The post Nearly 1000 Plugins Closed During WordPress Security Cleanup appeared first on Patchstack.
]]>Patchstack is always looking for new ways to make the WordPress ecosystem safer by organizing various events for ethical hackers and security researchers. Our experiments sometimes lead to unexpected results. Also, these events sometimes uncover issues that were overlooked before.
Our latest experiment took place in October. We announced a special event for our Bug Bounty program in October as part of Cyber Security Month, and we decided to make it count by cleaning the WordPress repository of old vulnerable plugins. And what better way to do this than by running a special event with many ethical hackers?
TL;DR
- 1571 valid security vulnerability reports received in October alone. More than $17K in rewards were paid to ethical hackers who contributed to making the WordPress ecosystem safer for everyone!
- Many plugin devs are impossible to reach, resulting in over 1000 plugins/themes to be temporarily closed in October. Plugins really need to set up proper VDPs - it's easy!
- The security community behind WordPress is stronger than ever. Patchstack Alliance is open to everyone. Don't miss out on our future events - so join us now!
So let's get to the details!
The usual Bug Bounty rules were adjusted to put all possible plugins and themes into the scope:
- Reports for plugins/themes with less than 1K active installs will get the same points as components with 1K active installs.
- There's no limit of 3 years since the last update for the October competition.
- Both exceptions to the rules are applied only for reports with these prerequisites. The vulnerability CVSS score must be at least 6.5 if you want rules "1" and "2" to be applied.
The event took off rapidly. It went so well that in the middle of the month, we added one extra challenge: “If you discover 1000 (or more) valid reports this month, we will give an extra +$100 bounty to everyone who has reported at least ten reports with CVSS higher than 6.5.”
And they did it. We had big expectations, but not as big as the actual result. The number of valid vulnerability reports shocked us—1571 valid reports (affecting 7141940 active installs) in total by 37 researchers. That’s huge on its own, but when we look at our previous record, 620 (January 2024), we can see even better how huge it was. It was pretty cool to see what the growing Patchstack Alliance community of ethical hackers and security researchers can achieve in one month.
As expected, most reports were for the vulnerabilities found in the plugins.
| Vulnerable component type | Count | % |
|---|---|---|
| Plugins | 1536 | 97.77 |
| Themes | 35 | 2.23 |
Looking at the overall report count numbers does not give a clear vision of what was discovered, so we started to dig deeper into the statistics, where the scary details began to appear.
Results in numbers
One industry standard for measuring the severity of vulnerabilities is a CVSS (Common Vulnerability Scoring System) score, which includes several essential parameters to give an idea of how dangerous a vulnerability is. CVSS results for vulnerabilities discovered in this event were the main trigger for looking at results from a slightly different angle.
| CVSS score | Count | % |
|---|---|---|
| 7.1 | 755 | 48.06 |
| 6.5 | 426 | 27.12 |
| 9.8 | 58 | 3.69 |
| 10.0 | 48 | 3.06 |
| 8.5 | 43 | 2.74 |
| 8.8 | 38 | 2.42 |
| 7.5 | 37 | 2.36 |
| 9.9 | 33 | 2.10 |
| 4.3 | 20 | 1.27 |
| 5.9 | 17 | 1.08 |
| 5.4 | 16 | 1.02 |
| 9.3 | 16 | 1.02 |
| 5.3 | 14 | 0.89 |
| 8.1 | 8 | 0.51 |
| 8.2 | 8 | 0.51 |
| 8.6 | 8 | 0.51 |
| 9.6 | 5 | 0.32 |
| 9.1 | 4 | 0.25 |
| 4.9 | 3 | 0.19 |
| 6.6 | 3 | 0.19 |
| 4.4 | 2 | 0.13 |
| 6.3 | 2 | 0.13 |
| 7.6 | 2 | 0.13 |
| 6.1 | 1 | 0.06 |
| 6.4 | 1 | 0.06 |
| 7.2 | 1 | 0.06 |
| 7.7 | 1 | 0.06 |
| 8.3 | 1 | 0.06 |
The two first lines of these stats represent the most common types of vulnerabilities in the WordPress ecosystem: Reflected and Stored Cross-Site Scripting issues. This is normal, and if we check stats from other events that would be similar, the unusual part is that the third, fourth, and eighth lines are for the highest severity vulnerabilities (ranging from 9.8 to 10.0).
Altogether there were 164 reports with CVSS 9.0+ and 270 reports were 8.0+.
| CVSS range | Count | % |
|---|---|---|
| 10 | 48 | 3.06 |
| 9+ | 116 | 7.38 |
| 8+ | 106 | 6.75 |
| 7+ | 796 | 50.67 |
| 6+ | 433 | 27.56 |
| 5+ | 47 | 2.99 |
| 4+ | 25 | 1.59 |
Sure, some researchers tried to get as many points as possible, but it’s an obvious indicator that it wasn't that hard to find such critical issues.
You can get an even clearer picture by looking into vulnerability types. Most of those dangerous vulnerabilities have been in the repository for over a decade. Yes, you read it correctly. Most reports were for plugins and themes, which were last updated 6 to 11 years ago. Do you think that’s a lot? One report was for the plugin that was last updated 17 years ago, yet there are still live websites depending on it.
| Vulnerability type | Count | % |
|---|---|---|
| Cross Site Scripting (XSS) | 1056 | 67.22 |
| Cross Site Request Forgery (CSRF) | 152 | 9.68 |
| Arbitrary File Upload | 73 | 4.65 |
| SQL Injection | 67 | 4.26 |
| Privilege Escalation | 58 | 3.69 |
| PHP Object Injection | 33 | 2.10 |
| Local File Inclusion | 26 | 1.65 |
| Broken Access Control | 22 | 1.40 |
| Remote Code Execution (RCE) | 17 | 1.08 |
| Arbitrary Content Deletion | 15 | 0.95 |
| Arbitrary File Deletion | 11 | 0.70 |
| Sensitive Data Exposure | 10 | 0.64 |
| Arbitrary File Download | 7 | 0.45 |
| Broken Authentication | 6 | 0.38 |
| Server Side Request Forgery (SSRF) | 4 | 0.25 |
| Full Path Disclosure (FPD) | 3 | 0.19 |
| Settings Change | 3 | 0.19 |
| Bypass Vulnerability | 2 | 0.13 |
| Insecure Direct Object References (IDOR) | 2 | 0.13 |
| Path Traversal | 2 | 0.13 |
| Arbitrary Code Execution | 1 | 0.06 |
| Content Injection | 1 | 0.06 |
Another aspect that strongly suggests this event removed some nasty vulnerabilities from the repository is the statistics of prerequisites (the minimal role needed to exploit the vulnerability successfully).
As you can see, most of those vulnerabilities could be exploited without authentication. Usually, that would show that there are many CSRF reports as we consider them to be the ones that don’t need any authentication (from the attacker's perspective). However, if you look at the table above again, you will notice only 152 CSRF vulnerabilities.
| Prerequisite | Count | % |
|---|---|---|
| Unauthenticated | 976 | 62.13 |
| Contributor | 416 | 26.48 |
| Subscriber | 148 | 9.42 |
| Administrator | 20 | 1.27 |
| Author | 5 | 0.32 |
| Editor | 3 | 0.19 |
| Salesman | 1 | 0.06 |
| Shop manager | 1 | 0.06 |
| Student | 1 | 0.06 |
That’s why we made an extra check and filtered out only vulnerabilities that did not require authentication from any perspective (neither from the attacker nor from the other users). We got 194 vulnerabilities, which is 12.35% of the whole catch.
| Vulnerability | Count | % |
|---|---|---|
| Privilege Escalation | 42 | 21.65 |
| Arbitrary File Upload | 41 | 21.13 |
| PHP Object Injection | 28 | 14.43 |
| SQL Injection | 23 | 11.86 |
| Remote Code Execution (RCE) | 10 | 5.15 |
| Arbitrary File Deletion | 8 | 4.12 |
| Sensitive Data Exposure | 8 | 4.12 |
| Arbitrary Content Deletion | 7 | 3.61 |
| Broken Access Control | 5 | 2.58 |
| Local File Inclusion | 5 | 2.58 |
| Arbitrary File Download | 4 | 2.06 |
| Broken Authentication | 4 | 2.06 |
| Full Path Disclosure (FPD) | 3 | 1.55 |
| Bypass Vulnerability | 2 | 1.03 |
| Arbitrary Code Execution | 1 | 0.52 |
| Content Injection | 1 | 0.52 |
| Insecure Direct Object References (IDOR) | 1 | 0.52 |
| Server Side Request Forgery (SSRF) | 1 | 0.52 |
Patchstack is the most extensive CNA working on WordPress vulnerabilities, with over 6K CVE IDs already published. By processing all those vulnerabilities, we've noticed that many vendors/developers don’t care how people can contact them and report vulnerabilities. This is a big problem for which we even created the free mVDP program for every WordPress plugin and theme.
Can we measure this problem? Yes! Out of 1571 reports, at least 1162 were sent to WordPress plugins and themes review teams because the vendors' contacts were unavailable, outdated, or not working (broken contact forms, bouncing back emails, URLs pointing to dropped domain names).
| Contact | Count | % |
|---|---|---|
| WP review teams | 1162 | 73.97 |
| Private | 409 | 26.03 |
We want to thank the WordPress plugins review team, which worked with us closely and provided quick reactions to all our reports.
Consequences to the WordPress Plugins Repository
