The post Is sovereign cloud all theatre? appeared first on Sendent.
]]>The technical architecture is real. The sovereignty claims require closer examination.
The question we should all be asking
Government agencies evaluating these offerings should start with two questions: Can this vendor access our data without our permission? Can foreign governments compel them to?
For infrastructure truly under European control, the answer to both questions is definitively no. For most offerings marketed as sovereign cloud, the answer is more complicated.
Under the CLOUD Act, location is irrelevant. Jurisdiction follows ownership. Even if data is hosted in Frankfurt or Paris, if it’s managed by a U.S.-based provider, it can legally be accessed by U.S. authorities. The US CLOUD Act of 2018 allows American authorities to compel US-based technology companies to provide requested data, regardless of where that data is stored globally.
Physical separation doesn’t change legal jurisdiction. While AWS claims there have been no access requests for data stored in the EU since 2020, this does not mean such requests cannot still come. While there is no automatic or unlimited access, on the basis of strict legal standards, it certainly can occur.
What sovereignty actually means
The European Commission published a Cloud Sovereignty Framework defining eight specific objectives with measurable criteria. The framework evaluates existence of legal, contractual, or technical channels through which non-EU authorities could compel access to data or systems.
Sovereignty means control over who can access data, under what circumstances, and subject to which legal framework. Marketing claims about EU data centers operated by EU staff don’t address whether the parent company can be compelled by foreign authorities to hand over access.
As long as a communications service provider is headquartered in the U.S., technical improvements and EU data residency do not change the fact that the CLOUD Act still applies. The jurisdictional problem remains regardless of where servers sit or who operates them day to day.
The Dutch example
The Netherlands demonstrates how procurement decisions based on sovereignty claims can backfire. Dutch public bodies had specifically chosen Solvinity to reduce their dependence on American firms and mitigate CLOUD Act risks. The acquisition of Solvinity by a US-based entity placed these systems squarely within the potential reach of US authorities.
Solvinity managed critical national infrastructure including the Netherlands’ citizen authentication system and government service portal. The acquisition exposed a structural flaw: deliberate choices for local providers offer no guarantee of long-term sovereignty when those providers can be acquired by US entities.
Sovereignty washing
American hyperscalers have recognized the market demand for sovereignty and now aggressively market sovereign cloud solutions, typically by placing datacenters on European soil or partnering with local operators. Critics call this sovereignty washing.
The term fits. When vendors market European data centers while remaining subject to extraterritorial legal reach, they’re selling compliance theater rather than actual control. Claims about control without compromise need a serious reality check. If a foreign government can compel data access, sovereignty is instantly compromised.
Government procurement officials evaluating these offerings need to distinguish technical features from legal guarantees. EU-based infrastructure operated by EU residents sounds reassuring until you ask which laws the parent company must obey.
What survives legal scrutiny
Real sovereign cloud infrastructure means the entity controlling access operates under European jurisdiction exclusively. Swedish cloud provider Safespring scores 86.25% on the EU Cloud Sovereignty Framework with 100% Swedish company ownership, Swedish governance, no dependency on non-European capital, and all employees as European citizens living in EU/EEA.
That level of independence is what sovereignty requires. The parent company, the operational entity, and the infrastructure all sit under European legal jurisdiction. No foreign authority can compel access without going through European legal processes.
Platforms like Nextcloud offer similar guarantees when deployed on infrastructure you control or on providers genuinely independent from non-EU jurisdiction. The difference between marketing sovereignty and actual sovereignty comes down to who can legally compel access.
The bridge that works
Government agencies don’t need to abandon familiar collaboration tools to achieve sovereignty. Solutions that connect Microsoft interfaces to Nextcloud deployments on European infrastructure let organizations maintain workflow continuity while moving data under their actual control.
European alternatives like Nextcloud, OVHcloud, and Collabora offer genuine sovereignty. For many organizations, distinguishing real alternatives from false promises has become increasingly difficult.
The technical work of bridging tools to sovereign infrastructure is straightforward. What matters is ensuring the infrastructure itself survives the two basic questions: Can the vendor access your data without permission? Can foreign governments compel them?
If the answer to either question is anything other than a clear no, the sovereignty claims don’t survive legal scrutiny. Everything else is marketing.
The post Is sovereign cloud all theatre? appeared first on Sendent.
]]>The post Europe spends more on IT, but where is the money going? appeared first on Sendent.
]]>61% of Western European CIOs now want to increase their use of local cloud providers, and around half say geopolitics will restrict their use of global providers. But wanting independence and paying for it are different things.
Feeding the same dependencies
Software will capture more than a third of Europe’s tech spend by 2029. Most of that money flows to the same platforms European organizations have been using for years. Microsoft 365 subscriptions. Google Workspace licenses. Salesforce seats. The vendors change their pricing, add AI features nobody asked for, and the bills go up accordingly.
Instead of investment, companies are feeding a recurring cost with a growth rate attached. Every euro spent on foreign subscriptions is a euro that leaves the European economy and doesn’t build anything you own.
The pattern is visible in every budget cycle: teams request more seats, platforms raise prices, features get bundled with services you don’t need. Finance approves it because switching would be worse. Nobody calls it what it actually is – paying rent on your own operations.
