This is a part of a sample chapter from my latest book, “Tactical Wireless Security” converted to article form. The book was originally created for a class to teach basic WiFi and SDR skills to Special Forces troops. The book is available now on Amazon.
DragonOS Introduction
DragonOS is a Linux-based system designed specifically for RF analysis and wireless security testing. What sets Dragon OS apart is its focus on critical RF tools, especially for tactical use. It comes pre-loaded with software like GQRX for spectrum monitoring, GNU Radio for signal processing, and tools for cellular network analysis. Basically, it’s built to handle a wide range of SIGINT and wireless recon missions right out of the box.
Dragon OS is also available for Raspberry Pi, making it ideal for field operations where portability is key. Whether you’re using an RTL-SDR or more advanced devices like BladeRF or USRP, Dragon OS has you covered. We will be using it because it’s tailor-made for tactical RF ops—monitoring peer or near peer signals, mapping networks, and securing communications.
What is Dragon OS?
- A free, Linux-based OS for RF analysis and wireless security testing
Key Features:
- Pre-installed and configured software for SDR and wireless security
- Built for spectrum monitoring, signal analysis, and recon
Why Use Dragon OS?
- Tailored for tactical RF operations
- Efficient for field use on Raspberry Pi
- Flexible, powerful tools for signal interception and analysis.
Tools in Dragon OS:
- GQRX, GNU Radio, SDRangel, OpenLTE, and more
- Supports RTL-SDR, HackRF, BladeRF, and more!
Dragon OS makes SDR based scanning and attacks extremely simple. Dragon OS comes pre-configured to work with most popular SDR devices. Simply boot Dragon OS, insert your HackRF, BladeRF or your favorite RTL-SDR and run one of the numerous pre-installed tools. It really is that simple.
Installing DragonOS
Dragon OS is available from the OS website in two formats, Raspberry Pi and X86-64. Simply pick the version you want and download it.
DragonOS website
Installing Dragon OS is extremely easy on a Raspberry Pi. Just download the Raspberry Pi image from the Dragon OS website (https://cemaxecuter.com/). Write it to a Pi compatible memory card using a tool like balenaEtcher. Insert it into your Pi, attach peripherals, and lastly power. It will boot up to the Dragon OS Desktop. You could also download the x86-64 .iso write it to removeable media and boot it, or use it in VMWare – Create a new Virtual Machine, setting the ISO as the boot drive, and then after it boots, running through the install routine.
The default password is “dragon”.

Dragon contains a lot of preinstalled tools for us to use. All are configured to run out of the box. Just boot up Dragon, insert your SDR adapter, start the tool you want, select your SDR from the tool configuration and you are off to the races.
DragonOS – A Quick Walk Through
I know Dragon is new to a lot of you, so let’s do a quick walk through. After login, you will be at the Dragon main desktop. The bird in the bottom left is the menu button, you also have 4 desktops you can use, a file manager, browser, console, and a “show desktop” button.

Clicking the menu button offers a standard Linux system menu.

Many of the RF spectrum scanning tools are under the menu option “Hamradio”. Many of the transmitting tools can be found under the “other” menu.
To logout and shutdown Dragon OS, just use the “Leave” menu option.
If you are familiar with Debian Linux, you will feel right at home. In fact, Kali Linux is also Debian based, and all the tools we covered in Kali could be used in Dragon as well. And some are actually already installed!
Enough introduction let’s get some hands-on time! In my book, I cover basic usage of several of the RF Scanning tools first, and then the tools to capture and manipulate signals in the next section.
The creator of Dragon OS has an extensive YouTube library of almost three hundred Dragon OS “How-To” videos. They cover literally everything from installing Dragon to using some of the more advanced tools and techniques like the Cell Tower tools and tracking down drones with his own hardware and software creation, the “War Dragon”.
I highly suggest that you check out his YouTube channel:
https://www.youtube.com/@cemaxecuter7783
Before I wrap up this article, I want to cover one tool in Dragon that is very good for scanning WiFi and Bluetooth – Sparrow WiFi.
WiFi Scanning with Sparow WiFi
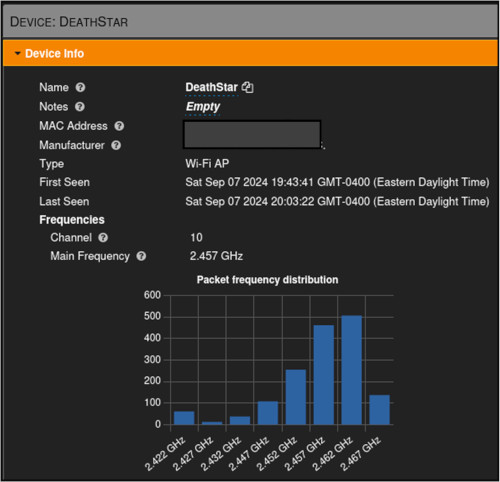
Sparrow WiFi is a quick and easy to use WiFi scanning tool that displays all WiFi networks detected and shows you a bandwidth map, so you can see, at a glance, what WiFi networks are using what channel bandwidth. Attach your WiFi USB adapter and a Bluetooth adapter if you have one.
- From the main dragon menu, select, “Other > Sparrow WiFi”
- Then type, “sudo ./sparrow-wifi.py”
Click the scan button, this will begin the WiFi Scan. Next, click “Bluetooth” from the top menu and click “start scan”. This will detect both WiFi and Bluetooth Devices.
That’s it, with just a couple clicks you can have a good layout of the WiFi and Bluetooth space around you! I personally really like this tool and use it a lot when I do use Dragon OS. It’s quick, easy to use and seems to show a lot more Bluetooth devices than other tools that I have used.
Conclusion
In this article, we introduced DragonOS. DragonOS is a great operating system that is totally pre-configured to use SDR. We also looked at the basic layout of the menu system and looked at one of the popular WiFi tools in Dragon.
In my latest book, “Tactical Wireless Security”, I cover performing Wireless security testing with some of the most popular WiFi tools on Kali Linux. I then switch to DragonOS and have two sections on using it – tools and techniques for Spectrum Scanning and Analysis, and a section on the transmission tools, learning techniques like signal modification and even jamming.
The book covers using hardware tools like the HackRF One, and covers numerous popular SDR software tools, like GNU Radio Companion (GRC), Universal Radio Hacker (URH), and SDRAngel.
Each of these sections is written in a hands on, step by step, learn by doing style that all my books are written in.
Check out “Tactical Wireless Security” on Amazon.com
Resources & References
- RTL-SDR, “About RTL-SDR” – https://www.rtl-sdr.com/about-rtl-sdr/
- Dragon OS Creator’s YouTube Channel – https://www.youtube.com/@cemaxecuter7783