The post Faraday v5.19: Removing Friction from Vulnerability Management at Scale appeared first on Faraday.
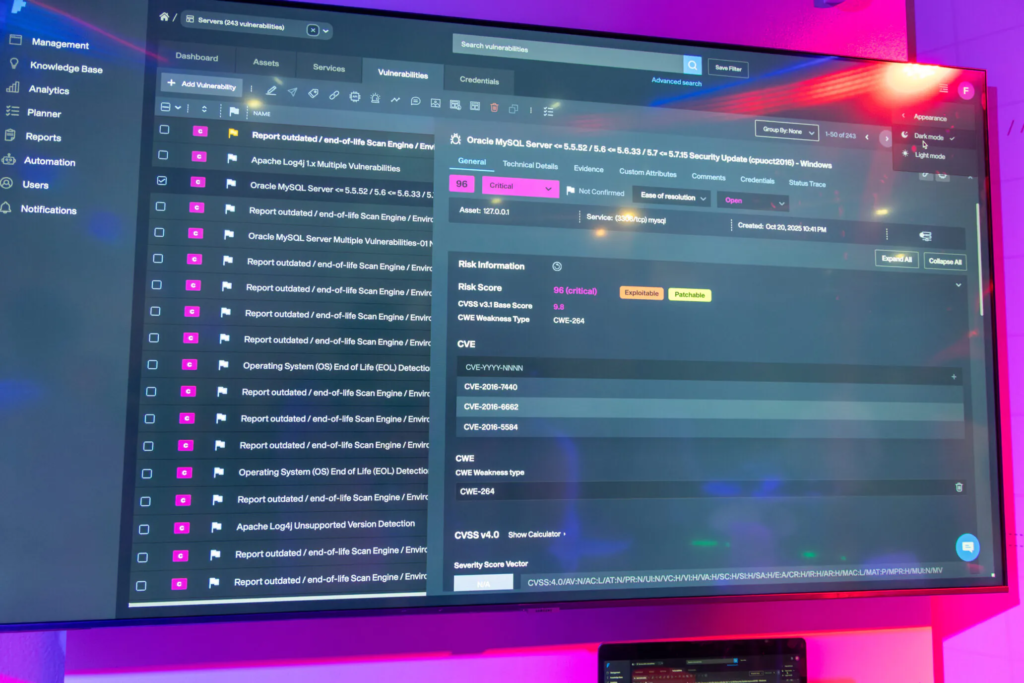
]]>Managing vulnerabilities at scale is rarely about finding issues.
For most security teams, the real burden starts after detection: handling massive volumes of vulnerability data, coordinating multiple scanners and tools, maintaining context across attack surfaces, and turning technical findings into decisions the business can act on.
With Faraday v5.19, we focused on exactly that reality.
Rather than introducing flashy features, this release focuses on improving performance and removing friction from the daily work of cybersecurity analysts, red teams, and hackers who manage vulnerabilities across complex attack surfaces.
Let’s take a look at what’s new
Highlights
Better context without extra clicks
Agents that scale with real-world data
Performance that respects your time
Better Context Without Extra Clicks
Enhanced Dashboard – Workspace Details
In large environments, analysts often need context before taking action, even when they are not actively working inside a workspace.
With this release, analysts now have immediate visibility of key workspace information directly from the dashboard through the new Workspace Details panel.
This panel allows teams to quickly review important workspace attributes such as scope, ownership, and engagement details without needing to enter the workspace first. The panel can be expanded for full context or collapsed to save dashboard space.
Agents That Scale with Real-World Data
Updated Agent Configuration
Modern vulnerability scanners such as Nessus generate large payloads of vulnerability data.
Until now, default agent parameter limits could be too conservative for real-world environments. In Faraday v5.19, these limits were increased to better match the typical output size of modern security scanners.
The result:
- Fewer failed agent runs
- Less manual reconfiguration
- More reliable ingestion of large scan results
Also the GVM OpenVAS agent was updated to support new socket locations, ensuring compatibility with updated deployments and environments.
This keeps Faraday aligned with upstream changes while preventing users from needing custom fixes or workarounds.
Performance That Respects Your Time
Faraday v5.19 also introduces improvements designed to ensure the platform remains responsive even in large environments managing thousands of vulnerabilities.
Agent configuration updates improve how security data is ingested from scanners, while improvements to the SonarQube agent provide clearer execution states and more accurate vulnerability counts when analyzing source code security results.
