Sparrow Wallet is a beloved Bitcoin software wallet that recently took two big hits to its functionality thanks to the legal prosecutions coming down on the founders of Samourai Wallet.
Despite recent events, however, Sparrow is still an excellent Bitcoin wallet that you should be using if you regularly interact with your Bitcoin holdings. From customizable custody setups to UTXO consolidation, there are still plenty of great offerings that make Sparrow Wallet worth using.
Understanding Sparrow Wallet
Sparrow Wallet is an open-source, self-custodial software wallet that you can download on your desktop. It comes equipped with a user-friendly interface, great privacy features, and integration with various Bitcoin tools and services.
Sparrow seamlessly integrates with connected wallets or other previously existing wallets – whether they be hardware or software wallets – and lets you configure your own custody setups, whether that be singlesig or multisig. You can host multiple wallets from the same computer, adjust your own fee rates for transactions, and generally enjoy a fuller range of options that make Sparrow incredibly flexible and useful.
Sparrow offers one of the most transparent and user-friendly experiences for navigating and managing your Bitcoin wallets.
It lets you see everything:
- Account balances
- Transaction histories
- Transaction previews
- Unspent transaction outputs (UTXOs)
- Fee payments
And previously, your:
- CoinJoin balance and transactions
- PayNyms
But as we’ll discuss, those last two beloved features are sadly no longer available on Sparrow. We’ll talk about what this means for users, and how the wallet can still come in handy outside of these use cases.
How the Samourai shutdown affects Sparrow Wallet
In an unfounded attempt to stifle Bitcoin privacy in the United States, the Department of Justice seized Samourai Wallet's servers, its websites, and arrested its co-founders.
As a result, some of our favorite aforementioned privacy features that Sparrow used to offer are no longer available due to the ongoing crackdown on Bitcoin privacy.
This doesn’t mean that you can’t still achieve the forward-looking privacy that CoinJoins enabled, it just means that it’s harder to access and will take a bit more technical prowess.
Is Sparrow Wallet still worth using?
There are a few different answers to this question. Sparrow Wallet will come in handy more or less depending on your personal situation.
If you hold Bitcoin with a custodian, and/or want to actively spend your Bitcoin or use it to fund your various online accounts, then yes, Sparrow Wallet is worth downloading. You’ll want to get that Bitcoin out of any custodially-managed vehicles if you want to enjoy the freedoms that real Bitcoin enables for holders. If you hold the Bitcoin in an ETF, unfortunately you’ll have to convert that ETF back into cash before converting to real Bitcoin, which will incur a taxable event along the way. You were never holding any real Bitcoin in the first place – it was just an IOU from the fund provider.
Sparrow Wallet security overview
Before even downloading Sparrow, you can check the safety of your download file by verifying with PGP Key, which Sparrow provides easy-to-follow instructions for on their download page.
Sparrow is entirely open-source, so anyone can verify that they have the correct version of the software.
Be sure to always refer to a Bitcoin product’s official website for any and all handling information. There are lots of scammers out there waiting for unsuspecting bitcoiners to click on the wrong link and mislead them into losing their own keys. Don’t become a victim yourself!
Taking this extra step is not necessary, but will provide peace of mind knowing that you haven’t been misled to the wrong website and are about to install malware onto your computer.
Sparrow Wallet ensures that the same standard of protection remains consistent throughout the platform.
You have full control over all the details of your wallet: your keys, xpubs, derivation paths, custody model, script type, descriptors, etc. When it’s time to make a transaction, Sparrow gives you clear, visualized overviews of the transaction, each party involved, and where the money is being sent. You can then manually verify, sign, and broadcast the transaction, or even use it to complete partially signed Bitcoin transactions (PSBTs).
Creating your Sparrow Wallet
First thing’s first:
- Download Sparrow Wallet: Visit the official Sparrow Wallet website and download the appropriate version for your operating system.
- Validate your download with PGP Key: According to Sparrow’s guidance
After downloading and installing Sparrow, open the application and create your first wallet!

- Click on "File" in the top left of your screen.
- Select "New Wallet".
- Choose a name for your wallet and click "Create".
- Click “New or Imported Software Wallet”
- Generate a new seed phrase and copy it down somewhere safe, ideally on a physical metal plate. NEVER online or on any device, period.
- Click “Create Keystore” and then import your keystore
After clicking apply, you’ll have the option to set a sign-in password that Sparrow will ask for anytime you boot up the app. Setting one is a good idea to have as a failsafe in case a thief somehow manages to steal your computer.
Navigating Sparrow Wallet
Once you’re in Sparrow Wallet, you’ll notice a few tabs on the left:
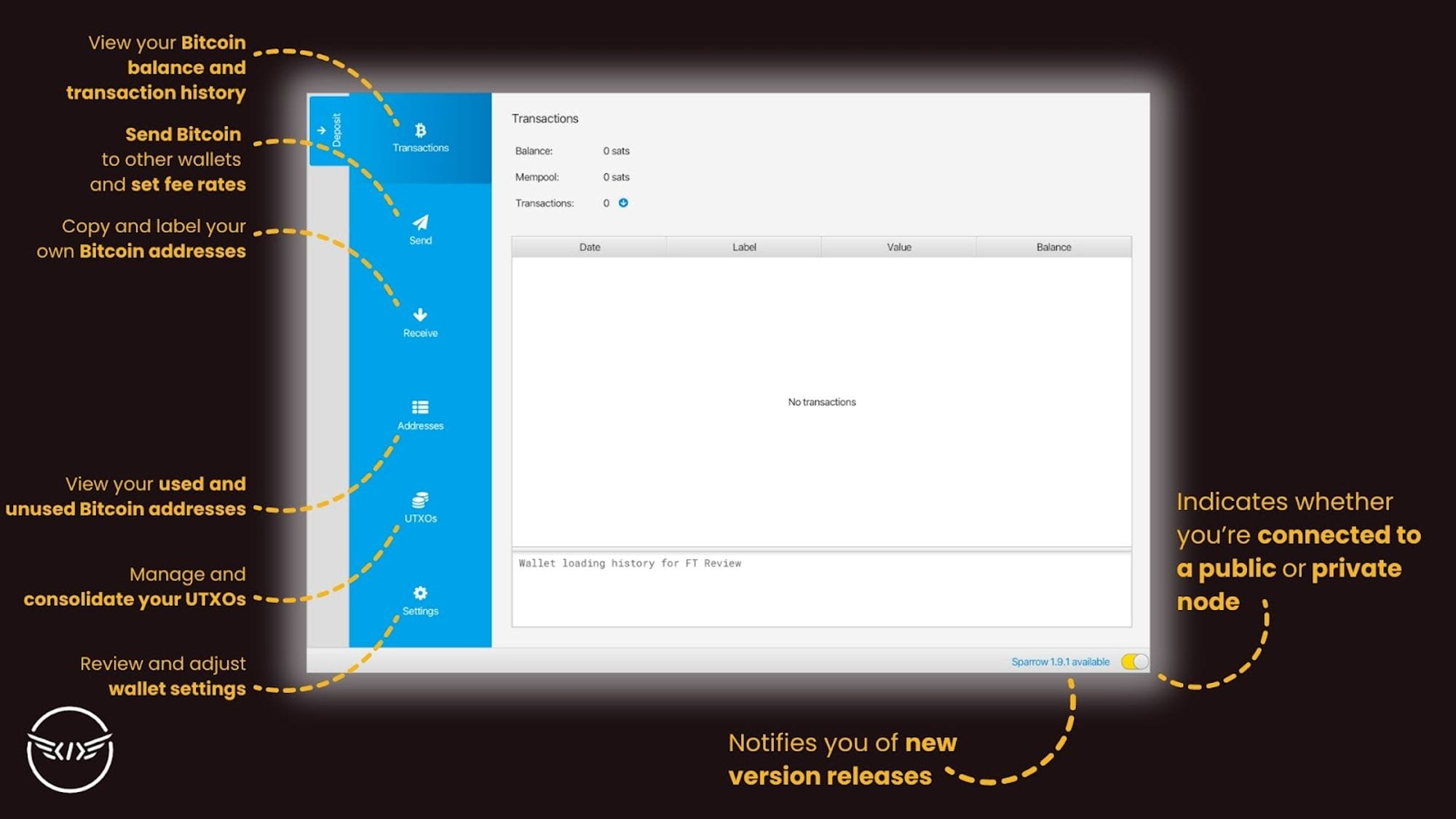
- Transactions: Shows you your current wallet balance as well as all incoming and outgoing transactions.
- Send: The interface you use to create transactions and set your fees.
- Receive: Where you can see and copy down your wallet’s Bitcoin addresses for receiving bitcoin.
- Addresses: Populates a list of unused Bitcoin addresses as well as ones that you’ve used in the past, in order to help maintain your privacy by ensuring you don’t reuse the same address.
- UTXOs: Shows a list of the UTXOs you’ve created from transactions.
- Settings: Lets you manage your wallet and software configuration.
6 favorite features from Sparrow Wallet
Sparrow Wallet comes with incredible value beyond mere sending and receiving. Despite the loss of CoinJoin and PayNym support, there are still plenty of useful applications for Sparrow Wallet:
1. UTXO consolidation
One of the best reasons to use Sparrow Wallet specifically is for easy UTXO management.
UTXO consolidation is one of the most impactful things you can do as your own bank to future-proof your Bitcoin. As transaction fees rise over time, small UTXOs may get priced out from being able to be spent, as the fee costs more than the sat balance of the UTXO.
This doesn’t mean that you should simply take all the tens, hundreds, or maybe thousands of your past UTXOs and consolidate them all into a single UTXO. If you want to maintain privacy, a single UTXO won’t offer that, as the recipient of any transactions from your wallet will be able to see your full sat balance if they check on-chain. Not exactly ideal if you’re wanting to prevent people from knowing how much Bitcoin you own.
The best method is to strike a balance between safety and privacy. You want UTXOs to be large enough to comfortably pay off any transaction fees (and accommodate for spikes in fee rates), but not so large that untrustworthy recipients realize your true amount of wealth.
In today’s fee climate, 1 million sat UTXOs are a good option.
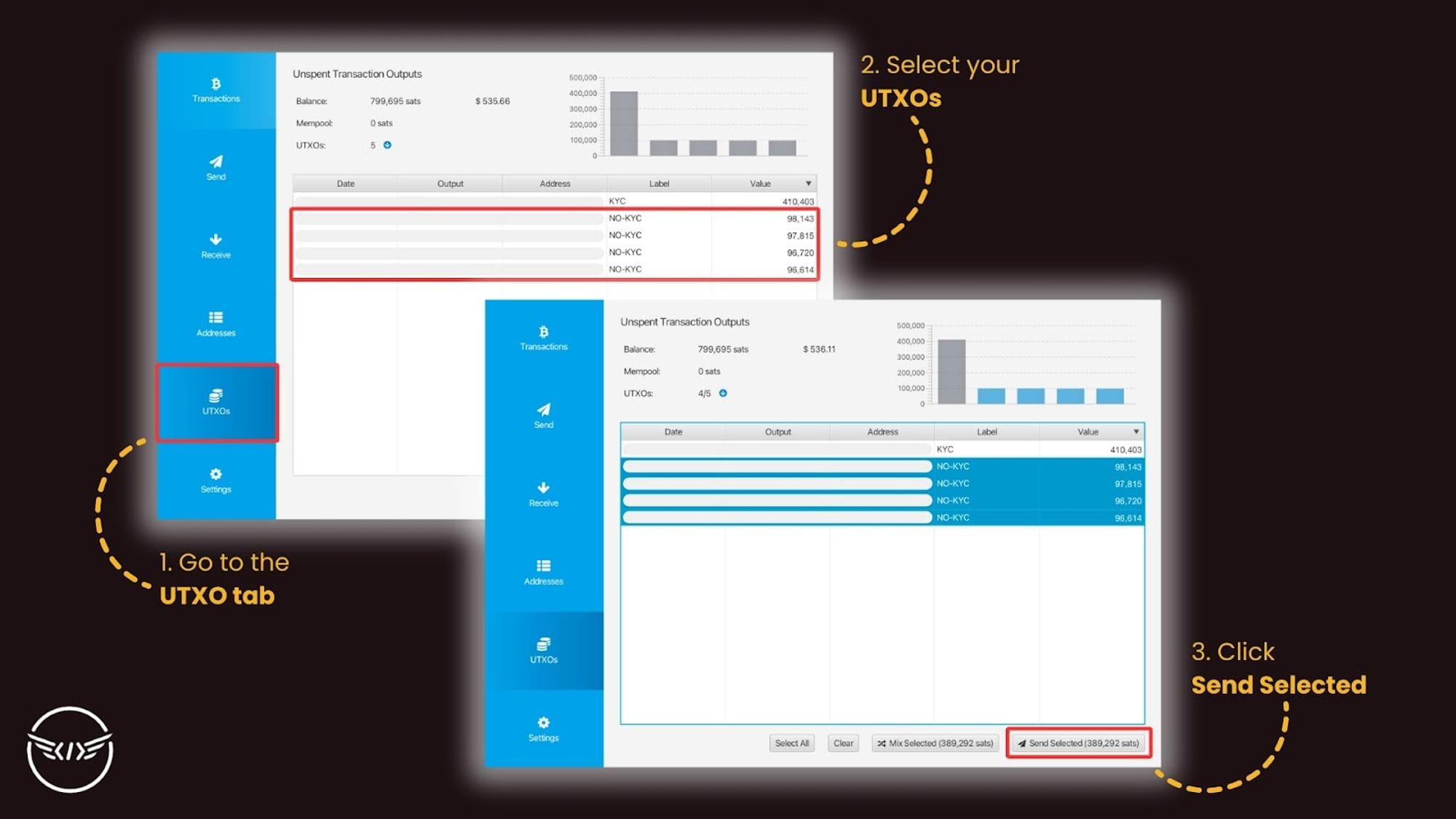
To consolidate them yourself, simply select multiple UTXOs from the UTXO tab that add up to your desired sat amount (e.g. 1,000,000 sats or 0.01 BTC) and send them back to yourself in a single transaction by copying and pasting a fresh Bitcoin address from your own wallet’s Receive tab. Doing so will leave you with a single, larger UTXO after the fact.
2. Transaction labeling
A very helpful feature for wallet organization, labeling your transactions on Sparrow is an excellent way to ensure that you can remember where transactions are going to or coming from. If there’s a regular KYC exchange that you send Bitcoin to Sparrow from for example, you can label that exchange’s address so that each time you receive payments in Sparrow, you know that it’s not anonymous Bitcoin.
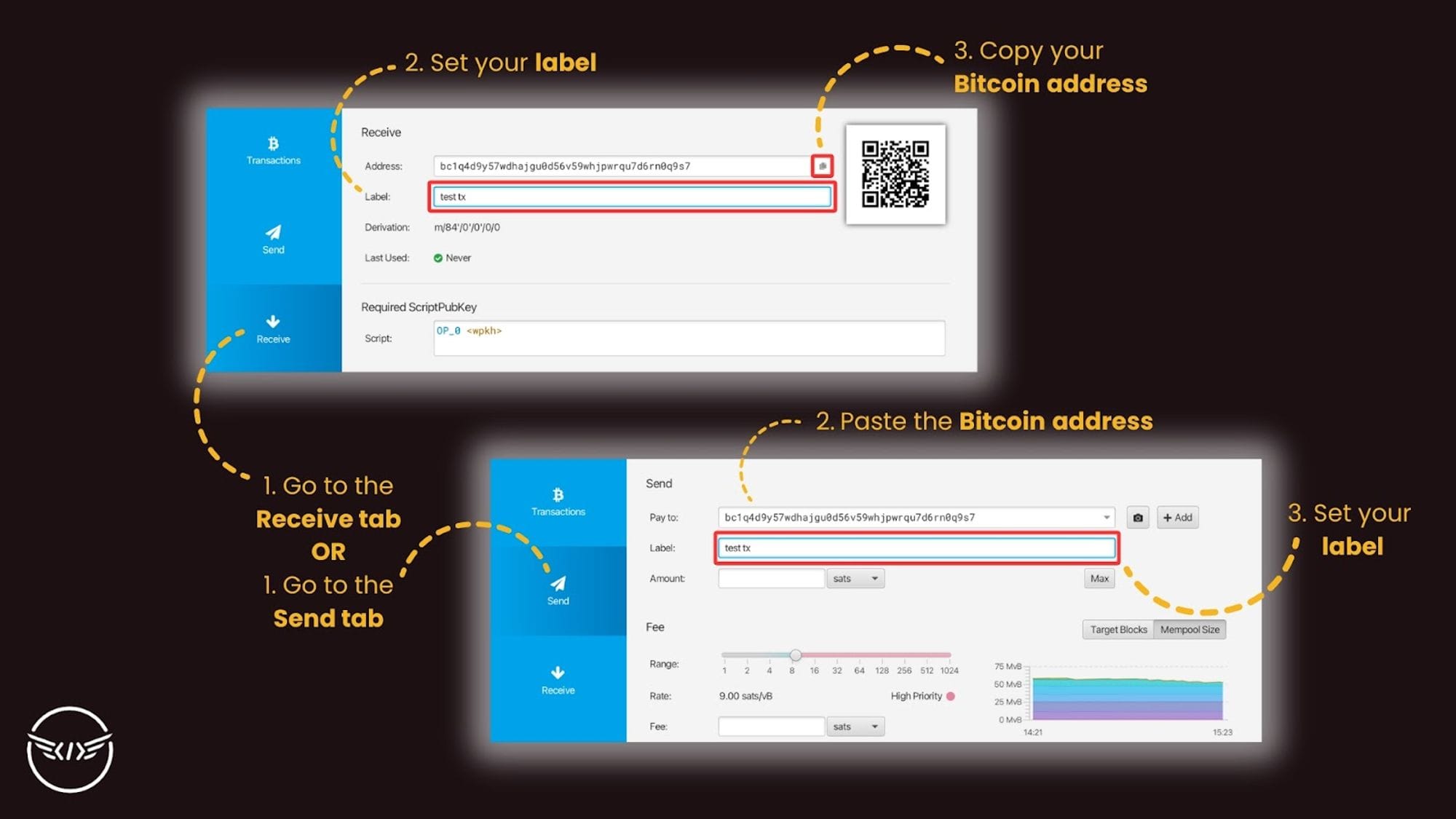
When it comes time to consolidate your UTXOs, you’ll appreciate having these labels in place so that you don’t accidentally consolidate your non-KYC UTXOs with other KYC UTXOs, thus breaking the privacy of your anonymous Bitcoin.
3. Syncing with your own node
By connecting your Sparrow Wallet to your own node, you take your privacy to the next level. Transactions you make on Sparrow will only run through your private node rather than on another public node, so if you transact with non-KYC Bitcoin, zero information about your IP address or other personal details reaches other public server logs.
All that other public nodes will receive is transaction data, but they won’t know who or where it’s coming from.
Beyond privacy, running Sparrow on your own node unlocks true financial sovereignty. You’re fully responsible for the ins and outs of your Bitcoin wallet, and connecting Sparrow to a node gives you the flexibility to tailor your experience exactly to your needs.
To learn how to set this up yourself, read up on Sparrow’s literature and check out Southern Bitcoiner’s easy five minute tutorial.
4. Create multisig setups
When creating a new wallet, you have the option to set up a multi-signature (multisig) custody model if you prefer distributed custody with family members, clients, friends, or other trusted parties.
BTC Sessions also created a fantastic overview for creating multisig wallets on Sparrow if you’re interested to learn how (skip to 25:00 for details).
5. Dynamic fee setting
Sparrow Wallet lets you manually select your own fees for transactions. You can make them as large or as small as you’d like – you just have to keep in mind that the transaction may not confirm if the fee is set too low, or you may overpay in fees if you raise the fee rate too high.
When you interact with standard mobile Bitcoin wallets, you’re typically subject to the average fee rate that the network happens to be charging at the time. During periods of high stress on the network, this may be frustrating if you’re trying to get a transaction out but it costs $100 to send.
If it’s not a time-sensitive transaction, like simply moving Bitcoin to another wallet for long-term storage for example, then you can lower your fee beyond the going rates and still broadcast the transaction to the network. You’ll only have to wait for fees to come down later for your transaction to confirm.
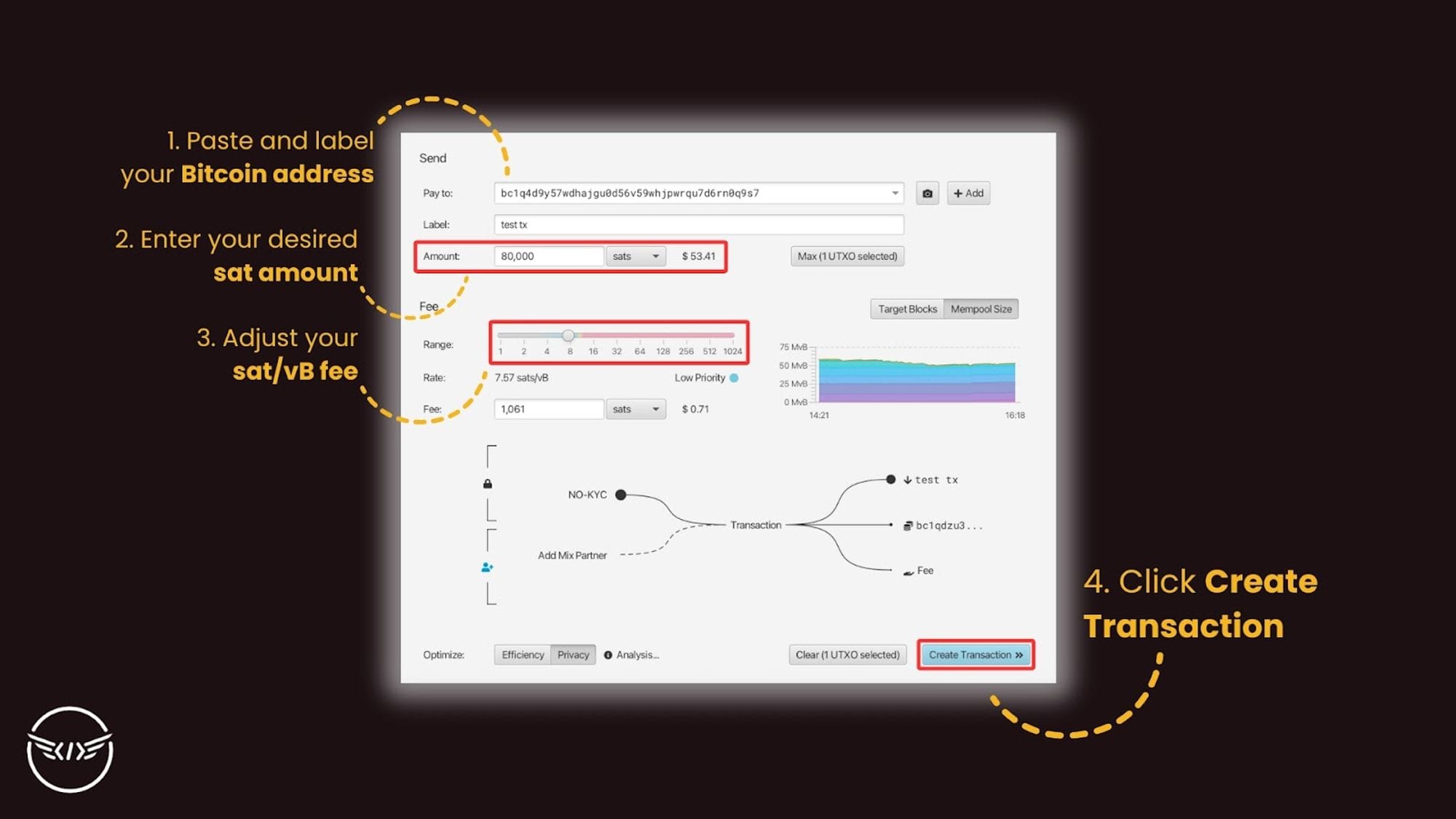
This level of flexibility that Sparrow offers makes it very handy for the everyday Bitcoin user. Especially in times where new developments on Bitcoin cause volatile swings in base layer fees, having adjustable fee rates is critical to easier Bitcoin navigation (and headache prevention).
6. BIP 47 Support
Thanks to BIP 47 reusable payment codes, Sparrow was able to integrate this functionality natively into Sparrow so that you can enjoy enhanced privacy.
Every time you use a BIP 47 payment code for a Bitcoin transaction on Sparrow, the software will generate a new, unused address automatically for you to ensure that you don’t reuse the same address.
However, if for some reason you do want to reuse an address, you can find it under the “Address” tab of Sparrow Wallet, which lets you see your previously used Bitcoin addresses.
It supports linking and sending directly to non-PayNym payment codes, allows you to set automatic labels for BIP47 receive addresses, and enables you to rename linked BIP47 contacts.
Dangers to be aware of with Sparrow
Sparrow enables you a truly tailored Bitcoin experience, but that level of flexibility also comes with some pitfalls to be aware of.
1. Improperly storing your wallet credentials
Sparrow Wallet, while it comes with many unique advantages, still works just like any other Bitcoin wallet. There are no extra protections in place for your seed phrase recovery. Never reveal your seed phrase or store it on a device. The same goes for any additional passphrases (which Sparrow supports), xpubs, etc. Keep all this information private and physically secured so you don’t run the risk of revealing it to the wrong person.
2. Overpaying for transactions
While it’s very helpful being able to set your own fee rates on Sparrow Wallet, you also run the risk of fat fingering the rate you pay and overspend by a wide margin.
If you take a look at the transaction fees paid in the most recent halving block #840,000, you’ll notice exorbitant levels of fees that some people paid in order to get their transaction in that block specifically.
Of course, you probably won’t accidentally spend five or six figures in fees. It just goes to show what’s possible. Sparrow Wallet’s fee slider cuts you off beyond a certain sat/vB rate so that you don’t drain your entire stack. But if you aren’t paying attention or being intentional when setting fees, you may spend more Bitcoin than you may have thought.
3. Accidental doxxing
As previously mentioned, If you mix non-KYC UTXOs with KYC UTXOs, you break the privacy that your non-KYC BTC was enjoying since outside entities can now see that each UTXO was sent to the same wallet, thus revealing you to be the owner of both UTXOs.
To prevent this situation entirely, you can create two independent accounts or wallets within Sparrow and separate your UTXOs between them. This adds an extra layer of protection to keep you from accidentally consolidating the wrong UTXOs together. Only send non-KYC Bitcoin to one wallet, and doxxed Bitcoin to another, and you’ll stay more organized and put yourself at less risk of doxxing your non-KYC stack.
Do you know what else you should be doing to keep your identity private when handling Bitcoin?
There isn’t a whole lot that can go wrong when using Sparrow. Any mistakes you make that separate you from your Bitcoin comes down to personal responsibility, so always be intentional and treat your Bitcoin stack as if you’re handling it for someone else to ensure you don’t make any hasty mistakes.
Conclusion
Many bitcoiners evangelize about “being your own bank,” but what does that look like in practice? Sparrow Wallet is one of the best user-friendly options for seeing and feeling that in action.
It’s like the command center for managing your keys and organizing your funds, much like what banks are paid to do for us today. But by using Bitcoin and Sparrow Wallet rather than dollars and a bank account, you open yourself up to true financial freedom that doesn’t require the permission of anyone. All you need is a computer and personal responsibility.
While it’s unfortunate to have lost Samourai’s privacy-enhancing features built natively into Sparrow, there are still plenty of reasons you should take advantage of it if you haven’t already.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step than to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