The alternative that actually builds something
Some European organizations are redirecting that spending differently. The European Commission is procuring up to €180 million of sovereign cloud services. SAP plans to invest €20 billion in its sovereign cloud. The German state of Schleswig-Holstein completed migration of 40,000 employee email accounts from Microsoft Exchange to Open-Xchange and Mozilla Thunderbird.
Businesses are now making strategic shifts that convert operational spending into infrastructure investment. Instead of paying Microsoft or AWS forever, you’re funding platforms that remain under European control and building capacity that serves European organizations first.
The European Commission’s Cloud Sovereignty Framework measures sovereignty across eight concrete objectives. That specificity matters. When procurement decisions get evaluated against actual sovereignty metrics rather than just feature checklists, spending patterns change.
What budget growth should buy
Rising IT budgets create room to rebalance spending from dependencies to capabilities. Government agencies implementing sovereign infrastructure are choosing where license payments go. Enterprises moving to European platforms are deciding what gets built with their money.
The technical work of connecting Microsoft tools to sovereign infrastructure like Nextcloud doesn’t eliminate software costs entirely. You’re still paying for something. But you’re paying to build infrastructure that strengthens European technical capacity instead of enriching foreign platforms that extract value while providing diminishing returns.
Spending on datacenters in Europe is set to grow 38.2 percent in 2025 to reach $83.6 billion. Some of that goes to AWS and Azure building European regions they ultimately control. Some goes to European providers building infrastructure that stays in European hands.
The difference compounds over time. Subscription payments reset every year. Infrastructure investment accumulates. Domestic capability grows. Technical expertise develops locally instead of concentrating in Seattle or Silicon Valley.
The question you should ask
Every budget cycle, somebody asks whether the organization is getting value from its software spending. The better question is whether that spending builds anything the organization owns.
Platforms that treat European markets as revenue sources while keeping operational control elsewhere aren’t partners. They’re landlords. Rising IT budgets shouldn’t just mean bigger rent checks.
Organizations converting license fees into infrastructure payments are making a different calculation. They’re asking what percentage of their IT spending actually builds capability they control. What portion develops European technical capacity. What amount stays in the regional economy instead of flowing to foreign shareholders.
The global sovereign cloud market is projected to reach over $250 billion this decade. That market exists because organizations are tired of paying for dependencies that look permanent.
Budget growth creates opportunities. Whether those opportunities go toward feeding existing dependencies or building strategic capabilities depends on what organizations choose to buy. The spending increase is already happening. The only question is where the money goes.
The post Europe spends more on IT, but where is the money going? appeared first on Sendent.
]]>The post Why few actually migrate off Microsoft appeared first on Sendent.
]]>The real reason: They underestimated what they were actually asking their organization to do.
The lock-in nobody talks about
Microsoft’s real competitive advantage can’t be found in its feature set. It’s that your colleague in accounting has used Outlook for fifteen years and can process invoices in her sleep. Your sales team’s entire workflow assumes SharePoint’s specific quirks. Ten thousand tiny learned behaviors add up to institutional muscle memory.
Try to replace that, and you’re asking everyone to relearn how to do their job while still hitting their targets. Training sessions help at the margins. What really happens is productivity drops for months, support tickets multiply, and the people who were most efficient in the old system become the most frustrated in the new one.
Migration projects fail because organizations can’t absorb that much disruption at once without something breaking. The technical capability of the new platform rarely matters.
The interface is the moat
User adoption is the actual barrier in migration projects. Microsoft has spent decades making sure Outlook feels like Outlook, and that Excel works the way people expect Excel to work. That consistency across versions and deployments is worth more than any individual feature.
When you tell someone they need to learn a completely new interface to do the same work they did yesterday, you’re asking them to surrender expertise they’ve built over the years. People resist that for good reasons.
Decoupling the problem
Today, you can separate where data lives from how people interact with it.
The technical architecture exists to let organizations keep using Microsoft’s collaboration interfaces while storing everything on infrastructure they control. Outlook still looks like Outlook. Teams still feels like Teams. The actual data sits on servers under European jurisdiction.
This approach doesn’t solve every sovereignty problem. You’re still running Microsoft software, still subject to licensing terms, still dependent on their roadmap decisions. But you’re not asking thousands of employees to rebuild their workflows from scratch while you’re trying to establish data independence.
What actually works
The organizations making progress on digital sovereignty aren’t the ones announcing dramatic platform switches. They’re the ones quietly decoupling their data layer from their application layer. Running familiar tools on top of the infrastructure they control.
It’s less heroic than a full migration. Doesn’t make for exciting interviews about breaking free from big tech. But it’s what you can actually execute without your organization falling apart during the transition.
Governments won’t tell every ministry to stop using Microsoft products overnight. Businesses moving to sovereign infrastructure aren’t handing employees a completely foreign collaboration suite and hoping for the best. They’re finding ways to achieve the control they need without the productivity collapse that kills most migration attempts.
The real choice
Perfect sovereignty would mean building everything yourself and controlling every layer of the stack. It would also mean your organization spends the next two years unable to function properly while people learn new systems.
The practical version recognizes that independence has gradations. Moving your data to infrastructure you control while keeping interfaces people already know how to use isn’t a compromise. It’s recognizing that user adoption is a technical constraint as real as any other.
Microsoft’s moat is the accumulated expertise of millions of people who know how to get work done using their tools. You don’t defeat that by asking everyone to start over. You defeat it by building underneath it.
The post Why few actually migrate off Microsoft appeared first on Sendent.
