.
The wellbeing of its citizens and their ability to flourish is based on a very specific phenomenon: the suffering of a child. In a basement room, this child is kept in darkness, terrified, and without human contact, year in and year out. The description of the child’s suffering is heartbreaking and morbid.
The child is no secret. Everyone in the city knows. It is explained to young residents between the ages of eight and twelve. And they know that their own happiness, loving relationships, and lavish environment depend on the child's misery.
Many, not all, take the time to visit and observe the child. Many are initially shocked but over the years learn to come to terms with the necessity of the arrangement – to protect their own and the city’s prosperity. But every now and then one of these observers walks away. Out through the city gates, never to return.
They walk away from Omelas.
This story is constantly with me as I figuratively see the “children in the basements” of the modern tech industry.
Children and pregnant girls working in mines to extract minerals. Young adults witnessing violence and abuse day after day in their roles as moderators and “AI” workers. People with disabilities facing digital stop signs. Disinformation and deceit that brings conflict and impoverishment. Violence facilitated by remote technology. Surveillance and biometric abuse that strip people of their self-determination.
As I continue to hear and read countless stories of abuse every week, my conviction and determination to continue writing and speaking out about human rights issues in the tech world only grows stronger.
The vulnerable people in the tech world are no secret. They are known but rarely mentioned. Every now and then, a journalist visits their “basement rooms” and reports on brutal distress, hardship, and injustice. For a moment, readers and viewers are upset when witnessing second-hand the naked truth of how people are exploited to enable the growth of the tech industry.
But the outrage is short-lived.
People soon come to terms with the fact that their happiness, relationships, and thriving environment require someone else’s misery. Behind the scenes, workers continue to contribute the natural resources and trauma necessary for the technology to work for its users. Or the technology itself harms through sheer negligence, obliviousness, or superiority.
Le Guin’s story feels cut off, leaving the reader shaken after the fifteen minutes it takes to read it. Who am I, really, in this story? It’s deeply uncomfortable. I just want to walk away from the horrific depiction—appreciating its brevity.
But the contrarian perspectives are flustering. There are people who stay and embrace their own wellbeing, building upon the rule that current circumstances rest on, finding it ever harder to judge what is unjust and what is dignified. And there are people who choose to leave, to walk away.
Who, then, remains to reform?
As long as I muster energy and am able to hold myself together, I want to continue to understand, pay attention to, and explain how technology is a force that profoundly affects equality, power structures, and universal wellbeing. What are current conditions – and what could they be when we do things differently. The multitude of diverse paths. Albeit a small contribution to a slow reform, it's where I see myself providing value.
Thank you dear reader, encourager and contributor, for being part of the journey.
Sketch of the month
Dialogue:
"Are you already in bed?"
"Yes."
"I thought someone was wrong on the internet."
"Lots. But it turns out I have more space for love when I don't fight. I'll write something educational tomorrow… Are you coming?"
Quote of the month
What makes LLMs work isn't deep neural networks or attention mechanisms or vector databases or anything like that.
What makes LLMs work is our tendency to see faces on toast.
– Jason Gorman
Source: mastodon.cloud
Next talk
On July 3rd I'm giving a talk in Manchester at the Camp Digital conference. And it's probably not a topic most people expect me to talk about. I'll be giving a closing keynote on the spectacular lies of maps. The day will take place at the prestigious Royal Northern College of Music and there are a few tickets left. Check out the full schedule.

How's the heart?
I want to spend more time writing about my experiences over the past year, but this latest update is worth sharing:

"Dear Per Axbom, The CT scan on April 30, 2025 shows a good surgical result. The remaining parts of the the carotid artery are completely normal. There is no further follow-up needed in this regard."
– Thoracic surgeon.
It's now possible to support my work. As a Supporter, you contribute 5 Euro per month.
Trivia: Le Guin came up with the name "Omelas" after she saw a road sign in her rearview mirror that read "Salem, O." (Oregon).
]]>
WhatsApp also has end-to-end encryption and even uses Signal's protocol for transferring messages. This implies it's just as safe – but is it really?
What people tend to forget about messaging services is that privacy isn't just about the content of your message. It is also about your metadata: the information about you, your message and your contacts.
Even though the message itself is encrypted, WhatsApp collects a ton of information about you, such as:
- Your phone model and mobile number.
- Your profile picture, and yes: every time you change your profile picture.
- Your contacts' phone numbers
- Data about the operating system, battery level, signal strength, app version, browser info, mobile network, language, time zone and IP address.
- Identifiers used by Meta that are associated with the same account or phone in their other services (Instagram, Messenger, Threads, etceteras)
- Your activity, such as when you send messages and to whom, how often you open the app, and for how long you use the app.
- Your geographical location (via cell towers, Wi-Fi networks and Bluetooth).
- The names of your own groups, and which groups you are a member of.
- and lots more...
Relationship mapping and communication fingerprinting have long been tools for identifying and drawing conclusions about individuals based on patterns in their communication. Your metadata is super interesting, and valuable.
Signal does not store any metadata except for an encrypted "hash" of your mobile number, the date when you created your account, and the timestamp of when you last connected to the Signal service. Things like group names and the like are stored on your device, not at all with Signal. And the metadata of sent messages is encrypted in the same way as the message itself.
If you don't save any information, there's no information to misuse
This means that when authorities request information from Signal, there is no information to share. There is also no information for scammers to steal, and no information for commercial companies to exploit.
WhatsApp is part of Meta's (Facebook's) ecosystem of products and the metadata they collect is how they create value for themselves at your expense by mapping you, your relationships and your behavioral patterns.
Signal has no other purpose than to be a secure messaging service. The Swedish Armed Forces have every reason to recommend Signal.
However, none of the apps will adapt to the Swedish government's wishful thinking of having a backdoor to accessing messages in social media platforms. After all, they don't have access to your messages today. They would naturally rather leave the Swedish market, just as they would 'walk away' from the UK.
It's important to note that you don't need to "have something to hide" for people in power, or a commercial company, to harm you – intentionally or through carelessness.
The statement "I have nothing to hide" truly has nothing to do with personal privacy. It isn't even true, but that's another story. A story that will be the subject of an upcoming newsletter.
This post is available in Swedish.
]]>We're in an era where using Big Tech products for managing our online presence, including our work and our relationships, feels inevitable. But it's really high time for taking steps towards protecting ourselves from data mining, surveillance, lock-in and human rights abuses. And we can certainly reduce our dependency on companies that are misaligned with our values, if not fully remove them. Sure, it requires effort and stamina, and yes, I'll even say it: it's a big trek from big tech. Sorry, not sorry. 😁
I get a great deal of questions about tools I use and/or recommend, and I finally compiled this list. My intent is to keep updating this list regularly, as my curiosity about new tools is ongoing, day-by-day. The internet can be pretty awesome when you leave the trodden path. Also, I've almost certainly missed mentioning a favourite.
Don't expect all services to be free, though! Actually paying for things that are valuable to you, made by other people, is a pretty reasonable deal. And some of these encourage funding in collaboration with friends.
