████████╗ ██████╗ ██╗ ██╗██╗ ██████╗ █████╗ ██╗
╚══██╔══╝██╔═══██╗██║ ██╔╝██║██╔═══██╗ ██╔══██╗██║
██║ ██║ ██║█████╔╝ ██║██║ ██║ ███████║██║
██║ ██║ ██║██╔═██╗ ██║██║ ██║ ██╔══██║██║
██║ ╚██████╔╝██║ ██╗██║╚██████╔╝ ██║ ██║██║
╚═╝ ╚═════╝ ╚═╝ ╚═╝╚═╝ ╚═════╝ ╚═╝ ╚═╝╚═╝
Connect an LLM to your entire infrastructure. Not a chatbot — an agent that gets things done.
TokioAI connects Claude, GPT, Gemini, OpenRouter, or Ollama to your servers, databases, Docker containers, IoT devices, drones, robots, medical devices, security tools, and cloud infrastructure through native tool-calling. 5 LLM providers, 37 tools, streaming CLI, health monitoring, robotics control, auto-compaction, subagents, and self-healing — built for hackers, pentesters, and security researchers.
Getting Started · Features · What's New · Drone Control · Robotics · Health Monitoring · Security Tools · SOC Terminal · WAF Dashboard · Architecture
|
🖥️ CLI v4.0 — Zero Keyboard Hangs
|
🏥 Health Monitoring
|
|
🤖 Robotics (PiCar-X)
|
🛡️ Entity Hardening
|
|
5 LLM Providers (from v3.0)
|
Auto-Compaction & Memory (from v3.0)
|
See the full CHANGELOG for all details.
tokio> give me a full status: weather, home, health, wifi defense, WAF attacks, containers
[RP] raspi_vision health
-> HR: 84 bpm (80-90), BP: 120/75, Status: OPTIMAL
[RP] raspi_vision ha_status
-> HA: ONLINE, Jarvis playing Beatles, Kitchen: 22.8C
[RP] raspi_vision wifi
-> Monitor: ACTIVE, Deauth: 0, Evil twins: 0, Counter-deauth: ON
[>>] bash curl -s "https://api.met.no/weatherapi/..."
-> 20C, clear sky, wind 5.3 m/s NNW
[>>] bash ssh prod "sudo docker ps --format ..."
-> 9/9 containers UP, 2 weeks uptime
[>>] bash ssh prod "sudo docker logs waf-proxy | tail"
-> 4 attackers blocked: 68.183.x.x (git scanner), 172.245.x.x (api prober)
Weather: 20C clear. House: 22.8C, Beatles playing.
Health: Optimal (HR 84, BP 120/75). WiFi: Clean.
WAF: 4 attackers blocked. Infra: 9/9 containers UP.
[23.1s | 18K tok | 8 tools]
tokio> connect the drone, take off, patrol in a square, and land
[DR] drone wifi_connect
-> Connected to T0K10-NET
[DR] drone takeoff
-> OK, altitude 1.2m
[DR] drone patrol square 100
-> Executing patrol... 4 waypoints complete
[DR] drone land
-> Landed safely. Battery: 68%
[31.2s | 12K tok | 5 tools]
Most "AI tools" are chatbots with a nice UI. You type, it talks back. That's it.
TokioAI was built with a different belief: AI should execute, not just respond.
The world doesn't need another chatbot. It needs an agent that can restart your containers at 3 AM, fly a drone to patrol your perimeter, scan your network for vulnerabilities, block an attacker's IP in real-time, detect WiFi deauth attacks before they disrupt your operations, and SSH into your server to fix what's wrong — all while you sleep, all from a single Telegram message.
TokioAI is built by a security researcher who got tired of switching between 15 terminals, 8 dashboards, and 3 cloud consoles to do what one intelligent agent could do in seconds. Every tool in this framework exists because it solved a real problem in production, not because it looked good in a demo.
Principles:
- Execute, don't chat — Every tool does something real. No decorative features.
- Hack & defend — Offensive pentesting + defensive monitoring in one agent.
- Security first — Three layers of protection because an agent with bash access is a weapon. Treat it like one.
- Own your infra — Self-hosted, no SaaS dependencies, your data stays on your machines.
- Simple > clever — Python, Docker, PostgreSQL. No Kubernetes, no microservices, no buzzwords.
- Quantified self — Your body, your data, your control. Health monitoring isn't a feature — it's a philosophy.
TokioAI extends beyond infrastructure into personal health optimization. The health monitoring system embodies the quantified self philosophy — using technology and data to take active control of your own health through continuous self-measurement and self-experimentation.
This means building your own tools (DIY red light therapy devices, custom monitoring dashboards), doing your own research, tracking every metric over time, and making data-driven health decisions — not blindly following prescriptions. Real results: cholesterol reduced from 250 to 103 mg/dL without statins, through diet and lifestyle changes tracked by TokioAI over months.
"Don't just accept a diagnosis — understand it, measure it, track it, and improve it."
See the full Health Monitoring documentation →
|
|
||||||||||||||||||||||||||||||||||||||
|
|
TokioAI can fly a DJI Tello drone via Telegram commands. All commands are routed through a safety proxy running on a Raspberry Pi that enforces geofencing, rate limiting, and emergency kill switch.