Each event has an outcome. In this case, again, we have something extraordinary. As we mentioned before, most of those plugins already looked abandoned or their developers were not accessible, so we were forced to report those vulnerabilities to the plugin review team. Such reporting often results in a plugin closure.
At the time of writing, 977 plugins are closed already (most of them temporarily, but if authors don’t take any action, the status will change). This is about 1.1% of all plugins in the repository.
While removing those vulnerable plugins is a great thing because we are making the repository safer, the problem with the visibility of closed plugins still exists. This means many users will still use those plugins and won’t even see any indicators of a security risk.
On the bright side, after many years, we are finally seeing some movement in this matter. There is even an experimental plugin allowing us to show statuses inside the admin panel. Kudos to Dion Hulse for pushing this. Now, we just hope that it will get merged sooner rather than later and that we won’t have to write about this topic again.
Some more stats
We want to share some stats about our rockstars who made this event that good. On average, each reporter submitted 43 reports. You can also see the October leaderboard here.
| Pos. | Researcher | Reports (valid) | CVSS (avg) |
|---|---|---|---|
| 1 | Kinorth | 275 | 7.32 |
| 2 | stealthcopter | 121 | 8.89 |
| 3 | SOPROBRO | 534 | 6.85 |
| 4 | Mika | 154 | 7.68 |
| 5 | LVT-tholv2k | 53 | 8.84 |
| 6 | Le Ngoc Anh | 44 | 7.1 |
| 7 | thiennv | 50 | 6.73 |
| 8 | TaiYou | 1 | 8.1 |
| 9 | Muhamad Agil Fachrian | 40 | 7.36 |
| 10 | Gab | 92 | 6.5 |
| 11 | Bonds | 9 | 9.73 |
| 12 | ghsinfosec | 18 | 7.92 |
| 13 | Dimas Maulana | 10 | 7.7 |
| 14 | theviper17 | 18 | 7.1 |
| 15 | Zlrqh | 16 | 6.9 |
| 16 | Joshua Chan | 21 | 7.48 |
| 17 | truonghuuphuc | 14 | 5.92 |
| 18 | C_T_R_L (Chance) | 6 | 8.65 |
| 19 | Fariq Fadillah Gusti Insani | 9 | 5.35 |
| 20 | Khalid Yusuf | 15 | 6.54 |
| 21 | hunter85 | 7 | 6.28 |
| 22 | Michael | 14 | 6.41 |
| 23 | Zaidan Rizaki | 3 | 5.63 |
| 24 | Marek Mikita | 16 | 5.14 |
| 25 | Hakiduck | 3 | 7.36 |
| 26 | Ayoub Nouri | 2 | 7.05 |
| 27 | savphill | 4 | 6.07 |
| 28 | Peter Thaleikis | 1 | 7.1 |
| 29 | casol | 3 | 6.3 |
| 30 | Pritam Dash | 1 | 5.3 |
| 31 | Hazem Brini | 1 | 6.5 |
| 32 | Junwoo Kang | 1 | 6.5 |
| 33 | Fazle Mawla | 1 | 6.5 |
| 34 | tahu.datar | 3 | 6.93 |
| 35 | UKO | 9 | 5.9 |
| 36 | Junsu Yeo | 1 | 4.9 |
| 37 | Certus Cybersecurity | 1 | 5.9 |
The highest AXP for one submission goes to TaiYou - 558.90. It’s also the highest score in Patchstack’s history. You can read more about it in this article.
While most of the findings got less than <1000 active installs (1471), there were also 2 reports for plugins with more than 1M active installs. On average there were 4551 active installs per report, giving a total of 7141940 active installs affected.
Everyone who made it possible 🥇
| Pos. | Researcher | Bounty | AXP |
|---|---|---|---|
| 1 | Kinorth | 3900 | 4386.3 |
| 2 | stealthcopter | 3300 | 4370.99 |
| 3 | SOPROBRO | 1800 | 3130.36 |
| 4 | Mika | 1600 | 2780.55 |
| 5 | LVT-tholv2k | 1000 | 1233.16 |
| 6 | Le Ngoc Anh | 500 | 624.8 |
| 7 | thiennv | 500 | 582.29 |
| 8 | TaiYou | 400 | 558.9 |
| 9 | Muhamad Agil Fachrian | 500 | 525.83 |
| 10 | Gab | 500 | 458.28 |
| 11 | Bonds | 500 | 420.8 |
| 12 | ghsinfosec | 300 | 407.37 |
| 13 | Dimas Maulana | 600 | 324.2 |
| 14 | theviper17 | 300 | 225.52 |
| 15 | Zlrqh | 300 | 182.22 |
| 16 | Joshua Chan | 200 | 171.06 |
| 17 | truonghuuphuc | 200 | 129.85 |
| 18 | C_T_R_L (Chance) | 100 | 129.16 |
| 19 | Fariq Fadillah Gusti Insani | 200 | 83.4 |
| 20 | Khalid Yusuf | 150 | 75.42 |
| 21 | hunter85 | 50 | 61.82 |
| 22 | Michael | 100 | 60.61 |
| 23 | Zaidan Rizaki | 0 | 48.6 |
| 24 | Marek Mikita | 0 | 44.05 |
| 25 | Hakiduck | 0 | 37.7 |
| 26 | Ayoub Nouri | 0 | 29.4 |
| 27 | savphill | 0 | 17.59 |
| 28 | Peter Thaleikis | 0 | 14.2 |
| 29 | casol | 50 | 13.98 |
| 30 | Pritam Dash | 0 | 10.6 |
| 31 | Hazem Brini | 0 | 6.5 |
| 32 | Junwoo Kang | 0 | 4.88 |
| 33 | Fazle Mawla | 0 | 4.88 |
| 34 | tahu.datar | 0 | 0 |
| 35 | UKO | 0 | 0 |
| 36 | Junsu Yeo | 0 | 0 |
| 37 | Certus Cybersecurity | 0 | 0 |
Also, the Lucky Researcher award goes to casol 🍀
Time to start the November Bug Bounty 📅
October was really difficult - submitting that many reports is not an easy task. That’s why in November we aren’t launching any special events, so we can all recharge a bit.
But it doesn’t mean nothing will happen. Soon we’ll announce more details on a Capture The Flag event we’ll host this month. All the challenges are created by our Alliance members.
Also, don’t forget to join our Discord, where you can find all the amazing conversations and learn from others. And if you want to learn more about security - check out the Patchstack Academy.
The post Nearly 1000 Plugins Closed During WordPress Security Cleanup appeared first on Patchstack.
]]>The post We launched Patchstack Academy appeared first on Patchstack.
]]>Why Patchstack Academy?
When searching for WordPress security online, most results focus on securing websites or recommending plugins (like Patchstack!). However, resources for aspiring ethical hackers and developers seeking to enhance code security are scarce.
What will you learn?
Patchstack Academy aims to fill this gap by educating on:
Our goal is to increase the number of skilled researchers in the WordPress community, contributing to a safer and more secure platform for everyone. Also, it’s a great place to start your adventure with our Bounty Program. By understanding how different vulnerabilities happen, you can start finding them on your own to build your profile and earn bounties as you improve your knowledge and skills.
How Can You Contribute?
While we've built the foundation of Patchstack Academy, your contributions can help it grow. You can:
- Improve existing articles (simply submit a Pull Request).
- Write new articles to expand our knowledge base.
Be sure to read our How to Contribute guide before you start.
We’re excited to see you in the Patchstack Academy hallways! If you have any questions or you like to chat about the Academy – join our Discord server.
The post We launched Patchstack Academy appeared first on Patchstack.
]]>The post Biggest WordPress Bug Bounty program upgrade is here! appeared first on Patchstack.
]]>Since the program's introduction in 2021, we have paid more than $80k+ in bounties. The program has evolved through many steps, starting with polishing the rules and making the competition between all researchers fair and open. With each upgrade, we have tried to make our WordPress Bug Bounty program more friendly, accessible to anyone, and generous to all deserving.
We always tried to put an accent on the community, and it paid off well. The Bug Bounty program was a trigger that gathered many people, like security researchers and developers to the Patchstack Alliance community, which is the backbone of the WordPress Bug Bounty program and is open to anyone on the Patchstack Alliance Discord server. Seeing so many people discussing, sharing information, and researching to make open-source software safer is a vision we always had on our minds.
We see that the Bug Bounty program has grown out of its former frame and needs another upgrade - and we are glad to announce that the Patchstack Bug Bounty program gets its most significant upgrade since its release in 2021!
Monthly competition and bounties
We have great news for all researchers competing in the monthly Bug Bounty program competitions. We thought what could be good enough to say that we really appreciate your input into WordPress security - and we got the idea! Monthly competition bounties will now be twice as big - double (2x). Also, we are introducing extra positions. From now on, the monthly competition will be for TOP 20 (instead of TOP 15). Oh, to mention, we have a guaranteed bounty pool of $8,800 for monthly competitions (the previous was $4,250).
| Position | Bounty |
| 1 | $2,000.00 |
| 2 | $1,400.00 |
| 3 | $800.00 |
| 4 | $600.00 |
| 5 | $500.00 |
| 6 | $400.00 |
| 7 | $400.00 |
| 8 | $400.00 |
| 9 | $400.00 |
| 10 | $400.00 |
| 11 | $200.00 |
| 12 | $200.00 |
| 13 | $200.00 |
| 14 | $200.00 |
| 15 | $200.00 |
| 16 | $100.00 |
| 17 | $100.00 |
| 18 | $100.00 |
| 19 | $100.00 |
| 20 | $50.00 |
| Random | $50.00 |
Zeroday program bounties
Patchstack Bug Bounty program researchers worldwide proved that they can find non-ordinary vulnerabilities that pose the highest risk to vulnerable software users and are exploitable due to their specific nature. Zeroday (0day) vulnerabilities are something special that we try to catch up on time and protect software users and website visitors from any malicious impact. To show how important it is for us and the WordPress ecosystem, we decided to increase the bounties we give for the Zeroday program, which is now up to $14,400 per valid report.