]]>The post Greenland, tariffs, and your company’s cloud strategy appeared first on Sendent.
]]>The US president floated tariffs against its allies (Denmark, Norway, Sweden, France, Germany, the United Kingdom, the Netherlands, and Finland) if Denmark won’t discuss selling Greenland to the United States. The proposal itself is unlikely to succeed, but what it reveals about the current geopolitical climate matters for organizations running critical infrastructure on American platforms.
For European organizations running critical operations through Microsoft 365 or Google Workspace, this should feel uncomfortably familiar. Your collaboration infrastructure, your institutional memory, and your daily operations all sit on servers ultimately subject to US jurisdiction. Not just US law, which is predictable enough, but US political pressure applied in directions you can’t anticipate.
The pattern we keep ignoring
We’ve seen this pattern before. The Privacy Shield framework collapsed when courts recognized that US intelligence access to European data wasn’t theoretical. CLOUD Act provisions give US authorities reach into data stored anywhere in the world if a US company controls it. These weren’t bugs in the system. They were features that only became problems when someone decided to use them.
Digital sovereignty used to sound like bureaucratic anxiety dressed up as policy. Something for compliance officers to worry about while the rest of us got work done on platforms that actually functioned well. But sovereignty is just another word for control over things that matter. When political winds shift, and your communications infrastructure becomes subject to leverage you didn’t agree to, “where does our data actually live” stops being an abstract question.
Beyond compliance theater
The shift is already visible. Government ministries are moving to domestic providers like Nextcloud. Organizations are reconsidering their cloud strategies. Not because American platforms work poorly, but because the ground underneath them keeps moving in ways that have nothing to do with technology.
This is where the conversation about European alternatives changes character. Solutions that connect Outlook and Teams to infrastructure like Nextcloud give organizations actual choices about where their data lives. These tools weren’t built because European developers couldn’t figure out how to make a decent cloud platform. They exist because operational continuity shouldn’t depend on the stability of transatlantic relations.
Organizations gain the freedom to choose their infrastructure strategy without abandoning the collaboration tools their teams already know. They can migrate entirely to sovereign infrastructure when that makes sense. They can adopt hybrid approaches that protect sensitive data while keeping other workloads on platforms optimized for public-facing services. They can make these decisions based on their actual security requirements rather than accepting whatever terms their current vendor offers.
The ability to safely migrate to sovereign infrastructure or use a hybrid approach transforms infrastructure decisions from locked-in commitments into strategic choices you can revisit as circumstances change. That calculation looks different now than it did five years ago. Probably looks different than it will five years from now.
The technical part is easy
Microsoft’s protocols are well-documented. Exchange can sync to other systems. Teams can coexist with platforms that keep data inside EU borders. The harder question is strategic: at what point does convenience become dependency, and dependency become vulnerability?
We’re willing to wager that Greenland isn’t going to become US territory. But the threat was real enough to make. That’s the point. When essential infrastructure sits under someone else’s ultimate authority, you’re always one policy shift away from discovering that what you thought was a technology decision was actually a geopolitical one.
Who controls the off switch
European organizations are waking up to this in different ways and at different speeds. Some are moving deliberately to platforms they control. Others are building hybrid approaches that keep sensitive operations on domestic infrastructure while using US platforms for less critical work. The common thread is recognizing that where your data lives isn’t just about latency or compliance checkboxes.
It’s about whether you’re comfortable with someone else holding the off switch.
The post Greenland, tariffs, and your company’s cloud strategy appeared first on Sendent.
]]>The post EU Data Act comes into force: What you need to know appeared first on Sendent.
]]>What the EU Data Act actually does
The Data Act establishes new rules for data access, cloud switching, and interoperability across the EU. It applies to any company operating connected products or cloud services in Europe, regardless of where they’re based.
The regulation tackles several key areas. Users gain new rights to access data generated by their connected devices and share it with third parties. Public sector bodies can access private sector data during emergencies like floods or wildfires. Most significantly for business operations, the Act eliminates unfair contractual terms in data sharing agreements and phases out cloud switching charges entirely by January 2027.
For cloud services specifically, the changes are substantial. Providers must offer seamless switching between platforms, maintain transparent registries of their data structures, and ensure compatibility with open standards. The days of proprietary lock-in strategies are numbered, at least in European markets.
The strategic implications
The traditional approach of accepting vendor dependencies in exchange for convenience is becoming a regulatory liability.
Your current data strategy likely assumes that switching costs and integration complexity will remain constant. The Data Act changes that calculation. By 2027, moving between cloud providers must be free and technically straightforward. This creates new possibilities for multi-cloud strategies, vendor negotiations, and infrastructure flexibility.
The regulation also emphasizes data portability and interoperability as core requirements rather than nice-to-have features. Organizations that have built their systems around open standards and self-hosted solutions will find compliance easier than those dependent on proprietary platforms.
Building a Data Act-ready strategy
Compliance starts with understanding your current data dependencies. Map where your business data lives, how it’s formatted, and what it would take to move it. Many organizations discover they have less control than they assumed.
Review your existing contracts with cloud providers and software vendors. The Data Act prohibits many common contractual terms that limit data portability or impose unreasonable switching barriers. New contracts must meet fair, reasonable, and non-discriminatory standards.
Consider your product roadmap if you develop connected devices or digital services. Products launched after September 2026 must be designed with data sharing capabilities built in.