Blog/newsletter 🧑💻
Having your own space to write can be empowering. Most of all, and especially if you own your own domain name, it is sustainable. People can always find you in the same place – at your domain. And if social networks die this is naturally where you let people know where to reach you. And if you don't feel like writing publicly, there is real value in just having a "business card page". Your singular address and start page.
- Ghost – open-source, you can self-host and monetize your writing (search for "Ghost CMS hosting providers" if you want to evaluate managed hosting) – working to integrate with ActivityPub.
- Write.as – a writing platform connected to the Fediverse, they have a free tier and if you are a paid subscriber and downgrade, your writing will still remain online
- WriteFreely – the open source tool powering Write.as, that you can install on your own server
- Posthaven – this old-school service has a goal of forever hosting, even after you stop paying – and note that 10 blogs (that readers can subscribe to) are included in the monthly fee
I don't generally recommend Wordpress anymore. Some years back it just became too bloated. And last year the Automattic CEO went rogue . I also avoid Substack, which has long had a recurring nazi problem. But I get that it's a tough choice for many.
For more info on owning your own space, see my 2022 newsletter on online resilience.
Bookmark manager 🔖
I used to be a fan of the social bookmarking site del.icio.us and Raindrop is a tool I use every day. I mention it here because it provides a ton of value for me in saving articles and PDFs I want to read later. It also makes it easy to share collections of links with others. A general principle is of course that I don’t use tools like this for bookmarking content that I wouldn’t want others to know I am reading. It’s developed and managed by Rustem Mussabekov, a Kazakhstan-based designer/developer, and uses AWS servers in Germany.
- Raindrop.io – all your categories can be given public RSS feeds,
As an example, check out my Digital Ethics collection.
Chat, including video 💬
I do like messaging apps that pride themselves on not knowing anything about you. I’d argue that Signal is an essential app today
- Signal – the app all privacy experts recommend
- Threema – Swiss alternative to Signal
- Delta Chat – decentralized, with multi-profile and multi-device support
- Element (Matrix) – open source and flexible hosting
- Rocket Chat – open source with a team collaboration focus
Cloud/photo storage 🗂️
It's still someone else's computer, but that can make some things easier for sharing. If there is content you really don't want to risk being seen by outsiders, the general advice is to not store it online.
- pcloud – Switzerland-based with a lifetime payment option available
- Jottacloud – servers in Norway powered by 100% renewable energy
- Exoscale – Switzerland-based S3 compatible object storage, meaning it can easily replace your Amazon (AWS) storage
- Hetzner – also S3-compatible with servers in Germany and Finland
- NextCloud – the content collaboration solution you can self-host, offering Files, Talk, Groupware, and Office
Email 📬
Probably one of your most vulnerable touchpoints, a dependable email platform is worth your investment. If you forget your password somewhere else you generally need your email to recover it. If someone with criminal intent gains access to your email you can be in for a world of trouble.
- Migadu – extremely price-worthy if you have many accounts and domains, Swiss company with servers in France – I love their Pro/Cons page with The Drawbacks.
- Proton – "Swiss privacy", with an Easy Switch app for migration
- Tuta – encrypts the entire mailbox, based in Germany
- Soverin – in the Netherlands, with servers across Europe
- Posteo – German-based, maximising sustainability and ethics, with autocrypt support, no own domains
I had Fastmail on the main list before but pulled it down here. It's Aussie-made and owned, but all servers are unfortunately in the US. This makes them a bit more vulnerable than the rest right now.
Email for temporary use 📮
Sometimes you want to sign up, or download, but avoid the potential spam and tracking. That's when burner e-mail comes in handy.
- SimpleLogin – set up email aliases using your own domain
- Maildrop – free, disposable email addresses for any use
- Burnermail – forwards to an account of your choice – generate new burners with a click
Forms/surveys 🧐
Forms are a powerful way of gathering feedback on anything, when you're not in the room. I depend on this for everything from contact forms to questionnaries, quizzes and sales.
- Tally.so – free, intuitive and self-funded form builder based in Belgium
- Formbricks – the open source form builder you can self-host
Forum 🗯️
Many people say they can't leave the groups and forums they love on Big Tech platforms. There were lots of online forums before Big Tech though. These are two pieces of software that come recommended.
- Discourse – self-host a group forum on any topic, comes with an app and email integration
- Mattermost – self-host a premium version of a platform akin to Slack
- Zulip – another open-source alternative to Slack, Teams and Discord
Notes 📝
- Notesnook – your notes are stored encryped even on your device
- Outline – note-taking software I use to write, collaborate and share texts with others
- Tiddlywiki – a note-taking single-file wiki that has been going strong for 20+ years! My colleague and friend James has been a long-time user
Office alternative 💼
- Cryptpad – end-to-end encrypted and open-source collaboration suite
- LibreOffice – compatible with Microsoft Office/365 files (.doc, .docx, .xls, .xlsx, .ppt, .pptx) and backed by a non-profit
Password manager 🕵️♀️
There are many password managers and the choice isn't always straightforward. Some of them let you share a family account, which can be a good thing. I added Bitwarden here because it may help you finally get started using one, if you don't already. Just gonna leave this here: Never have the same password to more than one service.
- Bitwarden – open source, safe and secure management of logins
Personally I have no passwords I can remember, for any service except my password manager.
Podcast players (podcatchers) 🎧
I have produced and listened to podcasts for almost two decades now. I've tried many apps over the years. You may be happy with what you have, or perhaps you want to try something new.
- Pocket Casts – Powerful player available for most platforms, free and open source, made in Australia
RSS readers 📰
The greatest, and most terribly disregarded, document structure in the history of the internet. In short: it allows us to read content from many places in one place. Imperative to podcasting, for example. Many of us swore by it in our use of Google Reader in the years 2005-2013.
- Feedbin – very flexible RSS reader that also gives you a unique, privacy-friendly e-mail address for email subscriptions
- Lire (for Mac/iOS) – pretty good at fetching full articles even when the RSS feed contains only a part of it
Bonus tip: You can convert newsletters to Atom feeds (which your reader will also read) with Kill the Newsletter.
Common Craft made a classic explainer video on RSS in 2007 (on YouTube).
Search engine 🔎
- DuckDuckGo – more powerful than most people realise, bangs are cool and mean you don't need to feel locked into only one search engine
- Qwant – French search engine, hosted in Europe
Self-hosting (VPS) 🔌
Yes, I am relatively technical but my coding and server management skills are mediocre at best. Running my own server seemed daunting and unreachable, until I came across Cloudron. Now, self-hosting my own apps on my own server (including several Ghost sites, document management, wikis, url shortener, social media, chat and more) is truly liberating. You'll need some skills to set everything up, but then it really runs very smoothly on its own, and certainly puts self-hosting within reach for many more people.
- Cloudron – ensures you get the latest releases within days and security fixes within 24 hours for apps and the server
- Yunohost – also has 1-click installation of apps but requires more maintenance from you
I wrote more about Indieweb and self-hosting my own space in 2022.
Social networks 📜
When it comes to the Fediverse there is really an endless number of different flavors of software you may want to try out. Mastodon and Pixelfed are the two most people are likely to start with.
