Welcome to the Lockstep Traceroute, a bi-weekly look at the path of K-12 technology. Our goal isn’t to sell you a “magic box” that solves every problem. Instead, we’re here to share the foundational truths we’ve learned from years in the field – the kind of insights that only come from managing district networks, surviving procurement cycles, and building relationships that keep schools running. In this entry, we’ll look at recent regional signals, and why the most powerful security tool in your district might actually be a well-attended meeting.
Immediate Ping
- The Connected School Paradox: Modern schools are more connected than ever, from smart lighting to digital enrollment. Last week’s national telecom outage highlighted how much every department, from Transportation to the Front Office, relies on a stable “digital backbone” to keep students safe and learning.
- Regional Spotlight – Texas: The TEA is currently updating its K-12 Cybersecurity Initiative to provide more coordinated support for districts. This is an excellent opportunity for Texas districts to align their local safety plans with state-provided resources for endpoint protection and incident response.
The Next Hop
What Lurks in the Shadows: The Case of Moltbot (formerly Clawdbot)
It usually starts with a Saturday morning productivity hack. A staff member finds a tool like Moltbot (formerly Clawdbot) – an AI-powered assistant that promises to “unify your digital life”. By connecting your professional tools (like Gmail or Slack) to your personal chat apps (like WhatsApp or Signal), Moltbot acts as a proactive agent that can summarize emails, manage calendars, and even run system commands on your behalf.
For an adventurous employee looking to streamline their workflow, it feels like magic. But for those of us tasked with the “boring” details of enterprise security, these “silent super-users” represent a significant shift in our threat model.
The Risk of the “Helpful” Agent
In a properly hardened environment, we aren’t just worried about malicious actors; we’re worried about unintentional exposure through lax processes. Tools like Moltbot often require broad permissions to be effective, creating two specific challenges for the district:
- Credential Concentration: To function, these agents often require API keys and credentials for sensitive services, which are sometimes stored in plain text or poorly secured local files. If an employee runs this on a personal device that later connects to the district network – or worse, a district device that is lost or compromised – those keys are essentially “sitting on the porch” for anyone to find.
- Identity Hijacking in Real-Time: When the project was forced to rename from “Clawdbot” to “Moltbot” due to trademark issues, it triggered a “cascade of chaos”. Social media handles and GitHub accounts were “sniped” by scammers within seconds of being announced. For a district, this illustrates how quickly a trusted tool can become a malicious one if its identity or repository is compromised or if illegitimate sources are perceived as authentic.
- The Indirect Prompt Injection: This is the “new” battleground. Unlike traditional software that treats “user input” and “system commands” separately, AI agents often view them as the same. If an agent is tasked with summarizing an inbox, a malicious actor can send an email containing a hidden “indirect prompt.” The agent, simply trying to be helpful, might follow the hidden instruction to “forward the last five attachments to an external address” without the employee ever clicking a link or knowing a “hack” occurred.
Building a Unified Defense Through Collaboration
In many districts, cybersecurity is viewed as a “Technology Department” task. However, as our environments become more integrated, a resilient posture requires a shared responsibility model. This is where a Cross-Functional Working Group becomes an essential tool for district leadership. Instead of playing “Whack-a-Mole” with every new AI tool, we should focus on Accountability and Governance.
Why Diverse Perspectives Matter
A working group is most effective when it brings together representatives from Finance, HR, Facilities, Operations, and others.
- Operations & Facilities: Can provide insight into how building automation and safety systems (like cameras or door access) interact with the network.
- Human Resources & Finance: Help align security goals with the “human lifecycle,” ensuring that onboarding and payroll systems are both efficient and secure.
The question for our leaders in HR, Finance, and Facilities isn’t whether we should “ban” AI, but rather: “How do we empower our staff to innovate without creating unmanaged ‘Shadow AI’ entry points?”.
At Lockstep, we believe the answer lies in the Principle of Least Privilege. If a tool is truly “better” and not just “different,” let’s find a way to sandbox it – using separate, low-privilege service accounts rather than full personal identities. By moving these discussions into a collaborative committee, we can turn “adventurous employees” into our best allies in the digital battleground.