Also, we are introducing lower-range bounties for components with lower active install count. We will accept reports for the Zeroday program even if the vulnerable component has 5000+ active installations. And now, the fun part. These are the new bounties for the Zeroday program:
| Active installs | Unauthenticated | Subscriber/Customer |
| 5000+ | $150.00 | $75.00 |
| 10,000+ | $450.00 | $225.00 |
| 50,000+ | $900.00 | $450.00 |
| 100,000+ | $1,800.00 | $900.00 |
| 500,000+ | $3,600.00 | $1,800.00 |
| 1,000,000+ | $7,200.00 | $3,600.00 |
| 5,000,000+ | $14,400.00 | $7,200.00 |
Let's celebrate!
Yes, let's celebrate because why not? You remember those special events we had before and how intense the competition was. Let's play again! Last time, we were looking for Cross-Site Scripting (XSS) vulnerabilities, but this time, let's hunt for SQL Injection (SQLi) vulnerabilities.
Let's call this special event "Back to SQL" because many researchers will soon return to their schools and universities at the beginning of September, so why not have some fun before that?

Rules are simple
- Time – from 1 August 2024 (00:00:01 UTC) to 31 August 2024 (23:59:59 UTC).
- Scope – SQLi vulnerabilities with severity not lower than 8.0 (excluding vulnerabilities requiring superadmin, admin, or any custom high privilege role) in components with 10K or more active installs with the last update not over three years old.
- Bounties: AXP x2 (will be counted for the monthly competition) + bounty per vulnerability if CVSS 8.x – $75, CVSS 9.X – $100, CVSS 10 – $150.
- For other rules check the WordPress Bug Bounty program guides and rules.
What's next?
The biggest change coming soon is self-managed profiles for researchers. We are upgrading the way researchers can manage their profiles and see all their stats and reports. More surprises are coming, so stay in touch to get the latest news right away.

More information
Official announcements and program updates are disseminated via the Patchstack Alliance Discord server and official Patchstack social media channels at Patchstack Alliance Discord Server. If you need additional information, you can use a support ticket on the Patchstack Alliance Discord to ask for help.
Twitter(X) https://twitter.com/patchstackapp
Facebook https://www.facebook.com/patchstackapp
LinkedIn https://www.linkedin.com/company/patchtsack
The post Biggest WordPress Bug Bounty program upgrade is here! appeared first on Patchstack.
]]>The post The New Chapter In WordPress Bug Bounty Hunting appeared first on Patchstack.
]]>This project was later renamed to Patchstack Red Team and then to Patchstack Alliance. Over the years, we’ve built the most active ethical hacker community behind WordPress and paid over $60,000 in cash rewards.
2023 was our most successful year ever, our community has grown to 400+ members, Patchstack became a member of the OpenSSF, and we’ve become the global leader of vulnerability intelligence in the world (highest number of CVEs assigned in 2023).
After we launched the Patchstack mVDP program in early 2023 for WordPress plugin developers, we started working on the new Patchstack bug bounty program. Today, we’re excited to announce the new Patchstack bug bounty competition, the Patchstack zero-day program, and the Patchstack researcher rank.
Updated WordPress bug bounty competition
We are not going to change what already works, but we are increasing the rewards significantly. Every month, the top researcher with the highest AXP score will receive $1000 USD. The second will get $700 and the third place will get $400.
Higher severity = higher AXP score.
The top 15 researchers get paid at least $100 each month (if they have at least 1 valid vulnerability reported). We also pay $50 randomly to one researcher each month who did not get to the top 15 but still contributed to the security of the open source with a valid vulnerability report.