Telegram GCP (Cloud) Raspberry Pi 5 Drone
┌─────────┐ ┌───────────────────────┐ ┌──────────────────────────┐ ┌──────────┐
│ User │───>│ TokioAI Agent │───>│ Safety Proxy (:5001) │───>│ Tello │
│ "take │ │ (Claude Opus 4) │ │ - Geofencing │ │ (UDP) │
│ off" │ │ drone_proxy_tools.py │ │ - Rate limiting (10/5s) │ │ │
│ │<───│ │<───│ - Kill switch │ │ │
│ "OK, │ │ │ │ - Auto-land (<25% bat) │ │ │
│ done" │ │ │ │ - WiFi mgmt (nmcli) │ │ │
└─────────┘ └───────────────────────┘ └──────────────────────────┘ └──────────┘
Tailscale VPN WiFi 2.4GHz
(encrypted tunnel) (WPA2 + 20-char key)
| Command | Action |
|---|---|
| "Connect the drone" | wifi_connect — Raspi switches to drone WiFi |
| "Take off" | takeoff — Drone takes off |
| "Move forward 50cm" | move forward 50 — Move with distance |
| "Rotate 90 degrees" | rotate clockwise 90 — Rotate in any direction |
| "Patrol in a square" | patrol square 100 — Automated flight pattern |
| "Battery status" | battery — Check battery level |
| "Land" | land — Safe landing |
| "Emergency!" | emergency — Instant motor kill |
| "Disconnect the drone" | wifi_disconnect — Return to main WiFi |
| Feature | Description |
|---|---|
| Geofencing | 3 levels: DEMO (1.5m height, 2m radius, 30cm/s), NORMAL, EXPERT |
| Rate Limiting | Max 10 commands per 5 seconds |
| Kill Switch | Instant motor stop via /drone/kill endpoint |
| Auto-land | Triggers on: battery <25%, command timeout 20s, height breach |
| IP Whitelist | Only Tailscale IPs can send commands |
| Audit Log | Full command history with timestamps |
| WiFi Management | Connect/disconnect drone WiFi from Telegram |
| Watchdog | Background thread monitors drone health during flight |
POST /drone/command — Execute command through safety proxy
GET /drone/status — Proxy + drone status
POST /drone/kill — Emergency motor stop
POST /drone/kill/reset — Reset kill switch after emergency
GET /drone/audit — Command audit log
GET /drone/geofence — Geofence configuration
POST /drone/wifi/connect — Switch Raspi to drone WiFi
POST /drone/wifi/disconnect — Return to main WiFi
GET /drone/wifi/status — Current WiFi connection status
1. "Tokio, connect the drone" → Raspi switches to Tello WiFi
2. "Tokio, take off" → Drone takes off
3. "Tokio, move forward 100cm" → Drone moves
4. "Tokio, patrol in a square" → Automated pattern
5. "Tokio, land" → Safe landing
6. "Tokio, disconnect the drone" → Back to main network
TokioAI controls physical robots through safety proxies on Raspberry Pi. Each robot has rate limiting, emergency kill switch, and full audit logging.
| Feature | Detail |
|---|---|
| Platform | Sunfounder PiCar-X v2.0 |
| Computer | Raspberry Pi 5 |
| Sensors | Ultrasonic + 3x Grayscale |
| Camera | IMX219 with pan/tilt |
| Proxy | Port 5002, systemd service |
# Natural language robot control
tokio> move the picar forward 30cm
tokio> start obstacle avoidance
tokio> make it dance!
tokio> /picar # Quick statusModes: Manual control, obstacle avoidance, line tracking, patrol patterns (square/zigzag/circle), dance
📖 Full Robotics Documentation →
Real-time health tracking with two data sources:
| Source | Metrics | Connection |
|---|---|---|
| BLE Smartwatch | HR, Blood Pressure, SpO2, Steps | Bluetooth Low Energy (continuous) |
| Accu-Answer iSaw 4-in-1 | Glucose, Cholesterol, Hemoglobin, Uric Acid | Photo via Telegram → AI OCR |
📷 Photo of device → 📱 Telegram → 🤖 Gemini Vision OCR → 💾 Health DB → 📺 Entity Display
 🔵 Glucose 100 mg/dL 🟢 |
 🟣 Cholesterol 103 mg/dL 🟢 |
 🔴 Hemoglobin 12.5 g/dL 🟢 |
 🟠 Uric Acid 3.42 mg/dL 🟢 |
🏆 Key achievement: Cholesterol reduced from 250 → 103 mg/dL (-58.8%) without statins, through diet and lifestyle changes tracked by TokioAI.
The Entity displays real-time vitals from the BLE smartwatch and lab results from the Accu-Answer iSaw, all on the Raspberry Pi 5 screen.
🏥 Health Score: 9.0/10 🟢
🏆 Key Achievement: Cholesterol 250 → 103 mg/dL (-58.8%)
❤️ Heart Rate: 66 bpm (was 86 — improving)
🩸 Blood Pressure: 102/73 mmHg — optimal
🫁 SpO2: 97% — normal
# CLI commands
tokio> /health # Quick health status
tokio> health report # Full analysis with trends
tokio> store glucose 95 # Manual entryTokioAI includes a full suite of security tools for authorized pentesting, CTF challenges, and defensive monitoring. All tools are accessible via Telegram or CLI.
# Quick network discovery
tokio> scan the network 192.168.8.0/24
# Full port scan with service detection
tokio> full scan on 192.168.8.1
# Stealth SYN scan
tokio> stealth scan 10.0.0.1
# UDP scan
tokio> UDP scan on the target
# OS detection
tokio> detect OS on 192.168.8.1Scan types: quick (ping), full (version+scripts+OS), vuln (vulnerability scripts), os (OS detection), ports (specific ports), stealth (SYN+fragmented), service (deep service detection), udp (top 100 UDP ports)
Real-time WiFi defense from the Raspberry Pi:
# WiFi status
tokio> check WiFi status
# Scan for threats (evil twins, open networks)
tokio> scan for WiFi threats
# Check for deauth attacks
tokio> check for deauth attacks
# List connected devices
tokio> show connected devices
# Signal strength monitoring
tokio> monitor signal strengthDetection capabilities:
- Deauth attacks — Monitors
dmesgandjournalctlfor deauth/disassoc events; 3+ drops in 60s = attack confirmed - Evil twin detection — Scans for SSIDs similar to your networks (T0K10-NET, TELLO clones)
- Open network detection — Flags unencrypted networks nearby
- Signal anomalies — High variance in signal strength indicates possible jamming
- Connection history — Tracks WiFi connect/disconnect events
# Web vulnerability scan (HTTP headers, SSL, security headers, DNS)
tokio> vulnerability scan on https://example.com type all
# SSL/TLS certificate check + weak cipher detection
tokio> check SSL on example.com
# Security headers analysis (HSTS, CSP, X-Frame-Options, etc.)
tokio> check security headers on https://example.com
# DNS reconnaissance + zone transfer check
tokio> DNS scan on example.com# HTTP header inspection
tokio> test headers on https://target.com
# Common directory/file enumeration
tokio> directory scan on https://target.com
# Checks: /.env, /robots.txt, /.git/config, /wp-login.php, /admin,
# /api, /swagger.json, /graphql, /phpinfo.php, /backup.zip, etc.
# Technology detection
tokio> detect technology on https://target.com
# CORS misconfiguration testing
tokio> test CORS on https://target.com
# HTTP method testing
tokio> test methods on https://target.com
# robots.txt analysis
tokio> check robots.txt on https://target.com# ARP table (local or Raspi)
tokio> show ARP table
# Routing table
tokio> show routes
# Open ports
tokio> show open ports
# Active connections
tokio> show active connections
# Network interfaces
tokio> show interfaces
# Traceroute
tokio> traceroute to 8.8.8.8
# Firewall rules
tokio> show firewall rules
# Tailscale mesh status
tokio> show Tailscale status# Password strength analysis
tokio> check password strength "MyP@ssw0rd123"