Bitcoin is the world’s freedom money, but over the years as it continues to grow, regulatory capture and other political tactics are being played in an effort to suppress Bitcoin from realizing its true potential.
No-KYC Bitcoin represents freedom money in its purest form, enabling its holders unlimited financial freedom to transact privately on their own terms, without risk of simple theft or seizure.
While having “freedom money” may sound cool and all, what are the benefits of no-KYC Bitcoin that you can actually expect to enjoy yourself?
What is KYC?
First of all, it’s helpful to understand what KYC is in the first place to truly appreciate no-KYC Bitcoin.
KYC, or “Know Your Customer,” is a standardized process of collecting and verifying the identities of customers who interact with businesses. It aims to let them know that they are actually working with real customers instead of bots or criminals.
KYC collects information about your name, home address, phone numbers, some form of government ID, and potentially more, depending on the exchange.
In the context of Bitcoin, centralized exchanges – where you purchase Bitcoin – enforce KYC procedures to comply with the regulatory regime. Mainstream ETF providers like Fidelity and BlackRock – who are likely to onboard billions, if not trillions, of dollars in capital to Bitcoin – all KYC gate their platforms so you give up your personal information before buying into a fiat-denominated IOU that they hold for you.
That isn’t the vision Satoshi saw for Bitcoin.
The Problem With KYC
While it’s all done in the name of protection, KYC actually ends up wasting more resources than those actually lost due to illicit financial activity, and endangering people’s online activity by collecting their data into a honeypot.
Based on estimates of Europol data from author Olivier Roland, who details the greater dangers of KYC, we learn that the EU spends ~€144 billion on KYC/AML (anti-money laundering) compliance costs each year, while only confiscating ~€1.2 billion in criminal funds.
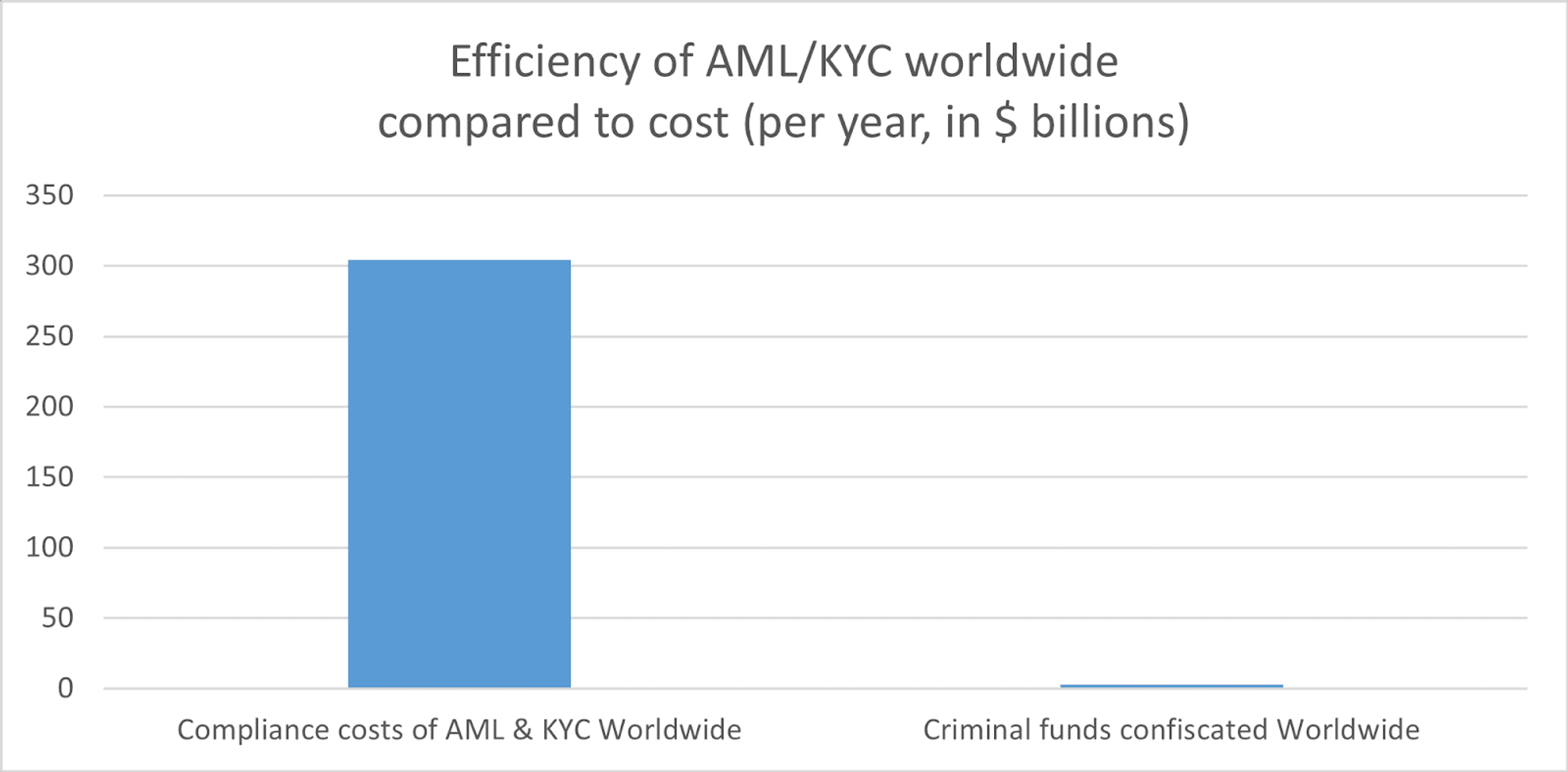
So while KYC/AML protection may have good intentions, the costs far outweigh the benefits.
All that KYC really does is dox the identities of everyday people and put them at risk. Just look at MobiKwik, a major payment provider in India. In March 2021, during the height of the previous bull run, a hacker managed to crack MobiKwik’s centralized network and execute one of the largest KYC data leaks in history. The hacker allegedly gained access to the entire customer KYC database, which he then offered up to the darkweb in exchange for 1.5 BTC.
Some of the data the hackers could get their hands on included:
- 7.5 TB of over 3 million merchants KYC data, including credit card information, passport details, and KYC selfie images of individuals
- 40 million 10-digit card numbers with month, year, and card hash
- 99 million mail, phone passwords, and addresses
- 350GB of MySQL dumps
- Data on installed apps, IP addresses, GPS locations, and more
- Other company databases
If you ever receive lots of spam calls to your phone number, email, or other online accounts, it’s likely due to the years of major data leaks like these that end up harming citizens forced to KYC themselves.
You may want financial sovereignty, and while Bitcoin can enable that for anyone through self custody, purchasing your coins through a KYC-gated exchange allows them to track that Bitcoin’s activity on the ledger, even after you move the Bitcoin off of the exchange (unless you mix your Bitcoin after the fact, but we’ll touch more on that later).
If you want to truly make your finances private and enjoy the full freedom of holding your own money, then no-KYC Bitcoin is what you’re looking for.
What is no-KYC Bitcoin?
As the name suggests, no-KYC Bitcoin is Bitcoin avoids all of that data collection that KYC processors enforce. No-KYC Bitcoin therefore keeps its holder’s identity entirely private since it has no transaction history associated with any KYC databases.
It’s the Bitcoin that you earn anonymously from mining, routing Lightning payments, payments from anonymous customers online or in person, or through purchases via no-KYC Bitcoin exchanges.
No-KYC Bitcoin gives you the freedom to save and spend privately without anyone being able to keep track of your activity.
While many people make sure to note that buying no-KYC sats typically comes with an additional percentage point premium above its current price, it’s worth considering that the “standard” price you pay at KYC exchanges is actually discounted, because you’re also paying with your data.
But once once you get your hands on no-KYC Bitcoin for the first time, there are plenty of benefits you’ll enjoy that handing out your data alongside your cash to KYC exchanges can’t offer.
10 benefits of no-KYC Bitcoin
Not every single benefit listed here may apply to you, but understand that no-KYC Bitcoin can benefit anyone, regardless of their circumstances.
1. Maximizing privacy: No-KYC Bitcoin cannot be easily tied to your identity by any outside parties, so you and you alone have untethered access to manage your money without financial surveillance.
2. Censorship resistance: Since you can’t track no-KYC Bitcoin, it’s the only money in the world that you can spend anywhere, as no local regime even has the potential to block transactions from Bitcoin that they don’t even know exists. This mitigates the off-chance situation where a particularly hostile government sees your Bitcoin spending within the country and comes knocking at your door to stop it.
3. Confiscation resistance: You also won’t have to worry about having your Bitcoin seized if it’s truly no-KYC. In the event of an Executive Order 6102-style confiscation, only those who’ve given up their keys and personal information to KYC’d custodians would possibly lose their Bitcoin. Meanwhile, you could sleep easy at night.
4. Accessible anytime, anywhere: No level of government censorship or limited “trading hours” will prevent you from accessing your money when you need it. With no-KYC Bitcoin, you won’t have to rely on the timing or rules of any other organization to access and spend your Bitcoin. There is a long history of exchanges suddenly blindsiding users, preventing them from withdrawing or moving their Bitcoin at all, and even cutting them off entirely from access to their account. All the while, deliberately doxxing their customer data for the world to see (I’m talking about Celsius).
5. Strengthening the Bitcoin network: The more KYC’d the Bitcoin network becomes, the more controls that the government can try to exercise over the network. While centralized entities are never fully able to contain decentralized networks over time, KYC certainly makes it easier, and delays Bitcoin adoption in the long run. On the other hand, no-KYC Bitcoin upholds the resilience of the Bitcoin network, as it creates more coins that are impossible for an external party to coerce or manipulate.
6. Protection against data breaches: Because your Bitcoin isn’t tied to any KYC databases, you don’t run the risk of having information about you owning that Bitcoin leaked online to hackers or scammers. Your money should never be a source of risk for your privacy, and no-KYC Bitcoin is the only money that’s capable of doing that.
7. Anonymous loans: With more practical application, you can fund loans entirely anonymously, enabling you the flexibility of financial instruments while maintaining your privacy. Platforms like lend.hodlhodl.com let you take out Bitcoin loans for other crypto, including stablecoins if you’re looking for a cash equivalent loan.
8. Anonymous donations: In case your region of the world doesn’t support charitable actions towards particular groups, you can use no-KYC Bitcoin to fund donations wherever you’d like and truly speak with your money. Or, you can use it to support freedom tech that’s enabling individual sovereignty for people around the world.
9. Use only in case of emergency: To adapt to the current monetary regime of today while still taking advantage of Bitcoin, you can choose to fund your everyday expenses and bills with your KYC Bitcoin stack, and save a smaller portion of your stack as no-KYC Bitcoin. This way, you can take the right step forward towards adopting a Bitcoin standard, while also hedging against government overreach. This is a practical first step for any new bitcoiner to take with no-KYC Bitcoin. And as always, hold your own keys, KYC’d Bitcoin or not, to prevent anyone from taking your wealth away from you.
10. Exploring the Bitcoin and privacy ecosystem: Developers all over the world are building encrypted messengers, social networks, open-source VPNs, and other privacy-focused tools to protect people’s online lives. Some of these platforms accept Bitcoin payments, making them a perfect outlet for spending your no-KYC Bitcoin. KYCnot.me is an excellent resource for exploring some Bitcoin platforms and other no-KYC privacy tools that you can spend your no-KYC sats on, on-chain or over Lightning, as well as Monero, fiat, and even cash.
The unfortunate irony
Although no-KYC Bitcoin comes with its many benefits as freedom money, the rails to acquiring and spending it aren’t so free and easily accessible.
Governments have always tried to suppress the people’s ability to access freedom tech like no-KYC Bitcoin; just look at the Catholic Church’s reaction to the printing press, or North Korea’s handling of the internet today.
Incorporating no-KYC Bitcoin into your daily life isn’t as practical in 2024. The good news, however, is that the benefits shared here go to show how much easier this technology is for people to access and take advantage of.
Regardless of the invasive policies that governments try (and fail) to enforce on protocols and their users, the technological trend historically wins out over time. Governments learn to play to the rules of technology instead of dictating them themselves. Historically the US dollar has managed to call the shots, but Bitcoin is here to update the rule book while enabling truly anonymous, private financial lives for anyone with an internet connection.
How to acquire no-KYC sats
So, to get your hands on no-KYC sats, you have a few different options.
- Buy from decentralized peer-to-peer exchanges: Probably the most simplest way, plenty of no-KYC Bitcoin exchanges are out there, including Bisq, HodlHodl, and many others. These platforms offer all different kinds of payment methods so you always have a way to buy Bitcoin without KYC. Be aware, however, that not all decentralized exchanges are created equal, and come with their own set of risks.
- Earn through integrating Bitcoin into your own business/service: If you operate a revenue-generating business, consider accepting Bitcoin as payment! Not only will you earn in the hardest money on earth, but having a direct source of no-KYC Bitcoin is a surefire way to uphold your financial sovereignty.
- Run a Lightning node: Routing transactions through your own Lightning node is another great passive source of no-KYC Bitcoin. Once you set things up, all you need to do is keep the node running, and you’ll have a steady stream of anonymous Bitcoin ready for you to use. It might not be much, but it’s honest Bitcoin.
- Mine Bitcoin yourself: Last but not least, mining Bitcoin is the most straightforward way of acquiring no-KYC sats. After setting up your first rig, mining no-KYC Bitcoin only becomes easier. There are a lot of steps involved with Bitcoin mining, and it often won’t be profitable initially. So be sure to do thorough research before getting started with Bitcoin mining, and consider the other options first if you want to save on costs.
How to clean your KYC stack
“If I have sats that are already KYC’d, is there a way I can de-KYC them?”
Not really, unfortunately. Once you purchase Bitcoin from a KYC exchange, they immediately log:
- Your personal credentials and banking information
- Exactly how much BTC you bought
- Exactly when you bought it
- The BTC address you withdraw to
- Your transaction patterns
- Communication records
- Your IP address and device information
After withdrawing to self custody, if you don’t do anything more to protect your Bitcoin’s privacy, then that exchange would be able to track all further transactions you make.
If you want to clean Bitcoin without anyone knowing that you purchased it or being able to see where you’re spending it, then you’ll have to sell that BTC back to fiat, bite the bullet and pay the incurred capital gains tax, and put your fiat towards one of the no-KYC Bitcoin sources mentioned above.
Alternatively, if you want more privacy but don’t care if others know that you once bought the Bitcoin, you just don’t want anyone seeing your activity, then you need to consider forward-looking privacy tools. Samourai’s CoinJoin was one of the most popular ones out there, but after the recent crackdown on Samourai, you’ll have to try other alternatives like JoinMarket.
Doing so will scramble your Bitcoin’s history, making it much more difficult to track the true owner. It’s not totally foolproof, assuming your transactions are being targeted, and especially if they’re tied to criminal activity. But for the everyday person, organizations with limited information like a Bitcoin exchange simply wouldn’t have the incentive or take the time to trace your activity. However, they would know that you mixed your coins, which may be a reason to target the address or add it to a smaller dataset of BTC addresses using mixers.
Keep in mind that these “solutions” are a temporary fix to a greater problem. Users shouldn’t have to act themselves to improve their privacy. We need privacy-first solutions that keep users protected from the very beginning when getting involved with Bitcoin. It needs to feel as intuitive as our favorite mainstream platforms are today. With time, it may come as the network continues to iterate, but it takes the efforts from every one of us to either integrate new privacy technology into our lives or create it ourselves!
Be sure to understand these implications, but don’t let them stop you from enhancing your Bitcoin’s privacy.
The bigger picture
All of the problems we see arise from KYC today stem from an attempt to solve a problem using broken infrastructure.
Today’s internet is critically lacking a security layer that can protect our data effectively without relying on counterparty risk. It’s the same problem plaguing our money too. Bitcoin is here to solve both of these realms for us.
The Bitcoin price alone demonstrates how effective it is at maintaining wealth over time, but with new application layers emerging on Bitcoin so rapidly today, we’re witnessing the emergence of a truly secure internet that the world has been working towards.
Communication platforms like Nostr are empowering its users to secure their voice with Bitcoin rather than relying on counterparties like Elon Musk or some other company spokesperson. There’s a buy-in incentive for others to adopt these protocols, that individually could only be financial, but collectively is beneficial for freedom at large.
Ultimately, Bitcoin is restoring free market mechanics to a world that’s been driving on monetary debasement, bailouts, and fraud. Technologies like Bitcoin are the natural responses to these problems, much like how the human body responds to a virus.
Government-ran legislature just doesn’t keep pace with the tactics and tools being used to avoid them. Invasive policies like KYC and surveillance tools like CBDCs, on top of an insecure internet, create an environment akin to walking through a landmine field for everyday people. And with the rate of technological expansion, the sophistication in cybercrime will only become greater and easier to fall into.
Conclusion
Buying, holding, and spending no-KYC Bitcoin is the only way that we’ve ever been able to enjoy financial sovereignty and grow our wealth over time without any risk of censorship, debasement, or theft.
Bitcoin that you bought through KYC exchanges and withdrawn to your own custody certainly still works just as Bitcoin is designed to, but if you don’t want third parties tracking the activity of your Bitcoin holdings, then you’ll need to get your hands on no-KYC sats for ultimate privacy.
It all comes down to your own needs. While privacy may not seem so important to some, rapid developments in technology make the internet’s need for privacy greater than ever before.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step than to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

In an unprecedented court case, Alex Pertsev, a key developer of an Ethereum-based privacy tool called Tornado Cash was sentenced today to over five years in prison as a result of his work on the project. The sentence handed down was the maximum requested by the prosecutors, and marks the first conviction of a developer who built a decentralized privacy tool for cryptocurrencies.
The ruling itself, translated from Dutch to English, is a disturbing and insightful view into the mind of the Dutch government and many governments across the world today.
Tornado Cash refresher
For those new to Tornado Cash as a tool, it is a decentralized, smart-contract-based privacy tool for Ethereum. It allows users to generate a Tornado Cash-specific private key (called a "secret note"), deposit their funds to the smart contract using this private key, and then withdraw their funds at any future time using this private key. Upon withdrawal, all links between past and future history are broken using a Zcash-like privacy protocol.
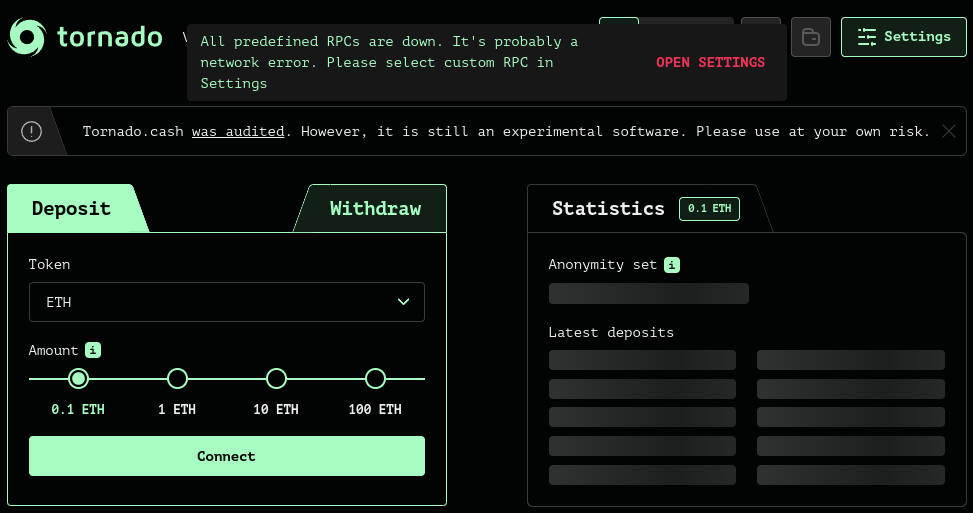
The most important details to note:
- The Tornado Cash devs removed their ability to edit the smart contract long before indictment
- The Tornado Cash devs never had custody over any user funds
- The Tornado Cash devs did not directly profit off of the smart contract's usage
- Most usage came through the official web UI, created and run by the Tornado Cash devs (including Alex Pertsev)
- The Tornado Cash smart contract has continued to function despite sanctions and indictments thanks to its decentralized nature
For those who are just hearing about this case now, please read our previous post on the original indictment for more info on Tornado Cash and the case at hand:

Breaking down the ruling
For the purposes of this post, we'll dive into the court's ruling itself to better understand the perspective of the Dutch government and come to grips with their view of open-source, decentralized privacy tools like Tornado Cash.
The court acknowledges Tornado Cash is unstoppable
Due to the nature of how this system works, it is virtually impossible to make user interface inaccessible. This fact, combined with the use of smart contracts, makes it virtually impossible to take Tornado Cash offline. - p. 8-9
One of the key aspects of the defense in this case and Roman Storm's is that they are entirely unable to prevent illicit usage of Tornado Cash, no matter what precautions they implement due to Tornado Cash's decentralized nature. The court fully acknowledges this (which is important) but that doesn't change their view as we'll get to later.
Custody is not required for money laundering
That Tornado Cash did not at any time have power of disposal over the cryptocurrency derived from crime in carrying out these concealment or concealment money laundering acts does not alter this fact.
Indeed, the performance of these money laundering acts does not require the existence of power of disposal over the laundered items. - p. 10
The matter of custody has long been the key factor for understanding if a tool is or is not liable for money laundering through their tool (and thus responsible for implementing KYC/KYT measures into their app). Between the recent DoJ response in the case against another Tornado Cash developer, Roman Storm, and this court ruling, it's clear that governments across the world have shifted the goal posts for money laundering.
This shifting of the goal posts now has to make you wonder – where exactly does the line get drawn? Is any cryptocurrency wallet that is used for illicit activity now liable? Where does it end?
Criminals using your code makes you a criminal
When these acts are performed with respect to felony-derived Ether, it is actually Tornado Cash that gives effect to the concealment or concealment money laundering act. Therefore, in the court's opinion, Tornado Cash cannot be viewed as merely a tool for the user. - p. 10
One of the most shocking segments of the ruling happens when the court makes it clear that if an illicit user is using your open-source, decentralized tool to gain privacy for themselves, their criminal liability is fully transferred onto you. Your tool is not merely a tool, it is as if you personally concealed the source of funds for them even if you had no ability to stop their usage.
Building decentralized, unstoppable tools makes you liable in perpetuity
In other words [the Tornado Cash founders] are the inventors, creators and implementers of Tornado Cash. As such, they are also responsible for the (consequences of the) operation of this tool. The autonomous, immutable and unstoppable nature of the smart contracts does not work in this context as a disulpatory factor. After all, this is not a fortuitous circumstance. These properties are the result of conscious choices made by the designers. Tornado Cash works as it was conceived. In the court's opinion, the defendant can therefore be classified as a perpetrator of the money laundering acts carried out by Tornado Cash. - p. 11
In a crazy, absurd twist, the Dutch court rules that the conscious choice of the Tornado Cash founders to create an unstoppable, decentralized tool means that they should be held liable for it's usage despite also acknowledging their inability to prevent illicit usage. This brings to the foreground so many questions its hard to know where to start.
For instance, if the developers working on Tor know they're building an unstoppable, decentralized privacy network, are they then held liable for any criminal activity perpetrated on the Tor network? If a Bitcoin core developer helps to improve Bitcoin as a decentralized, unstoppable form of money and it is used for illicit purposes, does that make them liable?
Tornado Cash functions as it was designed by them and in terms of its operation is entirely their responsibility. - p. 13
Everyone should be shocked by the gravity of these quotes and their implications.
Knowledge that your tool could be used for illicit means counts as intent
...it was foreseeable from the beginning that Ether derived from crime would be deposited in Tornado Cash, due to the concealment effect of Tornado Cash. - p. 14
This just in! Bad guys can use good tools for bad things! What doesn't shock any logical person seems to shock the Dutch government, as they are somehow able to find intent to commit money laundering in the mere fact that building a tool like Tornado Cash could potentially be used in the future for money laundering. If developers didn't build any tools that could potentially be used for illicit purposes, we wouldn't have:
- Smart phones
- Internet browsers
- Forums
- Chat apps
- Video games (yes, people use in-game chat for illicit purposes)
The list could be endless, but it's an insane proposition to consider any tool built with the ability to be used for evil as the developer intending the tool to be used for illicit purposes.
The foreseeability and knowledge of the widespread misuse of Tornado Cash did not prevent the defendant from developing Tornado Cash and offering it to the public without limitation (e.g., by incorporating compliance measures). On the contrary, defendant continued to design and roll out Tornado Cash despite that foreseeability and knowledge, with virtually every follow-up step reinforcing the concealment and anonymity of its users. - p. 15
Improving privacy tools implicates you
Securing the user's anonymity and concealing the transaction history have remained central. - p. 16
In the court's intermediate conclusion, they make sure to hammer home the point that Alex continued to improve the privacy protocol of Tornado Cash up until the day he was arrested.
Of course they don't mention that the overwhelming majority of Tornado Cash's usage was licit (~93% by the US Department of Treasury's measure, ~84% by the Dutch court's measure) and that Alex could have been building to protect those user's privacy.
Implementing all possible compliance measures doesn't matter
While at first glance the implementation of the [system] does indeed appear to be a form of a KYT control through which Tornado Cash aims to prevent abuse, in reality the implementation has little effect... Circumvention of the [system] is easy by not connecting to Tornado Cash's UI with a sanctioned address, but by doing so through one or more intermediate addresses. On top of that, the source code of the UI is public, so third parties can use it and easily modify it so that the check by the [system] does not occur. - p. 17
One thing that is often forgotten in this case is that the Tornado Cash founders did actually implement two compliance tools. One tool allowed users to voluntarily reveal the source of funds to a third-party, while the other tool altered the web UI to prevent deposits from known-illicit Ethereum accounts. The latter is the strongest possible compliance that the Tornado Cash devs could have implemented, as they had no ability to add compliance to the smart contract themselves.
Does that (already acknowledged and admitted) distinction matter to the Dutch court? No, because it was able to be circumvented by technically-savvy users. But these same tech-savvy users could easily circumvent the UI entirely and make direct RPC calls, making any possible compliance tool useless.
Everyone must build in compliance measures, not just those legally obligated to comply
However, the court held that the question of whether or not Tornado Cash was a financial institution subject to compliance regulations was immaterial. What is important is whether the defendant and his associates complied with the law. Complying with compliance regulations is helpful in preventing violations of the law, but not being subject to compliance regulations does not relieve anyone of the obligation to comply with the law. No one may engage in money laundering conduct that has been criminalized. Defendant's team violated this rule. - p. 18
Even though Alex and the other founders of Tornado Cash sought legal guidance and (rightly) determined that Tornado Cash was not subject to FinCEN guidance (and thus required to implement KYC/AML/KYT measures) the Dutch court still says they had an obligation to comply. Why? Because Tornado Cash was partially used for illicit purposes it retroactively required compliance.
Even if you're not subject to FinCEN/FATF guidance, the Dutch court says you should comply harder anyways.
Conclusion
In a complete victory for the Dutch government, Alex Pertsev was given the longest possible sentence, despite his complete inability to prevent illicit usage on Tornado Cash. In doing so, the Dutch court system has set a heinous precedent, declaring that any developer of a decentralized, unstoppable protocol or tool should be held responsible and criminally liable for all of its usage in perpetuity. This verdict could have wide-reaching implications, as much of the privacy landscape relies on decentralized, unstoppable tools or protocols like the Tor network, Bitcoin, Monero, SimpleX, and many others.
I urge those of you reading this to consider the implications of this conviction and do everything you can to encourage, sustain, and defend open-source developers working on privacy tools. We are officially in the "then they fight you" stage.
Lastly, we at Freedom.Tech continue to stand with Alex despite this conviction. #FreeAlex.

Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step than to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

While the core of our focus on Freedom.Tech has been Bitcoin up until this point, the recent shutdown of our favorite privacy tool on Bitcoin has made it necessary to more rapidly educate others on the value and importance of another cryptocurrency – Monero.
Monero is a decentralized, privacy-preserving cryptocurrency that started in 2014 and has continued to iterate and improve to become the preeminent form of digital cash today, due to it protecting every user's privacy no matter their personal interest in privacy, technical acumen, or background. Because of its effectiveness, however, governments have seen fit to make it harder and harder each year to acquire Monero directly from standard, centralized exchanges as a way to prevent the average person from gaining financial privacy.
Today, we'll quickly unpack what Monero is and walk through the best ways to acquire it, hold, and use it.
How does Monero work?
Quite simply, Monero at its core is very similar to Bitcoin. Every user has addresses they receive funds to, you send to any address on the network, and miners process transactions and add them to blocks. But what separates Monero from the crowd is that every sender and receiver gains strong privacy from outside observers in three key ways.
Protecting the sender
When you send Monero, unlike Bitcoin there is no way to tell when looking at a standard transaction what inputs are being spent. Instead of plainly revealing the true spend, Monero uses something called "ring signatures" to provide plausible deniability, making every input just one of 16 possible inputs in each transaction. These 15 other decoys are real transaction outputs from previous Monero transactions, and could plausibly be the true spend to any outside observer. Only the sender knows which input is the real one!
If you want more detail on ring signatures, you can read up on them here:

Protecting the amounts
In most cryptocurrencies, the amounts involved in every transaction can be viewed by anyone with access to an internet connection and a web browser, but not so with Monero. Every transaction in Monero uses something called "confidential transactions" to hide the amount of every input and output, making it impossible for an outside observer to know the amounts involved in any transaction on the network.
All of this can be done without sacrificing the ability to audit the supply of Monero thanks to some brilliant cryptography originally developed for Bitcoin; a zero-knowledge proof called a "range proof." Every transaction has its amounts validated by miners and node-runners to ensure that the inputs and outputs balance, without revealing the actual amounts to any outside observer. Cryptography is awesome.
If you want more detail on confidential transactions, you can read up on them here:

Protecting the receiver
Now onto the last major aspect of transactional privacy – the receiver. In Monero, all addresses used are known as "stealth addresses" or "reusable payment codes," and allow any person to share an address publicly without revealing any past, present, or future on-chain addresses. This is done by having the sender in each transaction derive a new address using two keys in the Monero stealth address, allowing them to create a transaction to a public address without ever revealing that connection. As an example, try to look this address up in a block explorer like xmrchain.net:
888tNkZrPN6JsEgekjMnABU4TBzc2Dt29EPAvkRxbANsAnjyPbb3iQ1YBRk1UXcdRsiKc9dhwMVgN5S9cQUiyoogDavup3H
What did you find? Thankfully, stealth addresses mean that no address you see in your wallet can ever be cryptographically linked to an on-chain address or transaction.
Want to learn more about stealth addresses in Monero? Learn more here:

Where to get Monero
As the global fiat regime has cracked down on access to Monero by putting pressure on banks that serve cryptocurrency exchanges, the Monero community has quietly been building and improving tools to make it easier and more private to acquire regardless.
LocalMonero
LocalMonero is a centralized peer-to-peer exchange, helping users find other real people locally or online to trade fiat or cryptocurrency for Monero. It's extremely easy to use and has great protections via a reputation system, dispute system, and arbitration bonds. Simply find an offer that fits the price your looking forward and the currency you want to trade for Monero, start the trade, and follow the instructions on-screen.

Where to go: LocalMonero.co or their Tor Onion site
Currencies supported: most fiat currencies and cryptocurrencies like Bitcoin
Get started: How to Buy Monero Online | LocalMonero
Trocador
Trocador is an aggregator of instant exchangers that support Monero, making it far easier to not only find a good price but also find an instant exchanger with a good reputation. Trocador investigates the exchanges they list and even guarantees your trade with any exchange up to a certain amount in case of any issues. Be sure to check the grade that each exchange has and factor that into which offer you want to take before trading, as the worse the grade, the higher possibility of "shotgun KYC" before you're able to get your funds or other difficulties.
Note that you can also use Trocador directly in the Cake Wallet and Monero.com wallets that we'll discuss later.

Where to go: Trocador.app or their Tor Onion site
Currencies supported: only cryptocurrency <> Monero swaps
Bisq
Bisq is a decentralized peer-to-peer exchange built on the Tor network, enabling anonymous trades between people online. Bisq has a bit of a steeper learning curve but provides excellent privacy and protections for users, while also being the only decentralized (and therefore more resilient) option today for acquiring Monero.
Bisq at its core leverages the Bitcoin network for trade fees, escrow, and more to secure trades. As such, when Bitcoin network fees are high trading on Bisq can be cost prohibitive, so keep that in mind.

Where to go: Bisq.network
Currencies supported: only Bitcoin <> Monero swaps
Tips and tricks for using Monero
Now that you've gotten some Monero from one of the exchanges above, how do you take self-custody and use it?
Monero wallets
The first step to gaining privacy from Monero is actually holding the keys to it yourself, and there are some fantastic wallets available in the Monero ecosystem.
Mobile
On mobile, the best two options are Cake Wallet (or their Monero-only app, Monero.com) and Monerujo, two open-source and user-friendly options. One key benefit for many users of Cake Wallet is that they also support Bitcoin directly, and have in-app exchange functionality that leverages Trocador under the hood.
Note that Cake Wallet is on iOS and Android, while Monerujo is Android-only.


Desktop
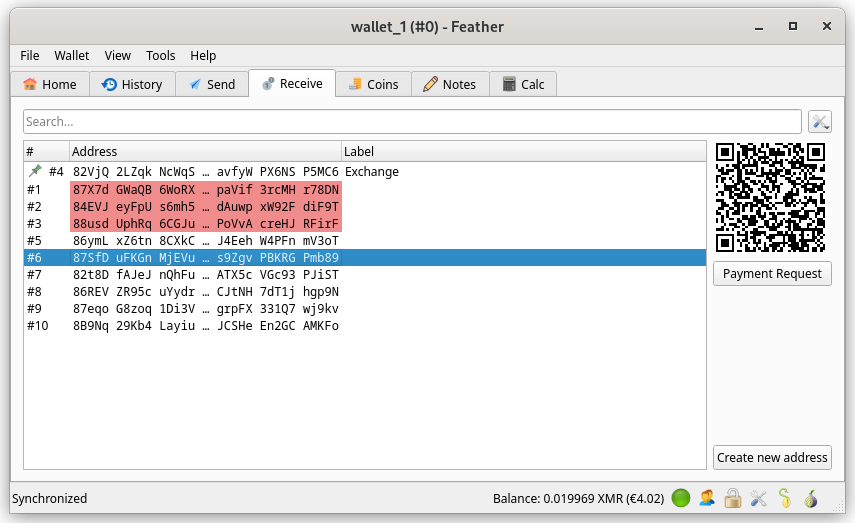
My favorite Monero wallet for desktop is Feather Wallet, an amazing, open-source wallet in the vein of Electrum but with immensely powerful features built for Monero.
Another great wallet is the "official" desktop wallet built by the Monero community, also sometimes called the "GUI" wallet (much to my chagrin).

What to know
There are some key differences to be aware of when using Monero, especially if you're used to the standard Bitcoin wallet approach to sync and spending. Here are some quick tips to be aware of:
- Monero wallets are "full" wallets, and connect to full nodes directly. As such, they don't offload sync by sending addresses or public keys to a remote server, and instead download the necessary data from every Monero block, check for received funds, and continue on to the next block.
- This has immense privacy advantages, but does mean that synchronizing a Monero wallet will take much longer than a standard Bitcoin wallet.
- If you don't spend frequently, try to just open your wallet and let it sync every now and then to minimize the amount of time you'll have to wait for sync the next time you use your wallet.
- Note that there are already efforts in progress to enable better background sync for Monero wallets, and Cake Wallet already implements a background sync functionality.
- When spending Monero, the change you receive back in a transaction is locked for privacy reasons for 10 confirmations before it is spendable again. If you only have one Monero output this can mean you can't quickly spend again, forcing you to wait for ~20min before your change output is spendable.
- Monerujo has worked around this with an awesome feature called "Pocket Change":

- Monero has two general types of addresses, "main" addresses that start with a
4, and "sub-addresses" that start with an8.- Best practice in Monero is to share a new sub-address with each entity you transact with, but this isn't strictly necessary.
Conclusion
While this is merely an introduction to Monero and how to acquire and use it, keep an eye out for future pieces that go into more depth! Monero is a valuable tool for everyone to explore adding into their toolkit, and is worth the time to try it out and see how it works for you.
Financial privacy is critical to human freedom, and Monero is one of the best tools around at providing it. Unfortunately, there is often push-back in the Bitcoin community against anything that isn't Bitcoin, with common fear, uncertainty, and doubt ("FUD") being spread about Monero. If you want a better idea of these common complaints and answers to them, you can read a previous blog post of mine on the topic here:

Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step than to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:


The war against financial privacy has just gone up a notch with the recent arrest of Keonne Rodriguez and William Lonergan Hill, the developers and operators of Samourai wallet, who are being charged with conspiracy to commit money laundering and conspiracy to operate an “unlicensed money transmitting business.” In the indictment from the Southern District of New York, it is alleged that from around 2015 to at least February 2024, Rodriguez and Hill operated Samourai as an unlicensed money transmitting business, earning millions of dollars in fees. Samourai is accused of executing anonymous transactions worth over $2 billion, with a significant portion being proceeds from criminal activities such as darkweb market sales, wire and computer fraud schemes, among others.
Message passing is not money transmission
The key absurdity of these charges is that coinjoin facilitators, like Samourai, act solely as message transmitters; similar to the SWIFT network. They are NOT money transmitters or facilitators in the traditional sense; they merely pass data packets to connected clients. Importantly, clients never relinquish custody of their funds to Samourai or any third party. This collaborative approach between clients distinguishes coinjoin transactions from traditional money transmission services. In short, operating software that suggests transaction templates to end-users without taking custody of funds does not constitute money transmission, even if the template includes an output directed to the service provider.
The indictment also cites specific tweets made by Samourai, alleging that they were open invitations for criminals and "Russian oligarchs" to launder money and evade sanctions through the company's services. However, upon closer examination, a strong argument can be made that these tweets were intended to be humorous and sarcastic, but we will leave that one for the courts to decide. What is undeniably true is that this action is a perfect example of the escalating hostility of the fiat system’s gatekeepers, towards any form of financial privacy. Apparently, their default position is to label any attempt to maintain financial privacy as money laundering, and anyone who develops tools that facilitate this is seen as an accessory to crime.
Financial privacy != criminal activity
This unfortunate conflation of financial privacy with criminal activity not only influences the perceptions of authorities but also seeps into the public consciousness, creating a negative perception of open-source technology. In other words the simple act of moving money privately may be criminalized, which raises significant concerns. The ineffectiveness of Anti-Money Laundering (AML) laws exacerbates the situation. Research indicates that the AML compliance costs incurred by banks are significantly higher, approximately more than 100 times greater than the amount of laundered money seized. Furthermore according to the Journal of Financial Crime 25(2), AML laws are "almost completely ineffective in disrupting illicit finances and serious crime,” as they only manage to seize a paltry 0.1% of illicit funds. To put that in perspective, American financial institutions spend approximately $50 billion annually in AML compliance costs, while stopping only 0.1% of the estimated $2 trillion in financial crime committed each year! While this may not be an argument that can hold up in court in Samourai’s favour, it is still worth noting that the banking system and fiat currencies are still by far the preferred channels for laundering money by criminals, but I digress.

The war on financial privacy
To anyone that has been paying attention this isn’t really much of a surprise, especially as regulators have been targeting “mixing services” and their developers for a while now. In April 2021 Roman Sterlingov was arrested at Los Angeles International Airport for facilitating the laundering of over 1.2 million bitcoin – worth over $760 million at today’s prices – tied to the darknet, in his capacity as the operator of the mixer, Bitcoin Fog. Sterlingov was found guilty of these charges and faces at least 20 years in prison based primarily on chain surveillance data; a verdict his lawyers have vowed to appeal.
The Sterlingov case is particularly concerning because the government was able to establish criminal venue solely by contacting Bitcoin Fog's customer service to inquire about the possibility of using the platform for laundering drug-related funds. Prior to his arrest, Roman, a Russian citizen, had never visited the United States. However, he was tried in Washington, D.C., raising concerns about the violation of the venue clause in the Sixth Amendment of the U.S. Constitution. In other words if the appeal is unsuccessful, the consequences would set a bad precedent that would grant the U.S. government jurisdictional authority over the internet. This means that any prosecutor in the United States could conduct a transaction on a website and potentially charge the owner of the site with a crime in the location where the prosecutor is based. The only thing Roman is guilty of is trying to protect his financial privacy.
In August 2022 the US Treasury Department sanctioned Tornado Cash (TC), an open source Ethereum based mixing service, and one of the developers working on TC, Alexey Pertsev was arrested on money laundering charges similar to those faced by Sterlingov, Hill and Rodriguez. Coincidence? Perhaps not, and it seems that privacy is the next battleground as the fiat overlords seek to maintain control over the financial system and preserve the financial surveillance powers that they have quietly amassed since the early 20th century.
Bitcoin is permissionless at the base layer and the permissioned fiat system’s power is derived from its ability to surveil and sanction enemies of the state, whether they be individuals or other nation states. These recent arrests are attempts to neuter and co-opt Bitcoin, and similar open source tools that will enable financial privacy for individuals that want to remain sovereign. In order to defeat this regulatory overreach that stems from desperation as the fiat system slowly crumbles under its own weight, the need for more decentralized and private by default tools has never been greater. As Eric Hughes pointed out in the Cypherpunk Manifesto, “We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place.” Developing such systems however, will now need to be done differently and intelligently given the battles ahead and the ongoing clamp down against privacy.
Conclusion
The time has now come to throw off the shackles of serfdom that the fiat gatekeepers insist we keep on. We have come to accept surveillance of our financial affairs and asking for permission to use our money from banks as normal. Without the right to privacy, you have no freedom; financial or otherwise. The promise of Bitcoin is that of a “peer to peer, electronic cash system that enables transactions without going through financial institutions”, true financial sovereignty. It’s this promise that they wish to extinguish while continuing to perpetuate their fiat monetary colonialism on the world.
If there is to be a silver lining in this debacle, it’s the opportunity for a case law precedent to be set for Bitcoin that is on the same level as Bernstein vs. DOJ, the case that enshrined code as speech; thus affording it protection under the First Amendment. Financially supporting Samourai’s legal defense will be pivotal in this regard. Privacy is not a crime.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

One of the things I touched on in my last article for Freedom.Tech was the importance of understanding how Samourai Wallet worked in order to better understand the illogical premise these charges stand on, but we only briefly covered it.

In this post, we'll dive a bit deeper into the architecture of Samourai Wallet's app and services to get a grasp on why their service would normally be considered legal, what some of its weak points were, and help us better understand the case for and against Samourai right now.
Let's start from the ground up.
Samourai Wallet sync
At its core, Samourai Wallet was a self-custodial "light-client" Bitcoin wallet. What that means in practice is that users of Samourai Wallet always had full custody of their funds but users without their own node relied on a remote server – operated by Samourai Wallet – in order to get balances, check for received funds, and send transactions like many other Bitcoin wallets.
The default mode of Samourai Wallet is for a user's wallet to send their extended public key ("xpub") to Samourai's back-end server, allowing Samourai's server to check for any transaction history for the user and relay that information back to them. While this makes sync very fast for the end-user and low on bandwidth usage, it reveals all transaction data past, present, and future to Samourai Wallet and anyone else with access to the xpub.
The Samourai team stated that they only cached these xpubs temporarily when a user requested sync information, purging them after they were no longer needed and not storing them in perpetuity. To avoid this potential privacy leak, advanced users were able to either run their own back-end server (called a "Dojo") or use an alternate wallet that could still leverage Samourai's privacy tools called Sparrow Wallet. Both of these approaches did not reveal addresses or balance information to Samourai Wallet in any way.
You can read more below:
https://blog.ronindojo.io/most-whirlpool-users-run-dojo/
Whirlpool
The core privacy tool offered by Samourai Wallet was known as "Whirlpool," and offered users the ability to break the deterministic (read: easily traceable) links between their past on-chain activity and future activity to outside observers. Whirlpool did this by bringing together 5 different users (or more, in what are called “surge cycles”) looking to gain privacy for the same-sized coin (i.e 0.01 BTC), helping them communicate their intent, and then allowing those users to construct and publish a collaborative transaction (also called a “CoinJoin”) together. When constructing these transactions, the 5 participants and coordinator work together in a way that does not reveal to them which participant receives which output, except their own.