The hybrid solution advantage
The regulatory landscape increasingly favors organizations that maintain control over their data while preserving operational efficiency. This is where hybrid approaches become strategically valuable.
Consider maintaining familiar productivity tools while hosting core data on platforms you control. With Sendent, teams can continue using Microsoft applications for collaboration while ensuring that data remains on self-hosted Nextcloud infrastructure that meets Data Act requirements.
This approach addresses multiple challenges simultaneously. You maintain workflow continuity, achieve regulatory compliance, and build resilience against future platform changes or pricing adjustments.
The post EU Data Act comes into force: What you need to know appeared first on Sendent.
]]>The post Why Chat Control threatens Europe’s digital independence appeared first on Sendent.
]]>What makes this moment particularly dangerous is how close the legislation stands to passage. Unlike the European Parliament, where democratic debate typically prevails, the Council of member states operates on qualified majority voting that could override citizen opposition through pure mathematical calculation.
The numbers tell a troubling story:
- 15 member states supporting the proposal
- Only 3 member states opposing
- 9 member states still undecided
- Final positions due by 12 September 2025
- Crucial Council vote scheduled for 14 October 2025
Proponents of Chat Control need 55% of member states (15 out of 27) representing 65% of the EU population. They already have the required number of countries. If Germany shifts from undecided to supporting, the population threshold would be crossed, making passage nearly inevitable regardless of how smaller nations vote.
Under this legislation, every communication would be automatically scanned without suspicion or consent. Even encrypted messages would be subject to this digital dragnet. The scope is breathtaking: your family WhatsApp groups, business communications, private photos, medical consultations conducted via messaging apps. Politicians and military personnel receive exemptions under “professional secrecy” rules, but ordinary citizens and businesses do not.

The stakes extend far beyond individual privacy. Europe’s economic competitiveness, democratic institutions, and autonomy all depend on maintaining robust digital security. Chat Control threatens to undermine the very foundation of that security.
Why is Chat Control dangerous?
Chat Control would fundamentally alter how digital communications work across Europe. The legislation would require weakening or breaking end-to-end encryption, the protection that currently shields everything from banking transactions to medical records from unauthorized access. This encryption serves as Europe’s digital immune system, protecting critical infrastructure from cyberattacks and espionage.
Automated scanning systems cannot examine encrypted content without first breaking that encryption or installing backdoors that bypass security protections entirely. These vulnerabilities cannot be limited to specific purposes or users. Once created, they represent permanent weak points that hostile actors can exploit.
European businesses rely on strong encryption for competitive advantage. Financial institutions use it to protect transactions worth trillions of euros. Healthcare systems depend on it to secure patient data. Government communications require it for national security. Chat Control would compromise all these systems simultaneously.
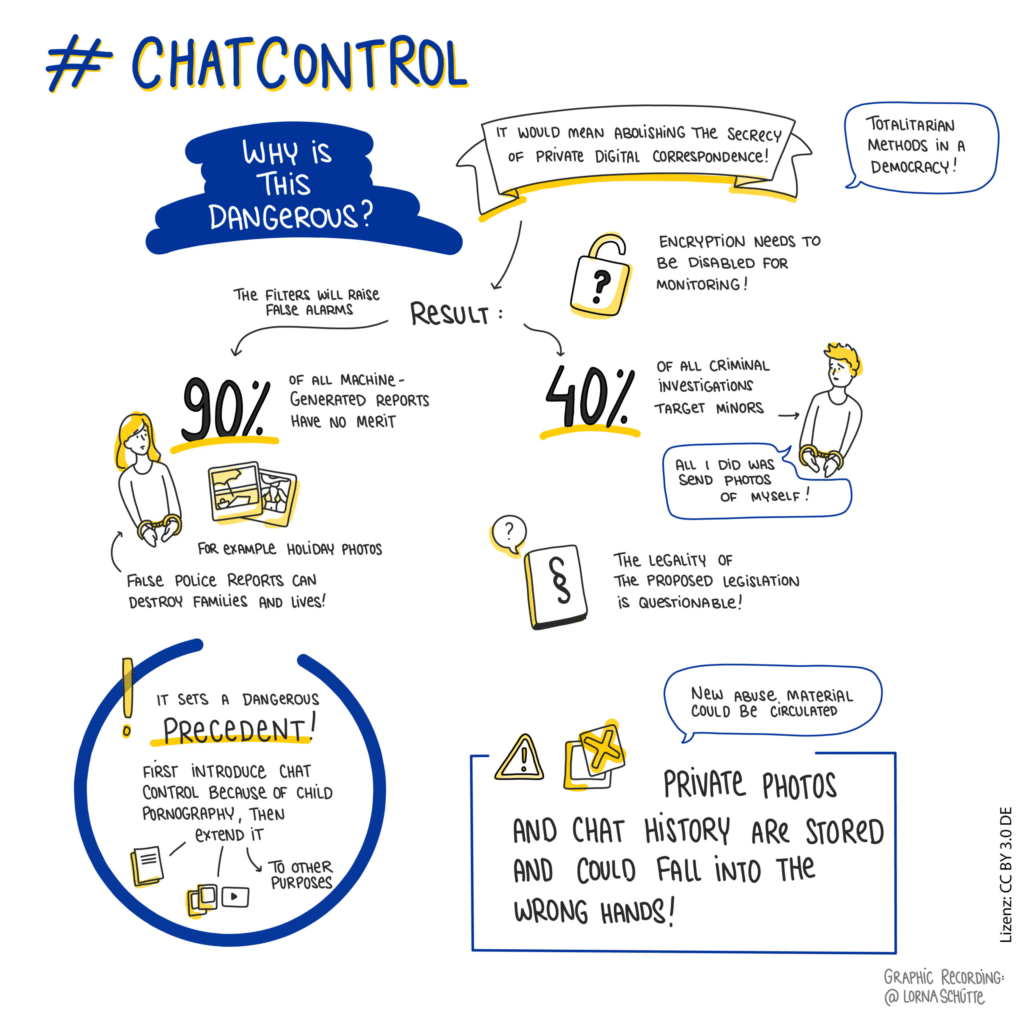
The proposal creates a paradox that exposes Europe’s digital naivety. In the name of protecting children from online predators, European lawmakers would create new attack vectors that make every European citizen, business, and institution more vulnerable to criminals, foreign intelligence services, and cybercriminals. The cure becomes worse than the disease.