- Mastodon – often referred to as a Twitter alternative, and you can of course join any instance that matches your values
- Pixelfed – there has been lots of development recently on this photo and video sharing platform
- Bluesky – I add this here with a warning: it’s looking good right now but their reliance on financial backers with a background in crypto has me wary; I have written more about how to ensure your resilience on Bluesky
- micro.blog – is a social media platform in itself but also happens to be where I back up most of my posts from other services
For newcomers to the Fediverse I recommend starting with an app that makes the experience a bit smoother, Mona for iOS/Mac or Tusky for Android. And in case you're curious, I actually don't use Mastodon myself, but software called Akkoma.
When I first started out, I wrote several guides for Mastodon. You’ll find me as @[email protected] on Fediverse/Mastodon, and @axbom.com on Bluesky.
Streaming 🎬
I talk a lot about the environmental costs of "AI" but streaming is likely just as big of a culprit. Alternative streaming platforms can be rewarding to try out, but also consider the benefits of renting at your library. 😊
- The Criterion Channel - Monthly curated collection of classic and contemporary films
- Mubi – a British global streaming platform with films by emerging and established filmmakers
- Invidious – an alternative front-end to YouTube, without all the tracking
Video meeting 🎥
- Jitsi – name your meeting room, click and meet, almost like a burner phone for online meetings
- Whereby – the small Norwegian platform I've used for a decade
VPN 🥷
- Mullvad – The Sweden-based and internationally acclaimed service that offers full anonymity – it's actually the only Virtual Private Network (VPN) I feel comfortable recommending
Web browser 🛜
It's not a bad idea to have a separate browser for all your logged in sessions, on Big Tech and otherwise (including video calls and streaming), and then use another primary browser for everyday surfing. That way it's harder for those logged-in sessions to track your movements on the web using embeds and tracking pixels.
- DuckDuckGo – yes, they have a browser, for Mac, Windows, iOS and Android
- Mullvad – yes, they also have browser, for Mac, Windows and Linux
- Firefox Focus – this is for mobile: both iOS and Android
- Librewolf – a custom version of Firefox focused on privacy, security and user freedom
A great complementary utility when you use multiple browsers is an app like Bumpr (Mac only), that allows you to choose which browser to open links in. A similar app for Windows is BrowserSelector.
Web analytics 📈
- Plausible – intuitive, lightweight and open source analytics, made and hosted in the EU
- Matomo – a comprehensive open source platform for web analytics with a ton of features
Web design
- Penpot – a web-based open-source design tool that can easily replace Figma, and do not miss all the tutorials by the brilliant and accessibility-minded Laura Kalbag
A word of advice for EU residents. Most experts agree the EU-US Data Privacy Framework is now null and void. When using US-based services, expect that your information can be read by US government actors. In which case, the less information a service collects about you, the better. The right to privacy is a human right.
Let me know if this post was useful to you, and if there are other nuggets out there you may want to share with me. This is a journey of exploration we can go on together.
Offline resilience
Something I do want to add, in light of the crumbling of democracy we are seeing across the world in 2025, is that it's important to mind your own wellbeing. And take small steps to ensure you have capacity left to check in with yourself and others. There is great power in more often choosing offline variants of dialogue and engagement. One path is to start attending local cultural events and more often visiting your library. Or getting to know a neighbour. These are the types of actions that fortify civil society.
Take care.
]]>You have many data shadows today. These are vague summaries of you as a person that authorities, banks and insurance companies use to assess your suitability for things like employment, benefits, sick pay, discounts and credit. In many contexts, you are merely a risk, the question is how big, and a 'data-driven' organization places great importance on your shadow to determine this.
Unfair treatment by government is certainly not new, or a result of modern algorithms and AI. It is a result of how people are viewed. And of how ideas about efficiency, and reliance on data, affect that view.
Sweden’s daily Svenska dagbladet, together with Lighthouse Reports, recently revealed that an automated system used by Sweden’s social insurance agency, supposedly predicting fraudulent behavior, showed clear signs of discrimination. People seeking temporary child support for sick children were disporportionately held up for scrutiny if they happened to be women, migrants, low-income earners or without a university education.
But we should not be surprised by a phenomenon that authorities have been moving towards for decades. It is today a norm in both the public and private sector to manage data shadows, diluted abstracts of each of us, as if they were a reasonable and accurate representation of our human worth and capacity in some form of presumed hierarchy.
"Payment difficulties, driver's license revocations, hospital stays, conflicts with the child welfare board, school grades, letters of recommendation, medical certificates, which books you've checked out, which newspapers you subscribe to, whether a brother has been to prison, whether a brother-in-law is an organized communist. Soon, perhaps, most of your payments and loans, if the banks are linked via the SIBOL system. Incomes are already there, in the tax agency skyscraper."
This is what human rights activist and member of parliament Kerstin Anér wrote back in 1972, more than half a century ago, when she warned about the data collection that was growing along with with computerization.
In 1972, Sweden’s employment agency had long been collecting data on all job seekers. It’s reported that agency workers protested against what they considered to be inhumane treatment – using people’s own information against them was immediately perceived as unfair. Their sister agency, the National Board of Health and Welfare, also put people into predefined boxes, exemplified by: "alcoholic, slacker, family issues...".
For every citizen, shadow after shadow loomed into existence.
There were reports coming from the United States about computer software being used to assess suitability for different jobs. And the software kept being used even when there were no programmers left who knew how the system worked. This carelessness seemed inconceivable.
But now, fifty years later, the "AI" industry refers to the inner workings of systems as existing in black boxes. Nobody can see or understand how they really function, and no explanations for outputs and conclusions are requested by decision-makers. A baffling number of managers and leaders express that this is fine.
Reducing humans into data points immediately feels scientific and awe-inspiring to people in power. Infallible. Human complexity becomes neat, binary and void of gray areas. Information is encoded in templates known as profiles. If those profiles are correct, fair or relevant becomes secondary. As long as we can output a number through some formulaic assumption. Numbers are so much easier to read than people. And difficult to dispute. Especially when you are kept from tracing their origins.
Anér’s essay continues:
"You hardly notice that it’s only a few single points, taken out of context, that make up the picture. You forget that much of the information in the data image has already been interpreted, and inserted into a context that may not be the original one at all. You have conclusions in front of you — but you think they are raw facts. And so you appoint, dismiss, judge and evaluate a data shadow, but the one who has to bear the consequences is a human being of flesh and blood."
I'm amazed by how accurate she was this early on. How few understood, or even understand today. That we've let it come this far.
Contrary to the promise of empowering humans, computers are also being used to lessen us. Trust can only be restored when these pseudo-calculations cease and organizations find a way back to treating citizens and customers with dignity. Automated evaluation often means automated discrimination, and more effective discrimination is a bad look for the idea of progress.
It is impossible to trust authorities that cannot explain the basis on which their automated assessments are made. Whose managers are unable to account for how the algorithms supporting their core operations work. That this governance through unawareness is even a viable approach in a democracy is mind-boggling.
I’m especially stirred when Anér, in the same essay, questions what happens over time if the purpose of the machine is seen as handling and judging more and more people without exchanging a single word with them. Without listening. Without considering any aspect of their physical being. Her words slap me to alertness, as if I’ve failed to pay attention in class:
"Does this serve humanity, or abolish it?"