We also improved integrations with several development security tools. Updates to the Dependabot, CodeQL, and GitHub Secrets agents ensure that scan results spanning multiple pages are correctly processed and ingested into Faraday.
In addition, performance improvements such as faster deletion of large workspaces help security teams maintain clean environments without delays, even when dealing with thousands of vulnerabilities.
Faraday v5.19 focuses on making vulnerability management faster, more reliable, and easier to operate at scale.
The result is simple: security teams spend less time troubleshooting tooling and more time prioritizing risk, managing vulnerabilities, and delivering meaningful security insights to their organization.
Your feedback continues to shape our roadmap. If you have questions or suggestions, contact us at [email protected]
See you in the next release 
Documentation:
Homepage
Documentation
Download
Issue tracker and feedback
Frequently Asked Questions
Twitter
The post Faraday v5.19: Removing Friction from Vulnerability Management at Scale appeared first on Faraday.
]]>The post Faraday v5.18 Release – Performance Improvements, Better Integrations, and More Control appeared first on Faraday.
]]>Faraday v5.18 focuses on improving performance at scale, integration control, and overall user experience, especially for teams managing large workspaces, complex vulnerability data, and multiple security tools.
This release is driven by direct customer feedback and real-world usage scenarios, delivering improvements that reduce friction in day-to-day vulnerability management and remediation workflows.
Let’s take a look at what’s new
Highlights
Improved Stability and Performance at Scale
Unlink issue trackers from vulnerabilities (Jira, GitLab, ServiceNow)
Plugin updates driven by customer usage (Nuclei, Tenable IO, Burp)
Improved Stability and Performance at Scale
This release introduces a new configuration option designed to protect the platform from oversize tasks that could impact system stability. Large imports, scans, or integrations can generate tasks that exceed queue limits and cause processing failures.
With Faraday v5.18, task size is now validated before entering processing queues, and oversize messages are blocked early, preventing interruptions and ensuring reliable workflow execution. Configuration details:
In addition, we addressed a critical performance issue affecting very large workspaces, including environments with hundreds of thousands of vulnerabilities. Which caused noticeable delays, impacting analyst productivity.
These improvements directly benefit organizations security teams managing large attack surfaces, running large-scale vulnerability scans and complex vulnerability datasets reducing delays.
Tailored Control Over Issue Tracker Integrations
Faraday now allows administrators to unlink issue trackers from vulnerabilities, including Jira, GitLab, and ServiceNow.

This feature was implemented in response to a specific customer request and is especially useful when Integrations need to be cleaned up without losing vulnerability context.
Plugin Updates Driven by Real Customer Usage

These plugin updates reflect how Faraday is actually used in real-world vulnerability management workflows. Based on direct customer feedback and integration challenges, we’ve improved accuracy, stability, and compatibility across the tools security teams rely on every day.
Nuclei Integration
- Full support for Nuclei JSON v3.x
- Correct mapping of critical fields such as impact and remediation
- Ensures accurate vulnerability data ingestion from updated Nuclei scans
Tenable IO Integration
- Improved alignment with Tenable Nessus
- Reduces inconsistencies and duplicate findings when using multiple Tenable sources
- Simplifies vulnerability management for teams using both tools together
Burp Integration
- Fixed stability issues when importing XML reports
- Improved handling of large base64-encoded HTTP responses
Faraday v5.18 strengthens the platform’s ability to support modern vulnerability management programs, especially in environments with large datasets, multiple integrations, and complex remediation workflows.
Your feedback continues to shape our roadmap. If you have questions or suggestions, contact us at [email protected]
See you in the next release 
Documentation:
Homepage
Documentation
Download
Issue tracker and feedback
Frequently Asked Questions
Twitter
The post Faraday v5.18 Release – Performance Improvements, Better Integrations, and More Control appeared first on Faraday.
]]>The post Our team’s vulnerabilities disclosures 2024 appeared first on Faraday.
]]>Throughout 2024, our researchers reported multiple security issues affecting DrayTek Vigor routers. These findings were responsibly disclosed and assigned CVEs where applicable, contributing to improved security for vendors and users alike.
The vulnerabilities below were identified through manual analysis and security research, covering authentication mechanisms, cryptographic implementations, and core network services.
CVE-2024-41334: Missing SSL certificate validation in DrayTek routers, allowing attackers to upload crafted APPE modules from non-official servers, leading to arbitrary code execution.
CVE-2024-41335: Non-constant time password comparison in DrayTek routers, allowing attackers to potentially obtain sensitive information via timing attacks.