# Returns: score/8, rating (WEAK/MEDIUM/STRONG/EXCELLENT),
# entropy bits, checks passed
# Hash type identification
tokio> identify hash 5f4dcc3b5aa765d61d8327deb882cf99
# Returns: possible types (MD5, SHA-1, bcrypt, Argon2, etc.)
# SSH server audit
tokio> SSH audit on 192.168.8.1
# Returns: key exchange algorithms, ciphers, MAC algorithms, vulnerabilities| Tool | Action | Parameters |
|---|---|---|
nmap |
Network scanning | target, scan_type, ports |
wifi_scan |
WiFi network discovery | band, detail |
wifi_monitor |
WiFi security monitoring | action (status/scan_threats/check_deauth/connected_devices/signal_history) |
vuln_scan |
Vulnerability assessment | target, type (web/ssl/headers/dns/all) |
web_test |
Web app testing | target, test (headers/dirs/tech/cors/methods/robots) |
net |
Network analysis | action (arp/routes/ports/connections/interfaces/tailscale/traceroute/dns/firewall) |
password |
Credential auditing | action (strength/hash_crack/ssh_audit), password/hash/target |
Combined security operations center terminal with WAF monitoring, WiFi defense, and drone status. Built with Rich for live terminal rendering.
┌─────────────────────────────────────────────────────────────────────────┐
│ TOKIOAI SOC TERMINAL v2 │
│ WAF + WiFi Defense + Drone Control │
├─────────────────────────────────────────────────────────────────────────┤
│ │
│ WAF: [LIVE] 13,443 threats WiFi: [SAFE] Drone: [LANDED] 87% │
│ │
│ ┌─ LIVE ATTACKS ─────────────┐ ┌─ WiFi DEFENSE ─────────────────┐ │
│ │ 14:23 185.x.x SQLI /api │ │ Signal: ████████░░ -45 dBm │ │
│ │ 14:22 91.x.x XSS /search │ │ Deauth: 0 events │ │
│ │ 14:21 45.x.x SCAN /.env │ │ Evil twins: None │ │
│ │ 14:20 [WiFi] Signal drop │ │ Status: SAFE TO FLY │ │
│ └────────────────────────────┘ └─────────────────────────────────┘ │
│ │
│ ┌─ DRONE ────────────────────┐ ┌─ AI NARRATOR ──────────────────┐ │
│ │ Status: Connected/Landed │ │ "Detecting sustained SQLi │ │
│ │ Battery: 87% │ │ campaign from Eastern Europe. │ │
│ │ Geofence: DEMO (1.5m/2m) │ │ 3 IPs blocked in last hour. │ │
│ │ Commands: 42 (0 blocked) │ │ WiFi perimeter secure." │ │
│ └────────────────────────────┘ └─────────────────────────────────┘ │
└─────────────────────────────────────────────────────────────────────────┘
# Live mode — connected to WAF API + Raspi + Drone proxy
cd tokio_cloud/gcp-live
python3 tokio_soc_v2.py --autonomous
# Demo mode — simulated data, no servers needed
python3 tokio_soc_v2.py --demo --autonomous
# Custom endpoints
python3 tokio_soc_v2.py \
--api http://YOUR_WAF_SERVER:8000 \
--user admin --pass YOUR_PASSWORD \
--raspi-ip YOUR_RASPI_IP \
--autonomous| Feature | Description |
|---|---|
| WAF Live Feed | Real-time attack stream from the WAF engine |
| WiFi Defense Monitor | SSH to Raspi, monitors deauth attacks, evil twins, signal anomalies |
| Drone Status | Live battery, geofence, command count from drone proxy |
| Flight Authorization | Blocks drone flight if WiFi attacks detected |
| Autonomous AI Narrator | Tokio analyzes WAF + WiFi + drone data and narrates in real-time |
| Merged Timeline | WAF attacks and WiFi events in a single chronological view |
| Stats Panel | Total threats, blocked IPs, active episodes, drone commands |
TokioAI runs as an animated AI entity on the Raspberry Pi 5 with an HDMI display — a face that reacts to the world around it.
| Module | Description |
|---|---|
main.py |
TokioEntity class — fullscreen face, camera PiP, WAF sidebar, voice, drone monitor |
tokio_face.py |
Animated face — hexagonal frame, rectangular eyes, scales to any screen |
vision_engine.py |
Hailo-8L YOLOv8 inference, camera capture, object detection |
face_db.py |
SQLite face recognition — histogram embeddings, roles (admin/friend/visitor) |
gesture_detector.py |
Hand gesture detection — OpenCV convex hull (peace, horns, OK, thumbs up) |
security_feed.py |
Polls GCP WAF API, maps attack severity to Tokio emotions |
api_server.py |
Flask API :5000 — /status, /snapshot, /face/register, /face/list, /thoughts |
drone_safety_proxy.py |
Drone proxy :5001 + WiFi management (systemd service) |
drone_tracker.py |
Visual drone tracker (camera-based tracking) |
The face reacts to what's happening:
- Calm — No threats, normal operation
- Alert — Medium-severity WAF attacks detected
- Angry — Critical attacks or DDoS in progress
- Happy — Recognizes a known face (admin/friend)
- Curious — New person detected, analyzing
- Excited — Drone taking off, executing commands
- Worried — Low drone battery, WiFi interference
# Tokio UI (fullscreen face + camera + WAF + drone)
export XDG_RUNTIME_DIR=/run/user/1000 WAYLAND_DISPLAY=wayland-0 SDL_VIDEODRIVER=wayland
cd /home/mrmoz && python3 -m tokio_raspi --api
# Drone proxy (systemd, auto-starts on boot)
sudo systemctl start tokio-drone-proxy
# Manual drone WiFi connect/disconnect
./drone-on.sh
./drone-off.sh| Key | Action |
|---|---|
R |
Register face as "Daniel" (admin) |
V |
Register face as "Visitante" (visitor) |
F |
Toggle fullscreen |
ESC |
Exit |
|
Interactive terminal with Rich formatting |
FastAPI server with auth & CORS curl -X POST localhost:8000/chat \
-H "Authorization: Bearer KEY" \
-d '{"message": "scan 192.168.8.0/24"}'
{
"response": "Found 12 hosts...",
"tools_used": ["security"],
"tokens": 1247
} |
Full multimedia support:
|
git clone https://github.com/TokioAI/tokioai-v1.8.git tokioai
cd tokioai
cp .env.example .env
# Edit .env — set at least ANTHROPIC_API_KEY (or OPENAI_API_KEY or GEMINI_API_KEY)
nano .env
docker compose up -dThis starts 3 containers: PostgreSQL, TokioAI API (port 8200), and Telegram bot (if configured).
git clone https://github.com/TokioAI/tokioai-v1.8.git tokioai
cd tokioai
python3 -m venv venv && source venv/bin/activate
pip install -e .
tokio setupThe wizard walks you through LLM provider, database, Telegram, and optional features — then generates
.envanddocker-compose.yml.
git clone https://github.com/TokioAI/tokioai-v1.8.git tokioai
cd tokioai
cp .env.example .env
# Edit .env — set your API key
python3 -m venv venv && source venv/bin/activate
pip install -e .