In many regards, how your many different data shadows are interpreted by machines and strangers is now more important than how you yourself actually feel.
_____
Per Axbom is a teacher, speaker and advisor in digital ethics, author of the handbook Digital Compassion and co-founder of the think-tank Dataskuggan.
Kerstin Anér's quotes are from the essay "Dataskuggan", published in the Christian cultural magazine "Vår lösen", in 1972. It was in this essay that the term "Dataskugga" was first coined, a term that has since been adopted internationally in the English form "data shadow".
References
- Amnesty International (2024). France: Discriminatory algorithm used by the social security agency must be stopped, amnesty.org, October 16.
- Amnesty International (2021). Dutch childcare benefit scandal an urgent wake-up call to ban racist algorithms, amnesty.org, October 25.
- Axbom, Per (2023). Diagram: Bias in Machine Learning. axbom.com, September 25.
- Axbom, Per (2023). Explaining responsibility, impact and power in AI. axbom.com, November 8.
- Axbom, Per (2023). The Elements of AI Ethics. axbom.com, June 2.
- Axbom, Per (2021). The Elements of Digital Ethics. axbom.com, March 2.
- Booth, Robert (2024). Revealed: bias found in AI system used to detect UK benefits fraud, The Guardian, December 6.
- de Heer, Sarah (2023). A Scandal on AI in Administration, Again: Fortifying Fundamental Rights in the Age of AI, verfassungsblog.de, July 25.
- Granberg, Sascha & Geiger, Gabriel (2024). Sweden's Suspicion Machine, Lighthouse Reports, November 27.
- Heikkiläa, Melissa (2022). Dutch scandal serves as a warning for Europe over risks of using algorithms, Politico, March 29.
- Meaker, Morgan (2024). Algorithms Policed Welfare Systems For Years. Now They're Under Fire for Bias, Wired, October 16.
- Schaart, Eline (2021). Mark Rutte pulls plug on Dutch government, plans immediate return, Politico, January 15.
- Stacey, Kiran (2023). UK risks scandal over ‘bias’ in AI tools in use across public sector, The Guardian, October 23.
- Yigitcanlar et al (2024). Local governments are using AI without clear rules or policies, and the public has no idea, The Conversation, December 11.
In Swedish
Original article: Dataskuggor hos myndigheter suddar ut människovärden (December 15, 2024).
- Anér, Kerstin (1972). 'Dataskuggan'. Vår lösen.
- Amnesty International (2024). Sverige: Försäkringskassan måste upphöra med sitt diskriminerande system, amnesty.se, November 27.
- Amnesty International (2024). Danmark: AI-verktyg riskerar att diskriminera människor som redan lever i utsatthet, amnesty.se, November 13.
- Granberg, Sascha & Geiger, Gabriel (2024). Hemlig AI såg oskyldiga kvinnor som vab-fuskare, Svenska Dagbladet, November 27.
- Kronblad, Charlotta (2022). Algoritmisk orättvisa – när domstolen är blind för digitala bevis, Advokaten nr 6 2022 Årgång 88.
Pictured in the featured image is my Remington Standard 12 typewriter from circa 1925, with a Swedish keyboard. Remington is notable as a brand of typewriter because their first two typewriters introduced features that are still in use today on computer keyboards across the world.
Now, get back to reading about typewriters!
Feature 1: Qwerty
The Qwerty keyboard layout was invented by Christopher Latham Sholes in 1868 and adopted by the first Remington typewriter in 1873.
Many people believe that the Qwerty keyboard layout deliberately placed keys to slow down typists, so that the typebars (the moving bars holding the hammers with the letters) wouldn't get jammed. But that's only partly right.
What Sholes did was place letters that were frequently used together far apart from each other in the mechanical circle that held the typebars. So for example the common letter pair "TH" meant that the respective typebars for T and H had to be hung far apart. This enabled typists to type faster, not slower, because it was now less likely for the typebars to get jammed. It wasn't perfect, but better.
Typing faster without typebars getting caught on each other was made easier when certain letter keys were moved further apart from each other.
What you also may not know is that the original patent by Sholes for the Qwerty keyboard layout had the keys placed like this:

To save on manufacturing costs, the digits 1 and 0 were simply not represented, and typists would just learn to use capital 'I' or capital 'O' to represent those numbers. Punctuation marks were also interspersed among the alphabetical letters, most notably with the period situated where we today find the letter "R". The "R", funnily enough, is on the bottom right, where we now find the period.
It was only in 1873 when E. Remington and Sons bought the patent and manufacturing rights for the Sholes & Glidden 'Type-Writer' that they modified the keys to something that is more similar to what we are accustomed to today. And yes, in case you were wondering, that's the same Remington that made firearms.
Interestingly, moving the R to where it is today enabled the typing of the word "typewriter" using only one row of letters.
While there have been attempts to design the ultimate keyboard layout (such as the Dvorak Simplified Keyboard layout claiming much improved ergonomics) it has been found repeatedly that one layout over another does not make a significant difference. Good typists learn to type fast whatever the layout. No need to fix something that isn't broken, and we've now had the Qwerty layout for more than 150 years.
A fair number of business books mention the Dvorak keyboard as superior and Qwerty as inferior, and while those stories live on, they have largely been debunked. Long story short: the studies claiming Dvorak was faster to type with have been found to be flawed in their execution or in their selection of sample populations.
When it comes to ergonomics and the placement of keys according to how often certain letters are used, this is shaky when considering that the letter placements are simply copied to other countries and languages, or may differ among professions (think programmers versus lawyers). Any such benefit also primarily affects people who touch-type, which many studies reveal to be only about 20% of computer users.
That being said, there are of course many enthusiasts who love to experiment with different layouts. Digital environments truly enable completely personalised key placements, which can help reduce finger strain if you are willing to re-learn typing. I myself am a bit intrigued by the Workman layout.
Feature 2: Shift key
The Remington no. 2 was released in 1880. One of its most notable proponents and users was mystery writer Agatha Christie. This model introduced the first Shift key. Because of its popularity, this of course is also the typewriter model that truly helped the Qwerty layout become mainstream.