CVE-2024-41336: Insecure password storage in DrayTek routers, where passwords are stored in plaintext.
Predictable 2FA code generation: Several DrayTek Vigor routers generate the two-step authentication code in a predictable way, allowing attackers to bypass this security measure. (CVE denied)
CVE-2024-41338: NULL pointer dereference in the DHCP server of several DrayTek devices, allowing attackers to cause a Denial of Service (DoS) via a crafted DHCP request.
CVE-2024-41339: An issue in the CGI configuration upload endpoint of several DrayTek devices allows attackers to upload a crafted kernel module, leading to arbitrary code execution.
CVE-2024-41340: An issue in several DrayTek devices allows attackers to upload crafted APP Enforcement modules via the signature update endpoint, leading to arbitrary code execution.
CVE-2024-51138: A stack-based buffer overflow in the TR-069 STUN server of DrayTek routers allows a remote attacker to execute arbitrary code with elevated privileges.
CVE-2024-51139: Integer overflow in the CGI POST request handling of DrayTek routers allows a remote attacker to execute arbitrary code via a crafted Content-Length header.
cJSON buffer overflow: Buffer overflow vulnerability affecting Tuya smart devices. CVE assignment pending.
CVE-2026-21639: Stack-based buffer overflow in the airMAX wireless protocol allows a malicious actor within Wi-Fi range to achieve remote code execution on affected Ubiquiti devices.
CVE-2026-21638: Stack-based buffer overflow in the airMAX wireless protocol allows a malicious actor within Wi-Fi range to achieve remote code execution on affected Ubiquiti devices.
The post Our team’s vulnerabilities disclosures 2024 appeared first on Faraday.
]]>The post Ekoparty 2025: otra edición, nuevas conexiones y la misma pasión por hackear appeared first on Faraday.
]]>Nos preparamos con la misma energía de siempre: para reencontrarnos con la comunidad, compartir lo que investigamos, aprender de otros y, claro… hackear un poco.
Armamos nuestro stand, recibimos clientes, amigos y curiosos, y creamos espacios donde se puede hablar de ciberseguridad, compartir un café y dejar que las ideas fluyan.
Pwnearon nuestro CTF, y nos animamos a participar en más de un desafío.
Aprovechamos cada charla, cada pausa y cada after como una oportunidad para conectar.
Antes de que abriera oficialmente la Eko, comenzamos con lo que más nos gusta: ensuciarnos las manos.
En nuestro training “Hands-on Vulnerability Research”, compartimos metodologías y herramientas para investigar vulnerabilidades reales, desde la exploración inicial hasta la explotación controlada.
Durante dos días, participantes de toda la región trabajaron junto a nuestro equipo, analizando código, descubriendo fallas y aprendiendo cómo transformar la búsqueda de bugs en conocimiento aplicable.
Como otros año, llevamos al escenario el resultado de meses de investigación y desarrollo.
Nuestro equipo de Research tuvo la oportunidad de cerrar el año compartiendo los hallazgos y aprendizajes más relevantes.
“The Missing Link: Draytek’s New RCEs Complete the Chain”, Gaston Aznarez & Octavio Ogianatiempo
Una charla imperdible, desde el hallazgo de la vulnerabilidad hasta su explotación, con demostraciones y la cadena completa de extremo a extremo.
También exploró su vínculo con los incidentes masivos de reinicio de dispositivos Draytek en marzo de 2025, sugiriendo que la explotación real podría ya estar ocurriendo.
Nos recordó la importancia de la transparencia en la investigación de seguridad embebida y el impacto que puede tener compartir conocimiento con la comunidad.
“Beyond the Scan: Automatizando la gestión de vulnerabilidades” – Gabriel Franco, Head of Security
Un recorrido sobre cómo la automatización puede convertir findings en decisiones más rápidas y efectivas, integrando tecnología y talento humano.
Aprendimos cómo un equipo de seguridad puede automatizar diferentes fases del monitoreo continuo apoyándose en herramientas públicas e inteligencia artificial: desde el reconocimiento hasta el análisis de vulnerabilidades.
Incluso con equipos reducidos, descubrimos que es posible construir un modelo de Continuous Security eficiente, combinando herramientas open source con automatización inteligente.



Durante esta edición presentamos oficialmente Doggie, un dispositivo open-source diseñado para experimentar de forma segura con el sistema CAN Bus de los autos modernos.
Doggie permite conectar, observar y entender cómo se comunican los distintos módulos del vehículo, abriendo la puerta a investigaciones más profundas sobre ciberseguridad automotriz.