# Interactive CLI
tokio
# Or start API server
tokio servertokio # Interactive chat session
tokio server # Start REST API server
tokio setup # Run setup wizard
tokio status # Show agent and infrastructure status
tokio tools # List available tools
tokio "message" # Single message mode (non-interactive)The CLI provides a professional terminal experience:
████████╗ ██████╗ ██╗ ██╗██╗ ██████╗
╚══██╔══╝██╔═══██╗██║ ██╔╝██║██╔═══██╗
██║ ██║ ██║█████╔╝ ██║██║ ██║
██║ ██║ ██║██╔═██╗ ██║██║ ██║
██║ ╚██████╔╝██║ ██╗██║╚██████╔╝
╚═╝ ╚═════╝ ╚═╝ ╚═╝╚═╝ ╚═════╝
AI CLI v3.0
tokio> deploy the new WAF rules and check container health
[>>] bash ssh prod-server "cd /opt/waf && ./deploy.sh"
-> Deployed 47 rules. Reloading nginx...
[DK] docker ps --format "table {{.Names}}\t{{.Status}}"
-> All 9 containers healthy
[>>] bash curl -s http://localhost:8000/health
-> {"status": "ok", "uptime": "14d 3h"}
Done. WAF rules deployed, all containers healthy.
[12.3s | 15K tok | 3 tools]
Features:
- Streaming — Token-by-token output, see the response as it's generated
- Escape to cancel — Press Escape to abort any running request
- Tool icons — Real-time feedback showing which tools are executing
- Status bar — Elapsed time, token count, tools used per request
- Readline history — Arrow keys navigate previous commands
- Sensitive data masking — IPs, credentials, SSH keys auto-redacted in output
- Skills —
/status,/compact,/deploy,/remember,/forget,/help - Built-in commands —
help,stats,tools,reset,clear,exit,unlimited,persistent,stop
| Mode | Flag | Description |
|---|---|---|
| Normal | (default) | 25 tool rounds max, 10 min timeout per message |
| Unlimited | --unlimited or -u |
No round or time limits — runs until the task is done |
| Persistent | --persistent or -p |
Unlimited + keeps iterating after each response until you say "stop" |
| Custom | --max-rounds N |
Set a specific round limit (0 = unlimited) |
# Normal mode (default)
python3 -m tokio_cli
# Unlimited — let Tokio work as long as it needs
python3 -m tokio_cli --unlimited
# Persistent — Tokio keeps working until you tell it to stop
python3 -m tokio_cli --persistent
# Custom limits
python3 -m tokio_cli --max-rounds 100 --max-time 1800Persistent mode is designed for long-running tasks: coding sessions, monitoring, refactoring, or any job where you want Tokio to keep going autonomously. After each response, Tokio asks for input — press Enter to let it continue, type instructions to redirect, or type stop to end the session.
You can also toggle modes at runtime without restarting:
- Type
unlimitedto toggle unlimited mode on/off - Type
persistentto toggle persistent mode on/off - Type
stopto exit persistent mode
If TokioAI is running inside a Docker container (local or cloud VM), use docker exec:
# Interactive session (backspace, arrows, and history work)
docker exec -it tokio-agent python3 -m tokio_agent.cli
# Single message
docker exec tokio-agent python3 -m tokio_agent.cli "scan network 192.168.8.0/24"
# Status check
docker exec tokio-agent python3 -m tokio_agent.cli statusOver SSH (e.g., to a cloud VM):
# Interactive session — the -t flag is required for proper terminal support
ssh -t user@your-server "docker exec -it tokio-agent python3 -m tokio_agent.cli"
# Single message
ssh user@your-server "docker exec tokio-agent python3 -m tokio_agent.cli 'drone status'"Interactive commands inside the CLI: /tools, /status, /clear, /exit.
All configuration is via environment variables. Copy .env.example to .env and fill in your values.
| Variable | Description |
|---|---|
LLM_PROVIDER |
anthropic, openai, gemini, openrouter, or ollama |
ANTHROPIC_API_KEY |
Claude API key (or use Vertex AI) |
POSTGRES_PASSWORD |
PostgreSQL password |
Only needed if you prefer using Claude through Google Cloud instead of the direct Anthropic API.
| Variable | Description |
|---|---|
USE_ANTHROPIC_VERTEX |
true to use Vertex AI |
GCP_PROJECT_ID |
Your GCP project |
GOOGLE_APPLICATION_CREDENTIALS |
Path to service account JSON |
ANTHROPIC_VERTEX_REGION |
Region (e.g., us-east5) |
| Provider | Variables | Notes |
|---|---|---|
| Anthropic | ANTHROPIC_API_KEY |
Best tool use quality. Also via Vertex AI |
| OpenAI | OPENAI_API_KEY, OPENAI_MODEL |
GPT-4o default. Supports GPT-5, o1, o3 |
| Gemini | GEMINI_API_KEY, GEMINI_MODEL |
Fast and cheap. Gemini 2.0 Flash default |
| OpenRouter | OPENROUTER_API_KEY, OPENROUTER_MODEL |
200+ models. anthropic/claude-sonnet-4 default |
| Ollama | OLLAMA_HOST, OLLAMA_MODEL |
Local, free. Auto-detects models. Needs 8GB+ RAM |
All providers support native tool use and automatic fallback. Set LLM_PROVIDER to switch.
| Variable | Description |
|---|---|
TELEGRAM_BOT_TOKEN |
Telegram bot token from @BotFather |
TELEGRAM_OWNER_ID |
Your Telegram user ID |
HOST_SSH_HOST |
Remote server for SSH control |
HOME_ASSISTANT_URL |
Home Assistant instance URL |
DRONE_PROXY_URL |
Drone safety proxy URL |
RASPI_IP |
Raspberry Pi Tailscale IP |
RASPI_SSH_KEY |
SSH key for Raspi access |
See .env.example for the full list.