Monthly cash rewards:
| 1st place | $1,000.00 |
| 2nd place | $700.00 |
| 3rd place | $400.00 |
| 4th place | $300.00 |
| 5th place | $250.00 |
| 6th place | $200.00 |
| 7th place | $200.00 |
| 8th place | $200.00 |
| 9th place | $200.00 |
| 10th place | $200.00 |
| 11th place | $100.00 |
| 12th place | $100.00 |
| 13th place | $100.00 |
| 14th place | $100.00 |
| 15th place | $100.00 |
| random prize | $50.00 |
While the monthly guaranteed prize pool almost doubles in size, we’ve removed the “special bounties” to simplify the program as they would partially overlap with our new initiative, the Patchstack zero-day program.
Introducing the Patchstack zero-day program
Ever since we launched the Patchstack mVDP for plugins, we’ve also worked on getting per-vulnerability bounties to researchers in direct partnership with plugin developers.
We’ve made it simple for plugin developers to process vulnerability reports & pay additional bounties to the ethical hackers.
To make sure more security vulnerabilities with a potential of becoming exploited as zero-days get reported ethically, we launch the Patchstack zero-day program starting from January 1st. 2024.
Patchstack is paying up to $2000 per vulnerability for exploitable & critical vulnerabilities found in any of our partners' plugins. It’s a simple and transparent system, where the payouts are based entirely on the number of active installs the vulnerable plugin has.
Today, we have over 200 WordPress plugins on the Patchstack managed vulnerability disclosure program such as Elementor, RocketWP, Kadence, MainWP, and many, many others.
You can see the full list here: https://patchstack.com/database/vdp
Per vulnerability cash rewards:
| Payouts: | Unauth. | Subscriber/Customer |
| Active installs 10,000+ | $100.00 | $50.00 |
| Active installs 50,000+ | $150.00 | $75.00 |
| Active installs 100,000+ | $300.00 | $150.00 |
| Active installs 500,000+ | $450.00 | $225.00 |
| Active installs 1,000,000+ | $1,000.00 | $750.00 |
| Active installs 5,000,000+ | $2,000.00 | $1,500.00 |
Here are the full requirements to be eligible for a bounty:
- The software has an active VDP listed on patchstack.com/database/vdp/
- The vulnerability leads to a full site compromise (ability to upload & access a functional backdoor).
- The vulnerability is exploitable with Unauthenticated(none), Subscriber, or Customer (WooCommerce) permissions.
- The report includes a working exploit.
- No prerequisites (default settings / most common environment / does not need any other vulnerability to be present).
- The exploitation does not require any user interaction.
All of the vulnerabilities reported to the Patchstack zero-day program will also receive AXP (with a bonus) which will be counted for the current month's bug bounty competition.
PS! If you’re a plugin developer, you can sign up for the program for free here: https://patchstack.com/for-plugins/
Introducing the Patchstack researcher rank
Many of the most active community members have been active in WordPress bug bounty hunting and have been staying with us for years. They have shown incredible consistency and passion for open-source security.
To make them stand out from the rest of the community, we’ve introduced a level system.
All of the AXP you earn from reports will be permanently added to your profile. After your first valid report, you will start from level 1 and can reach the maximum level of 10. We also have rewards from Level 2 - Level 10.
Each reward can be earned once you reach the new level and the total amount of rewards you can unlock is $5737 USD with additional 2 mystery box rewards at level 5 and level 10.
Rewards unlocked on each level:
| Rank | Reward |
| Level 2 | $200 |
| Level 3 | $300 |
| Level 4 | $400 |
| Level 5 | $500 + Mystery Box |
| Level 6 | $600 |
| Level 7 | $700 |
| Level 8 | $800 |
| Level 9 | $900 |
| Level 10 | $1337 + Mystery Box |
Building the largest open-source security community
Our vision behind the Patchstack Alliance community and WordPress bug bounty hunting is to bring ethical hackers and open-source developers together. We believe that ethical hackers who contribute security reports to open-source projects are equal contributors to developers who contribute code.
We are well aware that what makes open-source software so great is the community and people behind it, so we must do the same for open-source security.
What this community has done for the WordPress ecosystem is already historical, but it’s all just the beginning.
We have much more exciting news coming in Q1, so whether you’re an ethical hacker or an open-source developer - don’t forget to join our community in Discord: https://discord.gg/uHcsy8rgPu
The post The New Chapter In WordPress Bug Bounty Hunting appeared first on Patchstack.
]]>The post Patchstack Alliance Bounty Program Events for December appeared first on Patchstack.
]]>Events
We have four full competition weeks in December, each dedicated to particular vulnerabilities.
🏁 Week #1 - December 4-10, 2023 (finished!)
The first week is an easy one - warm up before getting serious. In the first week, you will compete by reporting Broken Access Control and Cross-Site Request Forgery (CSRF) vulnerabilities.

Week 1 results
🥇 Mika - 115,40 AXP ($300 bounty)
🥈 Le Ngoc Anh - 67,45 AXP ($200 bounty)
🥉 Friday - 32,75 AXP ($100 bounty)
🎖️ Yudistira Arya - 16,90 AXP
🎖️ Joshua Chan - 16,40 AXP
🏁 Week #2 - December 11-17, 2023 (finished!)
The second week will get more serious as you will compete by reporting Cross-Site Scripting (XSS) and Sensitive Data Exposure vulnerabilities.

Week 2 results
🥇 Le Ngoc Anh - 252,05 AXP ($300 bounty)
🥈 Ngô Thiên An (ancorn_ from VNPT-VCI) - 214,7 AXP ($200 bounty)
🥉 Joshua Chan - 78,2 AXP ($100 bounty)
🎖️ Yudistira Arya - 42,6 AXP
🎖️ Dhabaleshwar Das - 14,2 AXP
🎖️ Dimas Maulana - 14,2 AXP
🎖️ Mika - 13,99 AXP
🎖️ Bryan Satyamulya - 8,85 AXP
🏁 Week #3 - December 18-24, 2023 (finished!)
On the third week of December, you can show your skills by reporting SQL Injection (SQLi), Open Redirection, and Broken Authentication/Bypass vulnerabilities.

Week 3 results
🥇 Le Ngoc Anh - 69,13 AXP ($300 bounty)
🥈 Yudistira Arya - 59,77 AXP ($200 bounty)
🥉 Joshua Chan - 27,9 AXP ($100 bounty)
🎖️ Ngô Thiên An (ancorn_ from VNPT-VCI) - 9,56 AXP
🏁 Week #4 - December 25-31, 2023 (finished!)
In the year's final week, you'll compete with other elite researchers in finding Remote Code Execution (RCE), PHP Object Injection, Arbitrary File (upload/download/deletion), and Privilege Escalation vulnerabilities.

Week 4 results
🥇 Yudistira Arya - 149,80 AXP ($300 bounty)
🥈 Ngô Thiên An (ancorn_ from VNPT-VCI) - 75,45 AXP ($200 bounty)
🥉 Le Ngoc Anh - 38,65 AXP ($100 bounty)
🏁 Monthly competition - December (finished!)
The great news is that monthly competition will also happen, and all points from weekly events will be counted in your monthly point pool. It means you can participate in five events in December.
Results
Bounties?
Yes, we have them. Each week, we will give bounties to TOP 3 researchers. 1st place is $300, 2nd place is $200, and 3rd place is $100 - meaning the weekly bounty pool is $600. Plus, at the end of December, we will count the points for the monthly results, and TOP 15 + 1 researchers will split up an additional $2450. It means that the overall December bounty pool is $4850!
Rules!
- Patchstack Alliance standard rules apply to these events. Please read the rules carefully. Please report particular vulnerability types on specific weeks to compete in dedicated week events.
- Yes, you will get extra AXP points for boosted products from Patchstack mVDP program, you can check the list of boosted products here - Extra points!
- We will create public profiles for all new researchers who will submit valid reports. Each public profile will include information about your results, also it will have your Twitter, GitHub, Linked, your personal and social links. Also we accept "BuyMeACoffee" links on the profiles and on database entries for vulnerabilities you have discovered.
- December results will be visible on this leaderboard. Weekly results will be announced by updating this article, on Patchstack Twitter account and on Patchstack Alliance Discord server.
- All valid reports will get their CVE IDs. Even if your report does not get any points (like admin+ vulnerabilities), you'll still get the CVE ID if the report is valid.
- If you have any questions, create a ticket on the Patchstack Alliance Discord server or dm to [email protected].
The post Patchstack Alliance Bounty Program Events for December appeared first on Patchstack.
]]>The post Announcing Patchstack Alliance Season 1 - New Bug Hunt Challenge and Rewards appeared first on Patchstack.
]]>Let's start with the things we will hunt for this season - themes, page builders, and their extensions. All reports that will be related to themes, page builders, or their extensions will get a +15% XP boost!
Why boost? Because this season is integrated into the monthly competitions, it's not separate. So all reports are acceptable, but the ones for themes, page builders, or extensions are getting more points.

Higher bounties
With this season, we have increased the monthly bounty pool from 1900 USD to 2425 USD. It means the main pool is now 2025 USD, and there are 400 USD reserved for the special bounties (see the rules for more information about them).
We are also increasing the bounties for the top 10 researchers:
- The first-place winner will get 650 USD
- Second place 350 USD
- Third place 250 USD
- Fourth to tenth places will be awarded 75 USD bounties.
- Eleventh to the fifteenth position will earn 50 USD.
Get rewarded by the public
Patchstack database is powering security scans for nearly 5 million WordPress sites already. If a user gets alerted by a vulnerability you found, we want to give them an opportunity to say thanks to you as well (so look for vulnerabilities in plugins that have high installation counts).
We are introducing the personal BuyMeACoffee buttons that will be visible on the following:
- On your Alliance member profile page.
- On the report pages that we are sending to the vendors to let them know about the vulnerability you have found.
- On the database entries with the vulnerabilities, you have reported to the Alliance.

