Inspiration
Misconfigured firewalls are a major threat for small businesses without full-time security teams.
- 50% of small and midsize businesses (SMBs) rely on firewalls as their primary security control.
- However 82% of breaches in cloud and on-prem environments involve misconfigurations or human error (Verizon DBIR).
- Over 60% of SMBs that suffer a cyberattack go out of business within six months (U.S. National Cyber Security Alliance).
I imagined a nonprofit discovering an exposed RDP port too late, or a small business overwhelmed by vendor-specific firewall documentation. I built FireWize to close that gap and democratize security. It's an agentic AI management system that helps everyday orgs harden their firewalls without needing a security team or having a technical background.
What it does
FireWize autonomously analyzes and remediates firewall configurations through an agentic workflow. It:
- Normalizes diverse firewall exports (Cisco ASA CLI, iptables JSON, SonicWall, cloud SGs)
- Runs static scans to flag high-risk patterns (open SSH/RDP, broad NAT, DNS tunneling)
- Uses a Groq-powered LLM within an Orkes workflow to generate summaries, label severity, and produce vendor-specific CLI fixes
- Dynamically orchestrates its own tasks using MCP (Model Context Protocol), letting the AI decide which steps to take next, when to branch, and when to ask the user for input
- Presents everything in a user-friendly UI with charts, logs, remediation suggestions, and a chat interface to answer follow-up questions
How I built it
This is how I structured the system:
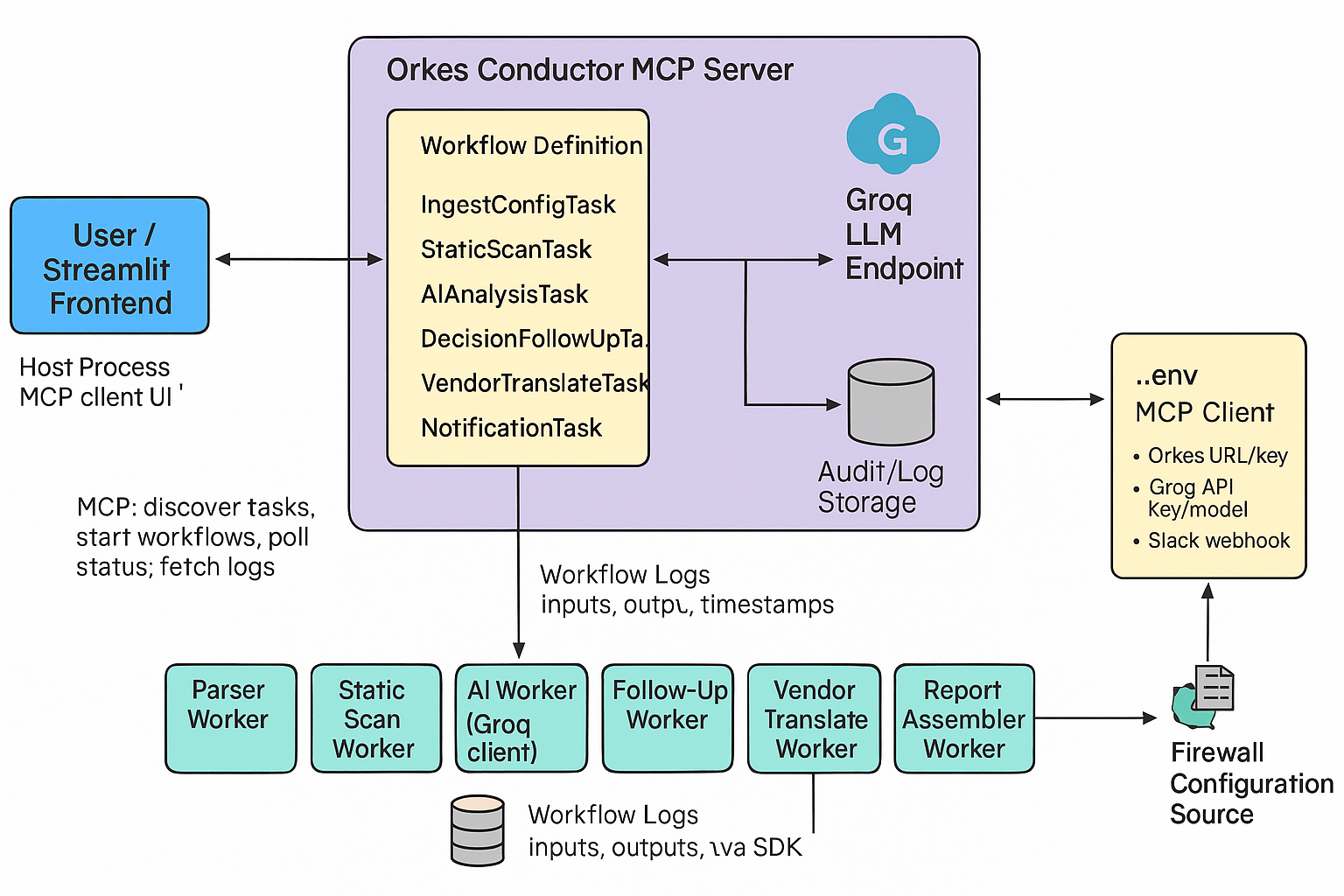
- Parsing Modules: Regex- and JSON-based parsers for each firewall type, producing a normalized rule format.
- Static Scan Engine: Flags insecure patterns using encoded best practices and known vulnerability heuristics.
- LLM Integration (Groq): Wraps parsed rules and scan results into a structured prompt; Groq returns structured JSON with risks and remediations near-instantly.
- Orchestration (Orkes + MCP):
- Orkes runs the backend workflows as tasks (e.g., parse, scan, analyze, translate, finalize).