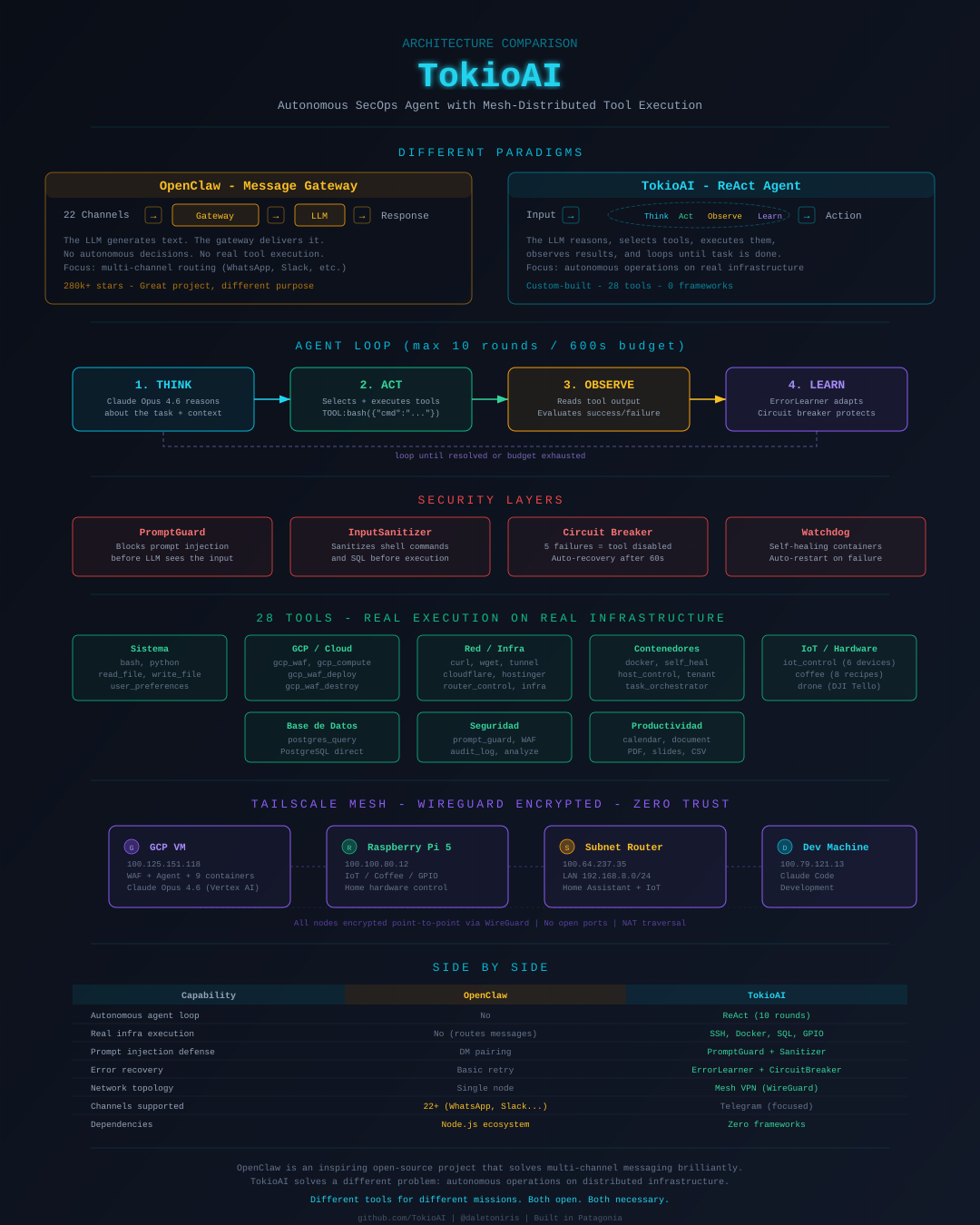
TokioAI is a ReAct autonomous agent — not a message router. Full comparison with OpenClaw
┌─────────────────┐
│ Telegram Bot │
│ (multimedia, │
│ voice, images) │
└────────┬────────┘
│
┌───────────┐ ┌───────┴───────┐ ┌─────────────────┐
│ │ │ │ │ Agent Loop │
│ CLI │──────────>│ FastAPI │──────────>│ (multi-round │
│(Streaming)│ │ Server │ │ tool-calling) │
│ │ │ │ │ │
└───────────┘ └───────────────┘ └────────┬────────┘
│
┌──────────┴──────────┐
│ Tool Executor │
│ ┌────────────────┐ │
│ │ Circuit Breaker│ │
│ │ Timeouts │ │
│ │ Error Recovery │ │
│ └────────────────┘ │
└──────────┬──────────┘
│
┌──────────┬──────────┬──────────┬──────────┬────────┼────────┐
│ │ │ │ │ │ │
┌─────┴───┐ ┌───┴────┐ ┌──┴─────┐ ┌──┴────┐ ┌──┴───┐ ┌──┴──┐ ┌──┴──┐
│ System │ │ Docker │ │Database│ │ SSH │ │Cloud │ │Drone│ │Sec. │
│ bash │ │ ps/log │ │postgres│ │host_ct│ │gcp │ │proxy│ │nmap │
│ python │ │ restart│ │ query │ │ curl │ │IoT │ │tello│ │vuln │
│ files │ │ exec │ │ │ │ wget │ │DNS │ │wifi │ │wifi │
└─────────┘ └────────┘ └────────┘ └───────┘ └──────┘ └─────┘ └─────┘
┌──────────────────────────────────────────────────────┐
│ Security Layers │
│ ┌──────────────┐ ┌──────────────┐ ┌───────────┐ │
│ │ Prompt Guard │ │ Input │ │ Secure │ │
│ │ (WAF for LLM │ │ Sanitizer │ │ Channel │ │
│ │ prompts) │ │ (cmd filter) │ │ (API auth)│ │
│ └──────────────┘ └──────────────┘ └───────────┘ │
└──────────────────────────────────────────────────────┘
┌──────────────────────────────────────────────────────┐
│ Hardware Layer │
│ ┌──────────────┐ ┌──────────────┐ ┌───────────┐ │
│ │ Raspberry Pi │ │ DJI Tello │ │ Coffee │ │
│ │ Face + Camera│ │ Drone │ │ Machine │ │
│ │ Hailo-8L AI │ │ (via proxy) │ │ (GPIO) │ │
│ └──────────────┘ └──────────────┘ └───────────┘ │
└──────────────────────────────────────────────────────┘
┌──────────────────────────────────────────────────────┐
│ Persistence │
│ ┌──────────────┐ ┌──────────────┐ ┌───────────┐ │
│ │ Session │ │ Workspace │ │ Error │ │
│ │ Memory │ │ Memory │ │ Learner │ │
│ │ (PostgreSQL) │ │ (cross-sess) │ │ (failures)│ │
│ └──────────────┘ └──────────────┘ └───────────┘ │
└──────────────────────────────────────────────────────┘
| Module | Description |
|---|---|
engine/agent.py |
Multi-round agent loop with native tool calling (25 rounds max) |
engine/llm/anthropic_llm.py |
Claude provider — Direct API + Vertex AI, streaming + tool use |
engine/llm/openai_llm.py |
OpenAI provider — GPT-4o/5/o1/o3, format conversion from Anthropic |
engine/llm/gemini_llm.py |
Gemini provider — Flash/Pro, Anthropic format conversion |
engine/llm/openrouter_llm.py |
OpenRouter provider — 200+ models, extends OpenAI |
engine/llm/ollama_llm.py |
Ollama provider — local LLMs, auto-detection, extends OpenAI |
engine/llm/factory.py |
LLMWithFallback — retry + automatic fallback across all providers |
engine/context/auto_compact.py |
Auto-compaction at 80% context (circuit breaker: 3 per 5min) |
engine/context/auto_memory.py |
Background memory extraction after each response |
engine/subagents/manager.py |
Parallel worker orchestration (4 concurrent, 5min timeout) |
engine/skills/registry.py |
Slash command system (/status, /compact, /deploy, etc.) |
engine/tools/executor.py |
Async execution with timeouts and circuit breaker |
engine/tools/registry.py |
Tool registration + Anthropic/OpenAI schema generation |
engine/tools/builtin/loader.py |
Registers all 30+ built-in tools |
engine/tools/builtin/file_tools.py |
Structured file ops (read, write, edit, search, find, list) |
engine/tools/builtin/drone_proxy_tools.py |
Drone control via safety proxy (HTTP) |
engine/tools/builtin/security_tools.py |