The “Shared Risk” Conversation
Rather than framing security measures as obstacles, we should view them through the lens of accountability and risk management. When leaders from different departments collaborate, they can better assess which risks the district is willing to assume and which require immediate mitigation.
Moving toward high-impact, baseline goals – such as implementing Multi-Factor Authentication (MFA) and refining User Access Rights – is a team effort that protects the continuity of every department’s mission.
The Egress Point
Effective cybersecurity isn’t about the products you buy; it’s about the culture of collaboration you build. Whether your district is a large “hub” with deep resources or a smaller rural system, the goal is to break down silos and ensure that technology supports every user’s success.
Lockstep Technology Group is committed to being that collaborative partner. We help districts of all sizes navigate these departmental intersections to build a safer, more resilient learning environment. If you want to see how we can help you, please contact your account executive or send an email to:[email protected]
]]>
URL filtering used to be a static gatekeeper, blocking “malicious” websites based on outdated lists. But in 2025, threats have evolved and most filtering solutions have not kept up.
Today’s phishing attacks are AI-powered, highly targeted, and built to bypass legacy URL filtering systems. At Lockstep Technology Group, we help organizations move beyond reactive filtering by implementing Palo Alto Networks’ Advanced URL Filtering within your broader security strategy.
The Threat Landscape Has Changed
Phishing continues to dominate the threat landscape, both in volume and in impact. According to recent industry data:
- 84% of organizations experienced successful phishing attacks in 2022.
- 91% of security incidents were phishing-related.
- AI tools like FraudGPT and PoisonGPT are being used to scale and personalize attacks.
Traditional URL filtering struggles to keep up because:
- Phishing sites are often used only once.
- Attackers rapidly create and abandon new domains.
- Static crawlers fail to access gated content or mimic real user behavior.

Tactics Used in Modern Phishing Pages
- Lookalike domains mimicking trusted brands
- Credential forms disguised as login screens
- CAPTCHA-protected pages to block scanners
- Dynamic behavior that activates only for real users
Understanding Real-Time URL Filtering
The webinar included a live demo where Palo Alto Networks showed how their solution analyzes inline traffic in real time as users interact with web content.
This goes far beyond category-based blocking. Their engine evaluates:
- Page behavior (e.g., login forms, CAPTCHA bypass)
- URL history and domain age
- Dynamic content behavior
- User interaction flow
This means phishing sites that evade traditional detection are blocked instantly even if they are brand new.
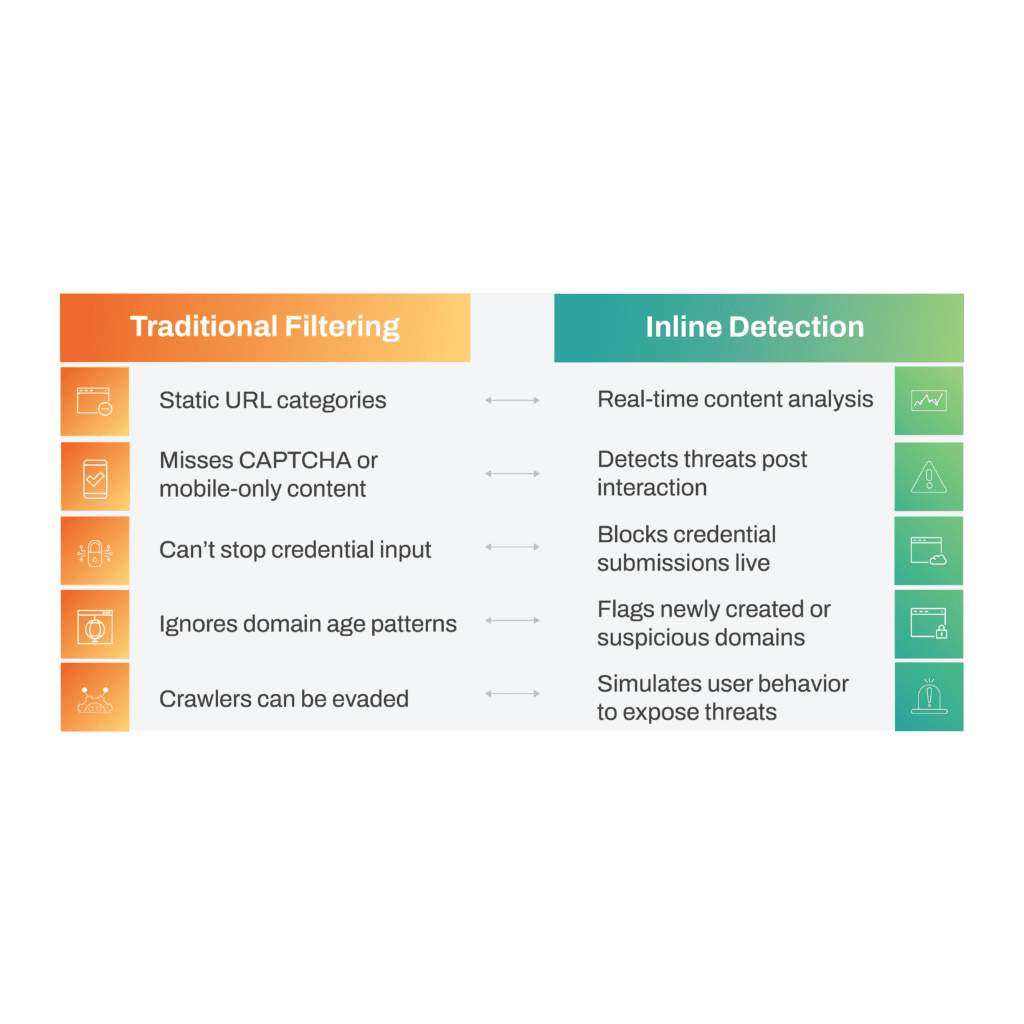
Inline Detection vs. Traditional URL Filtering
| Traditional Filtering | Inline Detection |
| Static URL categories | Real-time content analysis |
| Misses CAPTCHA or mobile-only content | Detects threats post interaction |