- MCP lets the LLM drive the workflow: it chooses which tasks to invoke, when to wait, how to branch, and when to request follow-up from the user.
- This creates an agentic system where the LLM controls the sequence to respond proactively to threats.
- Streamlit Frontend: Handles file uploads, progress display, log streaming, and final results. Also includes the remediation view and a chatbot allowing you to interact with the context through Groq.
- Notifier: Optional Slack integration to send reports or alert summaries from the workflow.
Challenges I ran into
- Parsing variability: CLI vs JSON vs cloud exports required a lot of normalization logic to avoid edge case bugs.
- Learning agent orchestration: MCP and Orkes were new to me and it took time to understand how to let the AI control the flow.
- Consistent LLM outputs: Had to carefully design prompts so Groq would return clean, structured JSON every time.
Accomplishments that I'm proud of
- Built an MVP that solves a creative, and real problem
- Delivered an agent-driven workflow that mimics how a real AI engineer might manage firewall hardening
- Created a full audit-traceable Orkes pipeline with branching based on LLM results
- Built a polished, interactive UI that includes summaries, charts, simulated remediation, and a contextual chatbot
What I learned
- How to build agentic systems with MCP where the AI is in control of backend decisions, not just passively responding
- Prompt engineering for structured, reliable LLM outputs
- Parsing real-world firewall configs and identifying unsafe patterns with static logic to start
- Using Groq’s API
- Designing a UX that balances security detail with clarity + usability
What’s next for FireWize
- Live firewall integration Add SSH and API connectivity so FireWize can apply fixes in real infrastructure, not just simulate them.
- Compliance mapping Ingest frameworks like PCI-DSS or HIPAA, and flag how current configs meet or violate them, including remediation suggestions.
- Scheduled scans & reporting Let orgs track their firewall health over time and visualize exposure trends.
- Wider support Add more parsers for common SMB firewalls like Ubiquiti, Fortinet, and cloud platforms.







Log in or sign up for Devpost to join the conversation.