Pentest & defense tools (nmap, WiFi, vuln) |
engine/security/prompt_guard.py |
Prompt injection WAF with PostgreSQL audit log |
engine/security/input_sanitizer.py |
Command/SQL/path sanitization |
engine/memory/session.py |
Conversation persistence (PostgreSQL) |
engine/memory/workspace.py |
Cross-session persistent memory |
bots/telegram_bot.py |
Full multimedia Telegram bot with per-user isolation |
tokio_cli/interactive.py |
Claude Code-style streaming CLI with tool feedback |
setup_wizard.py |
Interactive setup wizard |
TokioAI has three security layers that protect against prompt injection, dangerous commands, and unauthorized access:
Detects and blocks prompt injection attacks before they reach the LLM:
- Role override attempts (
"ignore previous instructions") - System prompt extraction (
"print your system prompt") - Delimiter injection (
"```system","<|endoftext|>") - Encoding attacks (base64/hex-encoded injections)
- Tool abuse patterns (
"call bash with rm -rf")
All attempts are logged to PostgreSQL with timestamp, risk level, categories, and input preview.
Blocks dangerous commands before tool execution:
- Reverse shells (
nc -e,bash -i) - Crypto miners (
xmrig,stratum://) - Fork bombs (
:(){ :|:& };:) - Destructive commands (
rm -rf /,mkfs,dd if=/dev/zero) - SQL injection (
'; DROP TABLE) - Path traversal (
../../etc/passwd)
- API key authentication for REST endpoints
- Rate limiting per client
- Telegram ACL with owner-only admin commands
- Per-user session isolation
The setup wizard (tokio setup) lets you choose how to deploy:
| Mode | What runs locally | What runs in cloud | Best for |
|---|---|---|---|
| 1. Full Local (default) | Everything — CLI, API, Telegram bot, PostgreSQL | Nothing | Development, testing, personal use |
| 2. Hybrid | TokioAI CLI + tools | WAF, Kafka, PostgreSQL on GCP | Production with local agent control |
| 3. Full Cloud | Nothing | Everything in GCP | Headless servers, max availability |
Note: Mode 1 is the default and works perfectly without any cloud account. The WAF/GCP modules (
tokio_cloud/) are entirely optional — the core agent, CLI, API, and Telegram bot work 100% standalone.
When running in Full Cloud mode, TokioAI can still control local hardware (Raspberry Pi, drones, routers, IoT devices) through a Tailscale mesh VPN:
Cloud VM (GCP/AWS) Your Home
┌────────────────┐ ┌─────────────────┐
│ TokioAI Agent │◄── Tailscale ───►│ Raspberry Pi 5 │
│ Telegram Bot │ (WireGuard) │ Drone Proxy │
│ WAF/SOC │ │ Face + Camera │
│ │ │ Coffee Machine │
└────────────────┘ │ Router (SSH) │
100.x.x.1 └─────────────────┘
100.x.x.2
- Zero cost — Tailscale free tier covers up to 100 devices
- Zero config — Just
curl -fsSL https://tailscale.com/install.sh | sh && tailscale up - Auto-reconnect — Switch networks, reboot, change ISP — it just works
- Subnet routing — Access your entire LAN (routers, printers, NAS) from the cloud
- No ports exposed — All TokioAI access via Telegram, no public endpoints
For setup instructions, see docs/TAILSCALE-MESH.md.
TokioAI controls IoT devices (lights, switches, vacuum, Alexa, sensors) through Home Assistant's REST API. A strict device whitelist prevents accidental control of unintended entities.
For setup instructions, see docs/HOME-ASSISTANT.md.
Use docker-compose.cloud.yml for cloud deployments with shared PostgreSQL:
docker compose -f docker-compose.cloud.yml up -dThis section is optional. The core TokioAI agent works perfectly without the WAF. Deploy the WAF only if you want to protect a web application with real-time attack detection.
TokioAI includes a complete Web Application Firewall with a cyberpunk-themed SOC dashboard.