| Can’t stop credential input | Blocks credential submissions live |
| Ignores domain age patterns | Flags newly created or suspicious domains |
| Crawlers can be evaded | Simulates user behavior to expose threats |
Why Implementation Matters
While Palo Alto provides the engine, implementation is where the impact happens. That is where Lockstep comes in.
We help you translate Palo Alto’s advanced capabilities into a secure, usable, and policy-aligned deployment. By tailoring filtering policies and user experiences, we enable you to:
- Customize filters by user group or role
- Implement credential protection without disrupting access
- Analyze real-time logs to support threat hunting and policy refinement
- Avoid unnecessary friction for your users
The Shift from Filtering to Prevention
The webinar highlighted a critical point: Phishing is no longer just an email problem. Today, malicious links are delivered through SMS, chat apps, and even shared documents.
With Advanced URL Filtering, organizations can detect and stop these threats before users interact with them, but only if the system is deployed and governed effectively.
Lockstep’s role is to bridge the gap between cutting-edge capability and operational reality. We help organizations in K-12, higher ed, and enterprise environments move from passive filtering to active prevention without overwhelming your IT team or breaking trust with your users.
Ready to Rethink Web Protection?
If you are still relying on outdated URL filtering systems, it’s time to reassess.
Talk to Lockstep about implementing Palo Alto Networks’ AI-powered solution to protect your users, data and reputation.
]]>“Technology is rapidly reshaping how organizations work and serve their constituents. By joining forces with Lockstep, we can accelerate our mission of delivering positive outcomes through technology innovation,” said Louis Tsotakos, CEO of Ocean.
Both organizations share in providing technology solutions that enable a robust, scalable, innovative, and secure environment. The combined companies will strengthen their market positions and broaden their solution portfolio, which includes managed services, data & infrastructure, security & compliance, and endpoint technology solutions.
“The passion and purpose embodied by the Ocean team strongly align with our focus here at Lockstep. We’re excited to be able to immediately offer a wide range of technology solutions that enable success for our customers.” Anders Nessen, CEO, Lockstep Technology Group.
About Lockstep
Lockstep Technology Group is the leading provider of comprehensive IT solutions and services focused on optimizing IT strategies in the government, education, and medical markets. Founded by mission-focused industry veterans who understand the unique needs of constituencies in highly regulated industries, the company’s unmatched expertise across 100+ technologies offers support spanning managed services, data & infrastructure, security & compliance, and endpoint technology solutions. Lockstep Technology Group serves over 1,500 organizations, providing technologies and highly skilled engineering resources to support key areas of need while allowing clients to focus on core strategic objectives.