How does Chat Control undermine our digital sovereignty?
Chat Control represents a fundamental surrender of European digital independence. By mandating the weakening of encryption, Europe would voluntarily create surveillance infrastructure that foreign powers could exploit for espionage and influence operations. China, Russia, and other authoritarian states would gain unprecedented access to European communications through the very backdoors Europe creates for itself.
The legislation also forces Europe into dependence on American technology companies for its surveillance apparatus. Current voluntary scanning programs already rely heavily on systems developed by US Big Tech firms. Patrick Breyer, a former German MEP who has emerged as Chat Control’s most prominent opponent, has filed lawsuits specifically challenging this American technological colonization of European digital infrastructure.
Breyer’s legal challenges targeted what he calls “chat control 1.0” – the existing voluntary scanning programs that major platforms already employ. The current legislative proposal represents “chat control 2.0,” which would mandate and expand these surveillance systems across all digital communications in Europe. His argument: Why should European communications be subject to scanning systems controlled by foreign corporations operating under foreign legal frameworks?
The irony runs deeper. While European officials demand mass surveillance of their citizens’ communications, they have exempted themselves through “professional secrecy” rules. EU politicians retain their privacy while ordinary Europeans lose theirs. This double standard reveals the true nature of the proposal: a system designed to monitor subjects, not to protect citizens.
Help stop Chat Control
Europe faces a choice between imported surveillance models and genuinely European approaches to digital security and child protection. Strong encryption represents a European competitive advantage in an increasingly hostile digital environment. Rather than weakening these protections, Europe should be strengthening them while developing privacy-preserving alternatives for legitimate law enforcement needs.
Child protection experts and organizations, including the United Nations, have warned that mass surveillance fails to prevent abuse and actually makes children less safe by weakening security for everyone. European innovation could focus on targeted, warrant-based investigative tools that protect both children and privacy rights.
When we started Sendent, one of our core beliefs was that privacy isn’t negotiable. Chat Control represents the antithesis of this principle, treating privacy as expendable in pursuit of security theater that experts warn won’t protect children.

Europe can choose to remain a global leader in privacy protection and digital rights, or it can surrender these principles to foreign surveillance technologies and authoritarian precedents.
With many member states still undecided and only three firmly opposing, the outcome remains uncertain. Citizens in supporting or undecided countries have until September 12 to influence their governments’ final positions. The future of European digital independence may depend on whether ordinary Europeans make their voices heard before it’s too late.
Take action now
The fight for European digital sovereignty requires immediate citizen engagement. With the September 12 deadline approaching, digital outreach offers the fastest way to reach the broadest audience.
Contact your government directly
- Email your interior ministry, justice ministry, and digital affairs ministry demanding they withdraw support for Chat Control
- Contact your country’s permanent representation to the EU with your concerns
- If your country supports the legislation, demand they explain why they’re willing to weaken European encryption
- Reference the joint letter from European children’s rights and digital rights organizations opposing the proposal
Amplify the message
- Share information about Chat Control and the October 14 vote on social media
- Contact local and national media to bring attention to this issue
- Explain to friends and family how this affects their daily communications
- Form local action groups to coordinate opposition efforts
If your country is among the 15 supporters or 9 undecided nations, your voice matters most. Germany’s position could be decisive; if it shifts from undecided to supporting, the population threshold for passage would likely be met.
The window for action closes on September 12. European digital sovereignty hangs in the balance.
The post Why Chat Control threatens Europe’s digital independence appeared first on Sendent.
]]>The post How to localize data without sacrificing productivity appeared first on Sendent.
]]>The agencies getting this right have discovered a different approach: deploying sovereignty-first platforms that maintain full integration with the collaborative tools government workers already depend on.
If your agency is still treating data sovereignty as a barrier to effective digital collaboration, you’re missing opportunities to deliver both compliance and performance. There’s a strategic approach that gives you complete data control without forcing your teams to abandon the productivity tools that keep government operations running smoothly.
Why data sovereignty efforts end in productivity loss
Most government localization projects begin with the best intentions but collapse under the weight of integration challenges. Agencies identify their sensitive datasets (e.g. citizen records, inter-agency communications, classified documents) and mandate that everything moves to domestic infrastructure immediately.