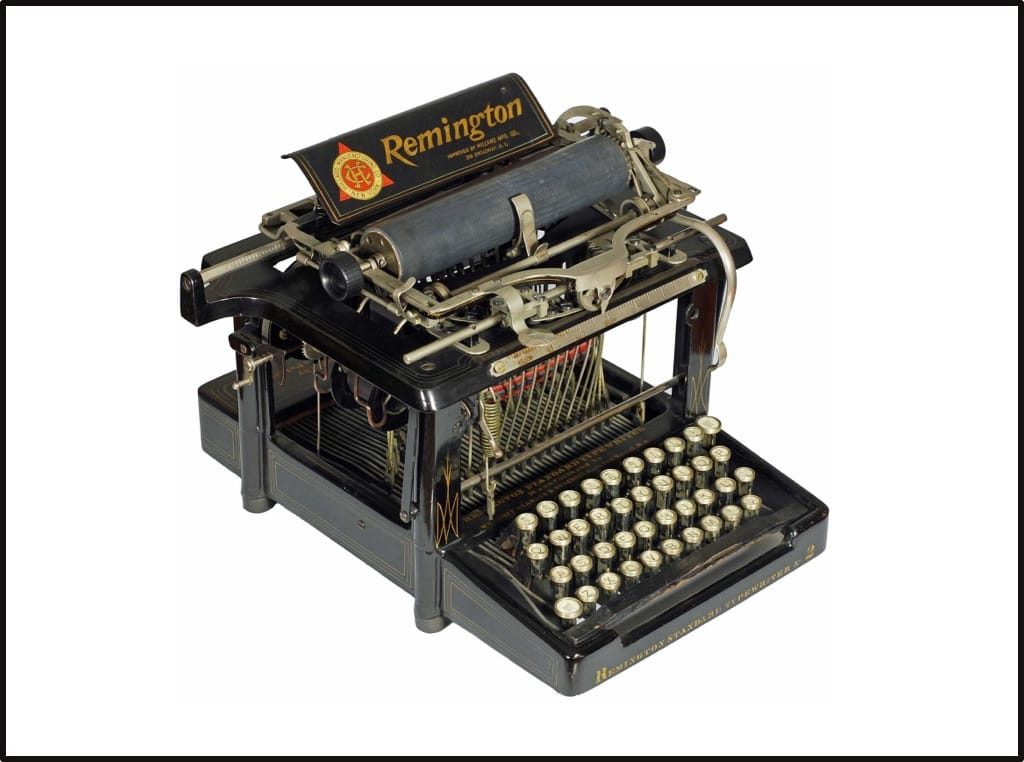
Previous typewriters only had capital letters and the Remington no.2 made it possible to type in both upper and lower case. It was called a shift key because it mechanically shifted the entire carriage upwards so the other character or letter on each typebar would strike the ribbon and paper.

There is no mechanical shifting of letter placement taking place in today's keyboards of course, but the name lives on, as do many more keyboard related terms based in mechanical functions.

The legacy of the carriage return
Some of the first computers I used had a key called carriage return (often today referred to as "Enter", or sometimes even "Return"), even though they of course had no physical carriage to return to its original position. The carriage return key placed the cursor at the beginning of the next line on screen.
Both CR (carriage return) and LF (line feed) live on as terminology in computer programming. In typewriter lingo a carriage return moved the whole carriage to the right, to enable typing at the leftmost position (but on the same line), and a line feed moved the the paper up while the carriage stayed at same horizontal position.
So what we are used to, pressing enter to move the cursor to the beginning of the next line, would formally be a CR + LF, i.e. a carriage return plus a line feed. Which, to be fair, is how many carriage return solutions were implemented.
In computing, both CR and LF are ASCII control characters, so when sending a command to a printer to cause a line break that starts at the leftmost position, this would be coded as CR (codepoint 13) + LF (codepoint 10). This practice has continued on for screen-based interfaces where non-linux based systems (such as Windows) use the combination "\r\n" to denote a return to the beginning of the line combined with a new line.
In some operating systems (notably on Apple Macintosh, but also Linux) the pairing of these two codes was abandoned in favor of a single command "\r" (Mac OS 9 and earlier) or "\n" (Mac OS 10 and later) to accomplish the same thing. This difference between operating systems has often been a source of frustration for engineers.
Demo of a person using a manual carriage return that also creates a line feed on a 1969 Hermes 3000 Vintage Typewriter. Source (Youtube)

Backspace did not delete
The backspace key on my typewriter (in Swedish: "bakslagstangent") of course does not delete the previously typed character but it moves the carriage into a position where the previous character can be 'overtyped'. Hence backspace is the exact opposite of space (move the carriage one space back rather than one space forward). This function could also be used to create combinations of characters. Some early typewriters did not have an exclamation mark so one would use the combination of "apostrophe backspace period" to give the appearance of one.
Later on of course came the correction tape that allowed the application of a thin strip of white tape over misstyped letters, thus making it possible to type a new letter in the same place.
Backspace on computer keyboards, as you know, just immediately deletes the preceding character.
Machines of compassion
The first mechanical typing machine was invented by italian Pellegrino Turri for his blind friend Countess Carolina Fantoni da Fivizzano so she could write him letters. It's suggested they were love letters.
In one of my favorite blog posts, The Technology of Compassion, Norman R. Ball retells the story of Pellegrino and Countess Carolina, and delves into how much mechanical typing machines have meant for people who are blind.
The more you know about them, it's hard not to love typewriters.
Writing "The End." on a typewriter.
Sources






The ambitions expressed by the social network Bluesky bring hope. In addition to its own network, the company is building a technical way to communicate, a so-called "protocol" called AT. This protocol is published in the open, enabling other organizations to create their own, independent platforms that can seamlessly communicate with Bluesky. The hope is that you will never lose your social media connections and posts again, and if you play your cards right: not even your username.
You can already – now – verify your identity and boost trust by having your own domain name as your username. And this costs nothing if you already have a domain name. The username can then continue to work even if in the future you move to another platform that uses the same "protocol".
For example, my username on Bluesky is @axbom.com, the same domain name as this blog.
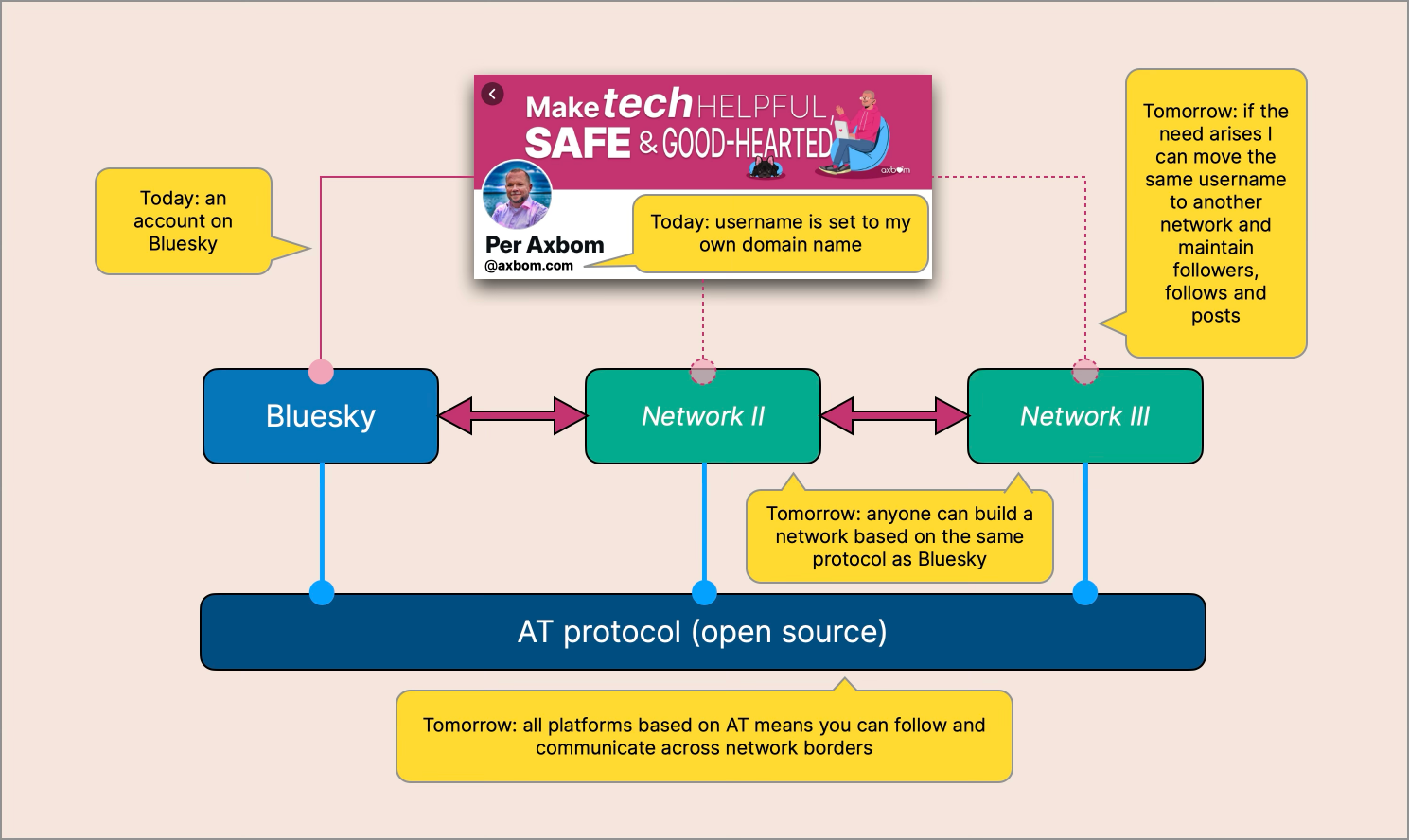
The idea is this: if you are not satisfied with the way the platform is operated, or if it's being shut down for some reason, you could potentially move to another platform and keep your account name, contacts and posts. Something you probably wish you could have done with X/Twitter and other social media you've left over the years.