What is often misunderstood about Samourai is that a user never gives up custody of funds and never receives someone elses funds. At all times when searching for a mixing round, participating in a collaborative transaction, or broadcasting the transaction the owner of each input only has control over their own input, and no one elses. Samourai wallet’s role in this process is to “pool” liquidity, making it easier to find other peers who want to mix the same size inputs, assist in communication between peers, and broadcasting the final signed transaction. Essentially, Samourai Wallet’s coordinator server acted as a glorified bulletin board and message courier, and not a custodian or money transmitter.
The basic flow of a mixing round looked like this:
- A user submits an input they want to mix to the Whirlpool server over a unique, one-time Tor connection.
- The Whirlpool server approves the input’s registration.
- The user waits for enough peers to be found by the coordinator (usually four).
- Once enough peers are available, all peers in a round register their output with the coordinator.
- Once all outputs are registered, the coordinator sends a partially-signed Bitcoin transaction containing the registered inputs and outputs of all participants to each participant.
- Each participant validates that the PSBT sends their input to themselves as an output, and signs the transaction.
- Once all participants have signed the transaction, the Whirlpool server broadcasts the signed Bitcoin transaction to the Bitcoin network.
What is “remixing”?
Once a user has sent their initial inputs through a Whirlpool transaction, they can then either immediately send those funds somewhere else, or participate in what was called “remixing.” Remixing is the ability for Whirlpool users to queue up their already-mixed outputs to join in further rounds of Whirlpool to increase the privacy of their outputs by adding additional potential flows of funds. In order to incentivize better privacy over the long-term, Samourai Wallet did not charge a service fee or a mining fee for remixes, with all fees for each Whirlpool round being paid for by new, unmixed inputs.
Remixing was done primarily by those who ran their own Dojo back-end or utilized Sparrow Wallet, as remixing on mobile was difficult and inconsistent due to battery and network concerns. Remixing also meant that gaining strong privacy was something that happened over weeks or even months, and not overnight, a major hurdle if illicit actors sought to use Samourai Wallet for their purposes.
https://twitter.com/laurentmt/status/1783589772021071973
Ricochet
The other service mentioned in the indictment was the Ricochet spending tool. Ricochet allowed users to put “hops” between themselves and a final spend to a recipient, giving additional plausible deniability (and thus privacy) when transacting. Just like Whirlpool, this service never allowed Samourai Wallet to take custody of funds or alter the flow of funds at any point.
Note that there was the ability for Dojo users to manually schedule out transactions using the “TX Scheduler” tool in Dojo to avoid paying a fee or interacting with Samourai Wallet’s servers.

The basic flow of a Ricochet transactions looked like this:
- A user sets a destination address, if they want the transactions broadcast quickly or in a staggered manner, and provides the final destination address.
- A user’s wallet signs a set of Bitcoin transactions accomplishing this thread of transactions.
- The user’s wallet submits this set of pre-signed Bitcoin transactions along with a fee to the Samourai Wallet servers.
- Samourai Wallet’s servers simply accept the fee and broadcast the transactions requested by the user.
As all transactions are signed client-side, the server has no way to take custody of funds or alter the flow of funds in any way without invalidating the signatures on those transactions.
Other Samourai Wallet privacy tools
Even though the following tools were not explicitly mentioned in the indictment, it’s valuable to take some time to better understand how they worked and what role Samourai Wallet as an entity did or did not play in their function.
STONEWALL
STONEWALL was the default way that funds were spent in Samourai Wallet after going through Whirlpool (if the wallet had enough unspent coins). This transaction type did not involve any Samourai server or other peer, and occured entirely locally in the user’s wallet. Ultimately, a STONEWALL transaction created a “fake” 2-person collaborative transaction, giving additional plausible deniability on which input is linked to which output.

As STONEWALL transactions were all performed locally, Samourai Wallet of course could not take custody of funds or alter the flow of funds in any way.
STONEWALLx2
As the name implies, STONEWALLx2 is similar to a standard STONEWALL transaction, with the exception of actually involving another peer to create the transaction. This type of transaction obfuscated which inputs are owned by which entity, and where the funds ultimately are going.
STONEWALLx2 did not utilize any Samourai Wallet servers or services, and was directly coordinated by the two parties involved in the transaction, either in-person via a QR code exchange, or online via the Tor network. Users connected to each other using their PayNyms (a centralized directory of BIP 47 payment codes turned into usernames).
The only exception to this rule was the recent release of “Joinbot,” a service run by Samourai Wallet themselves that acted as the other peer in STONEWALLx2 transactions and collected a fee for the service. Even when Joinbot was used, Samourai Wallet could not alter the flow of funds or take custody.

As STONEWALLx2 transactions were all performed peer-to-peer, Samourai Wallet of course could not take custody of funds or alter the flow of funds in any way.
STOWAWAY
STOWAWAY was an implementation of the concept behind PayJoins, a type of collaborative transaction that looks like a simple Bitcoin payment on-chain but actually involves two parties. Not only does STOWAWAY obfuscate the flow of funds, it also hides the amount being sent in a transaction. Just like in a STONEWALLx2 transaction, a STOWAWAY is entirely peer-to-peer, with users manually connecting to each other using PayNyms and communicating via the Tor network or an in-person QR code exchange.

As STOWAWAY transactions were all performed peer-to-peer, Samourai Wallet of course could not take custody of funds or alter the flow of funds in any way.
Key takeaways
The vital thing to recognize about the functionality of Samourai Wallet’s app and services is that they never had the ability to take custody of user’s funds, never had the ability to alter the flow of funds, and ultimately acted as a simple message passer in functionality. When viewed in the light of the technical functionality of Samourai Wallet, the charges quickly fall apart.
Conspiracy to operate an unlicensed money transmission business
We’ve covered this specific charge at-length in our article on the Tornado Cash founder’s indictment by the DoJ, but by all previous legal precedent and regulation there are no grounds for considering a self-custodial wallet and service to be considered a money transmitter. From our previous article:
In a fantastic working paper released shortly after the indictment was unsealed, the International Academy of Financial Crime Litigators broke down what I think is the clearest view of FinCen’s money transmission definition (emphasis theirs):
“This brings to the forefront a crucial distinction: to act as a money transmitter, a party must have necessary and sufficient control over the value being transmitted.”
What is “necessary and sufficient control” you may ask? “Necessary control” in this case can be viewed as the tool being a required component of someone transmitting money. “Sufficient” control can be viewed as the owners of the tool having actual custody and ability to move deposited funds without user interaction.
While you can absolutely argue that Samourai Wallet’s app and servers had necessary control over the value being transmitted through their app when using the default back-end, and through Whirlpool, as they never took custody of user’s funds there is no grounds for considering them to have had “sufficient” control at any point in time. Thus, according to FinCen’s own definition they should not be considered a money transmitter in our view.
Conspiracy to commit money laundering
Similarly, the case of the DoJ on the charge of money laundering typically hinges on custody. It helps to use analogies in these situations to get a better grasp of the concepts in play, as we also did in our article on the Tornado Cash indictment:
To make the absurdity of this claim more vivid, let’s apply it to the use of cash to launder money. If any tool that is used in the act of money laundering is considered complicit, why don’t we also indict the makers of armored trucks that are used to move cash for banks? While armored cars may be necessary for banks to launder money, they never have sufficient control as the manufacturer doesn't take custody of funds – only the bank does.
Banks are by far the largest conspirators in the act of money laundering globally, and yet we don’t fault any of the service providers or manufacturers whose products are used in these money laundering schemes. Unlike most banking-related money laundering cases, however, the DOJ seeks to hold an individual accountable for merely building a tool that was allegedly used for money laundering by North Korean hackers.
While in this scenario armored car manufacturers do make an indirect profit off of creating a tool that could potentially be used in the act of money laundering, they are in no way held liable for the way their tool is used. So why should a service that never has custody over a users funds be considered a tool for money laundering?
It’s clear to me from the fact that the DoJ only seeks to bring conspiracy charges against the founders of Samourai Wallet that they are less concerned with what the Samourai Wallet app and service actually did and more concerned with expanding the reach of their financial enforcement arm through precedent instead of through legitimate legislation.
More resources
If you want to deep-dive into the architecture and details of how these tools functioned, the Samourai Wallet docs site is still live as of publishing. Below you can find detailed information on all of the tools mentioned today:



Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

In an absolutely shocking turn of events, the United States Department of Justice has moved on from Tornado Cash to the next privacy tool in the cryptocurrency space on their list – an incredible Bitcoin wallet called "Samourai Wallet." While the war on privacy in the space is nothing new, the US government has been escalating their attacks more rapidly than anyone foresaw.
Taking the blueprint from their indictment of the Tornado Cash founders, the DOJ is now indicting the two founders of Samourai Wallet, charging them each with one count of conspiracy to commit money laundering (20y maximum sentence) and one count of conspiracy to operate an unlicensed money transmitting business (5y maximum sentence). Thankfully this is only an indictment, and both founders are technically considered innocent until proven guilty, and we at Freedom.Tech and Foundation will be doing our best to raise public awareness on this issue and fight for our right to privacy.
To better understand how incredibly illogical this prosecution is, we have to first explain briefly how Samourai Wallet worked.
How Samourai Wallet worked
Samourai Wallet, unlike many of the other Bitcoin mixers previously prosecuted by the DoJ, had one vital difference – they never took custody of users funds. Samourai Wallet was an entirely self-custodial wallet, requiring users to save their seed phrase and passphrase in order to restore funds. While it did provide privacy features like Whirlpool and Ricochet as mentioned in the indictment, at its core it was a self-custodial Bitcoin wallet.
For the average user of Samourai Wallet the default mode of operation for Samourai Wallet was for the users wallet to send their "xpub" (a master public key allowing derivation of new addresses but not spend funds) to a Samourai Wallet back-end server in order to sync their balance and get new addresses. While this architecture has some privacy disadvantages, it does make the sync process trivial even for those with very poor internet connections, and allowed Samourai to run a simplified architecture as well.
There were, however, ways to prevent sending this data to Samourai, either by running your own back-end server (called a "Dojo") or using an alternative wallet to interact with Samourai's privacy tools, called Sparrow Wallet. The core privacy tool that was used in Samourai Wallet was known as "Whirlpool," and allowed users to gain forward-looking privacy and disconnect their previous transaction history from future activity.

There are two vital things to understand about Whirlpool and how it functions:
- Samourai Wallet never has custody of funds nor say in where funds are sent.
- Each user retains full custody of funds, and their wallets will only sign transactions that ensure their funds are sent back to them in the Whirlpool round.
- Samourai Wallet merely helps each of the 5 users communicate their intent and talk to each other, making it easier to find other people trying to gain privacy for UTXOs of the same size.
Ricochet, the other tool mentioned in the indictment, simply allowed users to put distance on-chain between them and a previous transaction, giving more plausible deniability to their activity.

What's also vital to understand when it comes to Ricochet is that Samourai Wallet never has custody of funds or any say in where funds are sent. Samourai Wallet merely accepted Bitcoin transactions you signed via the Samourai Wallet app and sent to them to broadcast to the Bitcoin network at random intervals. As you alone held your private keys that signed these transactions, they could not be altered in any way by the Samourai Wallet server.
Before the case against Tornado Cash, the technical function of Samourai as a self-custodial wallet would traditionally be enough to absolve them of any responsibility to register as a money transmission business or perform onerous KYC/AML regulations on their users, as they are never materially involved in the execution of transactions. For a deeper dive on these two issues, you can read our previous piece on the Tornado Cash indictment as they have a similar technical functionality and face the exact same two charges:

Actionable next steps
While all of this is a bit political and philosophical, I wanted to leave you with actionable next steps, especially if you were already a user of Samourai Wallet or Sparrow Wallet. I'll break down below what you should be aware of and what you should do in each of the main ways people used Samourai Wallet.
As a privacy advocate
While it may seem too simple, the first and most important way that we can all take up the fight for privacy is to keep talking about this case and its implications. The moment we are silent and let the DoJ prosecute Samourai Wallet in the dark, we have lost. We each have a platform that we can leverage to get the word out there, push back on the DoJ's narrative, and explain to people how vital privacy is and how much the government wants to prevent easy access to it.
You have a unique platform, use it! Share this post, talk about this case on your favorite social media platform, or simply explain this case to your friends and family.
As a Samourai Wallet user (no Dojo)
Unfortunately, the architecture of Samourai Wallet meant that your xpub (a master public key, allowing anyone holding it to derive all your past/present/future Bitcoin addresses) was at some point in time held by Samourai, and could now possibly be in the hands of the DoJ.
Though it's a worst-case scenario, you should assume that your xpub was compromised, and thus all previous mixes you have done have been unwound and are now traceable. You should also assume that the government can now derive all past/present/future addresses of yours and track movement of funds if so desired.
In addition, Samourai's coordinator and backend sync server was seized, meaning that Samourai Wallet's app will no longer sync, show received funds, or allow sending funds out. As such, you have to migrate funds to another wallet like @SparrowWallet using our tutorial here:

In addition, I would recommend migrating funds to a new seed phrase to prevent anyone holding the xpub from seeing all future received/spent funds.
You should also disable automatic updates in the Play Store or F-Droid (if used) to ensure no malicious updates are pushed.
As a Samourai Wallet user (using your own Dojo)
Thankfully, you avoided having your xpub potentially compromised. The worst case scenario for you is that your previous mixes may not have the full anonymity set you expected if non-Dojo users xpubs were compromised.
You will still be able to sync/send/receive from your Samourai Wallet app, but should also migrate funds to another wallet as no further updates will come out for Samourai Wallet. To migrate to Sparrow Wallet, you can use our tutorial here:

You should, however, disable automatic updates in the Play Store or F-Droid (if used) to ensure no malicious updates are pushed.
As a Sparrow Wallet user
Thankfully, you avoided having your xpub potentially compromised as well. The worst case scenario for you is that your previous mixes may not have the full anonymity set you expected if non-Dojo/Sparrow users xpubs were compromised.
There is no real need to rotate to a new wallet as Sparrow remains an excellent option. Unfortunately you will no longer be able to mix and gain privacy in Sparrow as the Samourai coordinator was seized.
Next steps for privacy
If you (like me) relied on Samourai Wallet for privacy on Bitcoin, it is sadly time to look elsewhere. As of today I have two recommendations:
Use Monero for spending, keep using Bitcoin for savings
Yes, this isn't Bitcoin, but its by far the most used and most practical privacy coin out there with strong (and growing) ways to swap in/out of it without a centralized, KYC exchange. My recommendation is buying enough to cover your normal spending of Bitcoin for a month at least, and spend out of that lump sum as needed.
As the tools for privacy on cryptocurrencies like Bitcoin and Ethereum are being shut down daily, the importance and value of Monero's consensus-level, decentralized approach to privacy only grows. There has never been a more vital time to learn about it and consider using it.
Learn more:
Where to get Monero:
LocalMonero, a peer-to-peer exchange
Bisq Network, a decentralized peer-to-peer exchange
Trocador.App, an instant exchange aggregator
Cake Wallet, a Bitcoin and Monero wallet with in-app exchange
Wallets:
Feather Wallet, a fantastic Monero desktop wallet
Cake Wallet, a Bitcoin and Monero wallet
Monerujo Wallet, a fantastic Monero wallet for Android
Merchants that accept Monero:
Use JoinMarket
JoinMarket is a decentralized Coinjoin protocol that brings together peers to mix funds together, gaining strong privacy without relying on a central coordinator, without giving fees to a central entity, etc.
The best way to get started today is using the new UI built around JoinMarket, @jamapporg:

Conclusion
This has been an incredibly sad day in the history of Bitcoin, and in the history of freedom tech, but not all hope is lost. We can each play a role in fighting back and acting in public, civil protest against the prosecution of open-source developers running non-custodial privacy tools. We're also hard at work at Foundation to organize Bitcoiners, Bitcoin companies, and privacy advocates behind the defense of the Samourai Wallet team, including exploring a defense fund if necessary. Keep an eye out for updates there!
Thank you for taking the time to read through this today, and I hope it helps you know what's going on and where to turn next.
Onwards.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

For those of you directly affected by the indictment of the Samourai Wallet founders and seizure of their servers, we wanted to help simplify the process of migrating your funds to a new wallet as much as possible. Thanks to the help of two incredible Bitcoiners, this post will walk you through the process from start to finish in the latest versions of both wallets, making it as easy as possible to migrate and keep using your freedom money.
To learn more about why this process is necessary, read our latest article on the indictment itself below:
Video Tutorial
The fantastic Bitcoin QnA has taken the time to create a screen-recorded video guide for this entire process, which can greatly help simplify things as you can see the process play out in real time, pause when needed, and follow along. This video guide also covers the ability to export your Samourai Wallet backup file and import directly into Sparrow, functionality that was coincidentally released yesterday and extremely helpful in this process.
For those who prefer the written form of this restoration process, please keep reading below the video!
Importing your existing Samourai Wallet into Sparrow Wallet
Please be sure to read the entirety of the post to familiarize yourself with the process before proceeding! Before starting, you will need the following:
- Your Samourai Wallet seed phrase (12 words)
- Your passphrase
- Sparrow Wallet downloaded and installed on to your computer (https://sparrowwallet.com/)
1 - Configure your server
The first step in setting up Sparrow Wallet is to configure which server you want to connect to. If you run your own Electrum/Fulcrum server or run a local instance of Bitcoin Core, it's best to connect to your own node here!

2 - Connect to your selected server and create a new wallet
Toggle on your server using the switch on the bottom right. It should turn yellow, green or blue depending on what you've selected.
Now click "Import Wallet" in the center of the window:

3 - Import your Samourai Wallet seed and passphrase
On the dropdown menu besides the Mnemonic Words (BIP39) section, select "Use 12 words." Type your seed into the fields displayed in the correct order from 1 to 12.
Check the "Use passphrase?" option. Keep in mind to enter your passphrase carefully, as any typo will restore a completely different, empty wallet.
Then click "Discover Wallet" and then "Import Wallet."
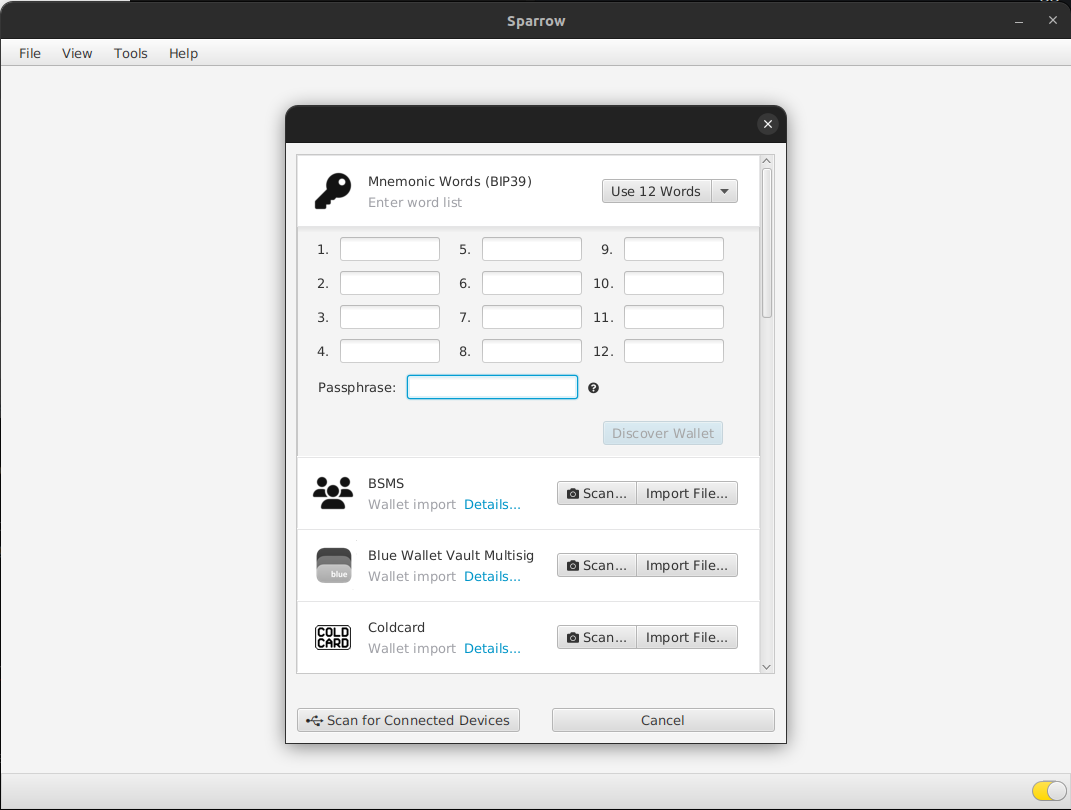
4 - Add a wallet password (optional)
Sparrow Wallet allows you to password-protect wallets, requiring a password to be entered before the wallet files can be decrypted and opened in Sparrow. This step is optional, but recommended, and should use a different password than your passphrase.

5 - Add accounts
In the bottom of the settings page, you will see ‘Add Account…’ button. Click on it.

From the dropdown menu, select "Whirlpool Accounts."

6 - Wallet sync
Your wallet will be scanned by the server you have selected. You should also be able to see your respective Deposit, Premix, Postmix and Badbank accounts.