This will give vendors and the community a clear way to thank you for your research. Just remember to create an account on BuyMeACoffee and provide us with your link so we can assign it to your Alliance profile.
More gamification
Oh, and that's not the end. We want to spice up your competition. You will be able to see your positions on the leaderboard, but the scores will be hidden until the end of the month. So you will play with "hidden cards," making it harder to understand how many points separate you from the other researcher above in the leaderboard.
Just keep an eye on the leaderboard, because you’ll never know when someone might take over your position!
Join the Alliance
Patchstack Alliance is a community of ethical hackers who contribute into making the entire web more secure. It’s a great place to learn new skills, make friends and create a portfolio of your security research.
If you're a security researcher, you can join our Patchstack Alliance program here to report vulnerabilities and earn rewards. You can also join our Discord channel.
The post Announcing Patchstack Alliance Season 1 - New Bug Hunt Challenge and Rewards appeared first on Patchstack.
]]>The post December WordPress Bug-Hunting Challenge appeared first on Patchstack.
]]>In December, we released a public leaderboard and profiles for the top security researchers who contribute to making WordPress and the open-source web more secure.
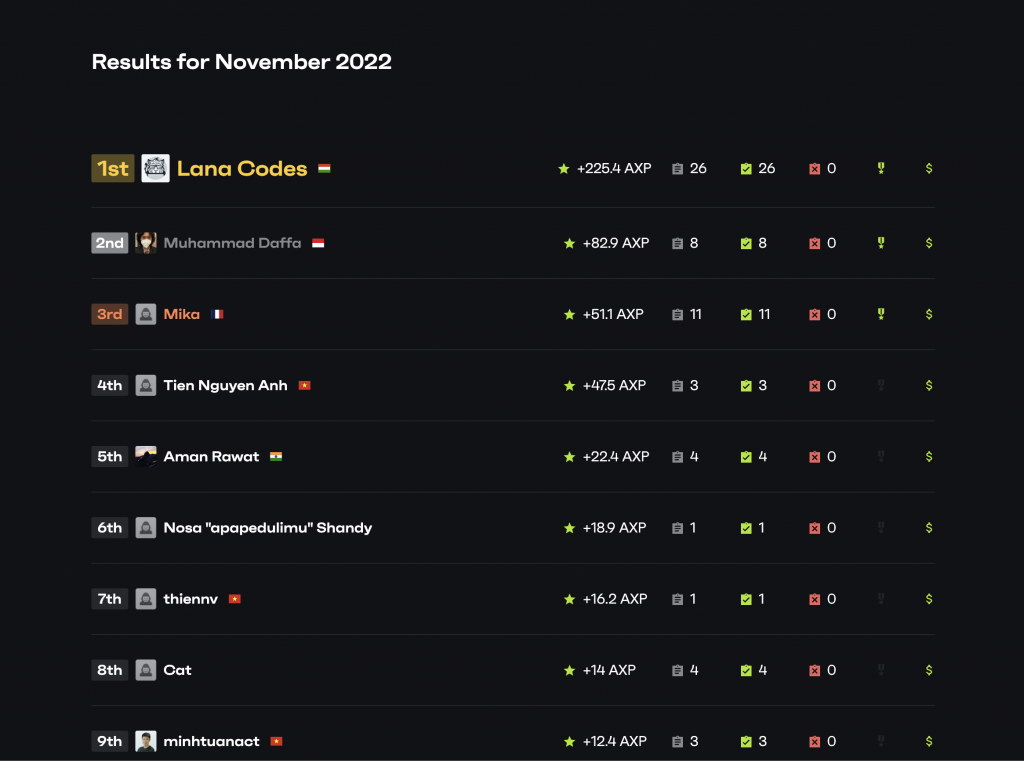
You can see the November WordPress bug-hunting winners and profiles here: https://patchstack.com/database/leaderboard?monthly=2
December prize pool is $4300 in cash rewards

On each Monday, we’ll announce the scope for the weekly WordPress bug-hunting focus. With 4 weeks of challenges and monthly prizes on top, we pay out $4300 in cash rewards!
Each week has a special vulnerability that needs to be hunted in any publicly available WordPress themes, plugins, or even in the core itself.
The top 3 researchers with the most points from each week will get cash rewards (1st place - $300, 2nd - $200, and 3rd - $100). All points will also be used for the monthly Patchstack Alliance competition, with an additional $1900 prize pool.
The first week (Dec. 5-11) - Cross-Site Request Forgery (CSRF) - finished!
1st place ($300 bounty) - Lana Codes reported 58x vulnerabilities (349.4 points)
2nd place ($200 bounty) - Muhammad Daffa reported 9x vulnerabilities (129 points)
3rd place ($100 bounty) - Cat reported 25x vulnerabilities (125.3 points)
The second week (Dec. 12-18) - Cross-Site Scripting (XSS) - finished!
1st place ($300 bounty) - minhtuanact reported 8x vulnerabilities (50.4 points)
2nd place ($200 bounty) - pilvar reported 1x vulnerabilities (31.5 points)
3rd place ($100 bounty) - Muhammad Daffa reported 2x vulnerabilities (21.5 points)
The third week (Dec. 19-25) - SQL injection (SQLi) - finished!
1st place ($300 bounty) - Le Ngoc Anh reported 2x vulnerabilities (16.8 points)
2nd place ($200 bounty) - minhtuanact reported 10x vulnerabilities (14.6 points)
3rd place ($100 bounty) - Lucio Sá reported 1x vulnerability (7.5 points)
The fourth week (Dec. 26-31) - Remote Code Execution (RCE) - finished!
1st place ($300 bounty) - minhtuanact reported 1x vulnerability (9 points)
2nd place ($200 bounty) - Le Ngoc Anh reported 1x vulnerability (8.5 points)
3rd place ($100 bounty) - none
More details on the Patchstack Alliance Discord
Claim your CVEs
Patchstack is an official CNA authorized by MITRE to assign CVE IDs to vulnerabilities reported through the Patchstack Alliance bug bounty program. We make sure the reports get to the developers and that all ethical hackers get credit for their research and contribution.
Join the community
Patchstack Alliance is a community of ethical hackers who contribute to making the entire web more secure. It’s a great place to learn new skills, make friends and create a portfolio of your security research.
For more information & rules, join our Discord server here: https://patchstack.com/bug-bounty/
The post December WordPress Bug-Hunting Challenge appeared first on Patchstack.
]]>The post Patchstack Alliance September Winners & Leaderboard appeared first on Patchstack.
]]>Our researchers found 53 confirmed vulnerabilities. 9 of the vulnerabilities were found in plugins with 100,000+ installs across WordPress, including one with 2 million installs. Thought to be fair, that vulnerability in question was not particularly severe.
A couple of vulnerabilities picked up did, however, have a CVSS score over 9.0.
Leaderboard and winners
September bug hunt winners are below:

Congrats to Lana Codes for turning up the heat, and nabbing the top spot this month!
A shoutout to L.Ayotte & T.Jacobs, who are not part of the Alliance but who did report a vulnerability in their own product - we salute you.
How are points awarded?
The score we use to see who gets what prize is made up of several factors, including the popularity of the plugin and the severity of the vulnerability.
For example, a vulnerability with a CVSS score of 6 in a plugin with 1,000,000 installs will give more points than a very critical vulnerability in a plugin with only 1,000 installs.
All reports are important, though, and help make the web more secure! On this note, we want to say thanks to all researchers who submitted vulnerability reports last month!
If you want to compete in the bug hunt and contribute to making WordPress safer, you can join the Patchstack Alliance here.
What is Patchstack Alliance?
Patchstack Alliance is a community of ethical hackers and researchers who support the open web by finding and reporting vulnerabilities in WordPress plugins and themes.
All valid vulnerabilities are also publicly available in our vulnerability database.
The post Patchstack Alliance September Winners & Leaderboard appeared first on Patchstack.
]]>The post Patchstack Alliance August Winners & Leaderboard appeared first on Patchstack.
]]>A very busy august
The Patchstack Alliance reported 105 new validated vulnerabilities last month. This doesn't mean that WordPress plugin developers have gotten lazy or careless over the summer - we've just had new people join in on the bug hunt and thus we're casting a wider net.
Oh, and a big "Welcome!" to our new researchers - and a big "thank you" for helping make WordPress safer. Happy to have you aboard!
As for stats, the most popular plugin with a reported vulnerability had more than a million installs. The highest CVSS score reported by our researchers was 9.9 out of 10, indicating critical severity.
We'll add that we also picked up a lot of less critical vulnerabilities in smaller plugins that didn't have many installs. A lot of these were abandoned plugins though, so helping the community find and get rid of those plugins is very important. If you want to know why it's important not to use abandoned plugins, then Robert has a great article about it on our blog.
Leaderboard and winners
August bug hunt winners are below:

How do we award points?
Eagle-eyed readers may notice that the number of vulnerabilities reported by an individual doesn't seem to have an impact on the total score. That's because the score we use to see who gets what prize is made up of several factors, including the popularity of the plugin and the severity of the vulnerability.
So for example, a vulnerability with a CVSS score of 6 in a plugin with 1,000,000 installs will give more points than a very critical vulnerability in a plugin with only 1,000 installs.
But in any case, we want to say thanks to all researchers who submitted vulnerability reports last month, we were excited to see such active contributions last month!
If you want to compete in the bug hunt and contribute to making WordPress safer, you can join the Patchstack Alliance here.
What is Patchstack Alliance?
Patchstack Alliance is a community of ethical hackers and researchers who support the open web by finding and reporting vulnerabilities in WordPress plugins and themes.
All valid vulnerabilities are also publicly available in our vulnerability database.
The post Patchstack Alliance August Winners & Leaderboard appeared first on Patchstack.
]]>The post Patchstack Alliance July Winners & Leaderboard appeared first on Patchstack.
]]>Below you'll find the leaderboard and winners of July's bug hunt.
July 2022 summary
Our researchers caught some seriously big fish in July - one reported vulnerability was found in a plugin with more than 3 million active installs. The average active installation count per reported vulnerability was 141,903.
This goes to show that bugs happen to the best of us - but as long as we take them seriously we can learn from our mistakes and become better developers.
The highest CVSS score reported was 9.1, which indicates critical severity. The plugin that contained that particular bug had 600,000+ active installs.
Besides the main prizes for the Alliance points each month, we have special bounties for vulnerabilities with the highest active install count and highest CVSS severity base score. This month once again Yeraisci managed to nab both prizes!
Leaderboard and winners
Without further ado, here are July's top bug hunters:

Thanks to all researchers who submitted vulnerability reports last month!
If you want to compete in the bug hunt and contribute to making WordPress safer, you can join the Patchstack Alliance here.
What is Patchstack Alliance?
Patchstack Alliance is a community of ethical hackers and researchers who support the open web by finding and reporting vulnerabilities in WordPress plugins and themes.
All valid vulnerabilities are also publicly available in our vulnerability database.
The post Patchstack Alliance July Winners & Leaderboard appeared first on Patchstack.
]]>The post Patchstack Alliance - June Winners and Leaderboard appeared first on Patchstack.
]]>Each month we give out rewards and recognition to our community of researchers for their contributions to finding WordPress vulnerabilities.
Below you'll find the leaderboard and winners of June's bug hunt.
What is Patchstack Alliance?
Patchstack Alliance is a community of ethical hackers and researchers who support the open web by finding and reporting vulnerabilities in WordPress plugins and themes.
In doing so, we help protect WordPress websites from attacks.
June 2022 summary
Our researchers had a pretty spicy month - a few of the reported vulnerable plugins had more than 100,000 active installations, and one of them even had more than 800,000 active installs.
We can say that in June, our researchers reported software that affects more than one million active websites on the Internet. Average active installation count per reported vulnerability - 79021 websites.
Let's talk about other numbers. To measure the severity of each vulnerability, we use the CVSS (ver. 3.1) scheme and calculator. The highest CVSS score vulnerability reported by Alliance researchers in June had 9.3 (critical) base score points. It was for the plugin that has 20,000 active installs.
One of the most impressive reports we received in June had a plugin vulnerability with a 9.1 (critical) base score at a whooping 100,000 active installs!
The average CVSS base score for reports received in June was 5.2 (medium).
Besides the main prizes for the Alliance points each month, we have special bounties for vulnerabilities with the highest active install count and highest CVSS severity base score. Both special prizes were won by Rafie Muhammad, aka Yeraisci, who also took the top spot on the leaderboard this month!
Well done, Rafie - you, sir, are on a roll.
Leaderboard and winners
June's leaderboard is as follows