The problems surface within weeks:
- Broken collaboration workflows: Staff can no longer share files seamlessly between the new sovereign platform and Microsoft Teams meetings
- Email integration failures: Outlook attachments can’t connect to the localized storage system, forcing manual workarounds
- Cross-agency communication breakdowns: Document workflows spanning multiple departments fail when different agencies can’t access shared resources through existing tools
- Dual-stack management nightmares: IT departments juggle completely separate technology environments—sovereign platforms for sensitive data, cloud tools for everything else
Staff members inevitably resort to dangerous workarounds, like downloading sensitive files to personal devices just to share them through familiar platforms.
The fundamental problem lies with implementations that treat localization as a complete separation from existing digital workflows rather than an integrated upgrade to them.
The intelligent integration approach
The intelligent integration approach
Government data localization strategies don’t start with infrastructure; they start with workflow preservation. Rather than forcing agencies to choose between sovereignty and productivity, modern integration platforms create a bridge that delivers both.
Sendent represents this new approach: a platform that transforms how government agencies handle sensitive data by making sovereign storage work seamlessly within existing Microsoft 365 workflows. Instead of requiring agencies to abandon familiar tools or compromise on data control, Sendent creates secure pathways that keep sensitive information within government-controlled infrastructure while maintaining the collaborative experiences government workers depend on.
What this means in practice:
- Staff continue collaborating through Teams and Outlook exactly as before
- All sensitive documents automatically remain within government-controlled infrastructure
- Zero workflow disruption or retraining required
- Complete data sovereignty without productivity sacrifices
- Intelligent routing ensures sensitive data never leaves approved boundaries
The technical architecture prioritizes user experience over technical complexity. Government workers interact with the same Microsoft tools they’ve always used, but behind the scenes, Sendent ensures that sensitive documents, communications, and data remain within designated sovereign boundaries. The platform acts as an intelligent traffic controller, seamlessly routing data to appropriate storage locations based on classification levels and compliance requirements.
Building sustainable data sovereignty
Effective data sovereignty doesn’t require choosing between security and productivity. The key is implementing solutions that enhance existing workflows while providing complete control over sensitive information.
Focus on platforms that integrate naturally with your current technology investments rather than requiring wholesale replacement of proven tools. The most successful government sovereignty initiatives build on existing user competencies and workflow patterns while adding the security and compliance capabilities that government operations require.
The technology and expertise to make this transition successfully are available today. Government agencies ready to explore how intelligent integration can enhance rather than complicate their digital operations have proven pathways to achieve both sovereignty and performance goals.
The post How to localize data without sacrificing productivity appeared first on Sendent.
]]>The post Building consumer-first tech the EU way appeared first on Sendent.
]]>- European tech companies prioritize privacy, sustainability, and customer trust over rapid scaling and data monetization
- This approach creates higher customer lifetime value, regulatory resilience, and genuine competitive moats through trust
- Global consumer attitudes are shifting toward European values: privacy over convenience, sustainability over novelty
- Companies built on surveillance capitalism face expensive retrofitting as privacy regulations spread worldwide
- The “slower” European model positions companies for long-term success as customer trust becomes a primary competitive advantage
Silicon Valley perfected a formula: collect user data, optimize for engagement, scale fast, and monetize everything. It’s produced some of the world’s most valuable companies, but as users worldwide grow skeptical of surveillance capitalism and throwaway technology, a different approach is gaining ground.
Instead of treating users as products, they’re creating sustainable businesses that prioritize privacy, transparency, and long-term customer relationships. What initially looks like a competitive disadvantage actually positions these companies for the next phase of consumer technology.
Privacy and sustainability as a business model
When European companies build consumer technology, privacy becomes the starting point for product design. This stems partly from regulatory requirements like GDPR, but more importantly from understanding that surveillance-based business models are ultimately unsustainable.
Take Proton, the Swiss company behind ProtonMail and ProtonVPN. Instead of offering free services funded by advertising and data collection, they built a subscription business where customers pay directly for privacy and security. When customers pay for a service, they become stakeholders rather than products.
Fairphone, a Dutch company, builds smartphones designed for repairability and longevity. Their devices cost more upfront and lack some cutting-edge features, but they last longer and create less electronic waste. As consumers become more aware of the environmental cost of constant device upgrades, Fairphone’s approach looks increasingly prescient.
Adyen built their payment processing business on transparency and fair pricing rather than hidden fees. Their straightforward approach attracted merchants tired of opaque pricing structures.
The trust advantage
Building privacy-first, sustainable technology creates genuine customer trust. This trust translates into business advantages that compound over time. Customers recommend trusted products, stick with companies longer, and pay premium prices for products that align with their values.
Consumer attitudes are also shifting worldwide. Young people increasingly value privacy over convenience, sustainability over novelty, and authentic company values over marketing promises. These preferences align naturally with the European approach.
Companies that built these principles into their foundation can expand globally seamlessly, while competitors face expensive rebuilding to meet evolving consumer expectations.
The compound advantage
The European approach initially appears slower and more expensive than Silicon Valley’s growth-at-all-costs model. But these investments compound over time. Privacy-first products don’t face expensive compliance retrofitting. Sustainable design reduces long-term support costs. Transparent business models generate predictable revenue.
The next decade will be defined by the backlash against surveillance capitalism. European companies have spent years building exactly the capabilities this new era demands. What looked like competitive disadvantages are becoming the foundation for sustainable growth where customer trust determines long-term success.
Building for the long game
The next decade of consumer technology will be defined by the backlash against surveillance capitalism and disposable technology. Users worldwide are demanding products that respect their privacy, last longer, and come from companies they can trust.