Note that this ambition has not been realized all the way yet, but let's dare to believe in Bluesky's statements for now, and let's assume they really are – as they say – wanting to "move the social web to protocols, instead of platforms". This means never locking you in and always willing to help you leave.
As an example of this more open culture Bluesky has also stated that they in no way have an algorithm that "punishes" anyone who links out to their own blog. On the contrary, they want you to link and share content to other sites. Yes, the way we probably imagine social media should behave, and more often did more than a decade ago.
Journalists should have verified accounts – for obvious reasons
If you are a company that wants to establish itself on Bluesky, then don't miss the chance to opt early for having your domain name as your username. It took me only a few minutes to set up.
I'm thinking especially of all the media organizations that are finally(!) abandoning X/Twitter. This provides a great opportunity to enable a verified channel and to verify usernames for journalists. Sweden's daily newspaper DN could easily have @dn.se as their username, and the editor-in-chief Peter Wolodarski could then have @wolodarski.dn.se as his username on Bluesky. In addition to boosting trustworthiness, this makes it more difficult for fraudsters to try to assume someone else's identity.
And I'd certainly expect tech journalist Jason Koebler to soon change his username to @jason.404media.co, given that they've already set up @404media.co.
Bluesky's CEO, since 2021, is a woman named Jay Graber. What I have seen of her statements so far feels like an honest intent to create a platform that takes into account the wellbeing of users, and their freedom of choice. The fact that few seem to know of her appears to be part of a conscious strategy not to make the CEO a figurehead and symbol.
I'm not naive - as Bluesky grows, there will be a lot of harassment, pile-ons and crises. And there has been some of that already. How Graber and her team act is during these times is something that many will be keeping their eye on. And yes, Blockchain Capital, with most of its other investments in the crypto world, is the main investor. This is far from trust-inducing, and while Bluesky right now do not use blockchain or cryptocurrency – or scrape user content for AI training, the future of how investors will want see returns is yet to be written.
Jack Dorsey? Yes, he was a key player in the beginning but has now deleted his account on Bluesky and has no ownership left either. He has fully swallowed the vision of X/Twitter as the platform of freedom. I personally see his departure from Bluesky as purely positive.
Eggs in all baskets
I of course won't be leaving the Fediverse (Mastodon et. al), where I enjoy most of my interactions immensely. But unfortunately the experience of getting started there is still not intuitive and user-friendly, nor is it easy to search and find content or users across instances. It's simply something else.
Bluesky is straightforward for more people, and I'm cautiously hopeful about their expressed ambitions and values with regards to the internet, tech and social connections - which broadly align with my own. So I'm giving Bluesky a go as well – and using my own domain name gives me flexibility and options in the future. Even if the AT protocol doesn't become as popular as Bluesky hopes, nobody can take my domain name away from me - it's still a reliable way to find me as social networks come and go. It's resilient.
If Fediverse hasn't been an option for you, chances are Bluesky could be the one if you're looking for community in the style of what Twitter was in its very early days. Just remember to keep an eye on your own wellbeing.
Links
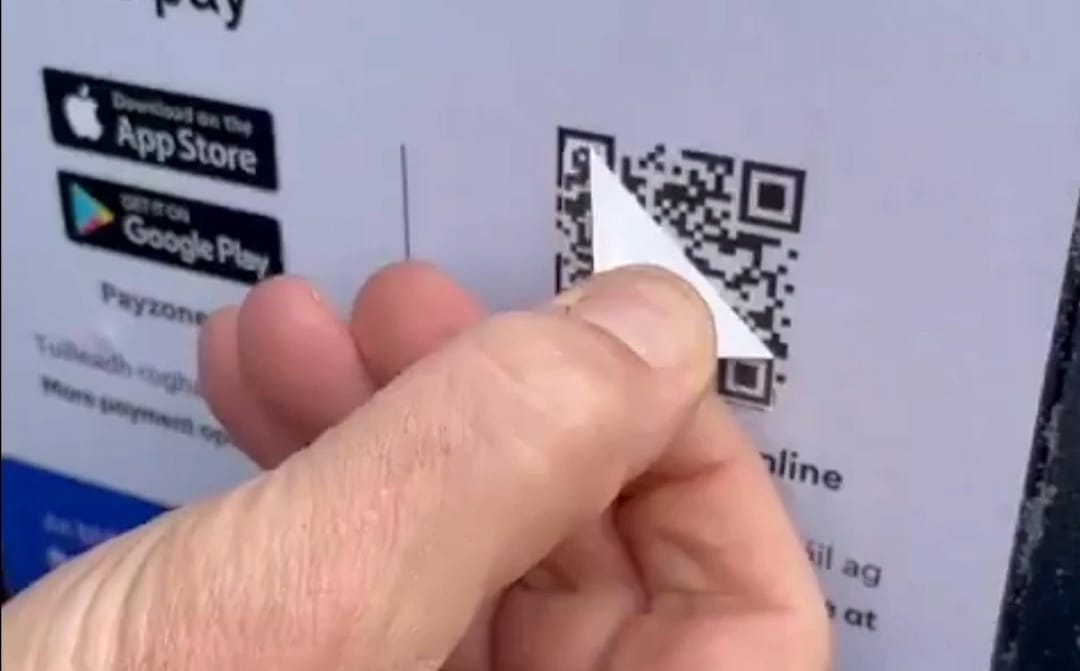
]]>I often warn people about QR codes, but it's easier to understand the seriousness of these warnings when you can clearly see what a scam looks like. Here is a film I was given the okay to use for educational purposes (with my voiceover). In the video a woman peels off a sticker on a sign about parking fees at a car park in Ireland. The sticker, placed with criminal intent, is a QR code that fits perfectly on top of a valid QR code that the parking company has encouraged you to use.