Thanks to all researchers who submitted vulnerability reports last month!
If you want to compete in the bug hunt and contribute to making WordPress safer, you can join the Patchstack Alliance here.
All valid vulnerabilities are also publicly available in our vulnerability database.
The post Patchstack Alliance - June Winners and Leaderboard appeared first on Patchstack.
]]>The post Patchstack Bug Bounty Guidelines & Rules (2026 edition) appeared first on Patchstack.
]]>Introduction
1.1. Patchstack operates a public Bug Bounty Program focused on open-source software, primarily vulnerabilities within the WordPress ecosystem. More information is available at: https://patchstack.com/bug-bounty/
1.2. The program includes monthly competitions and occasional custom events throughout the year. Participation is open to anyone who submits valid and unique vulnerabilities in accordance with these rules.
1.3. All program operations, timelines, and communications follow Coordinated Universal Time (UTC).
1.4. Patchstack reserves the right to change or update these rules at any time, without prior notice.
1.5. All valid, in-scope vulnerabilities submitted through the Patchstack Bug Bounty Program will be publicly disclosed in the Patchstack Vulnerability Database.
1.6. Patchstack is a CVE Numbering Authority (CNA). This means that each valid, in-scope vulnerability will receive a unique CVE ID and be published in the CVE database, provided no conflicts exist with previously issued CVEs.
1.7. CVE assignment follows official CVE Program rules, with the following exception - assignment may be delayed to prevent CVE conflicts between multiple CNAs operating in the same ecosystem (for example, WordPress).
1.8. By participating in the Patchstack Bug Bounty Program, researchers can earn bounties by reporting valid, unique, and impactful security issues affecting in-scope components such as WordPress core, plugins, and themes.
1.9. By submitting a vulnerability to the Patchstack Bug Bounty Program, you agree to comply with all rules outlined in this document and any related documents.
Reporting Protocol
2.1. All vulnerability reports must be submitted ONLY through the official reporting form - https://patchstack.com/database/report
2.2. Reports sent via email or any other channel will not be accepted.
2.3. A researcher account is created automatically after at least one valid, in-scope vulnerability is submitted. You can access your account any time via this link - https://vdp.patchstack.com/researchers/login by using the email address you're using for vulnerability reporting.
2.4. Each researcher may operate only one account. Creating or using multiple accounts may result in immediate suspension of all related accounts.
2.5. Participation is open to individuals and companies that follow and respect the program rules.
2.6. Reports must be submitted by individual researchers or organizations. Team submissions are not supported, as the monthly competition system does not allow team-based point calculations.
Scope
3.1. The Patchstack Bug Bounty Program accepts vulnerability reports for components in the WordPress ecosystem, including:
- WordPress core
- WordPress plugins (free/premium)
- WordPress themes (free/premium)
3.2. A vulnerability is considered valid only if it has a clear and measurable security impact.
3.3. Both free and premium plugins and themes are accepted. For premium components, researchers must provide the original, unmodified archive file for validation. If a theme depends on specific plugins, those plugins must also be provided.
⚠️ 3.4. The following are not accepted:
- ⚠️ Vulnerabilities with a CVSS v3.1 base score lower than 6.5 are not accepted.
- ⚠️ Components with fewer than 1,000 active installs are generally considered out of scope. Exceptions may be made for reports with a CVSS base score of 8.5 or higher, provided the required privileges do not exceed Unauthenticated, Subscriber, or Customer roles and install count is not lower than 100 active installs.
- ⚠️ Only vulnerabilities that can be exploited by unauthenticated users or by users with default Subscriber or Customer roles are eligible. Reports requiring Contributor-level access are accepted only if the CVSS base score is 7.5 or higher. Vulnerabilities requiring roles with higher privileges are out of scope.
- ⚠️ Reports involving custom roles are accepted only if the role provided by the affected component has capabilities equivalent or closely aligned with those of the Subscriber or Customer roles. Reports involving roles with capabilities exceeding those of the default Subscriber or Customer roles are not accepted.
- CSV injection vulnerabilities, as they depend on external actions outside WordPress and cannot be reliably evaluated.
- IP spoofing issues, unless they directly affect a feature that relies on IP integrity (such as IP-based blocking) and is explicitly intended to resist spoofing.
- Race condition vulnerabilities with a CVSS v3.1 base score below 7.1, unless a clear security impact is demonstrated.
CAPTCHA or any other version of Turing test bypass. - Arbitrary user registration by unprivileged/unauthenticated users, unless the vulnerability results in the creation of an arbitrary administrator account.
- Authenticated (Contributor or higher) shortcode preview issues, unless sensitive or security-related information (such as PII) is disclosed with measurable impact (this limitation does not apply to XSS vulnerabilities).
- CSRF or Broken Access Control issues that only dismiss notices, unless the dismissal creates a real security impact.
- IP bypass issues affecting non-critical actions (such as likes, views, or counters).
- If the last version of the component was released more than three years ago.
- If vulnerability doesn't exist in the latest version (for example patched by vendor, but never disclosed).
- The component must be publicly available through WordPress.org, the vendor’s official website, or another publicly accessible source such as GitHub, CodeCanyon, or ThemeForest. Custom-made, modified, or private components that are not publicly distributed are not accepted.
Uniqueness Requirement
4.1. All reported vulnerabilities must be new and unique and must not have been previously reported or publicly disclosed.
4.2. Exceptions apply if the vulnerability was first reported directly to the vendor prior to submission to Patchstack. Such reports are accepted only if the vendor confirms the vulnerability and indicates a willingness to patch it. This requirement is mandatory for components developed or owned by Automattic, which must first be reported through Automattic’s HackerOne program.
4.3. If researcher account is suspended, all associated XP, vulnerability reports, and CVE assignments remain permanently linked to that account. They cannot be transferred or reassigned.
4.4. If multiple researchers report the same vulnerability (even across different parameters or endpoints), credit is given to the first valid submission. Attempts to manipulate the system, such as using multiple accounts or submitting duplicates across different bounty programs may result in penalties, including account suspension.
4.5. Incomplete patches that are publicly disclosed are not considered new vulnerabilities. However, if an incomplete patch introduces a new attack vector that was not possible before, it may be considered a new vulnerability.
Quality Assurance
5.1. All reports must be submitted using the official reporting form and must follow the form’s requirements: https://patchstack.com/database/report
5.2. Reports must be complete, accurate, and reproducible. Incomplete reports will be rejected. Researchers are given up to two chances to fix and resubmit rejected reports.
5.3. Each report must include:
- A clear, step-by-step text-based proof of concept (PoC)
- Steps starting from plugin or theme installation and ending with successful exploitation
- All required raw HTTP request(s) in text form
- The exact payload(s) used during testing
- Video screenshots are highly appreciated
⚠️ 5.4. Repeated submission of false-positive vulnerability reports, or a high rate of false positives (5% or higher), will result in the researcher being removed from the leaderboard for one month, with a cooldown period applied (no reports accepted).
⚠️ 5.5. If same malicious behavior persists, the researcher will be permanently banned from the Patchstack Bug Bounty Program and the Patchstack Alliance community. Any pending bounties, if applicable, will be returned to the bug bounty pool.
⚠️ 5.6. Researchers who disregard the Patchstack mVDP by reporting or selling vulnerabilities to any third party will be permanently banned from the Patchstack Bug Bounty Program and the Patchstack Alliance community. Their accounts will be deleted, and any associated achievements will be removed.
Rejection Criteria
6.1. Reports may be rejected for reasons including, but not limited to:
- Incomplete or inaccurate information
- Invalid vulnerability claims
- Use of non-standard or modified user roles
- Reports for closed or inaccessible plugins or themes are not accepted.
- Patchstack may reject reports if the affected component is not publicly distributed through WordPress.org, Envato, GitHub, or another widely recognized repository.
- Reports submitted by the vendor or developer of the affected component are accepted for disclosure purposes but are not eligible for bounties.
Vendor Engagement
7.1. Patchstack will use the most efficient publicly listed vendor contact channels for vulnerability reporting.
7.2. Contact methods that require account registration will be ignored.
7.3. If no contact details are available, the vulnerability may be disclosed immediately.
7.4. Vendors are notified once. It is the vendor’s responsibility to patch the issue promptly.
CVE Assignment
8.1. CVE IDs are assigned only after confirming there are no conflicts with existing CVEs. Assignment may be delayed to prevent duplicate CVE IDs across multiple CNAs.
8.2. If multiple researchers report the same vulnerability, the CVE is assigned to the first valid report. All later submissions are rejected.
8.3. Researchers may disclose vulnerabilities already reported to other programs by selecting the appropriate option during submission. In such cases, the vulnerability may be listed without a CVE ID.
Research Points (XP)
9.1. XP (Research Points) are awarded for valid vulnerability reports and are used to determine competition rankings and winners on monthly competitions and custom events.
9.2. XP calculations are based on several factors, described below.
9.3. XP calculated by adding multipliers (listed below) to the initial CVSS base score number.
CVSS Base Score (v3.1)
10.1. The CVSS v3.1 is the primary indicator of severity and must be calculated using the official calculator: https://www.first.org/cvss/calculator/3.1
10.2. We are using only CVSS base score for all the calculations.
Active Install Count
11.1. Each range applies a multiplier to the final XP score
11.2. For premium products, active installs are estimated based on sales volume.
| Multiplier | Installs |
|---|---|
| ⚠️ x0.25 | < 1K installs (eligible only if component has at least 100 installs, a CVSS base score of 8.5 or higher, and can be exploited by unauthenticated users or users with Subscriber or Customer roles). |