El proyecto —nacido del trabajo de nuestro equipo de investigación— está disponible para toda la comunidad en GitHub, con guías, documentación y tutoriales.
Durante la Eko, muchos asistentes se llevaron su primer Doggie, lo probaron en vivo en el Car Hacking Village y se sumaron a la comunidad que ya está contribuyendo con ideas y mejoras.


Más allá del código, hubo encuentros, anécdotas y risas: un cartel callejero con vida propia, un after “intervenido al estilo Faraday”, y almuerzos con amigos y CISOs que acompañan nuestra evolución año tras año.
Cada Eko nos impulsa a seguir creciendo.
A conectar investigación, tecnología y comunidad.
A demostrar que la seguridad no se trata solo de proteger, sino también de entender, experimentar y compartir.
Gracias a todos los que pasaron por el stand, participaron, hackearon, charlaron o simplemente se acercaron a saludar.
Nos vemos en la próxima Eko, con más research, más ideas y más ganas de seguir hackeando juntos.
Soluciones en Ciberseguridad ofensiva, tecnología y talento. Habla con nuestros expertos.





Ekoparty 2025: another edition, new connections, and the same passion for hacking
Every year, Ekoparty reminds us why we love what we do.
We showed up with the same energy as always — ready to reconnect with the community, share our research, learn from others, and of course… do some hacking.
We set up our booth, welcomed clients, friends, and curious visitors, and created that signature Faraday space where security, coffee, and ideas flow naturally.
Our CTF got pwned, and we joined more than one challenge ourselves.
We made the most of every talk, every pause, and every after-party as an opportunity to connect.






Before Ekoparty officially kicked off, we started with what we love most: getting our hands dirty. In our “Hands-on Vulnerability Research” training, we shared methodologies and tools for researching real-world vulnerabilities — from initial exploration to controlled exploitation.
Over two days, participants from across the region worked side by side with our team, analyzing code, finding bugs, and learning how to turn vulnerability research into practical knowledge.
As every year, we took the stage to share the results of months of research and development.
Our Research team had the chance to close the year by presenting their latest findings and insights.
“The Missing Link: Draytek’s New RCEs Complete the Chain”
An outstanding talk that walked through the full path from vulnerability discovery to exploitation, including live demos and the complete end-to-end chain.
It also explored its connection to the massive Draytek device reboot incidents in March 2025, suggesting that real-world exploitation may already be happening.
A powerful reminder of why transparency in embedded security research matters — and how sharing findings can strengthen the community.
“Beyond the Scan: Automating Vulnerability Management” – Gabriel Franco, Head of Security
A deep dive into how automation can turn findings into faster, smarter decisions by bridging technology and human expertise.
We explored how security teams can automate different phases of continuous monitoring using public tools and AI — from reconnaissance to vulnerability analysis.
Even small teams can build an efficient Continuous Security model by combining open-source tools with intelligent automation.
“RedTeaming Everywhere (Breaking Everything Without Looking Back)” – Hack the Talent Zone, Gabriel Franco
Our Head of Security shared his experience and the challenges offensive security companies face today.
The key message: don’t be afraid to dive into this discipline.
From real-world methodologies and tools to the human side of offensive operations — phishing campaigns, backdoored apps, and beyond.
The talk also covered how AI is reshaping the future of hacking, what cybersecurity companies look for in new talent, and practical tips for anyone starting out in Red Teaming.
At this year’s Ekoparty, we officially launched Doggie, an open-source device built to safely experiment with the CAN Bus system in modern vehicles.
Doggie allows users to connect, observe, and understand how vehicle modules communicate — opening new possibilities for automotive cybersecurity research.
Born from our internal research, the project is now open to the community on GitHub, with full guides, documentation, and tutorials.
During Eko, many attendees got their first Doggie, tested it live at the Car Hacking Village, and joined the growing community already contributing with ideas and improvements.
Beyond the code, there were stories, laughter, and shared moments: a street sign with a mind of its own, an after-party “hacked the Faraday way,” and long lunches with friends and CISOs who have been part of our journey for years.
Each Ekoparty pushes us to keep growing — connecting research, technology, and community.
To show that security isn’t just about protection, but also about understanding, experimenting, and sharing.
Thanks to everyone who stopped by, joined a talk, hacked, or just came to say hi.
See you at the next Eko — with more research, more ideas, and the same passion for hacking together.

Ofensive Cibersecurity Solutions, red teaming services, or continuous scanning? We’ve got you covered. 

Reach out for more information.
The post Ekoparty 2025: otra edición, nuevas conexiones y la misma pasión por hackear appeared first on Faraday.
]]>The post EmploLeaks: Finding Leaked Employees for the WinWebinar led by Gabriel Franco appeared first on Faraday.
]]>Gabriel Franco is our Head of Cybersecurity Services and introduces this new open-source tool, presented at Black Hat Arsenal. Emploleaks enables the collection of personal information using Open Source Intelligence (OSINT) techniques.
It starts by taking a company domain and gathering a list of employees from LinkedIn. It then collects data about individuals across multiple social media platforms—such as Twitter, LinkedIn, GitHub, GitLab, and more—with the goal of identifying personal email addresses.
Once these email addresses are found, the tool checks the COMB database and other online sources to determine whether the user’s password has been exposed in any data breach. Watch the full webinar to learn more about how to use this tool within your own organization.
You can also follow and contribute to the project on GitHub. https://github.com/infobyte/emploleaks
The post EmploLeaks: Finding Leaked Employees for the WinWebinar led by Gabriel Franco appeared first on Faraday.
]]>The post Octavio Gianatiempo presents SadProtocol goes to Hollywood – English version appeared first on Faraday.
]]>We are excited to present Octavio Gianatiempo live webinar about one of the major breakthroughs of 2023 from his research team.
EZVIZ designed SADProtocol to set up their security cameras, but our researchers found a remote code execution bug and used it to take control of the cameras and achieve a post-exploitation attack worthy of the big screen.
The post Octavio Gianatiempo presents SadProtocol goes to Hollywood – English version appeared first on Faraday.
]]>The post Vulnerability Management: How to Protect Your Organization from a Practical Perspective— M. Tartarelli appeared first on Faraday.
]]>We invite you to watch our online talk “Vulnerability Management: How to Protect Your Organization from a Practical Perspective”, led by our COO, Martin Tartarelli.
During the session, we discuss different strategies and best practices for vulnerability management within organizations. You can find more information on our website: https://faradaysec.com/
The post Vulnerability Management: How to Protect Your Organization from a Practical Perspective— M. Tartarelli appeared first on Faraday.
]]>The post Defending by Attacking by Federico Kirschbaum appeared first on Faraday.
]]>In this webinar, Federico Kirschbaum, Founder and VP of Research & Development at Faraday, shared a practical perspective on offensive security and the value of understanding how attackers think.
Throughout the talk, he emphasized the importance of prioritizing vulnerabilities (not all of them are exploitable), mapping an organization’s real attack surface, and leveraging open data and tools to identify risk. He also presented concrete examples, ranging from catalogs of commonly exploited vulnerabilities to leaked credentials and phishing techniques that remain highly effective.
Federico highlighted the need for security teams to focus on what truly represents critical risk, rather than getting lost in noise and low-value metrics. By showcasing free tools, standards such as security.txt, and accessible practices, he demonstrated how it is possible to raise an organization’s security maturity regardless of budget. The conclusion is clear: the most effective defense comes from seeing what attackers see—and acting before they do.
The post Defending by Attacking by Federico Kirschbaum appeared first on Faraday.
]]>The post Martín Tartarelli presents “Keys to Prevent Attacks and Strengthen Your Cybersecurity” appeared first on Faraday.
]]>In a context where threats are becoming increasingly frequent, your company’s cybersecurity must be strategic in order to anticipate potential attacks. In this talk, we address what you need to stay protected: how to detect vulnerabilities and how to strengthen your digital infrastructure through a comprehensive solution.
The post Martín Tartarelli presents “Keys to Prevent Attacks and Strengthen Your Cybersecurity” appeared first on Faraday.
]]>The post Automation and Pentesting: How to Leverage AI and Open Sourceled by Gabriel Franco appeared first on Faraday.
]]>In this talk, we explore how artificial intelligence and public security tools can help improve the pentesting process by increasing the efficiency and effectiveness of vulnerability detection, while also allowing researchers to focus on more sensitive workflows during analysis.
Use cases are presented in which automation enables complex tasks such as network scanning, application analysis, and even phishing detection—reducing the time and effort required to obtain accurate results. The overall goal of this talk is to help those who are taking their first steps in security understand the power of development and the benefits of automating repetitive tasks to identify vulnerabilities in real-world scenarios. The session was led by our Head of Security Services, Gabriel Franco.
The post Automation and Pentesting: How to Leverage AI and Open Sourceled by Gabriel Franco appeared first on Faraday.
]]>