According to a statement, the woman's daughter lost €1,000 after scanning the code, landing on a page that looked legitimate, and entering her credit card details.
Credible actors should not be making use of QR codes in public places. Organizations put their own reputation at risk and they risk the safety of people who are encouraged to scan the code. Sometimes fraudsters are not immediately after money but are seeking to collect personal data or passwords they can use to commit further types of fraud.
Fake QR codes also appear, for example, on campaigns for donating money, marketing materials about getting discounts, and on fake traffic tickets. Criminals, of course, love the fact that government agencies and public sector institutions also encourage citizens to scan QR codes without verifying where they end up.
Friends don't let friends scan QR codes.
P.S.) Thanks to Jonas who tipped me off about the video!
P.S. 2) If you peel off stickers in public places, use a tool and not your bare hands. It has happened that malignant people hide razor blades behind stickers.
Also read

"Regular capacity" might be pushing it a bit. I obviously feel a
]]>On Monday October 14 it's been eight weeks since my open heart surgery. This means that my sick leave comes to an end and I'm back to work at my regular capacity.
"Regular capacity" might be pushing it a bit. I obviously feel a little out of practice and hesitant about how my head and body will deal. At any rate, the last few weeks I've started to feel quite bored, and I understand this is a sign of betterment. A desire to return to work and participate. Create.
And oh my, do I have stories to tell. Stories about blood tests gone missing, misplaced referrals, disputes between health care providers and a contrast fluid allergy that was ignored. I'll likely be sharing these stories in digestible chunks in future writings. There is a lot of truth to the expression that you have to be healthy to be sick. My "user journey" both before and after surgery has been enlightening.
But the operation did go well! The medical tech available today is truly astounding. With a mechanical heart valve and an aortic graft, I now have a healthier heart than ever before in my life. I've already noticed how I can manage steep climbs with more ease, without collapsing of exhaustion.
And you know what? The heart ticks. I don't mean that it's beating, because of course it is. It actually makes a sound... like the big old alarm clock I had as a child. If the room is quiet, I can clearly hear the regular sound of the prosthesis: tick…tock…tick…tock. I wasn't prepared for that. But it does somehow feel reassuring. Rugged.
I'm not gonna pretend there hasn't been a lot of time to think and ponder. Turning 50, vacation, heart surgery, sick leave. Time to think about where I want to focus my energy. What personal projects I want to realize. What I have to stop doing. This too will likely take shape over time and be shared in my forthcoming newsletters.
Getting in shape is my priority right now, though. Starting next week, in addition to going back to work, I will start training under the supervision of a physiotherapist. It's about making sure I get enough cardio training and am creating the habits that will keep my heart healthy.
I'm also now taking what's often called a blood-thinning medicine. Which does not thin the blood at all. It just keeps it from coagulating as quickly. So now you know. I'll be doing this for life, which also means regular blood tests to ensure the right month-by-month prescription. They gave me this terribly ugly necklace saying I'm on anticoagulant drug therapy, to wear in case of an accident. I had to order my own.
And the rest of my body? Primarily left to heal is my rib cage, which can take another month or so. Obviously I'll have to wait a bit on doing push-ups, but I promise a demonstration when the time comes.
I want to say thank you for all the support and well-wishes before, during and after this experience. I haven't been able to respond personally to everyone, but I obviously read EVERYTHING! Now I'm entering a new phase in life, the time after open heart surgery.
I do believe it's going to be a good phase. ❤️
]]>It's not uncommon that I see campaigns on social media asking for donations for pressing and commendable human interest efforts. What has caught my eye is an over-reliance on QR codes in the shared graphics. My concern is how simple it is for people with ill intent to simply edit those graphics and share them with a different QR code. A QR code that redirects any donations to their own accounts, and exploits the trustworthiness of the person or organisation behind the campaign.
The primary dilemma is how hard it is for humans to notice differences between QR codes. Or understanding any of their content, really. And from what I've seen, there is a growing, misplaced trust in QR codes that makes many people ready to scan pretty much anything without a second thought.
Scanning a QR code really doesn't encourage people to double-check they end up in the right place. It encourages speed and not thinking too much.
If people scan a QR code on a graphic that looks like the real deal and end up on a donation page, what would make them not donate? There would have to be a considerable amount of due diligence before suspicions arise. And are people encouraged by campaign owners to be careful and look for signs of fraud? Not often.
How does it work?
It's quite simple. Bad actors download your graphic and insert their own QR code on top of yours. Their QR code leads to a different payment gateway but is designed to seemingly support the same goal. It's virtually impossible for anyone to spot the difference in the graphic. And most people aren't even looking for a difference.
Then the bad actors publish their manipulated graphic and use words that are in support of your campaign, making it seem like they are boosting and advocating for your campaign. It's hard not to be flattered by this. You may even like or repost their kind words.

Con artists will likely use their graphic in own posts on different accounts but also when commenting or reposting, trying to spread it as much as possible. Their best hope is for people to mistakenly use their version of the graphic as much as possible. Even if it's just a few people, it's a cheap scam to pull off.
Social media scenario
Imagine you are a campaign owner who has produced a graphic asking for donations, encouraging people to scan a QR code. You see someone on social media posting your graphics and encouraging to donate to your efforts. It's likely full of praise for you and your mission. It makes you happy and proud, so you republish it and thank them.
Now what if I told you that person was not actually posting your graphic, but a manipulated one with their own QR code in place of yours. So now you've repeated their version of the image to all of your own followers, essentially endorsing it and helping them in their deceptive efforts.
Recommendations
- If you are a campaign manager,
- don't rely on QR codes in graphics on social media,
- print out official links with official, recognizable domain names,
- use a landing page on your official website with a link to the payment gateway, rather than link directly to a payment gateway,
- on social media: post the link to your own landing page, not QR codes.
- If you are a donor,
- avoid scanning QR codes when you are not extremely confident that it will take you to an address that you know of beforehand and can double-check,
- ask for the official link – the full web address – to the page where donations are to be made, and double-check it before sending your money,
- or alternatively, head over to the organisation's web page to find the campaign and donation link on the domain you trust.
- Whoever you are,
- don't repost graphics from accounts that are not affiliated with the campaign owner,
- find the official channel and republish their posts about the campaign,
- and alert campaign owners of these risks if they don't seem to be aware.
Remember, web addresses on campaign material can also be edited. This is usually more obviously found out, and especially by campaign owners themselves who can see that the address is the wrong one. That's why criminals love QR codes. But sometimes criminals are also able to register domain names that are very similar to the original ones, requiring a more close look.
All this underscores the need for a recognizable domain name for official communication. Do take this seriously to avoid publishing material that can be manipulated to funnel money to illegitimate people and organisations.