| x0.5 | 1k+ active installs |
| x0.75 | 5K+ active installs |
| x1 | 10K+ active installs |
| x2 | 25K+ active installs |
| x3 | 50K+ active installs |
| x4 | 100K+ active installs |
| x5 | 200K+ active installs |
| x6 | 400K+ active installs |
| x7 | 800K+ active installs |
| x8 | 1.6 million+ active installs |
| x9 | 3.2 million+ active installs |
| x10 | 5 million+ active installs |
| x20 | WordPress core |
Privilege Requirement Coefficients
12.1. XP multipliers are applied based on the minimum privilege level required to exploit the vulnerability.
| Multiplier | Level of privilege |
|---|---|
| ⚠️ none | Editor, Author, Admin, Shop Manager, SuperAdmin (not accepted) |
| x0.75 | Contributor |
| x1 | Subscriber and Customer (WooCommerce) |
| x2 | Unauthenticated |
Vulnerability Type Coefficients
13.1. XP multipliers are applied based on vulnerability type.
| Multiplier | Vulnerability type |
|---|---|
| x3 | Remote Code Execution (RCE), Arbitrary file upload, deletion, Privilege escalation to Admin users, Arbitrary code execution |
| x2 | SQL Injection (SQLi), PHP Object Injection, Insecure Deserialization, Local File Inclusion (LFI) |
| x1.5 | Arbitrary file download/ |
| x0.25 | Cross-Site Request Forgery (CSRF) |
| x0.2 | Race Condition |
13.2. If a CSRF vulnerability leads to another vulnerability type (for example, CSRF leading to RCE), both multipliers apply.
13.3. If install or sales numbers cannot be reliably determined, Patchstack may use public data sources such as Google SERPs or PublicWWW.
13.4. XP is calculated monthly or within the timeframe of a specific custom event. Ongoing results appear on the leaderboard: https://patchstack.com/database/leaderboard
13.5. Final results are announced after all reports are validated (up to 10 business days if a backlog of reports requires more time for processing).
Disclosure
14.1. All vulnerabilities are publicly disclosed to the Patchstack Vulnerability Database according to the Patchstack Vulnerability Disclosure Policy.
14.2. Disclosure may be delayed until a fix is released and sufficient user adoption is observed.
14.3. Policy details: https://patchstack.com/patchstack-vulnerability-disclosure-policy/
14.4. Researchers must not disclose vulnerability details to any third parties before official public disclosure by Patchstack, which occurs when the vulnerability is publicly visible in the Patchstack Vulnerability Database and the assigned CVE is published.
14.5. To comply with EU CRA requirements all publications will be instant once the patch is released and validated (or released after validation).
14.6. The patch must be released as a dedicated update containing only security-related changes, with no additional code modifications. The version number or changelog description must clearly indicate that the release is a security fix.
Escalation Protocol
15.1. If a vendor does not respond within 14 days, Patchstack may proceed with public disclosure and may notify relevant security teams.
15.2. For components enrolled in Patchstack mVDP, disclosure timelines may be extended. Disclosure may be accelerated in cases of active exploitation or third-party disclosure.
15.3. If a vendor overlooks a report and the vulnerability is publicly disclosed, they may contact us at [email protected] to receive prompt assistance with vulnerability details, quick patch validation, and issue resolution.
Attribution
16.1. Public disclosures include researcher attribution using the provided name or nickname, and include ‘Patchstack Bug Bounty Program’ for program recognition.
16.2. CVE IDs are published in the global CVE database after disclosure with the same researcher data as in the Patchstack Vulnerability Database entry.
Monthly Competition
17.1. Monthly competitions run from the first day of the month at 00:00 UTC to the last day at 23:59 UTC.
17.2. Results are announced on the Patchstack Alliance Discord server.
17.3. Patchstack guarantees a minimum monthly bounty pool of $8,800, distributed based on final rankings.
17.4. Leaderboard: https://patchstack.com/database/leaderboard
Custom Events, Challenges
18.1. Custom events and CTF games are announced on Discord as well as their rules.
18.2. Custom challenges might be announced for extra bounties as a part of monthly competition.
Monthly Bounty Pool
19.1. Monthly bounties are distributed based on final leaderboard rankings as follows:
| Rank | Bounty |
|---|---|
| 1st place | $2,000 |
| 2nd place | $1,400 |
| 3rd place | $800 |
| 4th place | $600 |
| 5th place | $500 |
| 6th–10th place | $400 |
| 11th–15th place | $200 |
| 16th–19th place | $100 |
| 20th place + one random researcher | $50 |
19.2. A random bounty of $50 is awarded to one randomly selected researcher outside the top 20 rankings who has submitted at least one valid report with XP greater than 0.
19.3. High-impact vulnerabilities may be eligible for individual bounty rewards even if they do not qualify for the Zeroday program. Such cases are evaluated individually and must be discussed by opening a support ticket on the Patchstack Alliance Discord server in the #support channel.
XP Requirement
20.1. Bounties are paid only if the researcher has more than 0 XP for the respective month. If a researcher has 0 XP, no bounty will be paid, even if their leaderboard position qualifies for a reward. This rule also applies to random rewards.
Level Rewards
21.1. Researchers receive passive rewards for accumulating XP and progressing through levels. XP is earned through:
- Monthly competitions
- Custom events
- Patchstack Zeroday bounties
21.2. Levels reset to Level 1 at the beginning of each year. Updated level-related rules are announced after final monthly and yearly results are confirmed.
21.3. Starting from Level 1, researchers unlock additional rewards. These rewards are paid together with monthly bounties.
| Level | XP Required | Reward |
|---|---|---|
| Level 1 | 100 | $50 |
| Level 2 | 300 | $100 |
| Level 3 | 600 | $200 |
| Level 4 | 1,000 | $300 |
| Level 5 | 1,700 | $500 |
| Level 6 | 2,700 | $700 |
| Level 7 | 4,000 | $1,000 |
| Level 8 | 5,500 | $1,337 |
| Level 9 | 7,500 | $1,700 |
| Level 10 | 10,000 | $2,500 |
| Level 11 | 13,000 | $3,500 |
| Level 12 | 19,000 | $5,000 |
Zeroday Bounties
22.1. Patchstack offers Zeroday bounties for high-impact vulnerabilities on a case-by-case basis (bounty per vulnerability).
22.2. Zeroday rewards are paid together with monthly bounties.
22.3. Zeroday Bounties are:
| Active Installs | Unauthenticated | Subscriber / Customer |
|---|---|---|
| 1,000+ | $250 | $125 |
| 5,000+ | $400 | $200 |
| 10,000+ | $600 | $300 |
| 50,000+ | $1,400 | $700 |
| 100,000+ | $2,600 | $1,300 |
| 500,000+ | $4,900 | $2,450 |
| 1,000,000+ | $7,200 | $3,600 |
| 5,000,000+ | $14,400 | $7,200 |
| 15,000,000+ or WordPress Core (latest stable) | $33,000 | $16,500 |
22.4. Zeroday bounty requirements are
- To qualify for a Zeroday bounty, all of the following conditions must be met:
- The component is a free or premium WordPress plugin, theme, or WordPress core
(excluding components hosted in private, non-public repositories) - The vulnerability leads to a full site compromise, including the ability to upload and access a functional backdoor
- Exploitable by:
- Unauthenticated users, or
- Subscriber / Customer (WooCommerce) roles or lower
- The report includes a working exploit
- No prerequisites are required:
- Latest stable version
- Default settings
- Common environment
- No additional vulnerabilities required
- Exploitation does not require user interaction
- The vulnerability:
- Has not been reported elsewhere
- Is not previously known to the vendor
- Is not publicly disclosed
- The vulnerability is eligible under all other Patchstack program rules
- End-of-life components or components not updated in the last three years are not accepted
- Any required POP chain must exist in:
- The latest WordPress core version at the time of submission, or
- The affected component itself
- A single vulnerability affecting multiple components is treated as one issue, resulting in:
- One bounty payout
- One CVE ID
- Total active installs across all affected components used to calculate impact
22.5. Valid Zeroday vulnerabilities are not included into XP for the monthly competition or levels as they are rewarded separately.
22.6. XP points earned from Zero-day reports do not contribute to level progression (21. Level Rewards), as these reports are rewarded on a per-bounty, per-report basis.
Benefits of Participation
23.1. Participation provides opportunities to:
- Earn financial rewards
- Gain public recognition
- Receive CVE IDs for valid vulnerabilities
- Contribute to improving the security of the WordPress ecosystem and open-source in general
- Engage with the Patchstack research community
Membership
24.1. Membership in the Patchstack Alliance is open to individuals committed to improving WordPress security and complying with program requirements. Members receive access to Discord member-only channels.
24.2. Patchstack reserves the right to remove or ban any researcher from the public Discord channels dedicated to the Alliance community and the Bug Bounty program (including account deletion) in cases of inappropriate behavior, violations of applicable rules, or failure to adhere to the ethical standards of responsible vulnerability disclosure.
Payouts
25.1. Bounties are paid via PayPal by default. Researchers are responsible for managing their PayPal accounts, complying with all local tax obligations.
25.2. If a PayPal account is blocked, restricted, or frozen due to sanctions, Patchstack will attempt to complete payment within three months. After three months, unpaid bounties are returned to the bounty pool.
25.3. For bounties of $500 or higher we offer two more payment options:
- Bank transfer payments
- Cryptocurrency payments (Bitcoin or Ethereum) are processed using the exchange rate available at the time of payment. Patchstack is not responsible for any decrease in cryptocurrency value. By choosing this payout method, you acknowledge and accept all associated risks.
25.4. Invoice is mandatory despite the payment method, PayPal has its own integrated invoicing engine, for other payments you need to generate invoices on your own. All payments require an invoice. Payments are not processed without one.
25.5. Invoices must include:
- Full name
- Country and address
- Addressed to: Patchstack OÜ
- Payment purpose:
“Security research (your name or nickname used in the program)”
25.6. Payments are processed 30 days after final results are announced.
25.7. Additional payment guidance:
https://www.notion.so/patchstack/Patchstack-Alliance-payments-b6d63c55099e4f65b842bc5ce60de2d7
Communication
26.1. Official updates are shared via:
- Discord: https://discord.gg/rkE8yxtNmS
- X (Twitter): https://twitter.com/patchstackapp
- Facebook: https://www.facebook.com/patchstackapp
- LinkedIn: https://www.linkedin.com/company/patchstack/
26.2. Support is available via Discord support tickets on #support channel.
26.3. Edge case or sensitive matter of question - [email protected]
The post Patchstack Bug Bounty Guidelines & Rules (2026 edition) appeared first on Patchstack.
]]>