The post Steps Involving In an OpenVPN Setup appeared first on IB Computing.
]]>This piece of article provides step-by-step instructions for OpenVPN setup:
- Search and Find and your public IP address
- Download openvpn-install.sh script
- Run the script to install OpenVPN server
Search and Find your public IP address
Use any one of the following command to find out your IPv4 public address. If your internface name is eth0 or eth1, enter the following in terminal:
ip addr show eth0
or
ip addr show eth1
or
Use the host command or dig command as follows:
host myip.opendns.com resolver1.opendns.com
or
dig TXT +short o-o.myaddr.l.google.com @ns1.google.com
Download openvpn-install.sh script
Type the following command in terminal:
wget https://git.io/vpn -O openvpn-install.sh

Run the Script to install OpenVPN server
To run the installation script, use the following command:
sudo bash openvpn-install.sh
(You will need to enter your system login password for the current user here)
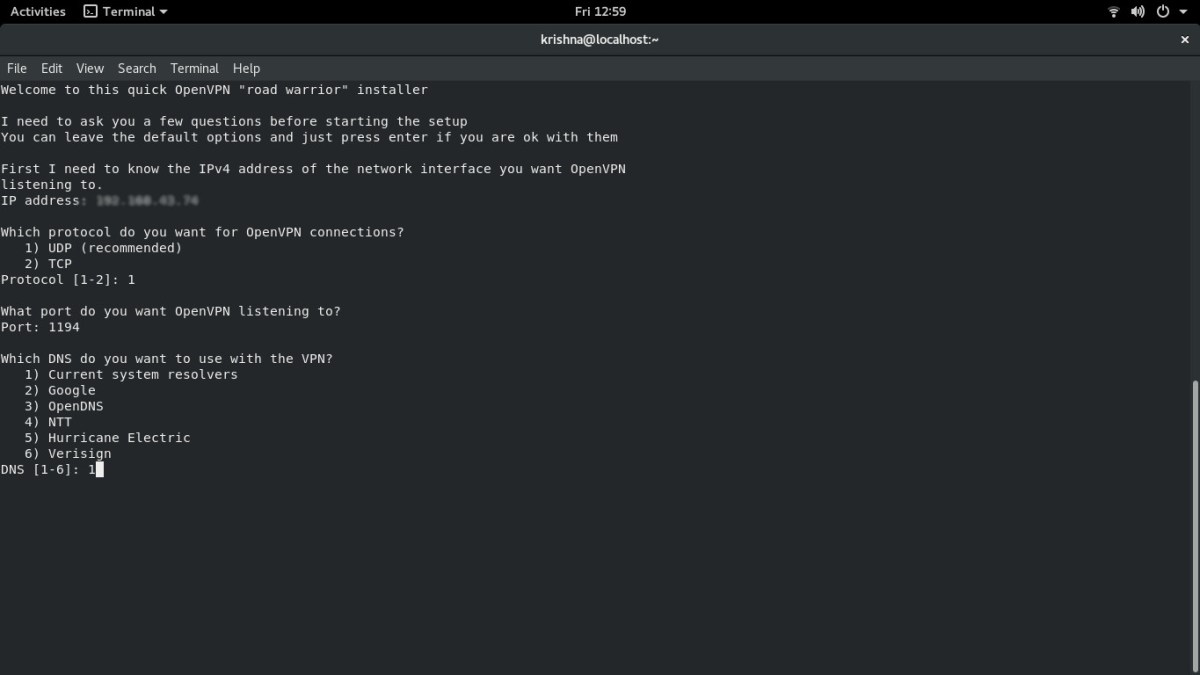
This will further generate keys, DH parameters and more as follows:

And we are done here. The OpenVPN setup is now accomplished and is ready to use.
The post Steps Involving In an OpenVPN Setup appeared first on IB Computing.
]]>The post Linux Kernel 4.15 Released With Spectre & Meltdown Patches appeared first on IB Computing.
]]>Linus Torvalds announced the release of the Linux kernel 4.15 series on 28th January 2018, the first major version release with patches against the Meltdown and Spectre security vulnerabilities.
Linux kernel 4.15 has been in development since the last two months. The new release arrives late by one week than the actual expected date. The kernel developers were under extreme pressure to redesign the kernel against the infamous Meltdown and Spectre attacks which resulted in the slowest Linux kernel release since 2011.
After a release cycle that was unusual in so many (bad) ways, this
last week was really pleasant. Quiet and small, and no last-minute
panics, just small fixes for various issues. I never got a feeling
that I’d need to extend things by yet another week, and 4.15 looks
fine to me.
Linux kernel 4.15 is reportedly the first kernel series that is fully patched against the Meltdown and Spectre hardware security vulnerabilities. But unofrutnately the patches are only available for the x86 and PowerPC (PPC) architectures. Linux kernel 4.15 is expected in the stable repositories of major GNU/Linux distros soon.
Also, it is worth pointing out that it’s not like we’re “done” with
spectre/meltdown.
Linus was so angry with the Intel developers last week such that he didn’t even hesitate to use the F word publicly.
As it is, the patches are COMPLETE AND UTTER GARBAGE.
They do literally insane things. They do things that do not make
sense. That makes all your arguments questionable and suspicious. The
patches do things that are not sane.WHAT THE F*CK IS GOING ON?
And that’s actually ignoring the much _worse_ issue, namely that the
whole hardware interface is literally mis-designed by morons.

What’s new in the Linux Kernel 4.15 release
- Meltdown and Spectre patches for the x86 and PowerPC (PPC) architectures.
- Support for RISC-V architecture
- Support for the User-Mode Instruction Prevention feature on Intel CPUs
- A new cgroupv2-enabled CPU controller for better CPU usage restrictions.
- Support for AMD Secure Encrypted Virtualization
- Improved video support for AMD GPUs.
- Added modesetting to the AMDGPU open-source graphics driver for supported AMD Radeon GPUs.
- Improved power usage for machines with SATA Link Power Management feature.
- Various updates regarding networking, filesystems, grpahics, drivers and more.
Anyway, while spectre/meltdown has obviously been the big news this
release cycle, it’s worth noting that we obviously had all the
*normal* updates going on too, and the work everywhere else didn’t
just magically stop, even if some developers have been distracted by
CPU issues. In the *big* picture, 4.15 looks perfectly normal, with
two thirds of the full 4.15 patch being about drivers, and even the
arch updates are dominated by the arm DTS diffs, not by CPU bug
mitigation.So the news cycle notwithstanding, the bulk of the 4.15 work is all
the regular plodding “boring” stuff. And I mean that in the best
possible way. It may not be glamorous and get the headlines, but it’s
the bread and butter of kernel development, and is in many ways the
really important stuff.
Download Linux Kernel 4.15
Those who aren’t patient enough can download Linux Kernel 4.15 from kernel.org and compile the sources right now. Otherwise you can wait until the new release arrives in your GNULinux distro’s official repository which is expected soon in the light of Spectre and Meltdown hardware security vulnerabilites.
The post Linux Kernel 4.15 Released With Spectre & Meltdown Patches appeared first on IB Computing.
]]>The post Spectre and Meltdown Delaying New Linux Kernel Release appeared first on IB Computing.
]]>Or is Intel basically saying “we are committed to selling you shit
forever and ever, and never fixing anything”?Because if that’s the case, maybe we should start looking towards the
ARM64 people more.

Here’s the official announcement from Linus Torvalds, regarding the delay in new Linux Kernel release, through the mailing list:
I really really wanted to just release 4.15 today, but things haven’t
calmed down enough for me to feel comfy about it, and Davem tells me
he still has some networking fixes pending. Laura Abbott found and
fixed a very subtle boot bug introduced this development cycle only
yesterday, and it just didn’t feel right to say that we’re done.So I’m doing an rc9 instead. I don’t particularly like to, but I like
it even less releasing something that doesn’t seem baked enough.Some people have already started sending me pull requests for 4.16
(generally because they aren’t expecting to be online next week and
expected the merge window to open). I appreciate it, and I’ll keep
them queued up, I just won’t start applying them quite yet.Anyway, rc9 is mostly arch updates (x86, arm, powerpc, mips) and
drivers (gpu, networking and md). And some core networking. And then
there’s various random misc fallout (tracing, bpf, and new selftests)I really expect no more delays after this. We’ve had rc9’s before, but
they have been pretty rare (the last one was 3.1-rc9 back in 2011 –
that release went all the way to rc10, and I really don’t think we’ll
do that this time _despite_ all the CPU bug mitigation craziness).Linus
As Linus already mentioned, the last Linux kernel release with more than eight Release Candidates was Linux 3.1 in 2011. Linux 3.1 even got a tenth RC. But since Linus said that there won’t be more delay, let’s hope that Linux 4.15 won’t reach the tenth RC and will release the final version on January 28th. Meanwhile, Linux kernel 4.15 RC9 is now available for download and testing.
The post Spectre and Meltdown Delaying New Linux Kernel Release appeared first on IB Computing.
]]>The post Firefox 58 Release; With Spectre and Meltdown Security Fixes appeared first on IB Computing.
]]>A two-tiered compiler which makes the code compilation fifteen times faster than the current optimizing compiler will be the main attraction of the Firefox 58 release. With the latest compiler changes Firefox can now compile the code while it is being downloaded and in fact compiles faster than being downloaded, means the code will be executed as soon as it is downloaded.
Regarding security updates, the new release will contain fixes for Meltdown and Spectre timing attacks. Firefox was one of the first browsers to respond and release updates to Spectre and Meltdown attacks. Another bug like background sending crash reports without user opt-in has also been fixed.
The upcoming Firefox 58 release will also include other features like support for form autofill for credit cards and improved page render speed for Windows users. Also, Mac OS X users can be happy as WebVR will be enabled on Mac OS X.
Warning: You will not be able to downgrade your Firefox profile to previous versions anymore, for such cases new profiles should be made!

Firefox 58 Release For Developers
- The old Responsive Design Mode has been removed from Devtools.
- A button to pause/play recording network traffic is now implemented on Network Monitor.
PerformanceNavigationTimingAPI has been implemented; it can be used to measure the time to load/unload a document.- Removed prefixed version of
HTMLMediaElement.srcObject - Removed support for prefixed WebGL extensions.
- TLS handshake timeout is implemented with the default value of 30seconds.
- Firefox Android now supports “Add o home screen”.
How to download Firefox 58?
Firefox 58.0 beta can be downloaded from Mozilla repo or you can wait for the official stable releases. If you are a Linux user, you can either download, extract and run the Mozilla’s official image or wait till the new update comes to your distribution’s package repo.
The post Firefox 58 Release; With Spectre and Meltdown Security Fixes appeared first on IB Computing.
]]>The post OnePlus website hacked – Credit Card Information of 40000 customers leaked appeared first on IB Computing.
]]>There were reports by several users on OnePlus forums that they doubt their credit cards were being charged without their knowledge; some Reddit users mentioned that they noticed their cards being used on betting websites. A week later, the company confirmed that the users who purchased phones through their website between the middle of November 2017 and January 2018. 11 have been victims of a credit card information leak.
It seems they did not take care of the basic precautionary measures. The one plus site was hosting the payment page that accepts the users’ payment details on their own site – which is a flawed design by itself since OnePlus is not PCI compliant (Payment Card Industry). If attackers are somehow able to inject malicious code into the website, the users’ data will be at risk. Ideally, all the payment flow should happen through a third-party payment gateway which takes care of everything – from accepting the user input to encrypting the information securely and then processing the payment.
In their statement, the company stated the users who had used PayPal or saved their credit card information before November should not have been affected. The company has since disabled credit card payment option on their website and claims to have quarantined the affected server.

Here is the complete statement from OnePlus:
Hi all,
We are deeply sorry to announce that we have indeed been attacked, and up to 40k users at oneplus.net may be affected by the incident. We have sent out an email to all possibly affected users.
1. What happened
One of our systems was attacked, and a malicious script was injected into the payment page code to sniff out credit card info while it was being entered.
- The malicious script operated intermittently, capturing and sending data directly from the user’s browser. It has since been eliminated.
- We have quarantined the infected server and reinforced all relevant system structures.
2. Who’s affected
- Some users who entered their credit card info on oneplus.net between mid-November 2017 and January 11, 2018, may be affected.
- Credit card info (card numbers, expiry dates and security codes) entered at oneplus.net during this period may be compromised.
- Users who paid via a saved credit card should NOT be affected.
- Users who paid via the “Credit Card via PayPal” method should NOT be affected.
- Users who paid via PayPal should NOT be affected.
- We have contacted potentially affected users via email.
3. What you can do
- We recommend that you check your card statements and report any charges you don’t recognize to your bank. They will help you initiate a chargeback and prevent any financial loss.
- For enquiries, please get in touch with our support team at https://oneplus.net/support.
- If you notice any potential system vulnerabilities, please report them to [email protected]. This is a monitored inbox, but please note, we may not be able to respond to all reports.
4. What we are doingWe cannot apologize enough for letting something like this happen. We are eternally grateful to have such a vigilant and informed community, and it pains us to let you down.
We are in contact with potentially affected customers. We are working with our providers and local authorities to better address the incident. We are also working with our current payment providers to implement a more secure credit card payment method, as well as conducting an in-depth security audit. All these measures will help us prevent such incidents from happening in the future.
A big thank you to our forum user @superdutynick for bringing this incident to our attention!
Sincerely,
The OnePlus Team
As a mobile giant that is dealing with millions of users’ confidential data, they should conduct periodic, in-depth security audits, penetration testing and monitoring. Payment processing should be completely dealt with a reliable third-party service that does their job well. That way, even if the attackers are able to breach the company website, the damage would be minimized.
The post OnePlus website hacked – Credit Card Information of 40000 customers leaked appeared first on IB Computing.
]]>