European technology companies have spent years building exactly these capabilities. What looked like competitive disadvantages in an era of rapid scaling and data monetization are becoming the foundation for sustainable growth in an era where customer trust and regulatory compliance determine long-term success.
The organizations that thrive in this environment will be those that can build genuine relationships with customers who choose to stay because they want to, not because switching costs are too high or because they’re trapped in an ecosystem designed to prevent choice.
The European model offers a blueprint for building technology that serves users rather than exploiting them. In a world increasingly skeptical of surveillance capitalism, that approach goes beyond ethics to become more profitable.
To get started with Sendent and Nextcloud, explore our guide.
The post Building consumer-first tech the EU way appeared first on Sendent.
]]>The post Why smart organizations are mixing open source with proprietary software (and you should too) appeared first on Sendent.
]]>The organizations that are thriving today have figured out how to capture the genuine advantages of open source while keeping the proprietary tools that actually make business sense. They recognize that the real world is more complex than the either-or choice that dominated earlier conversations about software strategy.
If you’re still thinking in terms of “all open source” or “all proprietary,” you’re missing out on a more effective approach that can give your organization better security, more flexibility, and lower long-term costs without the massive disruption that comes with completely switching your entire technology stack.
The open source advantage
Here’s what open source software actually gives you that proprietary software fundamentally cannot, no matter what the sales team promises.
You can see exactly what the software is doing. When you use proprietary software, you’re essentially trusting the vendor when they say their product is secure, efficient, or compliant with your needs. With open source, you or your technical team can actually look at the code and verify these claims. More importantly, thousands of other developers around the world are also looking at that same code, finding problems, and fixing them. This collective scrutiny often makes open source software more secure than proprietary alternatives, not less.
You control your own destiny. Proprietary software vendors can change their licensing terms, get acquired by competitors, or simply discontinue products that your business depends on. Remember when Adobe moved everything to subscriptions? With open source, these business decisions can’t hold your operations hostage. You have the code, and you can continue using it regardless of what happens to the original company behind it.
You can modify it when you need to. Business requirements change, and sometimes you need software to do something slightly different than what it was originally designed for. With proprietary software, you’re stuck submitting feature requests and hoping they get prioritized. With open source, you can make the changes yourself or hire someone to do it for you.
But here’s the reality check: not every organization has the technical expertise to take advantage of these benefits. Looking at code is only useful if you have people who can understand what they’re seeing. And managing your own software infrastructure requires skills and resources that many organizations simply don’t have or can’t justify developing internally.
This is why the “just go all open source” advice often fails in practice, even when the theoretical benefits are real.
Why all-or-nothing doesn’t work
Switching entirely to open source sounds appealing until you start calculating what it actually takes. A complete migration can require years of testing, staff training, and system integration work. Most organizations can’t afford to undertake this across all their systems simultaneously while keeping their day-to-day operations running smoothly.
Then, consider what happens when you replace a proprietary customer relationship management system with an open source alternative. Your sales team needs training on the new interface. Your IT department has to migrate years of customer data. Your integrations with accounting software, email marketing tools, and support systems all need to be rebuilt and tested. Meanwhile, you’re responsible for maintaining and securing the software yourself instead of relying on vendor support.
The math often doesn’t work out. Small and medium-sized businesses especially find themselves spending more on internal IT resources than they were paying for software licenses. Even large organizations with substantial technical teams discover that managing a completely open source infrastructure requires specialized skills they don’t have in-house.
The all-proprietary approach has its own problems. Vendor lock-in becomes expensive over time, and you’re always vulnerable to licensing changes, acquisitions, or discontinued products. The smart move is finding the right balance.
The smart hybrid strategy
The winning approach focuses open source efforts where they deliver the biggest impact with the least disruption.
Start with infrastructure. Operating systems, web servers, databases, and networking tools are ideal candidates for open source adoption. These foundational systems benefit most from transparency and community oversight, and switching them out typically requires less end-user training than customer-facing applications.
Keep specialized tools proprietary when it makes sense. If your accounting team loves their current software and it integrates perfectly with your bank, don’t force a change just to check an ideological box. Similarly, if a proprietary tool offers compliance features or industry-specific functionality that would take years to replicate in open source alternatives, stick with what works.
Evaluate based on business impact, not philosophy. The question shouldn’t be “is this open source?” but rather “does this choice give us better security, lower costs, or more flexibility than the alternative?” Sometimes the answer favors open source, sometimes it doesn’t.
Getting started
The most successful organizations have moved beyond the old open source versus proprietary debate. They’re building technology strategies that capture the transparency and flexibility benefits of open source while maintaining the specialized functionality and support that certain proprietary tools provide.
Getting started doesn’t require a complete overhaul. Begin by identifying one or two infrastructure components where open source alternatives are mature and well-supported. Build internal expertise gradually, and expand your open source footprint as your team’s capabilities grow.
The future belongs to organizations that can adapt quickly to changing circumstances. A balanced approach to software gives you more options when vendors change direction, when security threats emerge, or when business requirements evolve. You’re not betting everything on one philosophy or one set of vendors.
If you want to learn how to take advantage of platform flexibility, contact us for a free demo.
The post Why smart organizations are mixing open source with proprietary software (and you should too) appeared first on Sendent.
]]>The post Where EU tech leads despite lower investment appeared first on Sendent.