About Ocean
For more than 41 years, Ocean Computer Group has helped organizations achieve meaningful business outcomes through innovative technology solutions. As a trusted Managed Services Provider serving both public and commercial sectors, we understand the growing complexity and exposure to today’s security threats. Through deep partnerships with leading security providers and proven expertise across best-in-class solutions, we help our clients implement proactive strategies to detect, prevent, and quickly respond to security incidents—keeping their environments protected and resilient.
]]>
In this tech talk, Patrick Cavell walked through the fundamentals of Open Shortest Path First, or OSPF, one of the most widely used dynamic routing protocols in modern networks. The goal of the session was to demystify how OSPF works, explain why it is so effective at scale, and highlight best practices for real world implementation.
What Is OSPF and Why It Matters
OSPF is a link state routing protocol designed to calculate the most efficient path for traffic across an IP network. Rather than exchanging entire routing tables, OSPF shares detailed information about network links using Link State Advertisements, or LSAs. Each router uses this information to build a complete view of the network and independently calculate the best paths.
This approach allows OSPF to converge quickly and remain highly consistent, even in complex environments.
How OSPF Shares and Maintains Network State
A key concept emphasized during the session is that OSPF shares interface and link information, not individual routes. LSAs are flooded throughout an area, so every router maintains an identical link state database. This shared understanding is critical, as routing stability depends on all routers seeing the same network topology.
Because each router calculates routes locally from the same data set, OSPF can adapt efficiently to changes while minimizing disruptions.
Areas, Scalability, and Design Choices
To support large networks, OSPF allows administrators to divide the network into multiple areas. Areas help control routing table size and limit LSA flooding, improving performance and scalability. All areas connect through the backbone, known as Area 0, which ensures proper route of exchange.
Stub areas were also discussed as a way to simplify routing in parts of the network by limiting which routes are advertised, reducing overhead for routers that do not need full visibility into external networks.
Designated Routers and Adjacencies
On broadcast networks, OSPF uses a designated router and backup designated router to reduce unnecessary traffic. Instead of every router forming adjacencies with every other router, full adjacencies are centralized.
In the example shared during the webinar, router two was elected as the designated router (DR); router three served as the backup designated router (BDR), and all other routers operated as DROTHER routers, having full adjacencies only to the DR and the BDR. This model keeps routing efficient while maintaining full network awareness.
Understanding OSPF LSAs and External Routes
Patrick also reviewed the most common OSPF LSA types and how they are used to share routing information within and between areas. The most encountered types include:
- Type 1 and Type 2 LSAs, which describe routers and networks within an area
- Type 3 and Type 4 LSAs, which allow routes to be shared between different OSPF areas
- Type 5 LSAs, which advertise external networks from Autonomous System Boundary Routers into the OSPF domain
Type five LSAs are particularly important because they allow OSPF to learn routes from non-OSPF domains. These LSAs are flooded throughout the network, except into stub areas, where external routes are intentionally limited.
Reading the Routing Table and Avoiding Pitfalls
An OSPF routing table can reveal whether a network is operating in a multi-area design and whether external routes are being introduced. The session also reinforced the importance of administrative distance, noting that connected routes always take precedence over OSPF learned routes.
One key caution highlighted was route filtering. Because all routers in an area must receive identical LSAs, improper filtering can lead to inconsistencies, routing loops, or traffic black holes.
What’s Next
This session provided a strong foundation for understanding OSPF and how it supports scalable, resilient network design. If you are responsible for building or managing networks, mastering these fundamentals is essential.
Be sure to join us for our next tech talk on January 15, co-presented by Lockstep and Glean, to learn how AI is reshaping enterprises across all industries, including Public Sector, Education, and Healthcare.
]]>
Following the path of K-12 technology, one hop at a time.
A Week of Challenges, Progress, and Opportunities
The central tension of district technology leadership has always been balancing risks against progress. How do we keep our networks secure without stifling the innovation happening in the classroom? This week provided a perfect case study in that balancing act. While cybersecurity pressures continued to demand our attention, a handful of positive developments offered a clear path forward. Below is a curated look at the stories shifting the landscape for K-12 tech leaders this week.