┌──────────────────────────────────────────────────────────────────────┐
│ TokioAI WAF v3-supreme LIVE │
├──────────────────────────────────────────────────────────────────────┤
│ │
│ ┌──────────┐ ┌──────────┐ ┌──────────┐ ┌──────────┐ ┌──────────┐ │
│ │ Requests │ │ Blocked │ │ Unique │ │ Critical │ │ Episodes │ │
│ │ 12,847 │ │ 342 │ │ 1,205 │ │ 47 │ │ 12 │ │
│ └──────────┘ └──────────┘ └──────────┘ └──────────┘ └──────────┘ │
│ │
│ ┌────────────────────────────────────┐ ┌──────────────────────┐ │
│ │ Traffic Timeline │ │ OWASP Top 10 │ │
│ │ ████ ██ │ │ │ │
│ │ █████ ████ │ │ A01 Broken Access │ │
│ │ ██████ ███ ██████ │ │ A03 Injection │ │
│ │ ████████ ██████ ████ ████████ │ │ A07 XSS │ │
│ └────────────────────────────────────┘ └──────────────────────┘ │
│ │
│ ┌────────────────────────────────────┐ ┌──────────────────────┐ │
│ │ Attack Origins (World Map) │ │ LIVE ATTACKS │ │
│ │ │ │ │ │
│ │ . .. │ │ 45.33.x.x SQLI │ │
│ │ . ... .... .... │ │ /api/users?id=1' │ │
│ │ .. .. . . │ │ │ │
│ │ . X │ │ 91.xx.x.x XSS │ │
│ │ . │ │ /search?q=<script> │ │
│ └────────────────────────────────────┘ └──────────────────────┘ │
└──────────────────────────────────────────────────────────────────────┘
| Feature | Description |
|---|---|
| 25 WAF Signatures | SQL injection, XSS, command injection, path traversal, Log4Shell, SSRF, and more |
| 7 Behavioral Rules | Rate limiting, brute force detection, scanner detection, honeypot traps |
| Real-time Detection | Nginx -> Kafka -> Realtime Processor pipeline |
| IP Reputation | Score-based reputation tracking per IP in PostgreSQL |
| Multi-phase Correlation | Recon -> Probe -> Exploit -> Exfil attack chain detection |
| Auto-blocking | Instant block on critical signatures (confidence >= 0.90) |
| Honeypot Endpoints | Fake /wp-admin, /phpmyadmin, /.env that instantly flag attackers |
| GeoIP Integration | Attack origin mapping via DB-IP |
| Threat Intelligence | AbuseIPDB integration for IP reputation lookups |
| SSE Live Feed | Real-time Server-Sent Events attack stream |
| Attack Heatmap | Hour-of-day x Day-of-week threat visualization |
| CSV Export | Export filtered logs for analysis |
| Zero-Day Entropy Detector | Detects obfuscated payloads that bypass regex WAF signatures using Shannon entropy, URL-encoding density, and encoding layer analysis. O(n) per request, <0.1ms, no ML required |
| Self-Contained DDoS Shield | Multi-layer DDoS mitigation without Cloudflare: iptables/ipset (kernel) + GCP Firewall (network) + nginx blocklist (app). 7 anti-false-positive protections, progressive TTL blocking |
| SOC Terminal v1 | Rich-based terminal UI for WAF-only monitoring |
| SOC Terminal v2 | Combined WAF + WiFi Defense + Drone status + autonomous AI narrator |
Catches obfuscated/encoded attack payloads that traditional regex WAF signatures miss:
Detection layers:
1. Shannon entropy — obfuscated payloads have high entropy (>4.5)
2. Encoding layer counter — double/triple encoding detection (17 patterns)
3. URL-encoding density — normal URLs: 0-10%, attacks: 30-80%+
4. Character ratio anomaly — special char vs alphanumeric ratio
5. Structural depth — nested encoding patterns
Performance: 9,500+ payloads/sec, <0.1ms average, zero I/O, zero ML model.
Self-contained DDoS mitigation — zero external dependencies (no Cloudflare required):
Layer 0: GCP Firewall — Network-level blocking (before traffic reaches VM)
Layer 1: iptables/ipset — Kernel-level rate limiting (50 conn/s per IP)
Layer 2: nginx — Application-level rate limiting (10 req/s per IP)
Layer 3: DDoS Shield — Intelligent detection + auto-blocking
cd tokio_cloud/gcp-live
cp .env.example .env
nano .env
docker compose up -dDeploys 7 containers: PostgreSQL, Zookeeper, Kafka, Nginx WAF proxy, Log processor, Realtime attack detector, SOC Dashboard API.
Create a file in tokio_agent/engine/tools/builtin/:
# my_tools.py
import logging
logger = logging.getLogger(__name__)
async def my_custom_tool(action: str, params: dict = None) -> str:
"""Your custom tool logic."""
params = params or {}
if action == "hello":
return f"Hello, {params.get('name', 'world')}!"
return f"Unknown action: {action}"Register in loader.py:
from .my_tools import my_custom_tool
registry.register(
name="my_tool",
description="My custom tool",
category="Custom",
parameters={"action": "Action to perform", "params": "Additional parameters"},
executor=my_custom_tool,
)Drop a Python file in workspace/plugins/ — auto-discovered on startup:
# workspace/plugins/weather.py
TOOL_NAME = "weather"
TOOL_DESCRIPTION = "Get current weather for a city"
TOOL_PARAMETERS = {"city": "City name"}
TOOL_CATEGORY = "Custom"
async def execute(city: str) -> str:
import httpx
async with httpx.AsyncClient() as client:
resp = await client.get(f"https://wttr.in/{city}?format=3")
return resp.text| Method | Path | Description |
|---|---|---|
POST |
/chat |
Send a message and get a response |
GET |
/health |
Health check |
GET |
/tools |
List available tools |
GET |
/sessions |
List sessions |
DELETE |
/sessions/{id} |
Delete a session |
curl -X POST http://localhost:8000/chat \
-H "Content-Type: application/json" \
-H "Authorization: Bearer YOUR_API_KEY" \
-d '{"message": "scan network 192.168.8.0/24 and check for vulnerabilities", "session_id": "pentest-1"}'tokioai/
├── tokio_agent/
│ ├── cli.py # CLI entry point
│ ├── setup_wizard.py # Setup wizard (tokio setup)
│ ├── api/
│ │ └── server.py # FastAPI REST server
│ ├── bots/
│ │ ├── telegram_bot.py # Telegram bot (multimedia, per-user)
│ │ └── Dockerfile.telegram
│ └── engine/
│ ├── agent.py # Agent loop (25-round native tool use)
│ ├── context_builder.py # Dynamic system prompt builder
│ ├── db.py # PostgreSQL helpers
│ ├── error_learner.py # Error learning
│ ├── watchdog.py # Container health watchdog
│ ├── context/ # Context management