Also read
I wrote this post on the Sunday night before my open heart surgery took place in the morning of August 19.
The most common question I get is ”how are you feeling?”, but it is also the most difficult to answer, at least in a way that gives the emotions justice. Saying there are many emotions also feels wrong, because they are all forged into each other with no conflict, without struggling for space. Together they form this whole new feeling. There should be a word for harboring many emotions at the same time, without being particularly roused or conflicted.
”How are you feeling Per?”
”Interwoven, for sure.”
What overwhelms me is the thought of letting go. The idea of surrendering so helplessly to people who just want the best for me. I also feel this huge indescribable gratitude for strangers who devote their professional life to persistently repairing broken bodies. And I know now how necessary my operation is.
There is of course this inherent feeling of unrest in the need to completely surrender control. An unwillingness to be as weak as I will be for many months. A concern in the uncertainty, of course, of how it will play out. And how my life changes after this.
So I focus on communication, on logistics, on social interplay and design. The things I know. Everything I'm going through becomes part of what my industry calls a user journey. Where do things move quickly and where do they move fast. Where in the process am I frustrated, grateful or surprised.
When do I dare embrace the process.
The placement of the surgeon's tools is a design solution
I want to take this opportunity to tell you about one of my role models. Her name is Lillian Möller Gilbreth, and she lived during the years 1878 to 1972. The legacy of Lillian Gilbreth is not talked about enough in the business world, including my own industry.
As it turns out Gilbreth also happens to have had a great influence, alongside her husband, over the working methods of all surgeons.
Lillian M. Gilbreth worked with husband Frank in an area they called motion studies. You could say this was a development of the contemporary Frederick Winslow Taylor's time studies. They observed movements in physical labor with an intent to eliminate movements and make the work more streamlined. They wanted to distinguish themselves from Taylor by shedding light on workers' well-being, and weed out motion that led to physical strain and injury, rather than merely emphasising the profit margins of manufacturers and builders.
Frank loved technology, and pioneered using a film camera in their joint consulting firm. The camera became an important tool in observations of workers' movements. And this also means there are preserved moving images from both family life and daily work, and in this old clip from Frank Gilbreth's own film camera you get an understanding of how they performed their studies:
Note that there is always a 'clock' visible in the frame, a microchronometer, to help track the time required for the various stages of work. At this time, Frank used a hand cranked 35mm camera, and the speed of the resulting video of course varied. The only way to accurately perceive how much time passes is that clock.
Unfortunately, or perhaps fortunately, there are no moving images from an OR (operating room) among all the old clips. However, the work they did to streamline the work of surgeons was very successful.
Lillian and Frank systematically divided movements, or work steps, into 18 different elements, for example: Search, find, grasp, hold, plan, rest, avoidable delay and unavoidable delay.
The compilation of all these movements was called Therbligs. This inventive word is simply their surname backwards, save the th for the sake of readability. And the list of Therbligs appeared as follows, where each therblig not only had its own name, but also a symbol, its own color and a shorthand abbreviation (the abbreviation is not visible in the picture below).

By filming, and in detail documenting, surgical procedures with this method, Lillian and Frank were able to discover which steps contributed to time waste, injurious motion, and other forms of frustration. In my profession today this would be called user journeys, a method of mapping out where in a process a user encounters obstacles with the intent of improving important and poorly functioning stages of the experience.
The Gilbreths discovered how surgeons spent more time looking for the right instrument than performing the operation itself. One key point of advice in their report was for the surgeon to have a designated assistant responsible for the placement of tools and always ready to hand over the right tool. And you've likely seen the result time and time again on TV today: a surgeon shouts "Scalpel!", and immediately is handed one.
Lillian and Frank wrote several books together about their work, but it was only Frank's name that ended up on the book covers. Their publisher worried that the books would lose trustworthiness with a female co-author. This is where I like to point out to readers that Lillian had a doctorate in applied psychology, while Frank never attended a day of university.
Although they worked closely together for a long time, Lillian had a considerable solo career. Frank died in 1924, of heart failure, at the age of 55. And Lillian lived on for 48 years after that, improving a variety of workplace and household activities with the method she constantly improved by taking into account, among other things, physical exhaustion and mental well-being. She was the first woman inducted into the Society of Industrial Engineers, and has been awarded countless awards for her achievements. She has also been called the world's first industrial psychologist.
I observe and take notes
As I now enter a period of hospital stay, I allow myself to be inspired by the Gilbreths' work with motion studies and Lillian's razor-sharp focus on human well-being. They showed how it was possible to improve both working life and everyday tasks in a way that benefits individuals, organizations and society.
When I was registered at Karolinska University Hospital on the Thursday ahead of surgery, I of course had opinions on the survey I answered as part of the process, and spoke up about the wordings and layout of the procedure appointment letter . The Nurse Specialist I met with picked up on all this straight away and asked if I would want to sit down for an interview about my experiences after surgery. Of course! Could I suggest changes to the design of the appointment letter? Yay!
And what crossed my mind was that I immediately wanted to try out new design solutions for the letters and information in both digital and paper versions. I already have sketches in my head for changes in workflows and new support information, things that would make it easier for both patients and nurses, and create a sense of safety and comfort.
I'm identifying therblig moments in communicative processes!
So that's where I'm trying to be at in my head right now. I'll focus on what I'm good at and I'll let the care specialists focus on what they are good at. That feels like an okay deal.
And all at once it's easier to embrace the process.

Curious about what they did to my heart?
My aortic valve has been replaced with a prosthetic. The On-X Aortic Heart Valve looks like this:

I also had an interposition graft placed in the ascending aorta. I won't shock you with pictures but there are plenty online. 😉
I'm honestly blown away by the tech, how it's all possible and by the people working on making it all happen.
Take care ❤️ I'll be attending to my recuperation for a while now, but I'll be back,
Per
Mattel also organized play sessions for children with visual impairments as part of product development.
]]>When you read the news that Mattel is launching a blind Barbie with a white cane, note that the doll was developed with organizations and people who are experts in, and themselves have, visual impairments.
Mattel also organized play sessions for children with visual impairments as part of product development. Hence the news is also about attention to detail, right down to how the box is opened.
- The clothes are made of materials with a high sensory and tactile experience (a pink satin blouse and pleated skirt).
- To easily change clothes, the blouse has a high-contrast fastening with a hook and the skirt has an elastic waistband.
- The elbow joints have been designed so that the doll can use the cane in a way that is perceived as comfortable.
- Barbie in Braille on the box is strategically placed according to advice from people with low vision.
- To make it easier for people with visual impairments to open the box on their own, it has been supplemented with a new pull-out tab.
Note that high-contrast details are about making it easier to handle the doll for anyone with sight loss.
And the details on the box (the placement of the braille and the pull-out tab) will now be implemented on all Barbie boxes in the Fashionista series. It highlights how a focus on accessibility contributes to design that helps everyone.
I am aware that Mattel and Barbie are not without their controversy as a phenomenon, and have rightly been brought into question many times. But I do appreciate the process and attention to inclusive design they demonstrate in this case, and that many more organizations can learn from.
References
