You should now be able to send your bitcoin to another wallet/address of your choosing. I would recommend sending this out to a hardware wallet.
Notes
- Be sure you obtain sparrow wallet from sparrowwallet dot com. Get it right!
- Because you are inputing seed words into a computer, do your best to ensure your computer is secure. Be wary of dodgy browser extensions.
- Dojo users need not worry. This is for those who used the default Samourai Wallet back-end.
- Beware of scammers on the Sparrow Telegram chat. They're out in full force today. Nobody will ask you for your seed words. Do not give them out to anyone.
Conclusion
If you run through these steps and still have issues, we highly recommend joining the Sparrow Wallet Telegram chat for support, keeping in mind that no one there will ever ask for your seed phrase:

Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

Satoshi Nakamoto was keen on email aliasing when Bitcoin was in development.
As bitcoiners ourselves, there’s a lot we can learn from how Satoshi navigated the internet, and more importantly, why they were so keen on privacy tools like email aliases.
In today’s internet, spam, fraud, and other invasive pitfalls are everywhere. Simply clicking on the wrong link can mean you lose the Bitcoin on your hot wallet or give up your personal information to an anonymous rogue actor across the globe. Especially in the world of Bitcoin, the websites and platforms we use are hot-spots for criminals looking to catch you in a mistake.
It’s thus critically important that we adopt similar privacy standards for ourselves that cypherpunks like Satoshi did – especially if we’re socially active in the Bitcoin community. As adoption grows, so too will the number of bitcoiners getting targeted for their coins.
Email aliasing is one of many ways you can protect yourself from this targeting.
What is email aliasing?
Email aliasing is an essential practice for anyone who wants to enhance their online privacy.
An email alias is a unique identifier you can use in place of your real email address so that you can privately receive emails. It redirects emails from senders to your primary inbox without revealing your real email address, so it functions as an email forwarder, not as an independent mailbox.
Not only do email aliases help keep your identity safe, but they can also improve your efficiency and flow of information.
Let’s say you have one primary email address, but you use individual email aliases with three particular websites that you visit often. You can use multiple email aliases to route incoming emails to the same singular email address:

Imagine you have a basic email, [email protected], that you use for multiple different services, like Amazon, Netflix, your bank account, social media, etc. Now let’s say just one of these services experiences a data breach. Now that your email is compromised, the attacker can target you and link that email to all of your other accounts, giving them a much greater chance of breaching into one of them.
By using an email alias individually for these services instead, you cut the attacker off from learning about your other accounts. All of the information they steal would only relate to that specific singular alias, which you could then simply scrap and replace with a new one.
Why use an email alias?
Using an email alias naturally falls in line with the principles of good online privacy and security.
Instead of asking yourself why you should use an email alias, instead ask yourself, “Why should I have to disclose my real email?”
The way that the internet operates today, it’s commonplace to share way too much unnecessary private information to other companies. While companies often say it’s “for your safety” or for verification purposes, these data collection practices often end up harming people instead.
An email alias is one of many easy ways to take back the privacy that you have a right to when using the internet. You’ll avoid spam more easily and ensure that your actual email remains private to you and your email provider (or just you alone if you choose to self-host your email).
But beyond the first principles of privacy, email aliasing will also make your life easier:
- Even if the alias is compromised and somehow gets trapped in the endless flow of spam email, or you wish to simply cut communications ties from that alias, you can scrap the alias and start fresh with a new one without deleting your actual account.
- You’ll feel more organized since you have a choice of different channels to communicate with different parties.
- It will give you more confidence in your online experience since you can communicate with others without risking anyone tying your messages back to an account that may be linked to your identity.
This last point was probably particularly beneficial for Satoshi, who subjected themselves to immense scrutiny from criminals and governments alike by creating and posting about Bitcoin online.
Setting up your email alias
For a paid option, you can generate your own email alias using an open-source provider like SimpleLogin.io. Simplelogin respects user privacy, doesn’t collect ads or use trackers, and even enables you to self-host SimpleLogin on your own server if you want maximum privacy.
For free email alias options, try DuckDuckGo, FireFox Relay, or Addy.io.
You can also take advantage of the built-in email alias generators that come with popular private email services, such as:
- Proton Mail (free or paid)
- Note: Proton now owns SimpleLogin, and thus uses them for their email aliasing service.
- Tuta (free or paid)
- StartMail (paid)
All of these services accept Bitcoin as payment, and they all offer built-in email alias creators in case you don’t want to use a third party service like SimpleLogin.
Email aliasing is an essential practice for optimal online privacy, but if you’re using them with a privacy-invasive email like Gmail, that’s like installing a high-tech security system to your house, but then leaving all the doors unlocked so it’s easier for you to get in and out of the house.
Many people love the convenience of email platforms like Gmail, but if you’re here to enhance your privacy, then you’ll have to sacrifice some of that convenience.
After creating an alias using one of the platforms mentioned here (or another if it suits your needs), simply enter these aliases in place of email addresses when signing up for platforms, making online purchases, or while in communications with other parties.
Practical applications of email aliasing
In the mainstream world, you mainly see companies using multiple different email aliases that they use for customers to reach various departments of the company, but it’s not likely that your friends are sharing an alias with you when you’re trying to send something to them online.
As an individual, your needs likely aren’t the same as a large organization’s. So how can you use an email alias?
1. Reducing spam: By using unique email aliases for different services, you can identify which of them may be selling your information or sending unwanted emails. If one alias starts receiving spam, you can simply scrap and replace it without affecting other communications.
2. Testing/temporary sign ups: Whenever you sign up anywhere online, you’re entering your information into a database that can be hacked at any time, and are being hacked at an increasing rate. If you’re trying out a new website or want to create an account and explore gated content, using an email alias for these instances is a great way to keep yourself private during the process so that you don’t unnecessarily add your personal information to a list for the darkweb to exploit.
3. Social media signups: Whenever you sign up for social media, it’s always a great idea to use an email alias. In the event that a social media platform experiences a data leak – of which there have been many in history – your alias will nip the data leak in the bud and prevent the leaker from learning anything else.
4. Information organization: With an email alias, you can get ahead of hundreds of emails all piling into your one inbox. An email alias will help you sort through different messages and more easily find the email you’re looking for, as well as identify and filter out spam more easily. I’ll touch again on this below.
5. Professional communications: Perhaps you’re not a company, but have a responsibility to handle public interaction or front-facing support; You can use an email alias to manage and separate professional and personal communications.
6. Project development: You can use an email alias for testing email workflows, sign-ups, and other things within websites so that it not only keeps you private in the process but also conveniently compiles your findings into one section of your inbox for you to review.
Email alias organization
You can simply implement email aliases for enhanced privacy. But if you want to take full advantage of their organizational benefits, then it takes a bit more intention with how you structure your aliases.
With so many different aliases that you'll use over time, things can get cluttered fast. To mitigate this, you can implement sub aliases that make your filtering a bit more granular and easier to search.
For example, you could structure your aliases as:
“Category” to the left of the dash can represent the general topic of the email, and “companyname” is for the specific entity you’re receiving mail from.
Let’s say I’m using addy.io for my email aliases, and I have a lot of traveling to do this year
Now let’s say that you want to book three different flights this year, and have to use multiple different services to buy your tickets, like Expedia, Skyscanner, or Kayak.
For each alias, if I was using addy.io, I could then structure them as:
Meanwhile, the Bitcoin newsletter I’m subscribed could use the alias:
My 2024 taxes could be sorted under “finance” with:
When applying this framework to your aliases in conjunction with complementary private email service, your organization can become much easier.
For example, you could use Proton Mail’s custom folders and labels to categorize emails that arrive through different aliases. Just set up a filter to move all emails sent to your “[email protected]” alias directly into the "Bitcoin" folder, or create a “Finance” folder that collects incoming emails from “[email protected]”
You can go a step further and use more advanced filtering capabilities that create rules based on specific criteria, such as the sender/receiver alias or specific keywords in the title/body. This can function as a greater sort of “catch all” filter that will keep all your financial emails (or anything else) in one bunch, based on groupings of keywords you’d expect to find within those emails. And if you’re savvy with code, you can implement sieve filters to automate this filtering process within your inbox for you.
By strategically applying these features, you can maintain a high level of privacy while reducing friction elsewhere and make your organization simpler in the long run.
Your life will be so much easier down the road if you do this today before you start using many different aliases.
Keep in mind
Using an email alias doesn’t guarantee total privacy. Email service providers can still see where the alias came from and the email aliasing provider can still see emails they relay, so if you want total privacy, you need to either self host your email or anonymously set up an email address to then apply your alias on top of.
By setting up an account with one of the services mentioned above and paying anonymously with no-KYC Bitcoin, you can use an email alias and rest assured knowing that email service providers can’t use them to dox your identity. They could give up the email to authorities if subpoenaed or something similar, but if implemented properly, it would still protect your identity.
Don’t forget your other privacy tools
As bitcoiners, maintaining good online privacy doesn’t just mean good email hygiene. In fact, that matters very little if you leave the rest of your privacy foundation unchecked.
- Make sure that you’re using a privacy browser that complements the aliases and other efforts you take to keep your identity as hidden as possible, or use a VPN at the very least if you have to use a particular browser.
- Pay attention to the traces you leave on social media platforms, especially when talking about Bitcoin. These are the kinds of conversations that help criminals narrow down their target lists, so you don’t want to accidentally say too much and get your Bitcoin, identity, or something worse stolen.
- Bitcoin PayNyms work similarly to email aliases in that they provide an alias that masks Bitcoin addresses for you to receive payments with. The sender only sees a static PayNym address, but on the backend it’s generating new Bitcoin addresses for each payment, so the receive address is always unique.
Conclusion
Not only do email aliases keep you protected from phishing, spam, and other potential dangers, they make your online life easier too.
For any bitcoiners considering using an email alias, you won’t regret it. The hassle is minimal to set one up and well worth the privacy that it offers. Especially during a time when financial surveillance is at an all-time high, email aliasing is one of the small and easy measures you can take to better safeguard yourself.
Besides email aliasing, consider how else you’re potentially leaking private information online. Whether you're creating accounts, talking on social media, online shopping, or working with Bitcoin software: your privacy is quintessential to ensuring it can all happen without putting yourself at risk of theft or fraud.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

“Why should I even care about my privacy? I’ve got nothing to hide!”
Have you ever heard someone ask this before?
Despite how interconnected the world is today, not enough people have placed as much care into their online privacy. Instead, many actually like to flaunt their identities and locations online. It’s not popular to protect your privacy these days, but that certainly doesn’t mean you should forget about it altogether.
As Eric Hughes, author of “A Cypherpunk’s Manifesto” puts it:
Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn't want the whole world to know, but a secret matter is something one doesn't want anybody to know. Privacy is the power to selectively reveal oneself to the world.
If you want to be more selective about what you share with others online the same way you do in person, then privacy-preserving browsers are one of the first upgrades you can make to reclaim control over your online footprint.
How private is your online activity?
Just how much of your data is broadcast to the world when you connect to the internet?
Pretty much all of it.
Very little of what you do on the standard internet is private if you haven’t put any privacy protections in place before. That means that internet service providers (ISPs), app developers, and website hosts usually have the ability to freely collect your:
- Location data
- Device information
- Browsing history
- Search queries
- Online purchases
- Email content
- App and social media activity
- Metadata
- Time spent on page
- Time spent looking at a particular portion of the page
- Where exactly you scrolled to on the page
- Other micro measurements of your activity
And you expose yourself to:
- Government surveillance
- Online behavior profiling
- Cookies and tracking
- Public Wi-Fi attacks
- Data breaches
- Data selling
- Scammers
- And more
An old study from Pew Research found that 91% of Americans feel as though they’ve “lost control” of their online privacy. Despite it being from 2014, the age of this study only emphasizes how even a decade ago, when social media and mainstream browsing was only a few years into breaching the mainstream, people already overwhelmingly understood the lack of privacy that today’s internet provides.
Today those problems have only gotten worse.
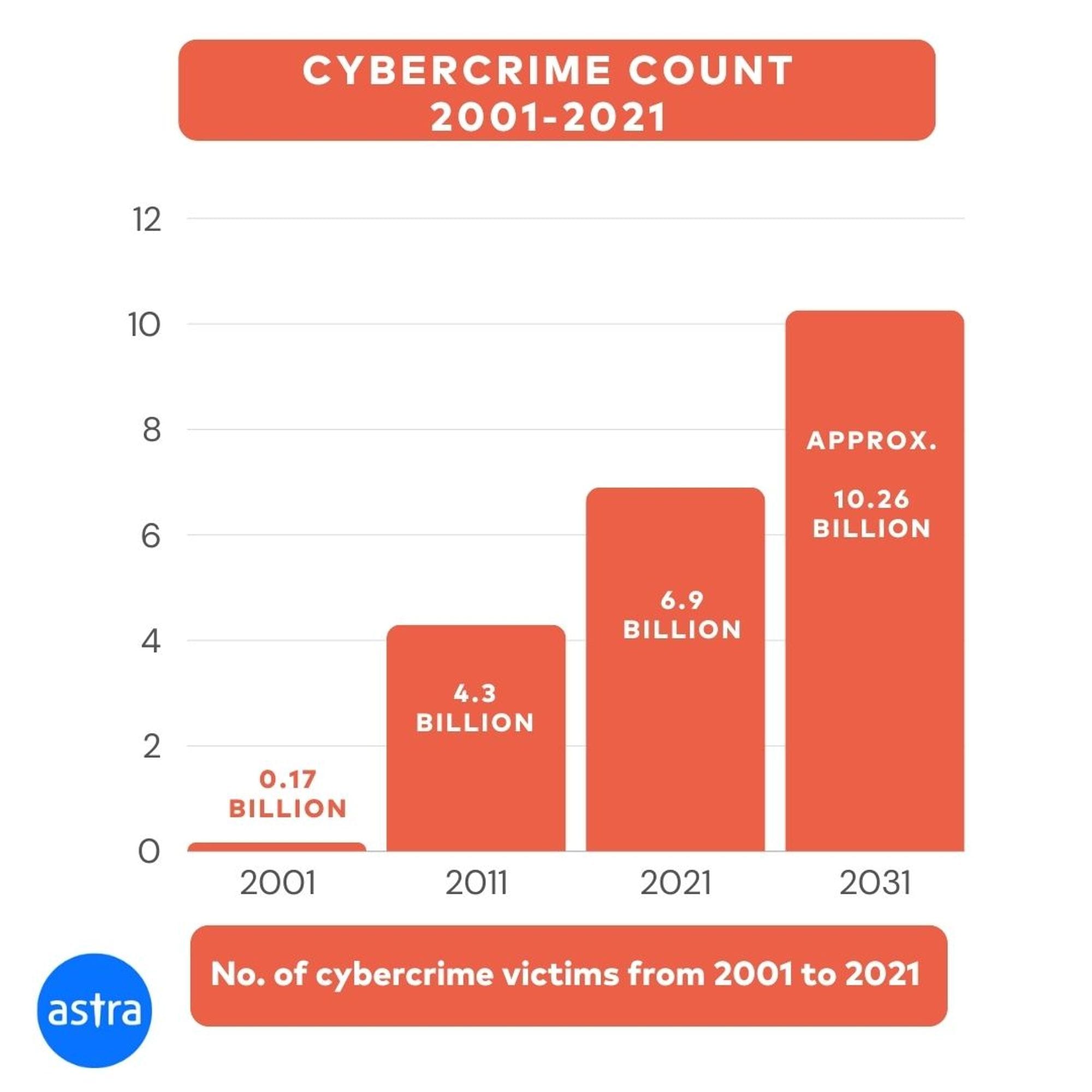
Cybersecurity provider Astra found that In 2001, there were under 200 million instances of general cybercrime attacks.
In 2011, that number grew to 4.3 billion.
In 2021, 6.9 billion.
In 2031, studies estimate over 10 billion cases of cybercrime.
It’s clearly a rising issue. And ultimately, most people do want to improve their online privacy, but don’t believe they’re able to reclaim it and confidently browse with privacy. It’s a result of the sunk cost fallacy; people have already put so much out there online that trying to change their behavior and get a handle on it now is simply overwhelming.
Risks of not protecting your privacy online
Privacy upholds your freedom, but the less you try to maintain it, the more subject to exploitation you are through ads, scams, data leaks, cyber attacks, and much more.
While some problems may be more trivial than others, not respecting your online footprint today could bring a world of pain for you tomorrow. Just ask a politician: they understand what having old baggage resurfaced is like.
Especially if you plan on using the internet to run your business, work with Bitcoin, or other financial or personal reasons, it’s still well worth being mindful of your privacy as it could save you from headaches, lost time, lost money, or even worse problems.
Here’s what privacy browsers offer you
Besides the ability to keep your activity and potentially even your identity private, using privacy browsers better protects you from:
- Intrusive data collection: With each website you visit, you leave a trail of data for companies to scoop up and learn about you. By using a private browser instead, you block those tracking cookies, scripts, and other methods that advertisers and websites use to monitor your online behavior. Without leaving that data trail, companies can’t intrusively target you for their business, and scammers and hackers are much less likely to start targeting you in the first place.
- Browser fingerprinting: Privacy browsers incorporate measures to minimize browser fingerprinting, which keep the unique characteristics of your own browser and device configuration private.
- Malware & phishing attempts: Good privacy browsers come with tools to detect and block malicious websites, phishing attempts, and malware, so you can feel confident installing new files onto your computer or visiting websites.
Of course, privacy browsers also come pre-installed with or let you download extensions such as ad blockers, VPNs, and more, so you can enjoy free access to geo-restricted websites, ad-free content consumption, video streaming, etc.
Privacy browsers also often let you customize settings to achieve the optimal privacy for your needs. However, there are certain cases where you may not want to mess with privacy settings too much, which we’ll discuss later.
5 great privacy browsers to check out
So which privacy browsers offer the best protection? There’s a lot of nuance here, so there likely isn’t a “best” browser. And the truth is, in today’s online panopticon: there aren’t many amazing options out there for privacy browsers.
All of these browsers are free and open-source software (FOSS). Each comes with its own unique tradeoffs, so refer to this comparison table from PrivacyTests.org for a comprehensive overview of the technical details for each.
Be sure to test these browsers out yourself before committing your private browsing to just one of them. In some cases, you may benefit from using a mixture of multiple.
1. Tor Browser

The first privacy browser, Tor, may not be ideal for your daily driver, but comes loaded with privacy tech that you should take advantage of for certain actions.
Unlike some other privacy browsers, Tor is also a private network. It relies on a decentralized network of volunteers running nodes – like Bitcoin – rather than centralized servers.
Tor keeps your identity anonymous by distributing and randomizing information through volunteers’ nodes in such a way that no single node can gather enough information about you to dox your identity.
Think of Tor like you would a VPN, except that information gets routed traffic through three different servers with randomized IP addresses, rather than just one in the case of a VPN.
It’s designed in such a way that no single server can extract enough data to dox you. The entry node that you initially connect to can see your home IP address, but it can’t see where you want to send your data to. The middle node extracts just enough information to know where to route your data next, but it can’t see your home IP address, so it doesn’t know where it’s getting this data from. The final node can identify the destination, but can’t see where the data came from in the first place.
There are plenty of advantages that come with browsing over a private network like Tor, like accessing .onion websites, or buying non-KYC Bitcoin. However, you also have to be mindful of the downsides of using it as a primary browser. Tor can be slow to move you from point A to point B sometimes, you may face compatibility issues with certain websites, and it’s not ideal for downloading larger files.
2. Mullvad

To complement the Bitcoin-enabled Mullvad VPN, Mullvad partnered with Tor to create its own browser that takes your privacy a step further. Mullvad browser makes it easy to pair Mullvad's VPN with your browsing activity, protecting you on both fronts.
The Mullvad browser is also designed to ensure that everyone’s footprint looks the exact same when using the Mullvad browser, making it much harder to decipher the differences in users from an outside perspective.
If you’re a regular user of the Mullvad VPN, then the Mullvad browser may be a good option to consider since it works in conjunction with the VPN without weighing you down with too many restrictions, making general browsing a breeze.
Important note: Since this standard configuration of settings is what makes everyone’s footprint look identical, you shouldn’t modify the browser in any way beyond changing the basic default security levels. Otherwise, you will create an outlier footprint that’s unique from others.
3. Brave

Brave is one of the most popular privacy browsers available, and for one primary reason: the great user experience.
Using Brave feels almost identical to using mainstream browsers like Chrome. However, it prevents trackers by default, automatically blocks ads, and comes with other built-in privacy enhancements to keep your online activity protected, along with a clean home dashboard filled with data on how your privacy browser is working for you.
You can also open private tabs over Tor using Brave, however, it doesn’t offer true anonymity (since you’re connecting via a browser with access to your IP address), and you might face more friction in the process of using Tor via Brave than you would just using the Tor browser directly. It’s nice to have the option in a pinch in case you’re in a good workflow using Brave, but if your own personal safety depends on anonymity, then this isn’t the best option for anonymous browsing specifically.
4. Mozilla Firefox

Firefox may feel more familiar than most other browsers on this list. It’s definitely the most popular. However, there is one caveat to Firefox: To get the real privacy benefits from it, you’ll have to spend some time tweaking settings to optimize it for private browsing.
By default, Firefox comes with too many features that may actually hurt your privacy rather than protect it. It comes ready with good stuff like social media tracker blocking, blocking cross-site cookies, fingerprint prevention, and more. But it also leaves some bad default settings on, like Firefox data collecting, setting Google to the default search engine, or the Pocket extension, which collects your reading data.
This list isn’t comprehensive. Just know that Firefox will take some setup to optimize for privacy. If you enjoy the Firefox platform and want to take the time to make the proper modifications, then check out the Arkenfox project, a privacy-optimized user.js file for Firefox. You can watch this video tutorial of how to implement Arkenfox for a smoother transition.
After implementing the right modifications, Firefox can be an incredibly robust private browser that feels comfortable to use.
5. LibreWolf

LibreWolf is essentially Firefox without all the additional bloat, and it feels similar because it’s actually a fork of Firefox. However, you can skip the Firefox tweaks and enjoy its default privacy settings. It improves on Firefox by cleaning up your online fingerprint so that you don’t leave traces of where you visit. And if it’s your everyday browser, you may actually want to go into the settings and reduce the level of default restriction that it comes with, such as cookie collection, browsing history, etc. (It may get annoying having to re-login to every website you use each time you open LibreWolf).
It follows the same updates as Firefox does, so you can enjoy the enhanced privacy features and other updates that come with it.
If you prefer a bit more flexibility, then the properly configured Firefox platform may be best for you. But to skip the customization and get straight to lean, private browsing, LibreWolf is a great choice.
Understanding VPNs vs. privacy browsers
Different privacy tools offer varying degrees of privacy protection depending on your specific needs. If you’re just using the basic internet with no privacy measures in place, then you expose your online activities to internet service providers (ISPs) and whoever hosts the websites you visit. This makes it relatively easy to trace your IP address and expose your identity.
You can improve your online privacy a bit more by simply implementing a virtual private network (VPN). A VPN serves as an intermediary server between your device and the websites you visit.
They encrypt your internet traffic and mask your IP address to prevent other entities from tracking your location. While this helps to protect your online activity from criminals and data collectors, it does not protect your identity. They still collect data about the local IP address you’re connecting from, and are subject to the laws of their regional jurisdiction. So if the state comes knocking for information on certain users of a VPN, they have to give it up.
Not all VPNs are created equal, however. Some, like NordVPN, still collect payment information and email accounts when signing up. Sure, you can go through extra hoops to set up private payments, but this doesn’t exactly align with the ethos of online privacy.
On the other hand, a VPN like Mullvad doesn’t collect this private data, doesn't even have accounts to begin with, and even accepts Bitcoin payments (both on-chain and even over Lightning) to make maintaining your privacy that much easier.
To achieve optimal online privacy, however, you need to take another step further and start using privacy browsers.
What else can you do?
Beyond private browsing, you can focus on tidying up your digital footprint. Sharing less often, and being sensitive about what and where you post, will keep you safer in the long run.
As far as passwords go, it's crucial that you diversify them. Keep them complex, and never use the same password twice. Be extra careful where you store your passwords too; LastPass has demonstrated in the past why storing sensitive data inside certain password managers may actually be a security gap. Someone managed to hack the platform back in October 2023, leading to millions of dollars in cryptocurrency lost in a single day. For those keeping their seed phrases stored on a password manager, they had a more expensive lesson to learn about what improper privacy protections can lead to.
Remember as Nick Szabo once said, “Trusted third parties are security holes.”
You always want to ensure that you are regularly updating your software and keeping antivirus protection in place so you don’t fall victim to an online attack due to outdated software.
Avoid any and all suspicious links. Be patient, be mindful, work on developing good browsing habits, and maintain skepticism to avoid clicking the wrong things. In the world of Bitcoin, the traps are set far and wide, and it’s all too easy to stumble into them if you’re not paying attention.
And of course, stay informed about Bitcoin privacy and the privacy space at large. With all the new developments taking place every year on Bitcoin, privacy is getting better and better for the internet of money.
Conclusion
We must defend our own privacy if we expect to have any. We must come together and create systems which allow anonymous transactions to take place. People have been defending their own privacy for centuries with whispers, darkness, envelopes, closed doors, secret handshakes, and couriers. The technologies of the past did not allow for strong privacy, but electronic technologies do.
Eric Hughes makes it clear why privacy is so important in today’s “open world.” With how interconnected we are becoming online, it’s essential to build and enable technologies that strengthen our privacy more than ever before.
Remember that the landscape of online threats you may face varies greatly depending on the platforms you’re using, where you live, and the legal jurisdiction of that region. No matter where you live though, privacy browsers are a foundational component of anyone’s online security.
Unfortunately, no single browser is a fix-all solution. There’s plenty else to learn too, like payments privacy, secure messaging, social media etiquette, and more.
Freedom.Tech wants to keep you informed on the latest in Bitcoin privacy, so stick around here to stay on top of it!
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