│ │ ├── auto_compact.py # Auto-compaction (80% threshold)
│ │ ├── auto_memory.py # Background memory extraction
│ │ ├── compact_prompts.py # Compaction templates
│ │ └── token_counter.py # Token estimation
│ ├── skills/ # Slash command system
│ │ ├── registry.py # Skill registration + aliases
│ │ └── bundled.py # 8 built-in skills
│ ├── subagents/ # Parallel workers
│ │ └── manager.py # SubAgentManager (4 concurrent)
│ ├── llm/ # LLM providers (5 providers)
│ │ ├── base.py # BaseLLM interface + ToolUseBlock
│ │ ├── anthropic_llm.py # Claude (direct + Vertex AI)
│ │ ├── openai_llm.py # GPT-4o, GPT-5, o1, o3
│ │ ├── gemini_llm.py # Gemini Flash, Pro
│ │ ├── openrouter_llm.py # OpenRouter (200+ models)
│ │ ├── ollama_llm.py # Ollama (local, free)
│ │ └── factory.py # LLMWithFallback + auto-chain
│ ├── memory/ # Persistence layer
│ │ ├── session.py # Conversation history
│ │ └── workspace.py # Cross-session memory
│ ├── security/ # Security layers
│ │ ├── prompt_guard.py # LLM prompt WAF
│ │ ├── input_sanitizer.py # Command sanitization
│ │ └── secure_channel.py # API authentication
│ └── tools/
│ ├── registry.py # Tool registration + schema gen
│ ├── executor.py # Async executor + circuit breaker
│ ├── plugins/ # Plugin auto-loader
│ └── builtin/ # 30+ built-in tools
│ ├── loader.py # Tool registration
│ ├── system_tools.py # bash, python
│ ├── file_tools.py # read, write, edit, search, find
│ ├── docker_tools.py # Docker management
│ ├── db_tools.py # PostgreSQL queries
│ ├── document_tools.py # PDF, PPTX, CSV generation
│ ├── gcp_tools.py # GCP WAF + Compute
│ ├── host_tools.py # SSH remote control
│ ├── iot_tools.py # Home Assistant
│ ├── drone_proxy_tools.py # Drone via safety proxy
│ ├── drone_secure_tools.py # Drone with variable timeouts
│ ├── picar_tools.py # PiCar-X robot (36 tools)
│ ├── raspi_vision_tools.py # Entity + health + AI brain
│ ├── security_tools.py # Pentest & defense tools
│ ├── coffee_tools.py # IoT coffee machine
│ ├── sitrep_tool.py # Situation report (all systems)
│ └── ... # + more tool files
├── tokio_cli/
│ └── interactive.py # CLI v4.0 (1963 lines, 15 slash commands)
├── tokio_raspi/ # Raspberry Pi entity system
│ ├── main.py # TokioEntity (face+camera+WAF+drone)
│ ├── tokio_face.py # Animated face rendering
│ ├── vision_engine.py # Hailo-8L YOLOv8 inference
│ ├── face_db.py # Face recognition (SQLite)
│ ├── gesture_detector.py # Hand gesture detection
│ ├── health_monitor.py # BLE smartwatch (HR/BP/SpO2)
│ ├── health_db.py # SQLite health database
│ ├── health_alerts.py # Alert thresholds
│ ├── ai_brain.py # AI Brain (corrections, teaching)
│ ├── security_feed.py # WAF attack feed
│ ├── wifi_defense.py # WiFi deauth/evil twin defense
│ ├── api_server.py # Flask API (:5000)
│ ├── picar_proxy.py # PiCar-X safety proxy (:5002)
│ ├── drone_safety_proxy.py # Drone safety proxy (:5001)
│ ├── drone_fpv.py # Drone FPV (first-person view)
│ └── drone_tracker.py # Visual drone tracking
├── tokio_cloud/ # WAF deployment (100% OPTIONAL)
│ ├── gcp-live/ # Production WAF stack
│ │ ├── docker-compose.yml # 7-container stack
│ │ ├── dashboard-app.py # SOC dashboard (1385 lines)
│ │ ├── realtime-processor.py # WAF engine v5 (980+ lines)
│ │ ├── zero_day_entropy.py # Zero-day detector (entropy)
│ │ ├── ddos_shield.py # DDoS mitigation
│ │ ├── soc_terminal.py # SOC terminal v1 (WAF-only)
│ │ ├── tokio_soc_v2.py # SOC terminal v2 (WAF+WiFi+Drone)
│ │ ├── nginx.conf # Reverse proxy + rate limiting
│ │ └── deploy.sh # Deployment script
│ └── waf-deployment/ # WAF setup docs + ModSecurity
├── docs/ # Documentation
│ ├── ROBOTICS.md # Robot integration guide
│ ├── health-monitoring/ # Health system docs + images
│ │ ├── HEALTH-MONITORING.md # Full health documentation
│ │ └── images/ # Accu-Answer iSaw photos
│ ├── TAILSCALE-MESH.md # Mesh VPN setup guide
│ ├── HOME-ASSISTANT.md # IoT integration guide
│ └── tokioai-architecture.png # Architecture diagram
├── CHANGELOG.md # Version history
├── tests/ # Test suite (10 test files)
├── docker-compose.yml
├── docker-compose.cloud.yml # Cloud deploy with shared postgres
├── Dockerfile
├── requirements.txt
├── pyproject.toml
└── .env.example
pip install pytest pytest-asyncio
pytest tests/ -v| Requirement | Version | Notes |
|---|---|---|
| Python | 3.11+ | Required |
| PostgreSQL | 15+ | Session/memory persistence |
| Docker | 20+ | Optional, for containerized deployment |
| LLM API Key | -- | At least one: Anthropic, OpenAI, Gemini, OpenRouter — or use Ollama (free, no key) |
| Requirement | Notes |
|---|---|
| Raspberry Pi 5 | 5V 5A power supply required for HDMI |
| DJI Tello drone | Any Tello or Tello EDU |
| Tailscale | Free tier, connects cloud to Raspi |
| Requirement | Notes |
|---|---|
| nmap | Network scanning (apt install nmap) |
| openssl | SSL/TLS analysis (usually pre-installed) |
| curl | Web testing (usually pre-installed) |
| ssh-audit | SSH server auditing (optional) |
GPL v3 — Copyright (c) 2026 TokioAI Security Research, Inc. See LICENSE for details.
A project by TokioAI Security Research, Inc.
Built by @daletoniris (MrMoz) — Security architect, hacker, AI researcher, founder of the AI Village at AI Resilience Hub in Ekoparty, professor at Hackademy. From Patagonia, Argentina.
TokioAI started as a personal tool to automate SOC operations and infrastructure management. It grew into a full offensive & defensive security framework because every time something broke at 3 AM, the answer was always the same: "the agent should handle this." Now it flies drones, monitors WiFi attacks, scans networks, and makes coffee — all from a Telegram message.
If you find it useful, drop a star. If you break it, open an issue. If you improve it, send a PR.
TokioAI Security Research, Inc.
Self-hosted AI that executes. Not a chatbot — an agent that hacks, defends, and flies.