]]>European tech companies receive a fraction of the venture funding that flows to Silicon Valley. In 2023, US venture capital investment reached $170.6 billion, while European startups received $52 billion. Yet despite this funding disparity, European tech has developed world-leading expertise in several critical areas.
The difference isn’t accidental. It’s strategic advantage born from necessity.
Innovation through regulation
European companies didn’t choose to become experts in privacy engineering and regulatory compliance: they had to. Operating under GDPR, strict data protection laws, and complex cross-border regulations forced European developers to solve problems their American counterparts could largely ignore.
This regulatory pressure created something unexpected: technical expertise in the exact domains now becoming essential as global priorities shift toward privacy, security, and digital sovereignty.
While US companies built fast and moved quickly, European companies built carefully and moved compliantly. That difference now matters more than ever.
Where Europe leads
Privacy by design engineering
European companies architected systems around privacy requirements from the ground up. These solutions go beyond compliance checkboxes to fundamental system design that protects user data while maintaining functionality.
Companies like Nextcloud, Proton, and Tutanota developed sophisticated privacy-preserving technologies years before “privacy-first” became a Silicon Valley marketing term. Their solutions handle complex scenarios like cross-border data transfers, granular consent management, and zero-knowledge architectures because European regulations demanded it.
Sovereign cloud infrastructure
European cloud providers had to solve sovereignty challenges long before most American companies understood what digital sovereignty meant. Providers like OVHcloud, Scaleway, and regional specialists developed technologies for keeping data within specific jurisdictions while maintaining cloud flexibility.
European security providers excel at identity management across complex organizational structures, fine-grained access controls, and audit trails that satisfy multiple regulatory frameworks simultaneously.
B2B security solutions
European B2B security companies developed approaches that assume hostile regulatory environments, complex compliance requirements, and multiple stakeholder interests. This created solutions that are inherently more robust than those designed for simpler regulatory contexts.
European security providers excel at identity management across complex organizational structures, fine-grained access controls, and audit trails that satisfy multiple regulatory frameworks simultaneously.
Regulatory technology (RegTech)
Perhaps nowhere is European technical leadership more obvious than in regulatory technology. European RegTech companies understand compliance not as an afterthought but as a core system requirement that drives technical architecture decisions.
These companies built solutions for navigating GDPR, financial services regulations, healthcare compliance, and cross-border data governance long before similar challenges became pressing concerns in other markets.
What’s our advantage?
This regulatory-driven innovation created unexpected competitive advantages as global priorities shifted. What seemed like European disadvantages — complex regulations, fragmented markets, compliance overhead — actually forced the development of sophisticated solutions to fundamental problems.
Technical depth over speed
While US companies optimized for rapid growth and user acquisition, European companies optimized for sustainability, compliance, and long-term viability. This created deeper technical expertise in complex problem domains.
Multi-stakeholder design
European companies learned to build systems that satisfy multiple stakeholders with conflicting interests: users, regulators, governments, and business requirements. This complexity created more sophisticated architectural approaches.
Cross-border expertise
Managing technology across multiple European jurisdictions required solving problems that most American companies haven’t encountered. European tech companies became experts at managing complexity that’s now becoming universal.
Why this matters now
Global technology priorities are shifting toward exactly the areas where European companies have the deepest expertise. Digital sovereignty concerns are intensifying worldwide. Privacy regulations are expanding globally. Security requirements are becoming more sophisticated.
The “post-surveillance economy” emerging from growing privacy awareness, regulatory pressure, and geopolitical tensions favors companies with deep expertise in the technical challenges Europe has been solving for years.
Regulatory expansion
Privacy regulations similar to GDPR are being adopted worldwide. Companies that learned to navigate complex European requirements have technical and operational advantages in these new markets.
Sovereignty demands
Governments worldwide are demanding more control over their digital infrastructure. European companies that solved sovereignty challenges for EU requirements now have exportable expertise.
Security priorities
As cyber threats become more sophisticated and consequential, the robust security approaches developed under European regulatory pressure become more valuable globally.
Beyond funding gaps
The venture funding disparity between Europe and the US often dominates discussions of tech competitiveness. But funding advantages don’t automatically translate to technical superiority in complex domains.
European companies may have raised less money, but they’ve solved harder problems. They’ve developed expertise in areas that are becoming strategically critical as technology priorities evolve beyond pure growth metrics.
Quality over quantity
European tech companies often focus on sustainable business models rather than venture-funded growth at any cost. This creates different technical priorities and often more robust solutions.
Problem-solving focus
Regulatory constraints forced European companies to become excellent problem solvers rather than just market expanders. This technical depth creates competitive advantages in complex domains.
The path forward
European tech’s regulatory-driven expertise positions it well for a world where privacy, security, and sovereignty are becoming universal concerns rather than regional peculiarities.
The companies that learned to build sophisticated solutions under European regulatory pressure now have technical advantages as similar requirements spread globally. What seemed like constraints became capabilities.
This doesn’t mean European tech companies should ignore growth and investment opportunities. But it does mean recognizing that European tech has developed world-leading expertise in the domains that matter most for the next phase of digital infrastructure development.
The future belongs to companies that can balance innovation with responsibility, growth with sustainability, and technical capability with regulatory sophistication. European tech companies have been practicing this balance for years.
The post Where EU tech leads despite lower investment appeared first on Sendent.
]]>