I learned about Jesper Graugaard’s activism against Chromebooks in Danish schools through my work on The Privacy Dad blog. Our shared interest in privacy and data protection in schools led to a collaboration in the form of an interview which was published in two parts.
Below is an abridged version of that interview. Some questions refer to a 2022 Wired article about Jesper’s case, which can be found here. It provides an excellent overview of the Elsinor Chromebook case.
As a parent, teacher, and privacy advocate, I greatly admire what Jesper is doing and hope his case against Google will garner more attention. A win for privacy in schools in Denmark could set a positive precedent for Europe and the rest of the world.
You can find Jesper on LinkedIn.
When did you first begin to have concerns about your children’s privacy in school?
I never imagined that privacy would be a problem in schools until the Chromebook came into my home. I honestly thought the school administration had everything in place and would ensure a digital safe space in school for my children, with protected data and privacy.
The day my kids came home with their first Chromebook, they were proud. I was even positive, as I expected they were about to learn coding, and tech history and culture. I put aside the knowledge that the Chromebook was a Google product, a company that makes most of its revenue by harvesting data and selling it.
But my hopes soon turned into disappointment and it became a digital nightmare. They were not learning anything. They were using the Chromebook as a substitute for books, pen and paper. And Google were doing what they do best: getting the data. I saw that getting data from a person age six is a best-case-scenario for a company like Google. And to achieve this nation-wide is better than ever imagined. They got it for free, and we even paid them for collecting data.
When the school implemented YouTube profiles for the students, giving away my child's full name, age, school name and class, that was the tipping point for me. I had not given consent to share everything about my child in public school.
It was then I really understood the importance of protecting my children's digital copy - the digital twin - and their data. As long as they are not of legal age, it is my duty as a parent to protect and care for my children. But in this situation, I couldn't. Or at least, it felt very difficult to achieve this within the public school framework in Denmark. As a parent you are not informed about what data is being collected and shared. In some schools there are more than 400 apps in use. Who can keep track on any of these?
The Wired article states you made an official complaint to Denmark's data protection regulator in 2019. Tell us more.
Denmark's data protection regulator is the Danish Data Protection Authority (DPA). The Danish Data Protection Authority is the central, independent authority that supervises that the rules on data protection are complied with.
I did not know much about them or their role before this case. I found out about them as I called friends within the tech industry and explained my problem. I approached the DPA, explained my issue to them, and they explained how to file the case, and what documentation was needed in order to begin.
Their role is to investigate the documentation and the solution to create closure on the case. Their decisions will set the standard for what Google and the municipalities shall do in order to make Chromebooks GDPR compliant.
If I do not agree on the final decision, which will hopefully be made this autumn, I will have to re-think my case and go the EU.
Your complaint initially led to a ban on Chromebooks in schools in the Elsinore Municipality in 2021. What is the situation today?
The ban was disabled after three months, because there was no “plan B” for continuing education in public schools. Without Chromebooks, schooling could not continue. The ban was not extended to other municipalities.
The ban could be reinstated if the DPA decides to do so. But if that happens, I expect that the ban will be final, and Google will be out for good, and schools will have to come up with a plan B. We are currently waiting for the final closure of the case from the DPA. It was expected to come end June, then in August and now in October. Not sure how long it will take, but it could be any day now. I am very excited.
We have at least 53 municipalities using Chromebooks in public schools who are waiting to know whether its legal to continue doing so or not. Then we have the rest of the 50 municipalities that are using Microsoft. They are holding their collective breath along with Microsoft.
On the 4th October, the Danish tech media site Version 2 published an article with access to documents that reveal that these Chromebook municipalities are tied to illegal transfers of school children's personal data to countries such as Mexico, Colombia and India. This is shown in the latest memo from the National Association of Municipalities to the Danish Data Protection Authority, which has announced a decision will be made very soon. It also documents that:
“Before the children's information - such as names, email addresses, direct communication, school assignments and much more - ends up in countries outside the EU, it is sent to Ireland, where Google, like other tech giants, has its European headquarters. Google's American department can also be sent the information, but after the recent data agreement between the EU and the US, it is no longer illegal to send personal data across the Atlantic.” link
What is it like being an activist? Have you or your family experienced negative consequences as a result of your activism? Has it changed your views about work?
I pursue the case in my spare time. I am not getting paid to do it, and that makes me free of any political and financial conflicts of interest. I keep focusing on the simple principle that my children have a right to digital privacy while in public school.
That is currently not the case. Data is being collected, a 'digital twin' or profile is being created, and when my children are of legal age they do not own the rights to their profile. They cannot change it, nor can they take it back. This must change. They should have the right to own and control their personal data when going to school.
One negative effect for me personally is that I quickly realized that I had to go public. Show my face in the media. That was a big step for me, as I am a private person.
I have also been targeted in local media and social media groups by local politicians for bringing Elsinore to the attention of the world with the data privacy issue.
What are your main frustrations with the case?
So far, lobbyists, lawyers, and NGO organisations, all with the power to affect change and help stop the commercialization and violation of children's privacy in schools, have not been able to make any significant impact, with the exception of the Danish Data Protection Authority. Most children's rights organisations and NGOs are spending their time and energy debating the negative side effects of screen time, mobile phones in schools and social media. Hardly anyone is addressing the principles of data harvesting and privacy.
The mistakes and lack of understanding of digital safety were brought to light with the Chromebook case in 2019, just one year after GDPR law was introduced. In 2022 the civil servants of Elsinore made excuses about their lack of following the law, stating GDPR was so new. But how long do we have to wait? It has taken more than four years now! How can the use of Chromebooks in schools continue if we do not know if it's legal?
How can it be that schools are still using Chromebooks while their use is being investigated for security and privacy issues? Public schools are using Chromebooks because there currently is no plan B. Today the Danish public school system is deeply dependent on two Big Tech companies, and there seems to be no way out.
I am not afraid of tech in schools. I just want to secure my children's rights to privacy, and I want schools to have relevant technology training and a safer digital culture. The current digital strategies that schools are following are more than ten years old and were designed in an era where digital safety and awareness were far from where we are today. I have weekly talks with parents who tell me about incidents in their schools, where basic mistakes are happening which put children's personal data and digital safety at risk. Photos are shared on social media, and passwords and logins for Chromebooks placed with stickers on the device or displayed on the wall in the classrooms.
Recently, we had a major hack on five educational institutions in Southern Denmark, because one laptop with infectious ransomware was connected to the school network, thereby giving hackers access to more than 10.000 students' private data, that now are being published on the dark web. This hacker attack led to schools having to contact 40.000 people potentially affected by the attack.
On the 11th of October, the Danish government presented a new plan for the public school sector to try to make schools and education better and more relevant. However, they did this without mentioning safety just once and without introducing specified subjects for technology. This is strange, when put in the context that Denmark proudly claims to be the best digitalized society in the world.
You were invited to speak in September 2023 at the Legal Design Summit in Finland. Can you tell us about that? What have been other, perhaps unexpected, positive outcomes of your activism?
The Chromebook case has pushed the debate of digitalization significantly into the mainstream, and there is a growing awareness of the detrimental consequences of hardcore digitalization of modern society.
The Finnish branch of the Save The Children organisation contacted me to let me know they had decided to base their Legal Design Summit on my case. I was invited to explain and give the context to my case, and help build an understanding of the privacy and data issues that children and parents are facing today in Scandinavian public schools. I hope they can develop a toolkit to make parents and children more aware of their rights and how to file a case.
Other unexpected positive personal outcomes have been that I was honoured by the Georgbruunske Foundation in 2022 for my digital fight. I can now officially call myself a 'Sympathetic Complainer'.
In 2023 I was nominated for the Danish digital freedom fighter 'Libre Prize'. I was nominated along with high profile individuals such as Max Schrems and David Heinemeir Hansson. Of course its hard to beat the large-scale impact that someone like Schrems has had, but being a “dad” without a technical background sitting together with prestigious lawyers and tech people was not only a big honour – it drove home the importance of my case and the impact it has had so far.
The Chromebook case has become a PhD fellowship programme at Aarhus University. Students across universities and schools are now doing Bachelor theses on the case. The Chromebook case is becoming part of the education, part of the history of tech.
I have spoken to Data Protection Officers across the country, and they confirm that my case has pushed Google to change, so I am sure that both Larry Page and Sergey Brin (Founders of Google) are familiar with my name. Politicians in the US Congress are also familiar with my case.
But what has touched me most has been everyone who has reached out to me from all over the world. Parents, professors, data scientists, privacy experts and journalists have contacted me and helped me build a fantastic network. They have inspired me, and, more importantly, pushed me in the right direction, keeping me focused and eager to learn more. That kind of support and acknowledgement has been essential, as I was very much alone in this fight, and still am today.
What further positive outcomes do you hope for?
For me the best outcome of the case would be that Chromebooks and Microsoft are left out of the classroom, at least until the children are around ages of 10 to 12. To date, I have not seen sound educational arguments for using Chromebooks before that.
Another positive outcome would be if Scandinavian countries got together to design custom educational platforms and hardware as an alternative to Google's and Microsoft's solutions. One of the main arguments for a combined Scandinavian strategy is our shared values and culture. Scandinavian countries share similar priorities, which are sometimes different to American ones.
Finally, this case is focused on public schools. But what about the private school sector? In Denmark, private schools don't work within a local authorities framework. In some of these schools, it is the parents who supply the digital device, which makes them the legal data controller instead of the school or local municipality. It is the responsibility of the data controller to make sure the device is GDPR compliant, but can we expect the parents really understand GDPR and can have that responsibility on their shoulders? Also, if private schools have their own device policies, they have to ensure that both risk and consequence analyses are in place.
Some argue that providing students with affordable hardware is more important than protecting their data, given how important IT skills are today. What are your thoughts?
Getting a Chromebook in school is not providing any IT skills. Before giving a child a computer, they need to be given the opportunity to study IT as a subject. This is currently not the case in Denmark.
There has been a debate in Denmark over the past few years about implementing a subject called “technology understanding,” but so far nothing has happened. In order to be a successful human being living in the digital age, we will need a far better understanding of technology, and it needs to be taught in the classroom, and not left to parents.
Imagine if we had a subject in schools where children learned not only how to use digital technology, including coding, but were also taught the history and culture of information technology. Just like we teach the history of the 20th Century, we should also teach the history of the Internet, the first social media company, what data and data harvesting are, the history of Microsoft, the impact of the iPhone, when streaming began, what social impact YouTube has had, and so on.
When it comes to being ready for the digital age, do we really need to compromise young people's data?
What advice would you give to concerned parents reading this?
- Check the device given to your children by the school.
- Check the school's digital policies. Discuss the subject with school board; it's a discussion that is constantly developing.
- Ask for informative guidelines from the local school authorities when receiving a digital device from school.
- Never use a school device for anything other than school-related work.
- Approach NGOs such as Save The Children or other national organisations that are focused on the subject of data privacy for advice and help.
- Exercise your right to be private on a daily basis. It is not about being a nerd or an extremist. Instead, it's about developing awareness.
- When sharing content such as a photo of your children online, remember this is not just photo. It is data, and everybody can use it as soon its public, and it can be used for anything.
- Make children's digital lives and rights a topic for discussion in school among other parents and teachers by bringing it up at school meetings.
- Talk often with your children about being a human in the digital world. Teach them to use digital devices responsibly.
- Educate yourself and stay updated on the subject of digital privacy.
- Spend less time online and more time offline with your children.
Any final thoughts?
First, let me state that I have nothing against the companies that sell digital services. This is not a fight against corporations. For me, it's a fight for privacy and digital rights.
As a modern digital society, we need to understand the basic needs for privacy and the legal rights we have. The digital age makes these rights more complex and more delicate because the line between what is private and public is blurring; digital services today have such extensive ways to collect data. This can make it difficult to see when our private sphere is breached. But when this does happen, highly personal data is often collected, which we subsequently cannot withdraw, don't own, and which we no longer have rights over.
What is decisive for me is that we as a society become better at understanding both the immaterial and material value of data. Data is part of us, our identity, our personality, and we have a right to have these protected on an equal footing with other fundamental human rights. Especially when it comes to children in a school system. This is to ensure their future rights are not violated until they are old enough to give consent.
Unfortunately, at it stands today, it is the parents who have the right to consent until the child is 18 years old, but parents often do not have the knowledge to make these types of decisions. Parents send their children to primary school, uninformed about their children's rights, and uninformed about the data collection that takes place. This is because, unfortunately, they often do not understand or have not familiarized themselves with these concepts. It has become too complex.
We have to change that, that's what the Chromebook case is about.
Further reading
- Jesper Graugaard on LinkedIn
- A Danish City Built Google Into Its Schools—Then Banned It (Wired, 23 September 2022)
- The Danish DPA imposes a ban on the use of Google Workspace in Elsinore municipality (European Data Protection Board, 19 July 2022)
- Denmark is banning Chromebooks in schools — here's why I'm on board (Laptop Mag, 19 July 2022)
- Version 2 articles on Chromebooks (Danish, paywalled)
- The Privacy Dad interviews Jesper Graugaard:
- Jesper Graugaard's Fight Against Chromebooks in Danish Schools (1/2) (18 October 2023)
- Jesper Graugaard's Fight Against Chromebooks in Danish Schools (2/2) (27 October 2023)
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

While many already in the freedom tech community may be familiar with the dangers and rapid development of central bank digital currencies (CBDCs) across the globe, a serious education issue still exists. The Human Rights Foundation (HRF) launched a fellowship in February 2023 with the goal of tracking the progress of CBDCs around the world and educating the average person on the risks of CBDCs broadly. Today, the HRF revealed the excellent output of that fellowship in the CBDC Tracker.
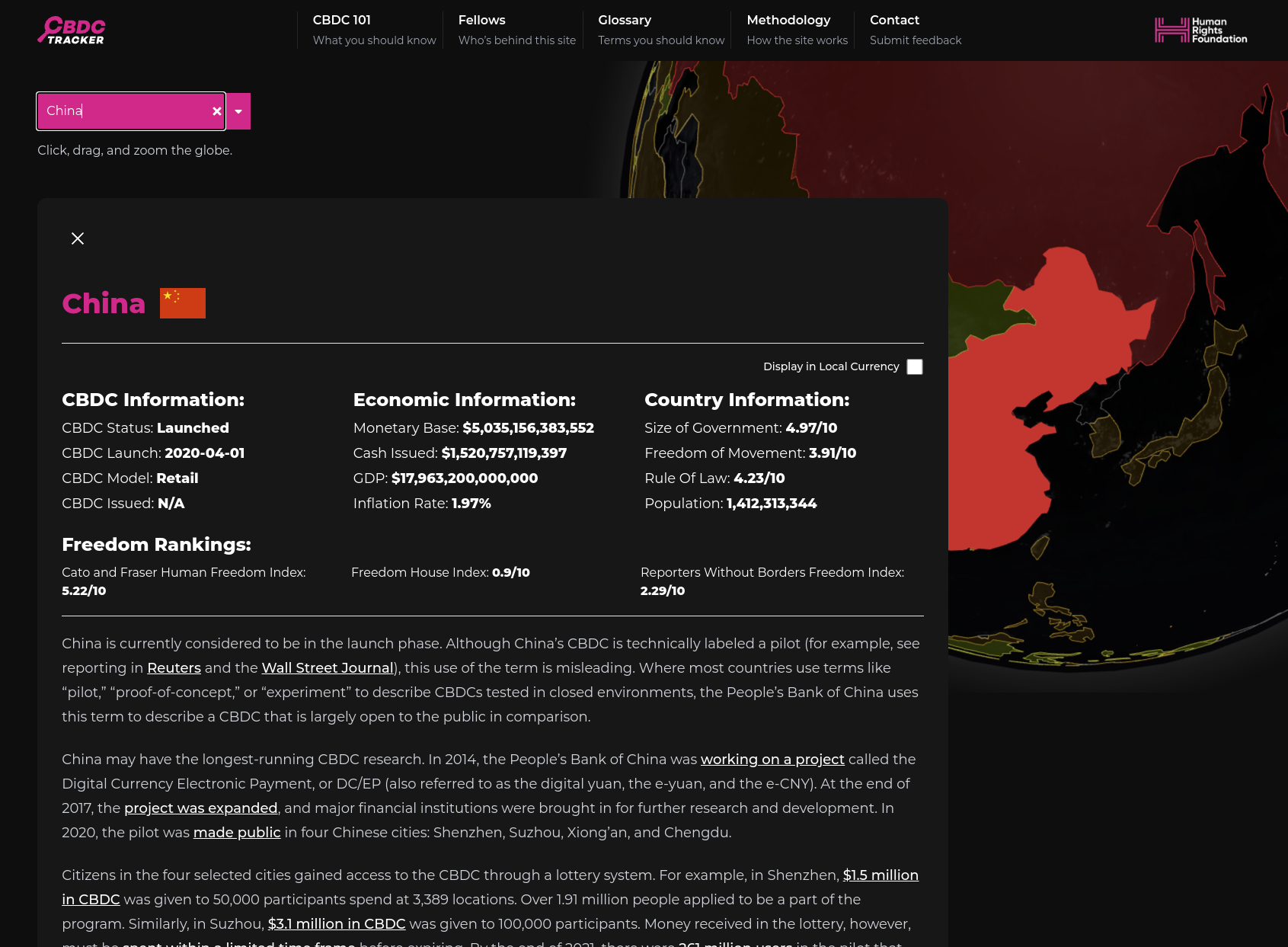
The HRF's new CBDC Tracker allows anyone to quickly check the current status of CBDCs in their country (or any country worldwide) in just a few clicks, get information on the human rights impacts of CBDCs, and quickly read more details on each countries CBDC program. This makes it trivial for even the most non-technical users to keep up to date with vital information surrounding the rapid advance of CBDCs and how it will impact their financial freedoms moving forward.
One of the most powerful aspects of the announcement made by the HRF was a summary of their findings so far while building the CBDC Tracker, showing that CBDCs are far from a niche human rights issue:
– A global trend: The majority of the world’s governments (62%) are actively researching, building, or deploying CBDCs, despite very little public awareness on the topic.
– Authoritarians lead the way: Dictatorships are leading the charge in CBDC deployment. HRF estimates that 3.7 billion people (46% of the world population) are living under autocracies currently experimenting with CBDCs.
– Vanishing privacy: CBDCs may upend traditional privacy norms as they replace paper cash, serving as tools of surveillance and control, especially in dictatorships
– Peer pressure: CBDC adoption is accelerating globally, with few major governments abstaining from the process.
– Adoption challenges: Retail adoption of CBDCs in places like China and Nigeria faces major hurdles. Citizens are skeptical. Governments should be expected to force the issue.
– Government and corporate collaboration: Governments are likely to partner with commercial banks or fintech companies to distribute CBDCs via existing banking or mobile applications.
If you want to learn more about the risks facing us in CBDCs or the background of the CBDC Tracker, we published an article featuring Alex Gladstein, CSO of the HRF last month:

I'd highly recommend you take a few minutes today and explore the CBDC Tracker yourself and consider sharing it with friends and family to help break down the education barrier that governments are relying on to push against financial freedoms with CBDCs:

Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:


Since time immemorial governments have been unable to resist the urge to control and dominate the monetary system. Controlling the money supply is a power so great that it bestows upon its possessor the ability to command control over human time; and it’s this lust for power that gave birth to central banking. From coin-clipping to central bank digital currencies (CBDC’s), monetary history is filled with numerous attempts by the state and/or banking cartels to be “masters of the universe”. In our modern society, this quest for unrestrained power by the state birthed legal tender laws that further entrenched the power and influence of the central banking leviathan; giving the state a monopoly over the issuance of money in a specific territory.
By establishing a monopolistic control over the issuance and distribution of money, as well as through the imposition of a given currency, legal tender laws not only disrupt the principles of a free market but also curtail consumer autonomy. These regulations are founded on the mistaken premise that money is a construct of the state thus placing the government at the heart of every transaction; as the final enforcer of all contractual agreements. If history is any guide, this position has been subject to abuse over and over again. Intriguingly, it's from the very heart of these legal tender laws that intrusion into financial privacy becomes normalized and codified into law.
The Rise of Financial Surveillance
Surveillance by the state and its corporate partners has become increasingly common and accepted in recent years. This is due to a number of factors, including the rise of new technologies that make surveillance easier (e.g. nano-tech and AI) and more efficient, as well as the perceived need to protect against terrorism and other threats; which gave rise to draconian legislations like the Patriot Act. However, this level of surveillance violates individual privacy and freedom; as one cannot be truly free without the right to privacy being protected. The unfortunate reality is that for the most part, existing laws and political processes are a major part of the problem in the fight to protect your privacy in a world where everything is tracked. It’s against this background that we will explore in depth some of the threats to privacy in our modern era, even more so where Bitcoin usage is concerned.
Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn’t want the whole world to know, but a secret matter is something one doesn’t want anybody to know. Privacy is the power to selectively reveal oneself to the world…Therefore, privacy in an open society requires anonymous transaction systems. Until now, cash has been the primary such system. An anonymous transaction system is not a secret transaction system. An anonymous system empowers individuals to reveal their identity when desired and only when desired; this is the essence of privacy. - Eric Hughes
The words of Eric Hughes in the quote above are just as true today as they were 30 years ago when they were written. Privacy is no longer a luxury but a necessity, especially in this age where we are constantly surrounded by more and more surveillance tools. In his keynote address at the recently concluded Bitcoin Amsterdam conference, NSA whistleblower Edward Snowden noted that, “Bitcoin has a privacy problem… the world has a privacy problem.” He went on to explain that while the development of coinjoins and mixers is a positive step, it is not a perfect solution to Bitcoin's privacy problem. A very valid but controversial criticism in my view.
Instead of relying solely on techniques like coinjoins and mixers, he encouraged the development of tools that do not require users to "contort themselves" to maintain privacy, while prioritizing the creation of privacy-first solutions. These solutions should not require users to jump through hoops to maintain their privacy but should be user-friendly and intuitive. While this is easier said than done, it’s the only way that will ensure that Bitcoiners will still be able to use Bitcoin freely without being burdened by onerous regulations. More importantly the enemies of Bitcoin are working hard, every single day, in an effort to destroy financial privacy and brand anyone who values and preserves their financial privacy as a potential cybercriminal.
Increasingly Anti-Privacy Regulation
For example, the bill H.R.2969, titled the "Financial Technology Protection Act of 2023," proposes the establishment of an Independent Financial Technology Working Group. This group is tasked with addressing the concerns of terrorism and illicit financing associated with new financial technologies. The working group includes representatives from various government agencies and sectors, such as the Treasury, the Department of Justice, the Department of Homeland Security, Financial Crimes Enforcement Network (FinCEN), the Central Intelligence Agency, and a select group of private financial technology and blockchain companies.
The potential dangers posed by this bill to financial privacy revolve around the broad-reaching powers of the working group. To begin with, the working group is composed of organizations that have previously been hostile, not only to Bitcoin, but to financial privacy in general. Furthermore, the bill's mandate to develop legislative and regulatory proposals to enhance anti-money laundering and counter-terrorist efforts may result in regulations that erode financial privacy. The broad representation of financial institutions, intelligence agencies, and government entities within the working group raises concerns about potential conflicts of interest and the prioritization of security over individual privacy rights. This bill highlights the ongoing efforts to outlaw financial privacy across the board.
Another recent example of this slow creep to outlawing financial privacy is the recent FinCEN rule proposal, which has rightly drawn significant criticism for its overly broad scope and potential implications for individual financial privacy. Underpinned by the Bank Secrecy Act and section 311 of the Patriot Act, it aims to mandate the reporting of various transactions involving cryptocurrency mixing, encompassing a wide array of activities that could be considered routine or benign. The proposal's definitions of mixing are expansive, covering actions such as pooling funds, using certain software, splitting and transmitting funds, creating single-use wallets, and exchanging different types of cryptocurrencies!
It’s also interesting to note that this is happening against the background of a Bitcoin price pump, which was sparked by the news of the approval of a spot Bitcoin ETF in the US. While many view this as a positive, I am of the opinion that if a spot ETF does get approved, it’s not a coincidence that these two events are happening concurrently. It’s likely that the retail investors are eventually going to be excluded from owning Bitcoin except via an ETF due to some of these onerous reporting requirements that are being put forward by this FinCEN rule. It goes without saying that there is no privacy to be had or enjoyed by owning an ETF to say nothing of the counter-party risk, as well as being once again fenced in a fiat environment through Wall St controlled financial instruments. I digress.
Another major concern with the FinCEN proposal is the extensive amount of private information that regulated businesses would be required to report to the government for each transaction, including details about the user's identity, transaction history, and associated addresses. Notably, there is no exemption for private individuals seeking to maintain the privacy of their financial activities, further raising concerns about potential breaches of privacy. Furthermore, the proposal's arguments in favor of the rule primarily focus on examples of stopping “illicit activities,” while downplaying the lack of data on legitimate uses of mixing. Funny how that works right? Anyway, this approach fails to consider the broader context and potential implications for individual financial privacy.
This not only puts individuals living in repressive countries at great risk; but despite the extreme surveillance of the current financial system thanks to anti-money laundering laws (AML), the impact on criminal finances has been less than 0.1%. Meanwhile, compliance costs far exceed recovered criminal funds by more than a hundred times and the public are penalized more than criminal enterprises by increased costs and privacy risks. Given this track record, it’s glaringly clear that the purpose of these laws is to “legally” create a dragnet surveillance apparatus that has the side effects of introducing a lot of unnecessary red tape around transactions and making the financial system more inefficient.
A Silver Lining?
While on the one hand it’s difficult to foresee how enforceable all of this would be in practice, the greater danger lies in the fact that when such vague and dangerous regulations are adopted they become even more difficult to repeal. Perhaps a silver lining in all of this is that the potential roll out of these regulations is proof positive that blockchain tracing methods of companies like Chainalysis are ineffective and inaccurate, hence why stronger measures are now being deployed.
Chainalysis’ tracing methods are currently being challenged in court in the case of Roman Sterlingov, a Russian national that is currently under arrest in the US on allegations of operating the Bitcoin mixer Bitcoin Fog which is believed to have been used to launder over $336 million. Sterlingov maintains that although he used Bitcoin Fog in the past to protect his identity from bad actors, he isn’t Bitcoin Fog’s creator. Aside from Chainalysis’ software pointing in his direction, no solid corroborating evidence has been found linking Roman to the creation of Bitcoin Fog.
It is even more perplexing when you consider that Elizabeth Bisbee, the head of Chainalysis' Investigative Solutions division, admitted in court during the ongoing Sterlingov case that she was unaware of any scientific evidence to support the accuracy of Chainalysis' Reactor software. In addition, a statement issued by Chainalysis also reveals that Bisbee is not only unaware of margins of error rates for Chainalysis’ software, but that Chainalysis hasn’t been keeping track of the false positive and negative rates for its software at all!
Conviction of Sterlingov under these circumstances would not only be a miscarriage of justice due to the insufficient evidence thus far, but would set a terrible precedent and make anyone seeking to protect their financial privacy a target for malicious prosecution based on “roll of the dice” type evidence. What’s really on trial here is whether or not you really do have the right to privacy.
We know that no one ever seizes power with the intention of relinquishing it. - 1984, George Orwell
Conclusion
Snowden, in his Amsterdam address, further warned attendees of the digital panopticon that was being built around them, and cautioned them against focusing exclusively on Bitcoin’s price when their freedoms are slowly being eroded. A warning that I hope will be heeded because the powers that be aren’t just stopping with prosecuting the Sterlingovs of this world, but are taking things a step further to include public-private partnerships with organizations like the World Economic Forum for combating “cybercrime,” something that will likely brand Bitcoiners as “cybercriminals.” This PPP (also known as WEF-PAC) includes everyone from Amazon, Chainalysis, the FBI, Interpol, the European Commission and Microsoft. Given the WEF’s “high regard” for Bitcoin and freedom in general, I expect nothing but “good outcomes” for the Bitcoin space from the WEF-PAC.
The time to build more privacy-first technologies and applications is now. Leveraging decentralized protocols like Nostr for social media as well as for building marketplaces and other services would be a step in the right direction. Easy to use, privacy-first solutions would not only lead to more mass adoption of these tools, but would also render any attempts to set up more financial surveillance systems by the state and its corporate partners fruitless. While this article only showed a few examples of the threats to your financial privacy and overall freedom as a human being, you can bet that many more are in the works, with CBDCs playing a large role. Without privacy there can be no freedom, as the erosion of one compromises the other.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX group:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