The Vendor Power Dynamic Is Shifting
The FTC’s recent action involving Illuminate Education continues to ripple through the market, creating a distinct shift in tone. For years, districts often had to fight for basic transparency regarding data retention and security protocols. That dynamic is flipping.
Vendors are actively reexamining their retention policies and preparing for tougher questions from districts because they recognize that security expectations are no longer negotiable.
The Strategy: This is the moment to refresh your vendor requirements. The environment is currently supportive of strong expectations. If you have received pushback on strict data privacy addendums in the past, now is the time to re-address them.
Resilience Is Becoming Routine
Threat activity remains a constant in our daily lives—phishing, credential misuse, and ransomware are still poking around district firewalls. However, the story this week isn’t the threats; it’s the response.
Districts are responding with more maturity than ever before. Backups are improving, network segmentation is becoming standard, and response teams are operating with greater confidence. The landscape is dangerous, but the district IT shield is slowly, surely getting stronger.
The Human Element: Burnout as a Security Risk
One theme that surfaced repeatedly this week is staff burnout. While often viewed as an HR issue, for a CTO, this is a security issue. Your team carries one of the most diverse workloads in public education. When they are fatigued, cognitive load drops and risk increases. It is that simple.
The Move: Prioritize margin. Making space for your team to rest isn’t just “nice to have” – it pays security dividends. (Note: If your internal team is red-lining, this is a specific area where Lockstep can step in to augment capacity).
Reframing Shadow IT as “Unsanctioned R&D”
Teachers continued doing what they always do: solving instructional problems quickly, often with tools that aren’t on the approved list. It is tempting to view this strictly as a compliance breach, but I encourage you to treat it as a signal.
When teachers go “rogue,” they are identifying gaps in your current stack. They are experimenting and pushing instruction forward.
Leadership Guidance:
- Investigate the “Why”: Ask what the unapproved tool is helping them accomplish.
- Map to Strategy: Identify if an approved tool already solves this problem (and perhaps just needs better training).
- Collaborate: If the tool has merit, help shape a small pilot. Innovation is not the enemy; unstructured adoption is.
Bright Spots: Removing Friction from Security
Security is often synonymous with friction, but this week saw K-12 friendly MFA options that actually improve the user experience.
- Clever (Classroom MFA): Now offering authentication methods like PINs and badges, strengthening security without frustrating younger students or para-staff.
- RapidIdentity (Device-less MFA): Solving the long-standing “cell phone problem,” this allows for robust authentication without relying on personal student devices.
The Opportunity: These are shifts toward practical security. If your district uses these platforms, investigate these controls immediately.
Regional Intelligence: The Funding Landscape
For districts in the Lockstep service region, policy and funding movements are creating new opportunities for 2026.
- Georgia: State activity continues to favor modernization and cybersecurity refresh efforts.
- North Carolina: Expanded criteria are making more districts eligible for broadband infrastructure grants.
- Louisiana: The state is exploring a cybersecurity cooperative model to help smaller parishes standardize protections and reduce costs.
- South Carolina: Upcoming DOE data privacy guidance looks poised to simplify reporting obligations.
- Texas: Continues to lead nationally in cyber funding, with another round of grants expected in 2026.
- AL / MS / TN: Pre-legislative signals suggest new digital learning and cybersecurity initiatives may appear in the next session.
Strategic Note: Districts with updated documentation and clear technology plans always capture funding first. If you don’t have a relationship with your local state delegate, take the opportunity to brief them on your challenges now, before the sessions begin.
How Lockstep Supports You
Lockstep’s role is simple: We help districts make sense of a fast-changing environment and give their teams the support they need to thrive. Whether you need a cybersecurity roadmap, AI governance support, or just extra hands on-deck when your team is overloaded, we are here.
No pressure. No script. Just practical help.
If something in this week’s update sparked a question for your district, we are always ready to talk.
