-
-

SafeStack Landing Page-1
-

SafeStack Landing Page-2
-

SafeStack Landing Page-3
-

SafeStack Landing Page-4
-

Login Page
-

Repository Dashboard
-

Vulnerabilities detected in the repository
-

GitHub PR generated by the application and summarised by Gemini 2.5 Flash LLM
-

GitHub PR generated by the application with the suggested upgrades to resolve CVEs
-

CVE search based on TiDB vector search
-

CVE search results based on TiDB vector search
-

Jira integration settings
-

Jira tickets raised through the Jira integration
-

Slack integration setings
-

Slack notifications sent to the teams for detected vulnerabilities and GitHub PR raised for fixes
-

CVEs stored in TiDB for running full text search and vector search
💡Inspiration
Modern applications rely heavily on open-source dependencies, but securing them is a constant challenge. Developers spend hours tracking CVEs, upgrading packages, and ensuring compatibility. We wanted to create a tool that automates this workflow, allowing developers to focus on building instead of firefighting vulnerabilities.
The idea originated from my recent project at work, where I had to upgrade the Spring version, Java version, and other dependencies to resolve CVEs for InfoSec compliance. The difficulties I faced during the project inspired me to build an application that can automate all the manual labor I put into upgrading the dependencies and securing services, while ensuring the upgrades do not introduce any bugs or regressions.
💻 What it does
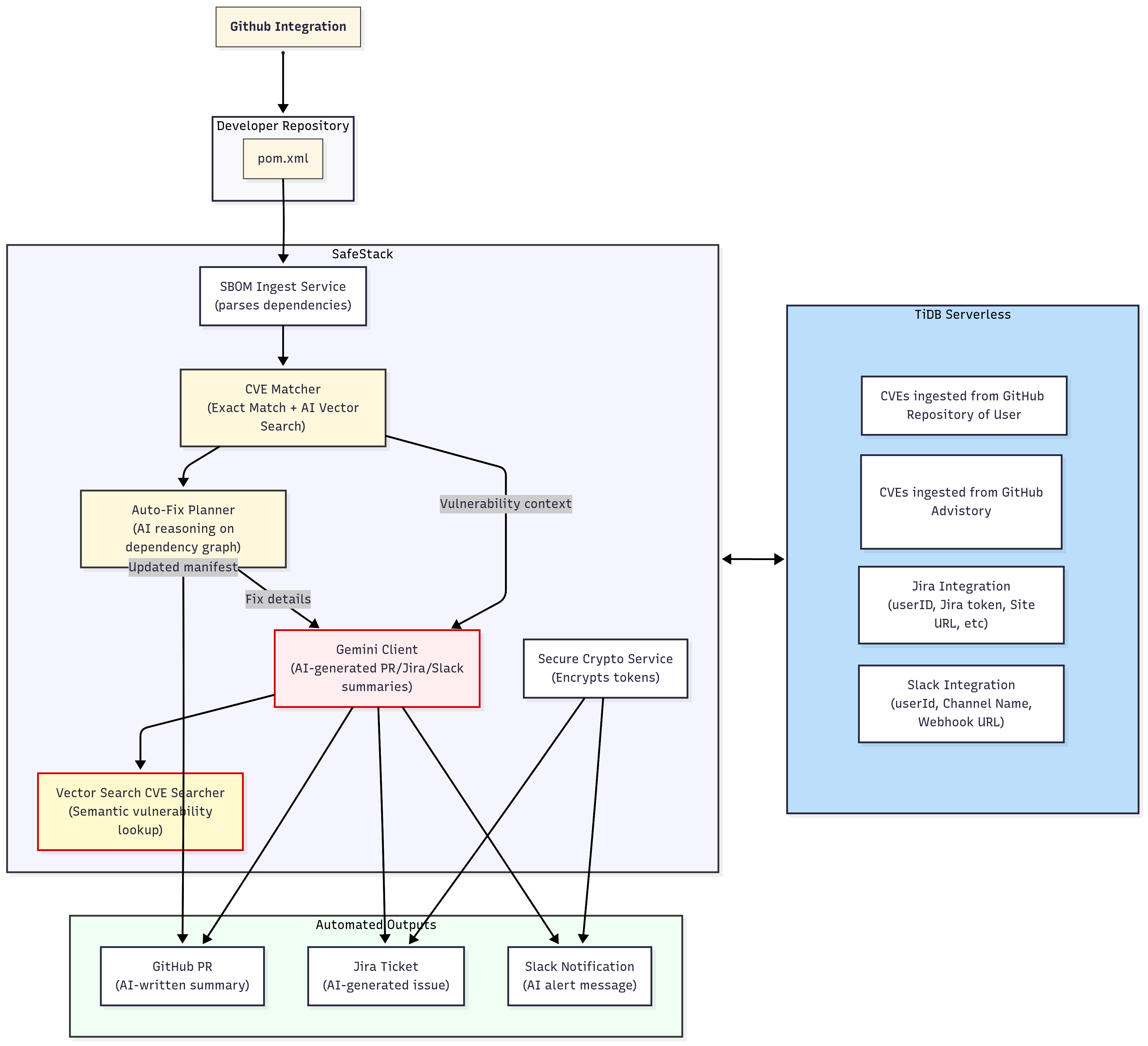
SafeStack scans your repositories for Maven-based dependencies, detects vulnerabilities (CVEs), and suggests safe fixes. It automatically:
- Parses SBOMs from pom.xml
- Matches dependencies against known CVEs using full text and vector search in TiDB
- Generates and applies safe upgrade plans
- Raises GitHub pull requests with fixed pom.xml files
- Creates Jira issues for tracking and sends Slack alerts for team visibility
🛠 How we built it
- Spring Boot backend for dependency parsing, CVE matching, and integrations
- TiDB for storing CVEs, SBOMs, integration metadata, and powering semantic vector search for vulnerabilities
- GitHub OAuth integration to fetch repos and raise automated PRs
- Gemini 2.5 Flash LLM for generating GitHub PR summaries, Jira ticket content, and Slack notifications.
- Slack & Jira APIs to push actionable alerts and track vulnerability fixes
📊 Flow diagram
⚠️ Challenges we ran into
- Mapping CVEs to the correct dependency/package version without mismatches
- Preventing duplicate scans when multiple requests were fired simultaneously
- Writing the frontend for the application as we are a team of backend developer and UI designer with minimal knowledge of frontend tech stacks
🏆 Accomplishments that we’re proud of
- Fully functional web application with end-to-end automated workflow: detect → fix → PR → notify
- Seamless GitHub, Jira, and Slack integration
- NLP-powered search for CVEs in natural language (“Show me Tomcat CVEs”)
📚 What we learned
- How to leverage TiDB’s vector search to power vulnerability detection
- The importance of package-level accuracy when suggesting fixes
- Best practices in handling OAuth flows for GitHub integration
- Coordinating multiple integrations (GitHub, Slack, Jira) in a single workflow
🌱 What’s next for SafeStack
- Expand support beyond Maven to NPM, Go, Python, and Gradle dependencies
- Smart transitive dependency resolution
- Integration with CI/CD systems for continuous security checks
- Deeper AI assistance for generating context-aware fixes
- Extending the application to scan projects stored on GitLab, BitBucket, etc.
- Enhancing the application to be an enterprise grade tool
Log in or sign up for Devpost to join the conversation.