Note: this article is a chapter from Juraj Bednar's book "Cryptocurrencies – Hack your way to a better life.
Why use cryptocurrencies as payment networks at all? After all, Bitcoin transactions are often expensive and relatively slow - although Bitcoin is still useful as hard money for saving. Why even bother with any payments for hipster flat whites and when making payments over the Internet?
My primary reason is privacy. There is nothing worse for privacy than paying with a credit card through a payment provider. You lose privacy in several areas right away. Your bank knows everything about you, or they wouldn't give you a credit card. When a Swiss banker did the KYC (Know Your Customer) process with me a few years back, he started by saying "this is going to be awkward, I'll probably ask you your shoe size and how often you have sex. Just answer yes and no, I don't really care about those answers, it's just because of the form and the regulations". The bankers (or the crypto exchangers that do KYC) don't really care about my personal information. They make money from the fees I pay them.
However, the situation is even worse in the rest of the payment network. There are several actors there who are interested in the information for other purposes. I mentioned that PayPal lists more than 600 partners with whom it shares data about your financial transactions. If you think it's a good idea to pay with cryptocurrencies with an "exchange app," I don't recommend it.
But what few people know is that cryptocurrency exchanges that know personal information about you share it with companies that provide so-called "blockchain analytics." They match (likely) wallet owners to transactions. One of the reasons they do this is to prevent trading in stolen cryptocurrencies that the exchange shouldn't convert into euros, dollars and other fiat currencies. The problem is that there is always a clause in the contract with such companies that the exchanges must in turn share your transaction data with the analysis company. So if you "pay" from the KYC of an exchange to make a purchase, that information is available to all customers of the blockchain analytics firm that the exchange uses - and we don't know if and to what extent these firms share the information with each other.
The consequence of this is that your identity "follows" you around the blockchain. While it is not directly stored in it, this does not mean that your purchasing behaviour is anonymous from the moment the cryptocurrencies leave the exchange. On the contrary, it is tracked and you don't even know exactly who is tracking you.
Due to the value of the data flowing through them, payment networks are a huge surveillance system from which private companies and public institutions (tax authorities, financial police, etc.) pull data.
A lot of people will say "but I have nothing to hide". Spy systems should always be looked at from the perspective of the worst case scenario. If we lived in communist Czechoslovakia, would you want the state secret police to have this information virtually instantly and on everyone? There are many examples of turns for the worse - Nazi Germany (first collecting information on Jews and then introducing repressive measures), Iran, North Korea, etc. Technological developments and the fact that we live in a liberal democracy give us the illusion that history only goes in one direction - from worse to better. In reality, however, the process of change is more stochastic and leaps for the worse are not rare. That is why, with every spy system, imagine that all the information is seen by your worst political enemy, who has a constitutional majority. And with this optic, let us look at the various payment systems.
From this point of view, it is probably best to use cash, but it is more difficult to send it over the Internet. Therefore, if you want to cultivate true peer to peer relationships, without sending information about your financial transaction to dozens of institutions, it is a good idea to at least use cryptocurrencies that you buy anonymously when making purchases over the Internet. At the time of this writing, you can do this in a variety of ways - for example, through Bitcoin ATMs or through exchanges that do not have your personal information, such as Bisq or HodlHodl. For a better list of exchanges and merchants that don't do KYC visit, for example, the kycnot.me. Of course, you can also buy cryptocurrencies from someone else who sells them - just for cash.
Payment cards are probably the worst in this respect because not only do they not conceal the identity of both parties, they also contain information about the transaction. The organisations that get your data know how often and for how much you shop at the supermarket (and which one), how often you order supplements over the Internet, and so on. In most banks, every bank employee has access to this data, although this access is monitored. And so you sit down at a desk in a branch with a bank employee, and the employee, in an attempt to sell you more products, goes through your account statement, entry by entry. He finds out that you're paying a competitor's credit card company, how much you're paying for life insurance, and so on.
Why is KYC a risk?
First of all, there is the possibility of leaking your personal data, which often goes much further than just your name, residence and date of birth. Institutions gather additional knowledge from your behaviour so that they can assess the risk of you as a client. If this data is leaked, it's a serious invasion of privacy that can cost you directly - in 2018, the direct cost of identity theft in the U.S. was $1.7 billion.
The leakage of personal data does not only have to occur directly at the institution to which you give your personal data. Under the OECD CRS, information about your balances must be shared with the tax authorities of the country where you are tax resident (usually evidenced by a "utility bill" or "proof of address"). This applies to all financial institutions involved in international payment networks (banks, payment service providers, and yes, even all crypto exchanges that can withdraw and deposit fiat) in all countries that have signed the international Common Reporting Standard treaty - which is basically all countries reachable via payment networks except the US. But the US has its own FATCA reporting scheme.
Since it is better for financial institutions to "overcomply" (i.e. go above and beyond what is actually required), if you have a Slovak passport and live in the Czech Republic, many institutions will send the information that you have an account with them, your balance, etc. directly to both Slovakia and the Czech Republic. This information then ends up in a computer database of both tax offices and there are local bureaucrats that have access to this database. This data should theoretically be well protected, but this is purely theory. For example in the country where I'm a citizen – Slovakia – even very sensitive medical data on people tested for COVID-19 has been leaked. And that's only a leak by hacking! What if someone went to an administrative official, put ten thousand euros on his desk and said "I want information on all the people who have an account on a bitcoin exchange" or "have a balance greater than a million euros". Do you think the official would have resisted? Would they all resist or would there be at least one who gives in to temptation?
A lot of people will say that sensitive data will only leak in underdeveloped countries, but it cannot happen in advanced countries. In 2020, the US anti-money laundering agency FinCEN leaked a number of reports of suspicious transactions. These are more than 2,500 documents on transactions from 2000 to 2017. In fact, banks are required to report any suspicious transactions. This gives them partial immunity from having to do financial policing. If it was suspicious and they reported it, it is the job of the financial authorities to investigate whether it was legal. That doesn't mean they prevented those transactions. If they did report them and the authorities acknowledge that they should have prevented them, they avoid prosecution precisely because they didn't hide them.
Here it is important to note that banks are incentivised to report transactions that look "strange", i.e. it is an unusually high amount or it is a transaction between unusual or “risky” countries. This does not mean that any reporting is automatically an unfair transaction. So there are plenty of normal legitimate transactions among the documents. The people and especially the companies that sent them did not know they were being reported and their transactions are suddenly public because the authorities failed to protect them.
However, you can protect yourself from leaks by not giving the information to anyone.
What can also happen is that you might accidentally get on some (rather poor quality) list of people at risk. People have been listed because someone with a similar name posted on some weird forum or some tabloid made up an article about them. If someone is doing a background check on you, they are very often checking to see if you are on such a list. Financial institutions have to protect themselves – they need to keep their banking license. It is very difficult to get off such a list, and often you will not even find out that you are on it, only that the financial institution will tell you that it cannot do business with you, and that this is a business decision by the bank that cannot be disputed.
Another risk is a situation similar to Executive Order 6102, by which U.S. President Franklin D. Roosevelt confiscated gold from its citizens. If you tell a financial institution about your transactions, the financial institution can (under a law that parliament or congress can pass at any time) obtain information about your transactions. And it will use that information to figure out who bought what and what it can confiscate.
So what is the solution? To also perceive the privacy that the payment network gives and takes away. Use cash, at least for "sensitive transactions," and pay over the Internet with cryptocurrency payment networks that you enter anonymously using cash.
Risks of no-KYC exchanges
Decentralized exchanges also have their risks. There is the possibility of getting coins with a "strange" history (maybe it is optimal to send them straight to a mixer like Wasabi or Whirlpool). Or you can use an anonymous cryptocurrency that doesn't have this problem. Better yet, use the Lightning network to receive it, where you control the history of your coins (the coins you receive are on-chain represented by the transaction used to open the channel).
Another problem with some exchanges may be a strange fraudulent scheme to send fiat. This is something that many decentralized money changers try to prevent in various ways - by reputation, or by special marking of payments to make it clear that it is a purchase on the exchange and not a loan or something similar.
For cash transactions, you need to be wary of counterfeit notes (as with any cash transaction) and of legal cash limits. Less is sometimes more.
Privacy of individual cryptocurrencies
Different cryptocurrencies have different levels of privacy. Ethereum-based cryptocurrencies have very low privacy because all payments typically come from a single account from which fees are also paid. Thus, at a click, a person can see all of that person's transactions on the Ethereum blockchain.
Cryptocurrencies like Bitcoin, Litecoin or Bitcoin Cash have a slightly better model based on the so-called UTXO (Unspent Transaction Output). Each user uses a different address for each incoming payment (although one address can be used multiple times, this is not recommended and wallets by default always generate a new address if they already see an incoming transaction at an existing address). Individual addresses can be linked, but this can be prevented to some extent. It is also relatively easy to use so-called mixers that try to remove transaction history using various techniques - the most well-known are Samourai Wallet and Wasabi Wallet.
We can see the transaction in the Bitcoin network, for example, this transaction moved over a billion dollars worth of Bitcoins.

We can see the addresses from which the transaction left, the address where it arrived, the amount and the fees. If we look at the Liquid network, we don't see the amounts, only the addresses (this particular technique of hiding amounts used here is called "Confidential Transactions").
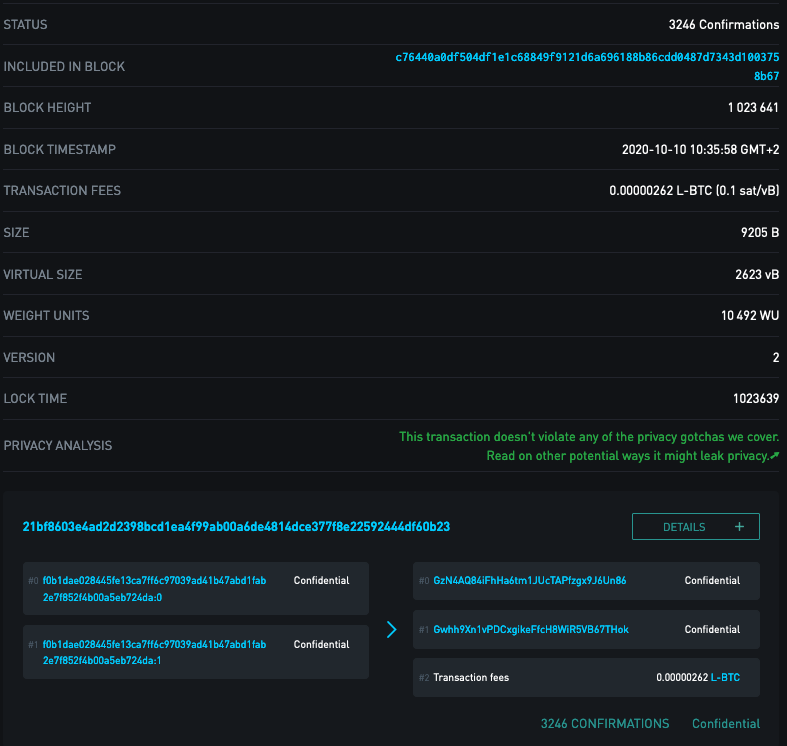
Cryptocurrencies that are more privacy-oriented, such as Monero, try to hide both addresses and amounts.
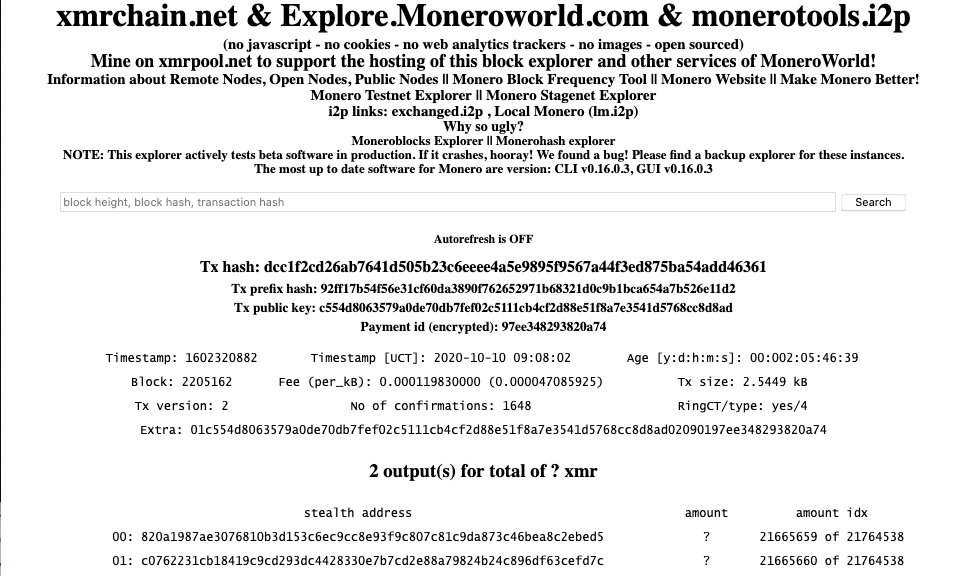
For anonymous cryptocurrencies, not only the technique is important, but also the so-called anonymity set. When I walked around Bratislava in 2019 wearing a black face mask, although my face was not visible, I was easily identifiable. I was the guy with a black face mask. In 2020, a large number of people are walking around in black face masks and it is more difficult to distinguish us from each other. Cryptocurrencies like ZCash have the ability to swap classic auditable coins, which work the same as Bitcoin, for hidden coins, which are mathematically fully interchangeable. However, if only few users actually use the feature, if someone swaps 0.1 ZEC for anonymous coins and three hours later 0.1 ZEC comes out of the anonymous pool to a different address, it's not hard to figure out that it's probably the same user. With respect to the anonymity set, it is thus a very good property that anonymity is mandatory in a given cryptocurrency - any transfer increases the size of the anonymity set. In addition, if there is no visible amount, a potential attacker must examine all transactions, including uninteresting "few cent" transfers, because there is no way to distinguish whether someone is moving ten cents' worth or ten million dollars' worth of cryptocurrency.
In the Lightning network, the privacy model is completely different than on the blockchain. Payments do not have a permanent record, they only change the balances of individual channels and are truly "peer to peer". This means that for a Lightning payment, the sender, the receiver, and the operators of the nodes through whose channels the payment passed know about that payment. No one else. And no one knows if it is the full amount or only part of the payment (a single payment can be divided into multiple routes through channels) and if the other side of the channel originated the payment or if it is just routing a payment for someone else.
It is interesting to combine payment networks. For example, using decentralized or instant exchanges, you can create a Bitcoin transaction using Monero payments. Or use Lightning Payments to create a Bitcoin on-chain, Litecoin, Bitcoin Cash or other transaction. For a demonstration of how to make such payments, see my course How to use the Lightning network to make payments in Bitcoin between friends and for goods and services. If you anonymize your Internet connection, for example by using the Tor network or by using a VPN, there will be no connection to your other activity in the blockchain history - in fact, the money that is sent in the target payment network belongs to the exchange (or the other party that did the exchange) and has nothing to do with you. So you have created a simple "I pay you via lightning and you send another cryptocurrency for me" contract. The permanent footprint in the blockchain thus goes to the exchange.
Comparison with the privacy of other payment networks
Other payment networks such as credit cards are tied to a name. Often a billing address is required, which is sometimes verified.
Since payment card security is based on knowing a few numbers (card number, expiry date and CVV) that are passed on to third parties, it is a good idea to verify some of the data that is not printed on the card. Some data are forbidden to be stored by the operators (CVV). Some payment gateways verify the billing address. This reason is largely redundant with the advent of 3D Secure payments or services like Google Pay and Apple Pay, payments are verified based on another factor (e.g. SMS or confirmation in the card issuer's app).
The billing address is also used for risk assessment. If you are accessing from a Russian IP address, but the card is issued and used in Slovakia, there is a high probability that it is a theft and the payment network will often reject such a transaction.
Cryptocurrencies solve these problems by making transactions electronically signed and irreversible. The provider does not need to know the identity of the client to make a payment at all, and also does not have to worry about chargebacks or fraud. If the payment is confirmed in the network, the merchant can be 100% sure that he has received the money irreversibly.
Another reason for decreased privacy is that the provider of products or services needs to charge the correct VAT. As many people realise that, especially for electronic services, it is enough to select "I am from Hong Kong" (Hong Kong does not have VAT), some providers verify the billing address with the card issuer so that it is not so easy to bypass paying VAT.
Other fiat payment networks are in a similar position with privacy. However, it is not only the retailer and the payment network that obtains information about the customer's personal data. As I mentioned above, PayPal, for example, has terms and conditions stating that it can share your personal information with over 600 entities. Regulations such as the OECD CRS, FATCA and so on even impose an obligation on every provider of banking, financial and payment services to automatically inform the tax authorities. Anti-money laundering regulations in turn force them to block transactions or inform the financial police. All of these information shares are automatic once certain conditions are met - it's not a case of 'after all, I'm making a small turnover' or 'I'm not doing anything wrong'. This data is sent, processed and retained for a long time.
The first and fundamental problem with automatic data sharing is - can the recipient protect it? The recipient is often a government institution. And we are talking about a technical hack; the second and much more likely attack vector is simply buying the data from an employee who has access to it. But government institutions are not the only recipients of data - there are also marketing firms, credit bureaus, and the like. Imagine that when you make a payment, an information firework is set off that sends out information about that payment to various third parties with whom you don't automatically have a voluntary relationship.
Another problem is that the payment network operator is very likely to know your entire buying behaviour - what you buy and where you buy it. Especially in Slovakia, after the introduction of the eKasa system, information is stored in a database accessible from the Internet not only about where and for how much you bought, but also exactly what items you bought. The information that you have printed on the receipt will be sent directly to the Financial Administration. Of course, the receipt (unlike an invoice) does not directly state your identity - but when you pay by card, it is possible to match the identity to the receipt (by terminal and amount).
In addition, this information is stored in the systems for a long time. I personally find it very annoying when a bank employee digs into my account movements in an attempt to sell me other products. It is clear to me that any bank employee can theoretically see all my account movements and get quite a lot of sensitive information. And not only theoretically. There is a well known case in my country where a bank employee, Filip Rybanic, abused this to leak private bank information about a politically exposed person’s account. In this case, however, the court found the bank employee guilty of a criminal offense.
Thus, classic payment networks are the worst possible from the point of view of privacy - they show not only when and for how much, but also where I bought (name of the store, location of the terminal).
It is important to understand that we do not need to know the identity of the customer to provide most products and services. We are sometimes forced to do so by regulation, but it is not necessary for the actual provision. If I am selling virtual servers, phone number services, domains, web addresses, access to software as a service, an e-book, an online course, and so on, I don't need to know the customer's first name, last name, and address at all. And if I don't have that information, I don't need to protect it.
Cryptocurrencies do not automatically carry an identity with the payment. I don't need to know your email, first name, last name or address to create a cryptocurrency account. A wallet-signed transaction is all I need to make a payment. Cryptocurrencies thus make it easier to comply with government regulations such as GDPR - if I don't have personal data, I don't have to protect it.
From this perspective, cryptocurrencies preserve both the privacy and security of the payment at the same time.
Travel rule
However, the invasion of privacy is making its way into cryptocurrency payment networks as well. The story of financial regulation is a complicated one, but I think it is a very interesting one. Most people think that the way that anti-money laundering regulations and many others are created is probably like this - officials (of the European Union, for example) sit down with experts, try to come up with sensible rules, and then put those rules forward as a proposal to be debated by a commission and later the parliament. This gets approved and then the parliaments of the individual EU countries adopt it into their legislation. This is the visible part, which comes after the rule has been in place for a long time. So what is the reality?
It works like this. FATF-GAFI, a non-profit and non-governmental organisation, issues "recommendations" to combat money laundering. It also produces "watch lists" of countries or organisations that are not doing enough to combat money laundering. If a country or organization wants to show that it is fighting money laundering, the country or bank in the payment network accepts the FATF-GAFI "recommendations." Since this is the consensus standard of the majority in the payment network, if an entity wants to participate in the payment network, it must somehow prove that it is fighting money laundering.
This is most easily demonstrated by implementing their recommendations as rules - and following and enforcing those rules on other partners. The European Union's AML5 is the implementation of the FATF-GAFI recommendations into a coherent legal framework. Many of these rules were already being enforced by banks and countries before regulation was ever adopted, because if someone wanted to send money to the US, for example, the correspondent bank would ask them what they were doing against money laundering. And the easiest thing to do is to show 'we are implementing this standard'.
That is, the adoption of rules in the banking network goes the other way around - it arises through mutual coercion in the banking network and then gradually translates into written rules. Let us note that the regulation of the banking network is done by a non-profit, based in the OECD building in Paris, which is not elected by anyone and has no official legislative power. Yet it can write rules that the whole world follows - not just members of the OECD, the EU or any other entity.
The FATCA and OECD CRS regulations were adopted in a very similar way - they were "virally disseminated through the network effect". Simply in a "if you want to do business with us, you have to follow these rules" way.
FATF-GAFI has a second role - enforcement, which "monitors money laundering". So, for example, they will find that Panama has not directly implemented the FATF-GAFI rules into law, but has fought money laundering in its own way. The result was that in 2019, Panama was put on a "watchlist" of jurisdictions that are at risk from a money laundering perspective. They didn't get there because they were proven to have laundered money in specific cases, but because they chose to fight money laundering in a different way.
What does it mean? Anyone following the FATF-GAFI recommendations must specifically screen all transactions with Panama. This slows down international trade, which is why Panama has done everything it can to get off the watchlist – FATF-GAFI has practically put a law on the table for MPs to pass. The OECD CRS rule has been extended in a very similar way.
What does this have to do with Bitcoin? One of the FATF-GAFI "recommendations" is to "tag" cryptocurrency transactions. If a transaction is worth more than $1000, it should somehow verify the identity of the sender and communicate it to the other party. This information does not need to go directly through the blockchain. Protocols have started to emerge that allow such an exchange of personal data.
The first to follow this rule are the exchanges that support deposits and withdrawals in government fiat money. These need to be plugged into the classical financial network for their business. The FATF-GAFI travel rule has already been adopted and is being enforced through the financial system, regardless of whether it has been approved by national or EU parliaments.
These rules are now being extended to other VASPs (Virtual Asset Service Providers – a new term introduced by FATF-GAFI), which include wallet providers, payment gateways and practically everyone who is touching crypto in any way. And one of the “recommendations” to be implemented is to make sure that VASPs only accept cryptocurrency transactions from wallets of other VASPs. So “self-hosted” or “anonymity enhanced” wallets are to be considered of high risk of money laundering and should be “considered” deeply. Because investigating transactions is often not profitable, this is a “nicely sounding” ban. We will see how exactly it will be implemented.
How does this enforcement work in practice? An illustrative thought experiment:
- We declare that "untagged" BTC transactions are used for money laundering
- We will create a standard for transaction tagging
- Banks, exchanges and the like will start implementing this because they don't want their partners in the fiat payment network to close their accounts or disconnect them from the payment network
- FATF-GAFI monitors which countries and which institutions do and do not comply
- If a country ignores this (and thus is not "in the cartel"), they declare them a "money laundering center" and put them on a watchlist
- This makes it much more difficult for them to interact with traditional financial systems of the world. The watchlist is global for all transactions, so if someone does not want to implement a travel rule for cryptocurrency transactions, the consequence is a restriction of access to international trade overall - the watchlist does not just apply to one segment. The country is very likely to say "screw some few Bitcoin traders, let's enact this because we don't want to be on the watchlist".
- FATF-GAFI and the consultants will supply the exact wording of the law, which they will translate into the local language and correctly paraphrase the sections of the “recommendations”. Members of Parliament pass the law in Parliament, basically unaware of what it is and how it came about.
- FATF-GAFI will add a press release to its website on its successful cooperation with another country and will issue a case study on how it has curbed further money laundering.
Every deposit and withdrawal from the exchange will therefore be marked with our identity - name, surname, address, residence, etc. That "innocent KYC data" that used to be collected and shared with chain analysis firms or under court order at most will become part of our transactions - by the way, this data can be populated retrospectively as well, since they knew your identity when you made withdrawals and know which transactions are withdrawals of your funds. This is if you went through a KYC exchange.
Dystopian vision of introducing financial tracking into cryptocurrencies
In time, states may force merchants to accept only cryptocurrencies marked as such. If a person wants to use cryptocurrencies to pay for anything legally, anonymity will be gone. And so the individual cryptocurrency "coins" will be divided into legal (marked with an identity) and illegal, which will be unusable for legal purchases. I don't mean that some cryptocurrencies will be legal and some won't, but the balance in the wallet will be marked and unmarked. Think of it like banknotes, some are stamped and you'll be able to use those to buy at the grocery store or hipster cafe and unstamped ones that will only be usable in the grey and underground economy.
Technical solutions to increase privacy would be unusable in such a case - coinjoin or other mixing and privacy-enhancing methods would simply turn the cryptocurrency units into unmarked ones. Using this mixing technique would be linked to our identity, so we would very likely be visited by some financial authority asking why we put our money in an anonymizing tool.
I think an even worse thing than not regulating or banning cryptocurrencies (which everyone thought was the worst case scenario, with the result "crypto can't be banned") would be to legalize it. And only legal, stamped crypto will be allowed to be used.
Why bother with cryptocurrencies then, if this is a possible scenario in my opinion? In fact, such a dystopian future is already well established in the fiat world. Cryptocurrencies are internet protocols that allow privacy and can play the role of digital cash even in a parallel economy (see appendix). Cryptocurrencies are therefore getting better from a privacy perspective and allow for a parallel economy without surveillance - and this is their advantage even if "approved" uses continue to be monitored.
We already see the first steps towards this dystopian future in the current FATF-GAFI recommendations proposal.
About the book
This text is a chapter from my book Cryptocurrencies - Hack your way to a better life. You can get at it:
- English ebook and paperback on my store
- English ebook and paperback on Amazon
- Spanish version: my store or Amazon
Use coupon FREEDOMTECH for a 10% discount on my store.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX or Signal groups:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:

The Tornado Cash indictment was only the latest salvo in the ongoing “crypto wars.”
In an astounding move, the U.S Department of the Treasury’s FinCEN agency has issued a new proposal that seeks to broadly expand the terrorist financing restrictions in the PATRIOT Act to cryptocurrencies. This extension would have all cryptocurrency privacy tools, regardless of technical function, custody, or decentralization be considered a threat to national security, and thus subject to extensive reporting to FinCEN by all regulated entities. This reporting would lead to a centralized and comprehensive list of all users of privacy tools, making further crackdowns and legal action against those seeking privacy much easier in the future.
This proposal is the latest in a long line of aggressive and expansive efforts by the U.S. government to collect information, collate it, and often prosecute anyone seeking to provide or use privacy tools when using cryptocurrencies, and will further limit the ability of individuals world-wide from gaining access to necessary financial privacy in the cryptocurrency economy.
The Supposed Justification
To propose a broad and sweeping set of additional regulations, FinCEN must set forth clear reasons before the broader government and populace for why this new regulation is supposedly necessary. In the aftermath of the outbreak of conflict in the Middle East, FinCEN has shifted their “boogeyman” from North Korean hackers to focus more heavily on Hamas and ISIS. Wielding a security risk that is a pressing topic in the mainstream media is an age-old tactic of the U.S. government, and while it’s clear this proposal was in the works long before the conflict in the Middle East broke out, they’re attempting to use it to provide “teeth” for this proposal.
There seems to be very little evidence to support these claims, however, with even Chainalysis denouncing much of the attribution of cryptocurrency usage to Hamas and other terrorist organizations as grossly exaggerated due to inaccurate chain surveillance, saying that they “have also seen overstated metrics and flawed analyses of these terrorist groups’ use of cryptocurrency.” But let’s take a look at the specific claims made by FinCEN in the proposal around justification ourselves.
Criminals like privacy, shockingly
While the claims made in the proposal are that illicit actors are heavy users of privacy tools, FinCEN makes no explicit claim on how much funding Hamas has received through cryptocurrency, much less how much (if any) of their funding flowed through privacy tools. Instead, they leverage their previous prosecutions of privacy tool admins and developers to attempt to show that criminals like privacy (shocker):
The multiple U.S. Government actions against CVC mixers… demonstrate that CVC mixing provides illicit actors with enhanced anonymity in CVC transactions, allowing them to more easily launder their illicit proceeds in CVC.
The cases referenced here in the proposal are those of Helix and Tornado Cash, both of which were cases against the operators of privacy tools, instead of any effort to go after the illicit users themselves. In the case of Helix, the government was only able to show that ~12% of deposits into Helix were from illicit sources, even though they captured the entire mixing infrastructure and had full access to all mixing wallets and transaction history. In the case of Tornado Cash, the government was only able to attribute ~7% of inflows to illicit sources despite all inflows on the Ethereum network being transparent by default and almost always trivial to trace to their origination point.
Illicit usage increasing, or legitimate users being scared off?
One of the other commonly cited justifying statistics throughout the proposal is that of illicit usage supposedly increasing over the past few years in the cryptocurrency space. To support these claims, FinCEN relies almost exclusively on Chainalysis’ reporting, and yet exclude the possibility of their fear tactics having an outsized impact on legitimate usage of privacy tools.
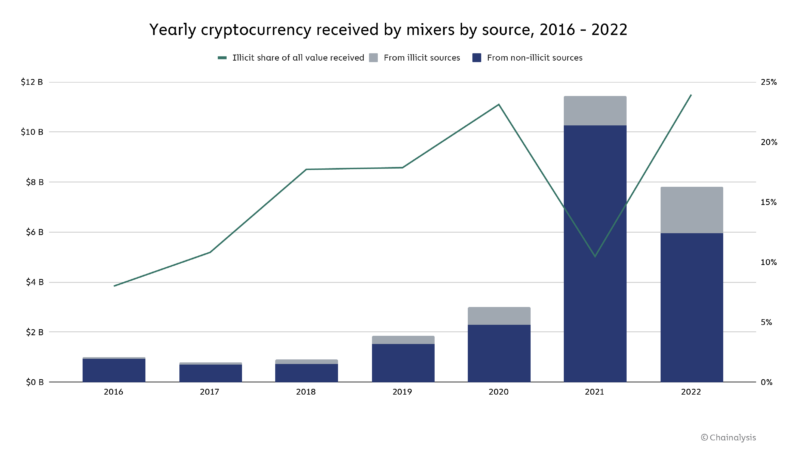
However, the analysis noted the CVC that was sent to CVC mixers in 2022 was more likely to come from illicit sources than in previous years—24 percent of the $7.8 billion processed by mixers in 2022 versus 10 percent of the $11.5 billion processed by mixers in 2021.
While on its face this seems like a serious increase in illicit usage as a share of total usage, you have to fully consider what happened in 2022. In August, the DOJ issued sanctions against the entirety of the Tornado Cash project, signaling to the cryptocurrency world that even legitimate usage of privacy tools could be considered illegal overnight. In addition to that, the DOJ also prosecuted several other privacy tools, including the aforementioned Helix. These two cases were used as weapons of fear against both illicit and licit users alike, and led to a significant drop-off in total usage of privacy tools in the space. Even Chainalysis themselves makes the same conclusion in their report, stating that “[t]he data suggests that legitimate users have decreased their use of cryptocurrency mixers” as a result of these actions.
Can we trust Chainalysis’ numbers?
These claims all rely on Chainalysis’ surveillance software being provably accurate and effective, something that we learned even Chainalysis’ own head of investigations doesn’t claim in a recent article on Bitcoin Magazine by L0la L33tz. L0la has spent the past few months digging through court documents and interviews to pull back the veil on the cooperation and dealings between the U.S. government and Chainalysis, so I reached out to her for comments on this proposal. She made it clear that we should be wary of their methods, as:
…the majority of heuristics and clustering algorithms applied have no scientific basis. Blockchain surveillance has no KPIs. The methodologies provided to inform FinCEN’s guidance have not been independently verified, leaving them subject to biases, faulty calculations, and wrong assumptions. FinCEN cannot, beyond a reasonable doubt, exclude the possibility that the Treasury has been misled or misinformed in its entirety by private corporations braving substantial conflicts of interest.
L0la’s comments are insightful and pointed; using a piece of black box software run by a company that stands to make immense profits if this proposal passes leads to all kinds of broken incentives and conflicts of interest. While Chainalysis will of course claim that their numbers are valid, even competitors in the chain surveillance space have made it clear that their work is “more art than science” in a marketing blog post. When both the government and their contracted agent in Chainalysis stand to gain power and wealth through this proposal, we should be very wary of trusting their black-box figures.
For more on the topic of Chainalysis and their recent battle to keep their proprietary methods secret, you can dive into some of L0la’s other articles along with a podcast below:
- Chainalysis, the Theranos of blockchain forensics? | Bitcoin Magazine
- Chainalysis denounces Bitcoin Core contributor as "unqualified" | Bitcoin Magazine
- US government frames Bitcoin privacy as "criminal" | Bitcoin Magazine
- Is Chainalysis Prosecuting Innocent People with L0la L33tz | What Bitcoin Did
What counts as a “mixer?”
Before the sanctions and subsequent indictment against Tornado Cash, the previous understanding of what counted as a “mixer” and “money transmitter” under FinCEN guidance was thought to be limited to only those services that take custody of funds and have a centralized business behind them. Unfortunately, the U.S. government has taken leaps to expand that definition over the past 18 months, leading to the proposal at hand.
The term “CVC mixer” means any person, group, service, code, tool, or function that facilitates CVC mixing. FinCEN acknowledges this definition is relatively broad; however, given the nature of CVC mixing, FinCEN deems the breadth of this definition to be necessary.
FinCEN held back no punches here, deeming anything and everything that could provide a shred of privacy to be categorized as a “mixer” under the new set of rules. To further clarify their definition, they expand on the act of “mixing” below (emphasis mine):
The term “CVC mixing” means the facilitation of CVC transactions in a manner that obfuscates the source, destination, or amount involved in one or more transactions, regardless of the type of protocol or service used.
While FinCEN outlines six specific categories of tools as a mixer, they are clear that these are just example categories and are not an exhaustive list. These categories are:
- “Pooling or aggregating CVC from multiple persons, wallets, addresses, or accounts”
- “Splitting CVC for transmittal and transmitting the CVC through a series of independent transactions”
- “Using programmatic or algorithmic code to coordinate, manage, or manipulate the structure of a transaction”
- “Creating and using single-use wallets, addresses, or accounts and sending CVC through these wallets, addresses, or accounts in a series of transactions”
- “Exchanging between types of CVC, or other digital assets”
- “Facilitating user-initiated delays in transactional activity”
These categories would seemingly include every cryptocurrency privacy tool (and many non-private tools, incidentally) currently in existence, including (but definitely not limited to):
- Centralized mixing services (i.e. Helix)
- Centralized Coinjoin tools (i.e. Wasabi Wallet)
- Decentralized Coinjoin tools (i.e. Joinmarket and Payjoins)
- Centralized “instant exchangers” (i.e. FixedFloat)
- Decentralized privacy tools (i.e. Tornado Cash)
- Decentralized privacy coins (i.e. Monero)
- Decentralized exchanges used to swap between cryptocurrencies (i.e. Bisq)
Any tool or service that prevents trivial tracking of the flow of funds on-chain falls under this category, and thus any usage of these tools would count as “mixing” under this new compliance regime. FinCEN fully understands that this scope is incredibly broad and encompasses many tools normally outside of the scope of privacy tools, and yet seems to not care at all. L0la L33tz, author of the aforementioned article on Chainalysis methods, added in her comments that this flagging of regular individuals seeking privacy as high risk arbitrarily assumes guilt. She goes on to add that “[t]he attempt to hold a group of people responsible for the unlawful actions of individuals, as suggested in FinCEN‘s proposal, is deemed collective punishment and illegal under international law.”
What this means for regulated entities
The immediate impact of this proposal would be increased reporting for regulated entities like cryptocurrency exchanges, requiring them to not only collect their normal KYC/AML information from customers, but also additionally provide detailed information on any user who has a history of interaction with mixers in the past. This additional reporting would then be bundled with all known KYC/AML information on any user of privacy tools and sent directly to FinCEN within 30 days. While FinCEN claims that his will not have a major impact on costs for regulated entities, it will involve drastically more expansive chain surveillance by companies like Chainalysis, increased reporting requirements, and a host of new data points to collect and collate for submission to the government.
This additional cost and effort will necessarily increase costs for the customer as exchanges and service providers must spend far more on surveiling and reporting on their customers activities.
The ineffectiveness of the compliance regime
FinCEN makes many claims about how effective this new proposal will be at dissuading and prosecuting privacy tool usage by illicit actors, and yet provide no concrete data to back their claims. When we look at the history of the compliance regime and attempt to gauge any sort of success metrics, it becomes incredibly clear that their attempts to fight illicit usage through reporting and regulation have been colossal failures that cost financial entities (and thus their customers) far more than they’re worth.
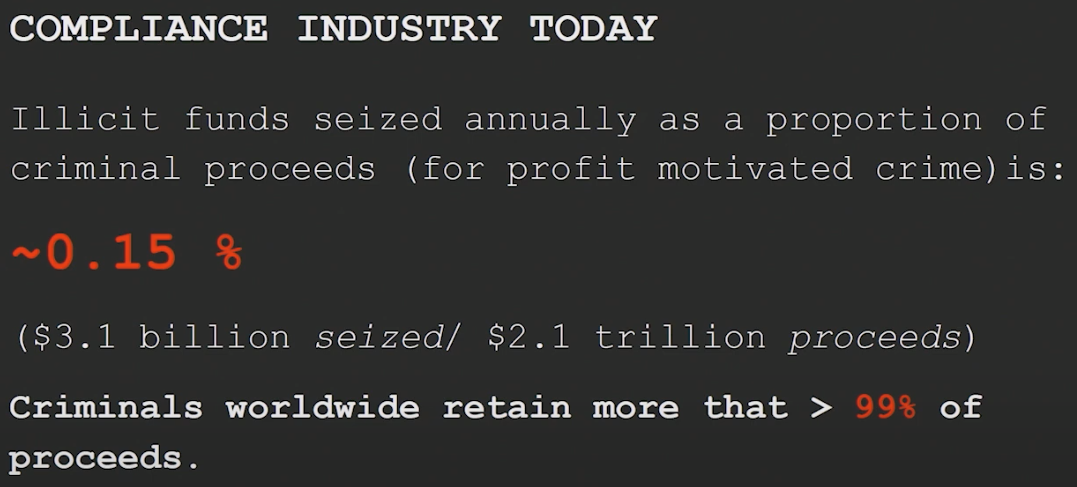
Not only is the financial loss due to compliance costs detrimental to an effectively functioning financial system, the privacy costs associated with our financial activity being surveiled, collected, and collated are hard to measure but sure to haunt us in the future. For an excellent primer on our rights to human privacy and the complete failing of the compliance regime, we recommend this talk by Silke Noa at this year’s Hacker’s Congress Paralelni Polis:
What this means for you
If you use any U.S. service providers or exchanges
This proposed regulation would mean that any time you interact with a U.S.-based regulated entity — i.e. a centralized exchange like Coinbase — they will be required to report you directly to FinCEN if there is any history of mixer usage associated with your funds. This reporting would include the standard KYC/AML data but be greatly expanded. The proposal includes an exhaustive list of information to be collected and submitted to FinCEN within 30d of mixing activity being noticed:
- The amount of any CVC transferred, in both CVC and its U.S. dollar equivalent when the transaction was initiated
- CVC type
- The CVC mixer used, if known
- CVC wallet address associated with the mixer
- CVC wallet address associated with the customer
- Transaction hash
- Date of transaction
- IP addresses and time stamps associated with the covered transaction
- Narrative
- "A summary of investigative steps taken, provide additional context of the behavior, or other such information the covered financial institution believes would aid follow on investigations of the activity."
- Normal KYC/AML information:
- Full name
- Date of birth
- Address
- Email address for all accounts
- Unique identifying number (i.e. SSN)
Any usage of mixers by FinCEN’s broad definition will get you added to a special list and all of your personal details sent off to FinCEN for tracking, making it trivial for the government to take further action to limit or prosecute any usage of privacy tools in the future.
This proposed rule would compel covered financial institutions to attribute a covered transaction to the involved customer(s) and report this information to FinCEN.
The creation of lists are always the starting point for further attacks against human rights when it comes to governments, and their clear hatred for privacy tools makes this specific list especially dangerous to be on moving forward.
If you use any international service providers or exchanges
While this proposal will initially only impact regulated entities that are subject to U.S. law, there is broad precedent for FinCEN’s proposals being rapidly adopted by other countries and ruling bodies across the globe. FinCEN sets much of the global regulation through its actions, and unfortunately much of the world quickly follows in their footsteps. Even if you are not currently subject to this proposal, that does not mean that it won’t apply to the services and exchanges you use today in the near future.
If you don’t use any service providers or exchanges
For those of you who have already opted out of the broken compliance regime and begun to use decentralized exchanges and no-KYC tools, this will have little impact on you today. It is likely that long-term usage of these tools will lead to funds being considered tainted and thus subject to this reporting if they ever enter the standard, regulated economy, but within the burgeoning Bitcoin circular economy things can go on as normal.
What this means for the cryptocurrency space
Ultimately, this is a further monumental leap in the U.S. governments attempts to prevent the usage of privacy tools in the cryptocurrency space. This crackdown, especially with the broad definitions imposed by FinCEN here, will kick-start the bifurcation of cryptocurrencies into two worlds — white-market and black-market money.
Users and entities who avoid privacy tools and decentralized exchanges will be able to continue operating within the “gilded cage” of the approved regulated entities and functional normally, albeit with much tighter surveillance and scrutiny around their on-chain activities.
Those who choose to take action and seek financial privacy through privacy tools, on the other hand, will be banished to a black-market circular economy. This economy will have to function separately from the state and traditional on- and off-ramps like centralized exchanges, as any usage of these services while leveraging privacy tools would lead to an automatic reporting of activity and personal information to a state intent on shutting down said tools.
The cryptocurrency world will split into two separate economies, one that functions as an add-on to the traditional finance and compliance regime, and one that acts as an independent and self-sustaining circular economy.
Guilty until proven innocent
This line of reasoning by FinCEN continues the steps of the U.S. government to shift the judicial system from one of “innocent until proven guilty” to a tyrranical system of “guilty until proven innocent," according to L0la. This shift has been seen in the case against Tornado Cash and even in subsequent efforts by the Ethereum community to bend to regulators. FinCEN’s chosen approach would have any attempt to seek privacy by the average individual have them thrown into the same suspicions as terrorists and dictators, making the words of Phil Zimmerman ring more true than ever:
If privacy is outlawed, only outlaws will have privacy.
What we can do
Be optimistic
As we laid out in our article on the Tornado Cash indictment, the drastic steps governments are taking to prevent the usage of privacy tools in the cryptocurrency space shows that they feel threatened:
It may not be immediately apparent, but one of the biggest takeaways is quite simple – we're winning. The fact that a massive government like the U.S. feels threatened enough by privacy tools to take overt legal action shows that the powerful tools being built out to empower you, the user, are working. The immense uptake of privacy tools like Signal, Proton Mail, and the Tor network have started to shift the balance of power back towards the individual.
The more push-back and fight we see from governments across the globe against encryption and privacy-preserving tools, the more evidence we have that the tools are actually working.
In addition, we can be optimistic because this is still just a proposal as of publishing. It is possible that this proposal will be shot down through mass sentiment and outcry. We are hopeful that will be the case and will do all we can to help prevent this proposal from being accepted as-is.
Keep using privacy tools
The last thing we want for our readers is that you should give in and stop using privacy tools today. There are excellent tools out there in the space that you can leverage to gain on-chain privacy, and we must continue to use them to gain the full measure of freedom that freedom money like Bitcoin can provide. Tools that allow you to reclaim your financial privacy like Samourai Wallet (a powerful, privacy-preserving wallet for Bitcoin) and Monero (a cryptocurrency that protects sender, receiver, and amount in every transaction) are indispensable tools for freedom, and should be something you practice with regularly, no matter what the state says.
If we allow regulation and fear tactics to dissuade us from fighting for the right to privacy, our ability to transact without fear of surveillance or censorship will be slowly stripped away from us.
Opt out of KYC exchanges covered by this guidance
The most practical advice we can give here is to opt out of the broken compliance regime entirely. The crux of FinCEN’s proposal hinges on centralized exchanges with broad swaths of user data complying, and most of these regulated entities will happily go along if profits continue. Thankfully, there are excellent solutions out there for getting into (and out of) cryptocurrency without being subject to heinous over-regulation and surveillance. These solutions make it so that you can continue using privacy tools to protect your right to financial privacy without being cut-off from the traditional economy.
If you want to learn more about where to get started with joining the “no-KYC” movement, you can find some excellent resources below:

Let your voice be heard
A key way that you can support the push against this proposal is to support it publicly. Sharing posts like ours within your sphere of influence (friends, family, social media following, etc.) can help to shift public sentiment away from invasive and abusive proposals like this one and make it more difficult and costly for FinCEN to enact this or similar regulation.
Join the Conversation
If this post has sparked an idea or motivated you to get involved, there is no better next step then to join the conversation here at freedom.tech! Subscribers can jump straight into the comments below, or you can join our community SimpleX or Signal groups:

If you have feedback for this post, have something you'd like to write about on freedom.tech, or simply want to get in touch, you can find all of our contact info here:











