La entrada Key Takeaways from FP OT Cybersecurity Day 2026 se publicó primero en InprOTech.
]]>The blurred boundary between IT and OT
One of the central debates focused on IT/OT convergence, a line that becomes increasingly blurred as factories continue to digitalize. Experts agreed that this reality requires rethinking three fundamental pillars:
- Protection strategies adapted to hybrid architectures.
- Governance that unifies policies between traditionally separate teams.
- Training for professionals capable of understanding both worlds.
At InprOTech Guardian, we address this convergence through passive monitoring of OT traffic, providing full visibility without disrupting critical operations. Learn more about Guardian →
Lessons from classic incidents
The conference revisited cases that marked the sector, such as Colonial Pipeline, WannaCry or the Jaguar incident. What proved most revealing were not the technical complexities, but the recurring patterns:
- Poorly managed basic configurations.
- Lack of effective network segmentation.
- Wide windows for critical updates.
These examples reinforce the idea that many OT breaches originate from operational deficiencies. Tools like Guardian detect these configuration issues in real time before they escalate. How OT detection works →

Profiles demanded by the OT industry
Industrial cybersecurity requires professionals who combine:
- Deep knowledge of industrial processes.
- The ability to assess critical risks specific to OT.
- Mastery of industry standards (ISA, IEC 62443, etc.).
Beyond technical competencies, the sector also looks for drive and curiosity, along with a willingness to work with emerging technologies. At InprOTech, we help train these profiles through hands-on practice with Guardian.
Key organizations and standards presented
The conference highlighted two key organizations:
- ISA (International Society of Automation): a global reference for standards in industrial automation and control.
- Cybersecurity Agency of the Community of Madrid: the regulatory framework guiding public administrations in OT cybersecurity.
Guardian aligns its capabilities with ISA/IEC 62443 from its design stage. OT standards guide →
Lightning talks: Bluetooth as an unexpected vector
One student highlighted Bluetooth vulnerabilities in OT environments:
- A protocol that is easy to detect and exploit.
- Privacy loss through identifiable wearables.
- Recommendation: systematically disable it when it is not essential.
Guardian includes detection of unauthorized protocols such as Bluetooth within OT networks.
InprOTech’s commitment to vocational talent
At InprOTech, we particularly value initiatives like this because they bring the reality of the sector closer to vocational training students. Strengthening the OT ecosystem means investing in awareness, hands-on training and the development of specialized profiles.
Join our talent program →. Our connected industry needs exactly these kinds of bridges between the classroom and the factory floor.
La entrada Key Takeaways from FP OT Cybersecurity Day 2026 se publicó primero en InprOTech.
]]>La entrada InprOTech deploys the new Industrial Cybersecurity Laboratory and Demonstration Center of the Xunta de Galicia. se publicó primero en InprOTech.
]]>VIGO, 5 March 2026. InprOTech has been awarded by the Xunta de Galicia, through AMTEGA, the contract for the supply, deployment and provision of services of the Industrial Cybersecurity Laboratory and Demonstration Center of Galicia, a strategic infrastructure that is part of a joint initiative of the Xunta de Galicia composed of two complementary laboratories and demonstration centers in the field of cybersecurity.
This initiative is part of the RETECH – Territorial Networks for Technological Specialization project and is developed in collaboration with the National Cybersecurity Institute (INCIBE), an entity under the Ministry for Digital Transformation and Public Administration, through the Secretary of State for Digitalization and Artificial Intelligence, thus consolidating a coordinated commitment by the Xunta de Galicia to strengthening regional cybersecurity capabilities.
The new laboratory will represent a qualitative leap in industrial cybersecurity with the creation of one of the most advanced infrastructures in Southern Europe, strengthening Galicia’s capabilities in this field and acting in a complementary way to the second laboratory promoted by the Xunta de Galicia within the same RETECH program. Together, both laboratories will form an integrated ecosystem that will provide companies, public administrations and technology stakeholders with an advanced environment for experimentation, training, validation and demonstration of solutions aimed at protecting production environments and industrial control systems (OT/ICS).
Furthermore, the center will contribute to increasing the international competitiveness of Galician industry by offering a space where solutions can be validated before reaching the market, fostering the attraction of specialized talent and strengthening Galicia’s positioning as a benchmark in industrial cybersecurity within the framework of the complementary laboratories of the Xunta de Galicia.
These initiatives will be carried out within the framework of the Recovery, Transformation and Resilience Plan funds, financed by the European Union – NextGenerationEU, through INCIBE.

A real testing environment for Industry 4.0
InprOTech’s proposal stood out for its high level of technical specialization and for the creation of a real testing environment that will allow Galicia to position itself at the forefront of cybersecurity laboratories oriented to Industry 4.0, in coordination with the rest of the complementary infrastructures promoted by the Xunta de Galicia within the RETECH program.
The new center is a real critical infrastructure designed to faithfully reproduce industrial scenarios of high strategic value for the Autonomous Community, reinforcing the demonstrative and experimental nature of this network of complementary laboratories of the Xunta de Galicia.
Seven industrial mock-ups
Physical scenarios will be deployed that replicate different strategic industrial sectors of the Galician economy, integrating mock-ups of the water cycle, energy generation and distribution, food industry, manufacturing for the automotive sector and the naval industry.
These mock-ups will allow real processes to be simulated and the impact of cyber incidents to be analyzed in controlled environments. Among the exercises that can be carried out, explained in a way understandable to any audience, are:
- Simulation of attacks that could halt production lines.
- Evaluation of incident impact on control systems.
- Practical training for operational failures or process interruptions.
Hybrid capabilities: physical + virtual
The laboratory will combine physical environments with multi-user simulation platforms and remote capabilities for external teams, enabling unique flexibility.
This will facilitate risk assessment, professional training and the execution of advanced tests without affecting real production environments, reinforcing complementarity with the rest of the demonstration centers of the Xunta de Galicia integrated in RETECH.
Cutting-edge technologies
The center will integrate leading market solutions for:
- OT traffic monitoring,
- asset and anomaly detection,
- industrial firewalls,
- auditing and vulnerability analysis,
- event correlation,
- and advanced incident response tools.
High-value services for Galician industry
Beyond the design and deployment of the laboratory, InprOTech will also assume its operation, offering services aimed at promoting resilience, maturity and capability development within Galician industry.
The operation of the laboratory will generate a continuous flow of knowledge, train new OT specialists and support companies in their cybersecurity evolution, contributing in a coordinated way to the global objectives of the network of complementary laboratories of the Xunta de Galicia developed in collaboration with INCIBE.
InprOTech: experience, specialization and commitment
InprOTech will contribute to the project with a qualified technical team experienced in OT/ICS technologies, promoting a collaborative approach in a Galician project designed to respond to the needs of Galicia’s industry. The initiative combines high value-added cybersecurity capabilities with the reality of the Galician industrial ecosystem, with the aim of promoting a progressive and sustainable improvement in industrial cybersecurity, supporting sectors with different levels of maturity and contributing to the development and training of specialized talent within the region.
“The award of this project represents an important step for InprOTech and reinforces our work in the field of industrial cybersecurity and OT systems. Our experience allows us to approach this project with responsibility and a vision focused on delivering real value to the Galician ecosystem,” says the company’s CEO and founder, Iago Fortes Caramés. “At InprOTech we are already working to live up to the commitment acquired and to contribute, through our expertise, to strengthening sovereign industrial and technological capabilities from Galicia to the world.”
This publication is part of an initiative funded by the European Union – NextGenerationEU and the Recovery, Transformation and Resilience Plan (PRTR), through INCIBE.
Contact:
José A. Cascallana | IC Laboratory Coordinator
+34 886 113 106
[email protected]
La entrada InprOTech deploys the new Industrial Cybersecurity Laboratory and Demonstration Center of the Xunta de Galicia. se publicó primero en InprOTech.
]]>La entrada TAPs vs Port Mirroring se publicó primero en InprOTech.
]]>To protect industrial environments, it is essential to collect and observe network traffic. In this context, InprOTech Guardian, our real-time industrial network monitoring solution, enables continuous and non-intrusive analysis of industrial network traffic, facilitating early detection of anomalies, unauthorized behaviors, operational failures, and potential cybersecurity incidents, while also providing visibility into connected assets, vulnerabilities in deployed services, and normal communication patterns. To adapt to different environments and operational requirements, InprOTech Guardian3 can collect traffic using two technologies available in the industry: Port Mirroring (also known as SPAN, Switched Port Analyzer) and TAPs (Test Access Points)4.
This article provides an overview of what they are, how they work, their advantages and disadvantages, and which is more suitable depending on the industrial context.
Port Mirroring – SPAN
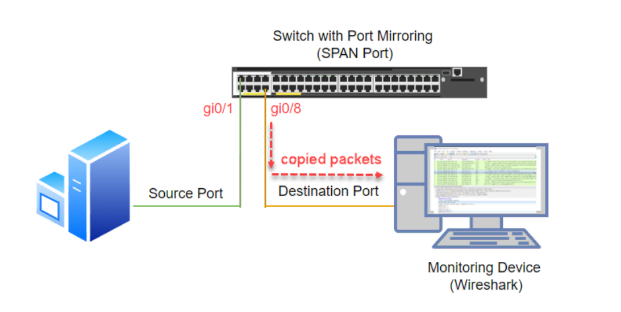
Port Mirroring is a technology available in many switches and network devices that allows traffic from one or more ports or VLANs to be replicated to another port, known as the mirror port, where it can be analyzed.
Typically, an administrator specifies the source port(s) to be duplicated and a destination port from which the traffic can be read. Nowadays, this is a basic feature that can be easily configured through the switch’s web management interface. Some vendors also include options to filter traffic before it is sent, as well as more advanced features such as RSPAN (Remote SPAN, meaning traffic duplication from one switch to another within the network)5.
Advantages of Port Mirroring
- Low cost: does not require additional hardware beyond the switch.
- Flexible: multiple ports or VLANs can be selected.
- Remote configuration: can be changed via software without physical access to cables.
Disadvantages of Port Mirroring
- Packet loss: In high-traffic situations, the switch may not copy all packets. In addition, the mirror port may become saturated and drop data.
- Impact on switch performance: Some implementations degrade switch performance during mirroring.
- Limited visibility: Traffic that does not traverse the switch cannot be observed. It does not capture physical traffic between devices that do not pass through the mirrored ports.
TAPs (Test Access Point)
The taps have a long history dating back to the invention of the telegraph, with a general definition as a small device that can be attached to a communication system, such as a telephone, to secretly listen to communications. However, in the world of telecommunications and cybersecurity, this definition has evolved to refer to a physical hardware component inserted into a network link to split the traffic flow and send an exact copy to an analysis tool without interfering with the original traffic. In this redefinition process, the term has become the acronym Test Access Point6.
Since the emergence of the first network TAPs, communications technology has evolved significantly: speeds have increased, new protocols have emerged, and high-speed fiber optics have become the standard.
At the same time, organizations increasingly need to deploy security and monitoring tools to protect their digital assets, ensure service continuity, and improve user experience.

Types of TAPs
As a result, network TAP technology has also evolved and now offers multiple operating modes that should be considered when designing a reliable and resilient connectivity architecture7. Functionally, they can be classified as:
- Breakout “Normal” TAPs: Traffic copying and forwarding to monitoring tools has high priority to ensure no packet loss.
- Filtering TAPs: Establish traffic filtering rules before traffic reaches monitoring tools.
- Aggregation TAPs: Combine traffic from different sources.
- Replication TAPs: Create multiple copies of traffic data so that several devices can read from different points in the network.
- Bypass TAPs: Prevent network outages caused by devices in case of failure or when maintenance and updates are required.
- Media Changing TAPs: Ensure compatibility between networks and connected devices when technology changes or upgrades occur.
Advantages of TAPs
- Complete traffic capture: No packet loss due to capture device saturation. Exact physical frames are obtained, including collisions or errors.
- No impact on network performance: Being passive, it introduces no latency and does not alter traffic.
- Higher reliability: It is a more attractive solution for critical industrial monitoring, as mentioned earlier, since there are TAPs that maintain connectivity even if they lose power (by-pass).
- Deep visibility: Allows capturing traffic that does not pass through smart switches or complex VLANs.
Disadvantages of TAPs
- Cost: Additional physical devices that can become expensive depending on the installation, especially when deployed across many links.
- Physical installation: Requires access to cabling and may involve brief service interruptions.
- Management and expertise: Requires planning of monitoring ports and analysis. Compared to enabling port mirroring, it demands a higher level of knowledge about the different types and models, which is often limited to manufacturers and partners.
Summary
In summary, both TAPs and port mirroring provide visibility into industrial network traffic, but they address different needs and contexts. Port mirroring stands out for its ease of deployment and low cost, leveraging the capabilities of the switch itself, making it suitable for environments with lower traffic volumes or for occasional analysis; however, its dependence on network device performance can lead to packet loss and incomplete visibility in demanding scenarios. TAPs, on the other hand, offer passive, continuous, and faithful traffic capture without impacting the network or production devices, making them the most robust and reliable option for critical industrial environments where availability and analytical accuracy are priorities. In practice, the choice between one or the other—or even a combined approach—depends on the desired balance between cost, ease of deployment, and required level of visibility.
Both methods are used by InprOTech Guardian to passively capture industrial traffic and perform all necessary monitoring and analysis tasks to prevent, mitigate, and investigate potential issues and attacks.
References
[1] https://www.incibe.es/en/incibe-cert/blog/itot-convergence
[2] Security of IT/OT Convergence: Design and Implementation Challenges. B. Zahran et al.: https://arxiv.org/pdf/2302.09426
[3] https://inprotech.es/guardian/
[4] https://learn.microsoft.com/en-us/azure/defender-for-iot/organizations/best-practices/traffic-mirroring-methods
[5] SPAN (and RSPAN) is CISCO terminology, the first to incorporate port mirroring into their switches.
[6] Technically, this would be a retronym: https://es.wikipedia.org/wiki/Retroacr%C3%B3nimo
[7] https://www.garlandtechnology.com/wpi-network-taps-101
La entrada TAPs vs Port Mirroring se publicó primero en InprOTech.
]]>La entrada Protect and optimize your network with OPNsense se publicó primero en InprOTech.
]]>Protection must be accessible to everyone, regardless of the size or budget of the infrastructure. In this article, we will explore OPNsense, an open-source firewall that offers advanced security and flexibility.
In addition, we will see how InprOTech GUARDIAN integrates with different firewalls to offer optimal cybersecurity service, especially in industrial environments.
History and origin
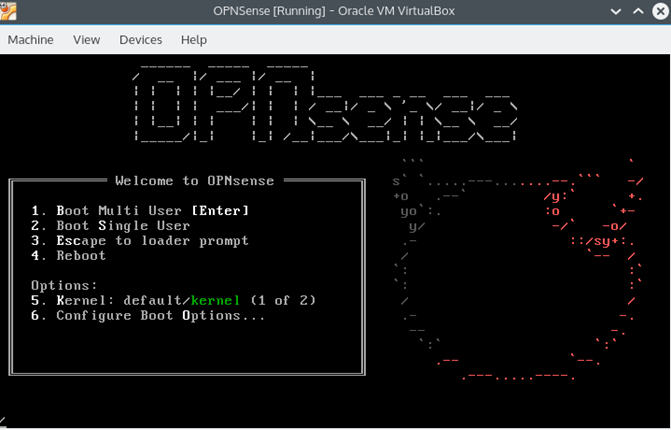
OPNsense was born in January 2015 as a fork of pfSense, which in turn descends from the m0n0wall project. The main motivation for this separation was to have a clearer code base, a more open development community, and a BSD license that offered greater flexibility. Since its inception, the project has remained an open initiative in which users and developers from around the world collaborate, backed by the company Deciso, which also manufactures hardware optimized for OPNsense and offers professional support. The pace of development is steady: two major releases are published each year, supplemented by biweekly security updates. OPNsense Business Edition is qualified in the CPSTIC (Catalog of ICT Security Products and Services) for use in accordance with ENS in specific versions evaluated by the CCN. With this model, the project combines sustained evolution and verifiable guarantees for public and private environments.
Architecture and components
The strength of OPNsense lies not only in its intuitive interface, but also in the solid architecture on which it is built. Here are some of the fundamentals and modules that bring it to life:
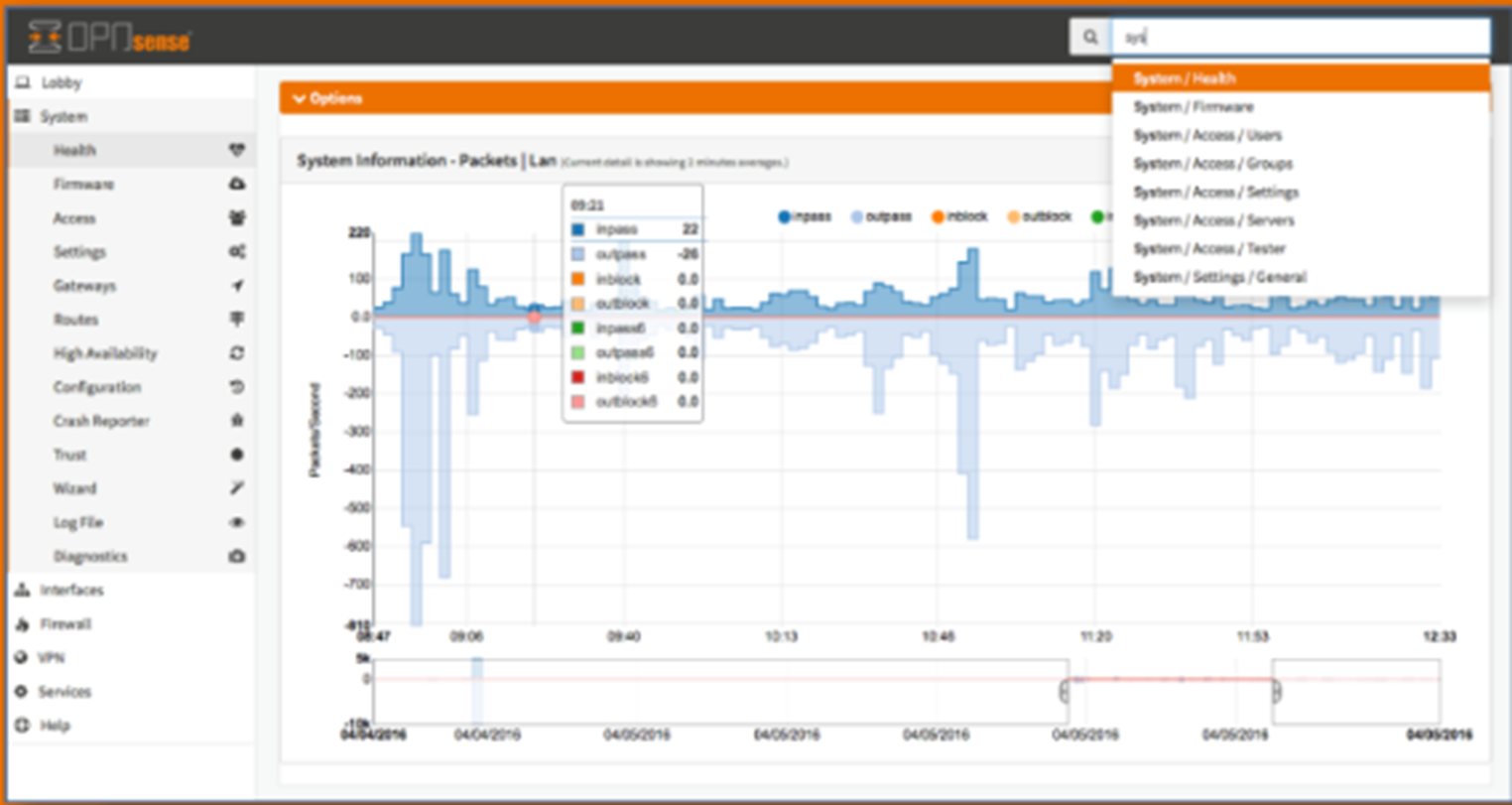
System base
OPNsense is based on FreeBSD, a robust and mature operating system that is widely recognized in the networking world, inheriting stability, performance, and a well-proven ecosystem of utilities.
Its design follows a modular logic, where each component fulfills a specific role and can be extended or updated. Its BSD license reinforces the open nature of the project, allowing both companies and independent users to contribute and reuse the code.
Network interfaces and roles
Flexibility in interface management is another of its strengths. OPNsense supports IPv4 and IPv6 and allows you to define different network roles:
- WAN: connection to the internet
- LAN: internal user network
- DMZ: intermediate zone for public servers
- VLANs: network segmentation using 802.1Q tags
In addition, it supports advanced configurations such as multi-WAN or the use of transparent bridges.
Key internal modules
OPNsense consists of a series of subsystems that cover most network security and management needs:
- Firewall: tracks active connections to apply rules
- NAT: essential for connecting multiple computers to the internet with a single public IP address
- VPNs: facilitate secure interconnection between remote locations and users
- IDS/IPS: for deep traffic inspection
- QoS / traffic shaping: prioritizes or limits traffic according to business needs
- High availability: ensuring continuity in the event of hardware failure
- Logging and monitoring systems: essential for auditing and diagnostics
Extensibility and plugins
OPNsense offers a repository of plugins that extend its capabilities. It also has an API, which facilitates integration with external tools and task automation.
Advantages of OPNsense
OPNsense has strengths that make it a very attractive alternative to other firewalls.
- Open source and BSD license
- Frequent updates
- Modern and easy-to-use interface
- Active community
- Plugin system
- Advanced features
- Deployment flexibility
- CPSTIC certified for use in accordance with ENS
Limitations and disadvantages
Like all technologies, it also has certain disadvantages that should be considered before adopting it in a production environment:
- Limited scalability under very high loads
- Hardware compatibility
- Learning curve
- Incomplete documentation in advanced cases
- CPSTIC certification is not generic, only for specific versions
- Potential lack of support or continuity due to not having a manufacturer to back it up
InprOTech GUARDIAN
InprOTech GUARDIAN is a cybersecurity technology designed specifically to protect industrial networks and production environments. Its value lies in continuous traffic monitoring, combining different technologies (static rules, IDS, AI algorithms, and honeypots), which allows it to learn from network traffic, detect anomalies and potential threats in real time, identify vulnerabilities, and inventory network assets.
Beyond detection, GUARDIAN incorporates active blocking capabilities, allowing it to integrate with firewalls, such as OPNsense and solutions from other manufacturers, to respond to the detection of connections to malicious external IPs (whether they are the source or destination of communications). This integration can operate in different modes: from simple notification to manual or fully automatic blocking of suspicious addresses.
Resources
[1] https://docs.opnsense.org/index.html
[2] https://www.pfsense.org/
[3] https://m0n0.ch/wall/index.php
[5] https://ccnadesdecero.es/opnsense-vs-pfsense/
[6] https://www.rootsolutions.com.ar/opnsense-firewall-utm-opensource-cuenta/
[7] https://backsec.net/opnsense-que-es/
[8] https://inprotech.es/guardian/
[9] https://cpstic.ccn.cni.es/es/catalogo-productos-servicios-stic/377-opnsense-business-edition25-4
[10] https://ens.ccn.cni.es/es/
La entrada Protect and optimize your network with OPNsense se publicó primero en InprOTech.
]]>La entrada Client Opinions on InprOTech in 2025 se publicó primero en InprOTech.
]]>This exercise not only allows us to measure results, but also to identify how the sector is evolving, which challenges are emerging in factories, plants, and critical environments, and how we can better support each organization.
A level of satisfaction that drives us forward
Industrial digital transformation is advancing rapidly, and with it, expectations regarding security. In this context, our clients rated their overall satisfaction with InprOTech on a scale of 1 to 10.

The score obtained was 9.33 out of 10, a figure that shows that our specialization in OT environments continues to be a significant differentiator.
Alongside this global assessment, we also requested a more detailed evaluation of different aspects of the service:
- Responsiveness to incidents.
- Compliance with deadlines and commitments.
- Professionalism and technical expertise of the team.
- Flexibility and adaptation to changing needs.
- Quality and usefulness of the proposed solutions.
The average specific satisfaction obtained this year reached 4.46 out of 5, reflecting that our practical and operations-oriented approach aligns with the real needs of the sector.
Recommendation and trust: InprOTech’s NPS
In such a sensitive environment as the industrial one, trust is essential. For this reason, we measure our clients’ willingness to recommend us through the Net Promoter Score (NPS) indicator.

In 2025, InprOTech reached an NPS of 83, a value that highlights the strength of the relationships we build and the perception that our work provides security and peace of mind in critical operations. This figure encourages us to continue strengthening our role as a strategic partner for plants and OT environments.
InprOTech, a trusted partner in industrial cybersecurity
The results obtained this year motivate us to continue evolving alongside our clients, reinforcing our knowledge of emerging industrial technologies and expanding our capabilities to anticipate the risks that may impact the sector.
We will continue working hand in hand with each organization to ensure that their processes remain secure, resilient, and prepared for the challenges ahead.
Finally, we sincerely thank everyone who participated in this edition for sharing their feedback. Your comments are essential to continue growing and adding value in the field of industrial cybersecurity!
La entrada Client Opinions on InprOTech in 2025 se publicó primero en InprOTech.
]]>La entrada Success Story: Inventory and Continuous Monitoring at Adhex Tech Tapes se publicó primero en InprOTech.
]]>Adhex Tech Tapes is a subsidiary of Adhex Technologies created in July 2001 and specialized in the development of activities linked to the manufacturing of adhesive solutions and protection solutions (sealing, acoustic, thermal, and surface) for the automotive sector (OEMs and Tier1).

Currently, it holds the quality certification IATF16949, in addition to ISO 14001, ISO 45001, and CCAP (Certification for China). The production plant in Porriño (Spain) is recognized as a Q1 supplier for Ford and A level for the VW Group, and carries out sustainable and environmentally respectful activities.
THE CHALLENGE
Adhex identified a critical need: the lack of visibility regarding the devices connected to its industrial network, especially in relation to wireless networks such as Bluetooth and WiFi. This deficiency pointed to the absence of a complete and updated asset inventory, which generated uncertainty and concern within the technical team.
The main consequence of this scenario was a greater exposure to cybersecurity threats. The presence of obsolete devices, unknown devices or unmonitored devices could represent hidden risks, critical vulnerabilities and difficulties when implementing effective preventive measures. Additionally, Adhex needed to improve OT network supervision as part of its industrial security reinforcement strategy.
INPROTECH SOLUTION
To respond to these needs, InprOTech deployed our solution InprOTech Guardian, an advanced platform for automatic asset inventory, vulnerability detection and the generation of real-time security alerts. This solution offers full visibility of devices connected to industrial networks, including those present in wireless environments.
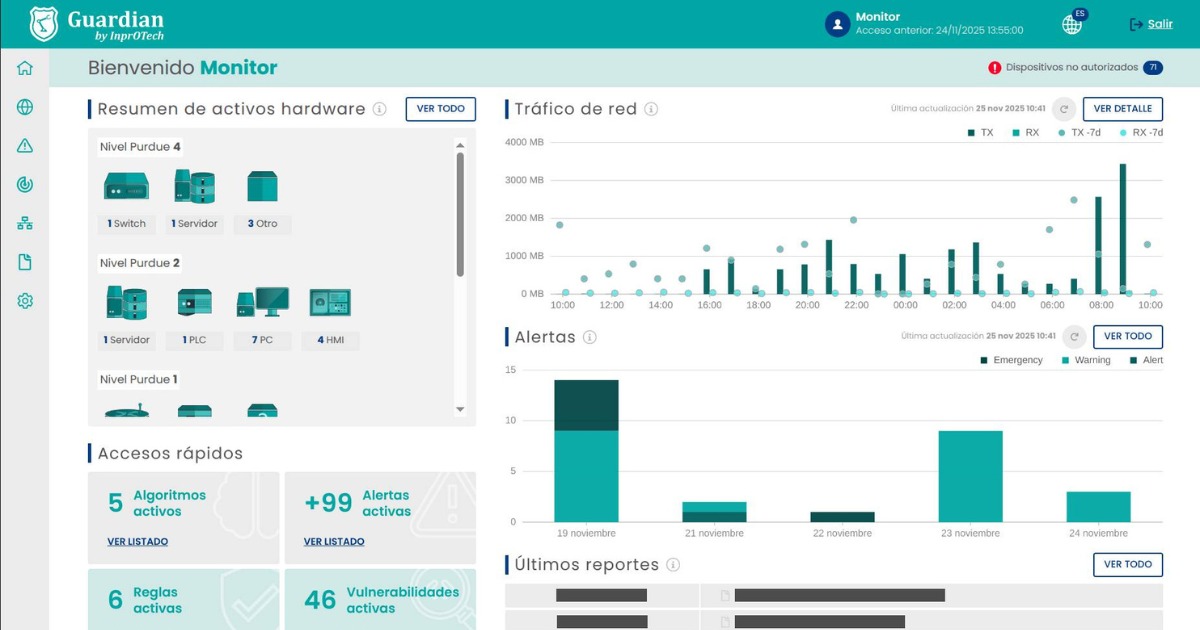
Additionally, a monitor was integrated with Guardian, allowing Adhex’s technical team to consult in a simple and centralized way the status of its industrial network at any time from its IT room.
Before our intervention, the client did not have an automated or updated system for asset management or for constant monitoring of its OT network. This made proactive threat detection difficult and increased the dependence on manual reviews, which were inefficient in production environments and completely ineffective for early cyberattack detection.
The solution implemented by InprOTech corrected these deficiencies by enabling dynamic visualization of the network map, automatic detection of unknown devices, and proactive identification of vulnerabilities. During the deployment phase, unmonitored connected devices and exposed assets that were not properly fortified were even detected, issues that the client had not previously identified and which could be resolved quickly.
RESULTS
The implementation of InprOTech Guardian at Adhex made it possible to achieve the following benefits:
- Complete visibility and updated OT environment, including wireless networks.
- Automatic inventory of connected assets, reducing previous uncertainty.
- Detection and correction of critical vulnerabilities, increasing plant security.
- Interactive network panel and visual map that facilitates control and supervision of the environment.
- Improved decision-making and industrial security management.
- Reduced risk of intrusion or malfunction due to uncontrolled devices.
- Early anomaly detection, allowing faster action in the event of any cybersecurity incident.
ADHEX TESTIMONIAL

“Thanks to this tool, we have been able to identify previously unknown vulnerabilities in the OT infrastructure, which has enabled early intervention and action. One of the most remarkable achievements has been the detection of devices connected to the network that were not being monitored and exposed devices that were not properly fortified.
Through the OT network analysis provided by GUARDIAN, we have been able to obtain full visibility of the connected OT devices, improve its segmentation and reinforce preventive measures, enabling more effective security management.”
La entrada Success Story: Inventory and Continuous Monitoring at Adhex Tech Tapes se publicó primero en InprOTech.
]]>La entrada Forensic Analysis in OT Environments se publicó primero en InprOTech.
]]>Unlike traditional IT forensics, this field presents unique challenges that require specific methodologies, specialized tools, and a careful approach to avoid impacting production or physical safety.
In this article, we will explore what forensic analysis in OT environments is, its importance and challenges, and how InprOTech GUARDIAN can become a key ally to carry it out effectively and strengthen industrial cybersecurity.
What is it and what does it involve?
Forensic analysis is a methodical process aimed at investigating cybersecurity incidents to discover what happened, how it occurred, when, who was involved, and what impact it had.
It involves the collection, preservation, and analysis of digital evidence from industrial equipment and networks. The goal is to reconstruct the sequence of events of an incident, identify exploited vulnerabilities, and determine the origin of the attack — all without interrupting system operations.
Forensic analysis in industrial environments pursues several key objectives:
- Determine the origin and scope of the incident
- Identify weaknesses and propose security improvements
- Gather valid evidence that can be used in legal or regulatory processes
- Strengthen cyber resilience by learning from each incident to improve future responses.
Why is it necessary?
Industrial systems form the backbone of critical sectors such as energy, water, transportation, and manufacturing. A failure in these environments can have serious consequences: from production interruptions to economic impacts, environmental damage, or even risks to physical safety.
For this reason, having forensic processes is not just a best practice but a strategic necessity that enables:
Effective problem resolution
When an incident occurs, discovering the exact cause is essential. Forensic analysis makes it possible to identify whether it was a technical error, human failure, or cyberattack. This enables precise and rapid solutions, reducing downtime and operational impact.
Learning from mistakes
Each incident is an opportunity to improve. Forensic analysis helps document what happened and understand the root cause, generating knowledge that can be used to strengthen procedures, adjust configurations, and prevent similar future incidents.
Strengthening security and training
The forensic process not only protects systems but also contributes to training human teams.
By sharing findings and lessons learned, cybersecurity culture increases, making operators and technicians more aware of risks and more effective in detecting and responding to incidents.
Ensuring continuity and trust
In sectors where availability is critical, trust in operations is essential. A well-executed forensic analysis provides solid evidence that supports strategic decisions and demonstrates to clients, partners, and authorities that security is being managed responsibly and professionally.
Challenges and important considerations
OT systems are often designed to ensure operational continuity, not necessarily security, leading to unique challenges that must be considered during the investigation:
Poorly documented architectures
Many industrial environments use legacy or customized infrastructures, with devices that may have been in operation for more than 20 years.
These architectures often lack up-to-date documentation, making it difficult to understand system interconnections and locate evidence.
This requires forensic teams to conduct prior investigation, interview plant personnel, and have deep knowledge of industrial processes.
Complexity in data collection
Industrial devices such as PLCs, RTUs, or HMIs do not always log events in detail or use proprietary formats that are difficult to interpret. Additionally, stopping equipment to extract evidence is often not possible, as it could interrupt production or pose physical safety risks.
This requires non-invasive collection methods, such as passive network traffic captures or parallel analysis using system replicas.
Chain of custody
In an industrial environment, collected evidence may have legal value.
Therefore, it is essential to follow a strict chain of custody, documenting who accessed the evidence, how it was transported, and how it was stored.
This ensures that information remains intact and can be presented to authorities or auditors.
Vendor involvement
In many cases, industrial systems and equipment are managed by external vendors who possess critical information, such as configurations, firmware, or proprietary keys.
This means the forensic process may require coordination and confidentiality agreements, potentially delaying the investigation if a clear prior relationship does not exist.
Order of volatility
During evidence collection, it is important to follow the order of volatility, meaning prioritizing the capture of data that disappears the fastest (e.g., RAM memory).
If this order is not respected, key information needed to reconstruct the incident may be lost.
Order of evidence
In addition to volatility, a logical extraction and analysis sequence must be established to minimize system impact and facilitate later interpretation.
This involves planning which equipment will be examined first, how evidence will be named and stored, and which tools will be used in each phase to maintain consistency and traceability.
Phases of a forensic analysis
A forensic analysis is planned in phases, and each one must respect the chain of custody and order of volatility.
Asset identification
It is necessary to know what exists, where it is, and its level of criticality.
- Determine inventory by levels.
- Gather topology, versions, configurations, vendor contacts, etc.
- Define safe observation points such as port mirroring, TAPs, etc.
The objective of this phase is to thoroughly understand network assets and their context.
Anomaly detection
It is essential to identify signs of compromise without interrupting production.
- Detect alerts, unusual failures, shutdowns, unauthorized changes.
- Review logs and configurations of key devices.
- Perform network analysis with passive captures to detect anomalous behaviors, new connections, scans, port changes, etc.
- Verify time synchronization (NTP/PTP) to ensure proper event correlation.
The goal is to inventory suspicious events, prioritize them, and establish a timeline of occurrences.
Threat analysis
During this stage, detailed analysis of collected evidence is performed, correlating the attacker’s techniques, tactics, and procedures (TTPs). The main goal is to confirm hypotheses, validate identified risk scenarios, and detect exploited vulnerabilities.
Additionally, lessons learned are extracted and integrated into internal organizational processes, both technically and in personnel training programs. This strengthens the defensive posture and prevents similar future incidents.
Report generation
It is important to rigorously document the entire process. The recommended structure is:
- Executive summary: clearly and briefly explain what happened, what impact it had, and what decisions were made.
- Timeline and scope: establish a chronology showing how the incident unfolded and which systems were affected.
- Evidence and Indicators (IoCs): detail what evidence was collected, how, and where. Include integrity checks and chain of custody to ensure legal validity. Enumerate indicators of compromise found, such as suspicious files or IP addresses.
- Technical analysis: describe the TTPs used by the attacker, explaining how the attack occurred and progressed.
- Recommendations: provide concrete actions for containment, eradication, recovery, and prevention.
- Annexes: provide supporting materials useful for other analysts, such as captures, hashes, scripts, configurations, etc.
- Remediation and prevention: the objective of this final phase is to recover safely and reduce future probability/impact.
-
- Safely and collaboratively contain affected devices/processes.
- Eradicate and recover with exhaustive and controlled testing to ensure proper service restoration.
- Implement preventive measures based on lessons learned.
- Train the team and update plans, playbooks, etc..
Analysis techniques
Different techniques are used to investigate incidents in industrial systems, each focused on a specific type of evidence. These tools allow valuable information to be gathered without interrupting operations, always respecting the chain of custody and order of volatility.
Network forensic analysis
Capture and analyze network traffic to identify the origin, destination, and content of communications.
Memory forensic analysis
Capture volatile memory from a device at a specific moment. Useful for discovering hidden processes, running malware, and temporary data not stored on disk.
Device forensic analysis
Review storage devices and other system components, such as logs and active processes. Ideal for detecting deleted, modified, or disguised files.
Malware analysis
Reverse engineering techniques to understand the behavior and capabilities of malicious software affecting the industrial environment.
Log analysis
Collect and correlate logs from various sources, such as PLCs, SCADA servers, or firewalls, to reconstruct events and detect suspicious activity.
InprOTech GUARDIAN
InprOTech GUARDIAN is a cybersecurity technology specifically designed to protect industrial networks and production environments. It operates by continuously monitoring and analyzing network traffic, using a combination of static rules, an IDS, artificial intelligence, and honeypots. This allows it to learn normal network behavior, detect anomalies in real time, identify device vulnerabilities, and automatically inventory network assets.
Thanks to these capabilities, Guardian not only helps prevent attacks and failures but also becomes an essential source of information during forensic analysis. By collecting and correlating industrial communication and event data, it provides a historical record that enables incident reconstruction, hypothesis validation, and better decision-making in response and OT cybersecurity improvement.
Conclusion
Forensic analysis in OT environments is essential to understand the origin and impact of incidents, enabling organizations to learn from them and reinforce industrial security. However, this process depends on the quality and availability of data collected during and before the attack.
In this context, InprOTech GUARDIAN positions itself as a strategic ally, providing continuous and precise visibility of the OT network.
Resources
[1] Forensic analysis in an industrial automation environment – Industrial Cybersecurity Center
[2] Secure access guide to field devices
[3] Forensic Analysis in Industrial Control Systems – Industrial Cybersecurity Center
[5] CyberOTworld: Forensic Analysis in OT environments after a Cyberattack (I)
[6] https://inprotech.es/importancia-de-la-formacion-y-concienciacion-en-ciberseguridad-ot/
La entrada Forensic Analysis in OT Environments se publicó primero en InprOTech.
]]>La entrada The Inprosec Group, Strategic Sponsor at the V Encontro Ciber.gal 2025 se publicó primero en InprOTech.
]]>Held in Santiago de Compostela, the event brought together professionals, institutions, and citizens to discuss, share, and promote a safer digital culture.
As a strategic sponsor, the Inprosec Group reaffirmed its commitment to cybersecurity, participating in a variety of technical, educational, and awareness-raising activities throughout the three days of the event.
Presentation of the Industrial Cybersecurity Laboratory and Demonstration Center

On Thursday, November 6, our Business Development Director, Pedro Estévez, took part in the session dedicated to the cybersecurity laboratories and demonstration centers promoted by the Xunta de Galicia, presented by AMTEGA.
During his talk, Pedro introduced the ambitious project for the Industrial Cybersecurity Laboratory and Demonstration Center, assigned to InprOTech, designed as a key element of Galicia’s emerging cybersecurity ecosystem.
This center is part of the network of laboratories that the Xunta plans to launch in early 2026, within the framework of the Galician Center of Excellence in Cybersecurity (CECIGA). Its mission is to promote advanced cybersecurity services, specialized training, product validation, and applied research.
The InprOTech Laboratory will focus specifically on industrial and OT environments, serving as a space to experiment, demonstrate, and train with real-world industrial cybersecurity solutions — from threat detection and attack simulation to the validation of countermeasures adapted to operational environments.
POSEIDON Project Demonstrator: Innovation Applied to the Integral Water Cycle

On November 5 and 6, a model of our POSEIDON project, developed together with TECDESOFT, was on display in Room 10 of the event. This demonstrator showcases and anticipates InprOTech’s practical vision for the Industrial Cybersecurity Laboratory, previewing one of the demonstration models that will be featured in the future facility.
Through POSEIDON, attendees discovered how we integrate the management of instrumented systems and processes within the Integral Water Cycle with cybersecurity event monitoring, illustrating real use cases on the protection of essential infrastructure.
Cybersecurity Begins with People: “The Human Factor as the First Line of Defense”

That same day, our Cybersecurity Manager, Antonio Cebreiro, delivered a talk titled “The Human Factor: The First Line of Defense”, highlighting the importance of awareness, continuous training, and cybersecurity culture as key elements to protect organizations against today’s threats.
The presentation emphasized that technology alone is not enough without a well-prepared and committed team, and it also served as a preview of one of the flagship services in our new Information Security portfolio at Inprosec.
Equality and Digital Safety: Building Spaces Free from Gender-Based Violence

On November 7, as the final activity of the 5th Encontro Ciber.gal, our Key Account Manager, Paula Marcelino, moderated the panel “Equality and Safety Online: Building Digital Spaces Free from Gender-Based Violence”, sponsored by Inprosec.
The discussion featured the participation of:
- Pilar Vila, Member of the Professional Association of Computer Engineering of Galicia.
- Roberto Barba, General Director of the Department for the Fight Against Gender Violence, Consellería de Política Social e Igualdad, Xunta de Galicia.
- Inés Amor, Head of the Press Office of the Galicia Regional Police Headquarters (National Police).
This initiative reflects the Inprosec Group’s commitment to equality, digital education, and social responsibility, contributing to the creation of safer and more inclusive digital environments for all citizens.
Committed to a Closer, More Collaborative, and More Human Cybersecurity
Our participation in the 5th Encontro Ciber.gal reinforces the Inprosec Group’s mission to promote cybersecurity and technological innovation in Galicia, as well as to bring cybersecurity closer to people and organizations.
The project for our Industrial Cybersecurity Laboratory and Demonstration Center represents a key milestone in this journey and will mark a before-and-after in how we understand the protection of OT and industrial environments in Galicia.
We encourage you to stay tuned to our blog and social media channels, where we will soon share more information about this laboratory.
Finally, we would like to thank AMTEGA, the Xunta de Galicia, the organizers and collaborators of the 5th Encontro Ciber.gal, and, of course, everyone who joined us during these three days for their interest, trust, and support.
See you next year!
La entrada The Inprosec Group, Strategic Sponsor at the V Encontro Ciber.gal 2025 se publicó primero en InprOTech.
]]>La entrada 19ENISE Summary se publicó primero en InprOTech.
]]>Throughout the three days, our team shared with clients, partners, attendees, and public representatives our main lines of work in Information Security.
Highlights of our participation included:
- Reconnections and new contacts throughout the event, both with familiar faces and with many interesting new people.
- Live demos and use cases focused on protecting critical processes, early threat detection, and response orchestration.
- Exchange of insights and trends on regulation, cyber resilience, and control maturity, with a particular focus on the NIS2 Directive.
This edition of ENISE leaves us with a very positive outcome: increased brand visibility and new business opportunities, exceeding last year’s results. The event itself also grew significantly, bringing together approximately 4,000 in-person attendees and 2,000 virtual participants.

In addition, on October 16th at 10:00 a.m., Pedro Estévez, Business Development Director at InprOTech, delivered a talk at the event’s Speakers’ Corner about InprOTech Guardian. He presented how the solution helps to monitor, detect, and respond to risks in OT environments. The session drew strong interest, with many attendees stopping by to learn more about the proposal and discuss real-world use cases.
Finally, from the Inprosec Group, we would like to thank INCIBE for organizing such an outstanding event, and everyone who visited our booth to learn about our solutions.
If you would like to learn more or request a meeting or assessment, please contact us. We will be delighted to help you strengthen your organization’s security!
La entrada 19ENISE Summary se publicó primero en InprOTech.
]]>La entrada MQTT in OT Environments: Efficient Communication and Emerging Threats se publicó primero en InprOTech.
]]>However, this flexibility comes at a cost: most MQTT implementations lack default security mechanisms. This can turn it into an attack vector if an adequate cybersecurity strategy is not applied.
MQTT in Industrial Environments
MQTT follows a publish/subscribe architecture, where devices (clients) publish or subscribe to messages identified by a ‘topic’. A central MQTT broker manages the distribution of these messages among connected devices.
Advantages for OT networks:
- Efficient and stateless communication
- Low bandwidth consumption
- Configurable QoS (quality of service) support
- Ideal for distributed sensors, IIoT gateways, or controllers connected to wireless or mobile networks
Typical Architecture and Use Cases
Common scenario in industrial plants:
- Sensors publish values such as plant1/temperature/zone3
- A SCADA or dashboard subscribes to those topics
- An internal broker distributes messages, even among remote nodes or in the cloud
Common uses:
- Environmental monitoring (temperature, humidity, CO₂)
- Telemetry of mobile industrial assets
- Remote control of actuators through topics such as plant1/valve1/close
Risks and Attack Vectors
Although MQTT can coexist stably in OT networks, most industrial MQTT brokers and devices are installed with minimal security configuration. This implies serious risks:
- Public topics allow attackers to spy on the entire network
- No authentication allows anonymous access or default passwords
- Unencrypted messages (without TLS) make data interception easier
- Command injection through control topics can cause unwanted actions
- Malicious persistence via retained messages or high QoS can prolong attacks
Simulation and Exploitation of MQTT
An attacker could subscribe to ‘#’, receive sensor data, and publish commands to critical topics, causing unauthorized shutdowns of equipment.
In controlled environments, it is possible to simulate real attacks against MQTT brokers with tools such as:
- MQTT Explorer
- mosquitto_sub/mosquitto_pub
- Metasploit
- Wireshark
An attacker could subscribe to ‘#’, receive sensor data, and publish commands to critical topics, causing unauthorized shutdowns of equipment.
OT Cybersecurity Best Practices with MQTT
To reduce the risks associated with MQTT in OT environments, we recommend the following measures:
- Broker isolation in a segmented network
- Strong client authentication
- Mandatory use of TLS
- Topic filtering via ACLs
- Continuous monitoring of MQTT traffic
- Deployment of MQTT honeypots for threat detection
- Event and access logging and auditing
Conclusion
MQTT is a powerful tool for improving operational efficiency, but in OT environments its implementation must be done with special caution. Its simplicity and flexibility should not overshadow the risks involved if not accompanied by an adequate security strategy. Tools like InprOTech Guardian allow monitoring and identification of anomalous behaviors in industrial networks, enabling secure integration of protocols like MQTT within resilient and controlled OT architectures.
References
- MQTT.org. MQTT Version 5.0 Specification.
- OWASP MQTT Security Assessment Cheat Sheet.
- Eclipse Mosquitto – An open source MQTT broker.
- Rapid7 – Metasploit Framework.
La entrada MQTT in OT Environments: Efficient Communication and Emerging Threats se publicó primero en InprOTech.
]]>