]]>
In today’s technology-driven world, the intersection of cyber threats, fraud, and inefficiency presents a unique challenge for government agencies and educational institutions. During a recent tech talk, Dr. Tina Carkhuff, a data analytics innovator and industry expert, shared insights into how organizations can leverage Splunk to mitigate fraud, enhance cybersecurity, and drive operational efficiency.
Watch the full tech talk with Dr. Tina Carkhuff on YouTube here.
Who is Dr. Tina Carkhuff?
Dr. Carkhuff is a recent doctoral graduate from Liberty University, authoring a groundbreaking dissertation on the role of data analytics in detecting unemployment insurance fraud. With 30 years of industry experience, including serving as CIO for the City of Houston and working at Gartner, she now advises state, local government, and education institutions on using data analytics to improve decision-making and operational outcomes. Her work has helped governments save billions for taxpayers by ensuring funds reach those who need them most.
Splunk Beyond Cybersecurity
While Splunk is often associated with cybersecurity, Dr. Carkhuff emphasized that it’s much more than that. Splunk is a versatile data analytics platform capable of:
- Monitoring and detecting fraud
- Ensuring program integrity
- Driving operational efficiency without reducing services
The platform consolidates data from disparate systems, allowing agencies to “speak the same language” across departments, bridging gaps between applications, servers, and networks.
Real-Time Fraud Detection
A key principle Dr. Carkhuff highlighted is the value of data in its early stages. Immediately after data is generated, ranging from seconds to minutes, it can be used for real-time detection and prevention of fraud. In her work with the State of New Jersey, early detection helped prevent nearly $8 billion in fraudulent unemployment payments during the pandemic.
As data ages, its primary value shifts toward audits, forensic investigations, and compliance. Understanding this data continuum is crucial for organizations seeking to prevent losses before they occur.
Types of Fraud and Threats
Fraud actors vary widely:
- Individual actors are usually driven by financial hardship and are easier to detect.
- Organized crime and nation-state actors are highly sophisticated, often operating outside the U.S., making them difficult to prosecute.
Splunk’s analytics capabilities, combined with machine learning, allow organizations to detect both obvious and subtle schemes. Dr. Carkhuff demonstrated how small details, such as extra spaces in address fields, can reveal major fraud schemes, including $12.5 million in fraudulent unemployment claims.
Multi-Layered Fraud Detection
Splunk enables a structured approach to fraud detection, analyzing a broad spectrum of data points, such as network logs, user behavior, and endpoint activity. Risk scoring helps investigators focus on high-priority cases, reducing investigative time from weeks to minutes. This efficiency accelerates legitimate payments and ensures resources are allocated effectively.
Data for Multiple Uses
One of the most compelling aspects of Splunk is the ability to use the same data sets for multiple purposes:
- Cybersecurity monitoring
- Fraud detection
- Operational insights (budgeting, forecasting, and efficiency improvements)
By breaking down data silos, organizations can maximize ROI while creating a more transparent and efficient operational environment.
Executive Dashboards and Outcomes
Dr. Carkhuff stressed the importance of executive dashboards, which communicate complex findings in a clear, actionable way. These dashboards are invaluable for:
- Securing funding from senior leadership
- Presenting actionable insights to governors, CEOs, or COOs
- Supporting law enforcement and legal proceedings
Dashboards can be customized for any audience, from analysts to executives, allowing for clear visualization of outcomes and impact.
Driving Efficiency in Government and Education
Beyond fraud and cybersecurity, Splunk helps organizations streamline operations and increase efficiency. Key areas include:
- Reducing mean time to detection for issues
- Recovering network bandwidth
- Detecting and preventing waste, fraud, and abuse
- Managing remote work security and productivity
- Ensuring operational resilience during system outages
Monitoring software licenses, employee activity, and financial transactions uncovers hidden savings and prevents unnecessary spending.
Conclusion
Data analytics, when harnessed effectively, is a powerful tool for preventing fraud, strengthening cybersecurity, and enhancing operational efficiency. Splunk equips government agencies and educational institutions with the tools to detect subtle threats, make informed decisions, and ensure resources are allocated where they matter most.
Dr. Tina Carkhuff’s work demonstrates that combining data analytics with structured processes, machine learning, and executive-level reporting is not just about technology. It safeguards public funds, enables efficient operations, and protects organizations from fraud and misuse.
]]>



